
Yesterday we did a run down of Transmission 2 as part of a series of posts covering the ARG that we ran throughout April. Today I’m going to reveal all the details in Transmission 3, how we put it together and what the answers were.
In classic Hackaday fashion we hadn’t planned any of this, so by this point all our initial ideas we already used up and we were now running out of creativity so it was a real slog to get Transmission 3 out the gate. However we somehow managed it and opened Transmission 3 by posting a series of 5 images of space telescopes:
Major Tom also posted a new page Transmission #3 on his profile with the image below and the text “Confirm launch site”:
Since the last puzzle was solved in just a few hours, and the first in a mere 20 minutes we decided we needed to up the difficulty on this one. We were hoping it would take a few days, which I think would have been about right if a couple of things hadn’t gone completely wrong…
Hidden data
The telescope images are much bigger in file size than they have any right to be. Those of you that noticed this soon discovered that there was a block of data tacked on the end of each file. This is a lovely little trick that takes advantage of the fact that the JPEG file format has an End Of Information marker at the end of the file, 0xFF 0xD9. You simply tack on whatever information you want after this byte and the jpg file is magically still valid. You can do this with the copy command on Windows “copy /B file.jpg + file2.whatever > hidden.jpg” or with cat on linux “cat file.jpg file2.whatever >> file.jpg”.
We used the same method to append a Minecraft skin onto the end of the Transmission 3 rocket image, this was just a little easter egg hint towards the following week’s puzzle.
So everyone found the data blocks at the end of the telescope images, giving them 5 binary files but no clue as to what they were. After a little while a couple of people on the IRC channel noticed that the data blocks contained the word ‘Salt’. It became clear that this was an OpenSSL encoded file since the first 8 bytes of the file started with the word ‘Salted__’ indicating that the file was encrypted with a salted password. The chase for the appropriate decryption methods started to heat up.
People got really ingenious here trying all manner of tools. One person even wrote a script to try to brute force the encryption method using every available option in OpenSSL. Many passwords were tried and everyone worked really hard on this for hours. The files were encoded with OpenSSL using the aes-256-cbc encryption method, the password for which was given out in the hidden data in Transmission 1, “I’m floating in a most peculiar way”, or so we thought. It turned out that when I had encoded these files at the command line on Windows the apostrophe had been swallowed up resulting in the password actually being “Im floating in a most peculiar way”. Thankfully someone tried decoding on Windows eventually and they cracked it, everyone in IRC figured it out from there and soon all 5 files were decoded and discovered to be MP3 files:
Generating Audio Puzzles
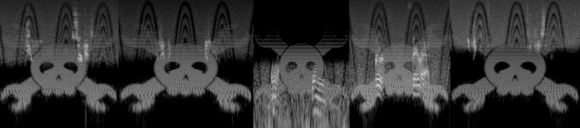
When the MP3s were found the first thing everyone noticed was the little easter egg we hid inside the noise in the video. We were inspired by the hidden images that [Aphex Twin] encoded into his release of Windowlicker back in the late 90’s. So of course since we were releasing audio files we just had to encode the Hackaday logo into the audio:
From these spectrographs you can see the Jolly Wrencher very clearly, and you can also see how each file is band pass filtered to a specific set of frequencies.
The images were created using the tool Coagula. Using this tool and its basic settings you can import an image and have it converted into an audio file. There’s a few settings to play with but we found that using the ‘Render the image without noise’ option made the best result when played back in various audio players. Using the other option made it very hard to view the image. Once we had the wav files we simply added them as another layer of audio in audacity, this was merged together with a noise track and an audio track from [Brian]. After all the effects were applied we then added hi and lo pass filters to place the audio in a range that was some multiple of the reception range of each telescope. I believe we took each telescopes frequency range and divided it by 250,000 to end up with something in the range of human hearing.
We also added one additional easter egg, we had calculated how long it would take for a radio transmission to go from Major Toms position in orbit to each of the telescopes in the images. 3 of the scopes would never have received the audio, but 2 of them would have. So in the ID3 comment field in the MP3s we added the following information:
Transmission received at T-1090800.0222786265106846
Transmission received at T-1090800.0296872268554892
This indicated the time at which each scope would have received the signal. We had hoped that with this information in hand some enterprising folks would have worked out how to triangulate Major Tom from his orbital inclination, altitude and the longitude/latitude of each of the telescopes. In theory this is still possible, but we’re not exactly sure of the answer ourselves! If anyone out there has a good explanation of how to do this sort of math to figure out where Major Tom was at the time of Transmission 3 then we would love to hear it in the comments.
What on Earth?
Once everyone had found the audio files they began trying to extract the audio from the noise to decipher the words that were being said. In each track 2 words were spoken. On some of the files this was pretty easy, words like ‘Earth’ and ‘Ground’ were quite easy to distinguish. However it appears that while it was easy for us to figure out what was said it was very very hard for someone who didn’t know what the words were supposed to be. In typical fashion we didn’t have time to test the files on people who weren’t already familiar with them so we ended up making the files far too noisy for anyone to understand. That’s not to say that you all didn’t try really hard, there were some very valiant attempts to clean up the audio and remove the image noise, some more successful than others. In the end I believe all but 3 words were unidentified.
Since it became clear nobody was going to get any closer we decided that we had to help everyone along with this one so we posted out an email to the 1000 or so people who had signed up on April 1st. This email contained the following text:
A signal was received from Major Tom at 00:01 on 15/04/2014, transmission archive available here:http://hackaday.com/2014/04/15/119822/
A pirate signal was detected on the transmission and has since been removed. Clean transmission data is now available at the following locations:http://hackaday.s3.amazonaws.com/space/1.mp3
http://hackaday.s3.amazonaws.com/space/2.mp3
http://hackaday.s3.amazonaws.com/space/3.mp3
http://hackaday.s3.amazonaws.com/space/4.mp3
http://hackaday.s3.amazonaws.com/space/5.mp3Please confirm launch site coordinates.
The links lead to cleaner versions of each file. As soon as these went out we immediately had people responding with the words they could now hear clearly.
“Earth Farad”
“Joule Circuit”
“Amp Gain”
“Electron Capacitor”
“Dielectric Diode”
Codewords
The question then became what did they mean? A lot of ideas were floated around. My favorite by far was the idea that these words were hidden throughout Hackaday posts to create a secret message based on the position of the words in each post, or some other variation therein. I really wish I had come up with that, but sadly it was much simpler.
The first letter of each word mapped to a 0 indexed number where A=0, B=1, C=2 etc. This gave us the following numbers, 45 92 06 42 33. From here it took a while for everyone to guess what these might mean eventually somebody hit on the idea of these numbers being a longitude and latitude, 45.920N 64.233E. This didn’t point to a location of any particular interest, but was quite close to the Baikonur Cosmodrome in Kazakhstan. Since the target was a little off the folks on IRC quickly discarded this as an option and moved on to other things. Later on someone more persistent tried every possible combination of the 5 pairs of numbers and plotted them all on a google map from there it became clear that the last two numbers had been reversed and that the correct answer was in fact the Site 1 launch pad (Gagarin’s Start) at the Baikonur Cosmodrome.
We’re really sorry that the guys that first went down this track missed the solution, this was in part our fault in that we had decided to make it harder to find the right coordinates. The intention was to have the numbers scrambled in a random order, but if you rearranged them into the telescope coordinate latitude order then they would point to the correct location. Of course I randomized the coordinates by hand and ended up with the first 3 being in the correct order which made the whole thing a little misleading. Still, brute force wins all and eventually the solution was found.
After the correct coordinates were confirmed and posted to the Transmission 3 page we had Ground Control issue another message to close the round:
Major Tom, this is Ground Control.
Launch site confirmed.Await rescue mission at T-525600. Suit up!
This time we returned to the T-seconds notation we used in Transmission 1, more confusion, but by now everyone was getting the idea to expect another puzzle each week so it didn’t matter much! The next transmission was to come out a week before the announcement of The Hackaday Prize so we decided it needed to be something big and inclusive, but more on that tomorrow.





















I don’t care about your tricks and games. Canonisation od Polish Pope John Paul II is what matters for most od US.
“Most of us.” Bloody android keyboard.
Who give a c*** ?
I didn’t participate in these as much as I would have liked to, but they really were fun and I hope you do it again next year. I basically spent about 20 minutes with each puzzle and then went back to doing my real job :). A+ on the effort you guys put into these.
I’m just glad of the massive David Bowie references….
I also didn’t get to spend as much time as I would have liked. I really like the fact that you’re writing up the story, though, as well as the things you did wrong. Can’t wait for the Minecraft piece!
I’m really glad that you’re taking the time to tell us “Here are the things we did wrong, here are the things that were figured out immediately, and here are the things that took longer than we expected.”
This is the sort of information that is great to know for anyone planning on making their own ARG in the future.
Epic!