The RF signal transmitted from a modern key fob and received by the associated vehicle is only used once. If the vehicle sees the same code again it rejects the command, however there is a loophole in those carefully chosen words. The code must be received by the vehicle’s computer before it can be added to the list of spent codes. [AndrewMohawk] goes through the process of intercepting a code sent from a key fob transmitter and preventing the vehicle from receiving it in a thorough post to his blog. You can see this attack working in his studio quality reenactment video after the break.
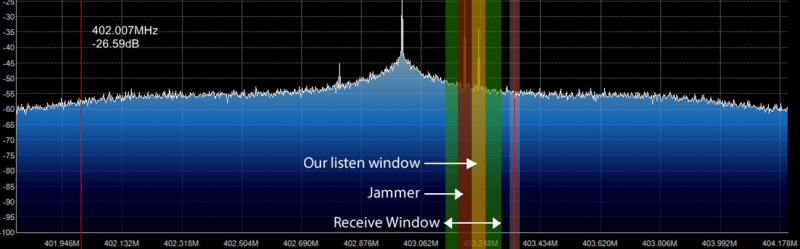
[Andrew] uses the YARD Stick One (YS1) which is a sub-GHz wireless tool that is controlled from a computer. The YS1 uses RfCat firmware, which is an interactive python shell that acts as the controller for the wireless transceiver.
This system is not without its problems: different frequencies are often used for different commands, [Andrew]’s scripts are designed to work with On-Off keying (OOK) leaving it useless when attacking a system that uses Frequency-Shift Keying (FSK). There is also the issue of rendering a target key fob non-functional but you’ll have to pop over to [Andrew]’s blog to read more about that.
We covered previous SDR hacks which were aimed at stealing cars and ringing doorbells. You may also recognize the hardware setup in the thumbnail as [Samy Kamkar]’s RollJam rig and you guessed it, that’s a shoehorned segue to another post covering one of [Samy]’s projects.















There was similar article on HAD two years ago : http://hackaday.com/2014/03/17/hacking-rolling-code-keyfobs/
So if multiple people succeded in such attacks we can assume there are devices on black market that can utilize this in more malicious ways than just security research.
I’d guess so. It’s relatively easy to protect against, but car electrical systems manufacturers aren’t the fastest-responding…
These type of devices were created very long time ago, i mean the rolling code grabber i remember first seeing them in 2006 but all information is on russian forums which is good and cannot be found easly if you search english terms. They support alot of encryption “standarts” keeloq, cfm and all car manufactor keyfobs are supported. If you search more they also posted a opensource code grabber for keeloq . oh and keyless system are also saupported.
you know!! this could be how the cars was getting broken into?
remember the tesla coil trick for unlocking cars? maybe it is this instead
They are 300-400 megahertz(and have been since the 90s) and there are at least 13 different rolling code algorithms.
They just jam the receiver and replay to dongle code later. It’s actually not hard to RE the dongles for the whole challenge/response algorithm they use cheap spec chips that have ROM/SDRAM/RESONATOR buses that typically have debug enabled..
If you wanted to RE the RFID key algorithms you’d have to dump the ROM of an ASIC in the ECM or BCM or SCM(I’ve seen them in each)(Now days they are usually in a SCM)..
Theives usually just use “unlocked” ECMs because they usually have connections inside dealerships and plants.
So after 30+ years this rolling code encryption is (shoud be) finally obsolete.
Strangely andrewmohawk still suggests “two way authentication” is “far more expensive”.
What’s the latest price of a nRF24L01 rfm69 etc? (versus Keeloq).
duckducking “keyloq” gives a link to an article (including pdfs, russians, etc) which is apparently 8,5 years old:
http://www.wired.com/2007/08/researchers-cra/
Technically salting or encrypting with a RNG or clock-scew or discreet-math or a time-stamp is rolling code.
These jam+replay attacks aren’t even really advanced attacks. If someone dumps a stamp and publishes the algorithm on the net that is far more dangerous. It’s perfectly possible. The chips that hold it in the dongle have debug enabled and aren’t tamper resistant..
The key challenge/response is far more hard because the ASIC in one of the three PCBs typically has some security like encrypted-firmware with key-rom or write-only debug.
I was really in to this stuff in the nineties and early two-thousands. The corvettes had it in the eighties and then everyone else got it around 1994. Before that even economy Nissan’s had anti-hotwire circuits.
100% agree with your points. Do you have any of your research available still? I’d dig to take a look!
I have a lot of data. For tools I only have something for Megamos RFID crypto(nothing has ever been published on it) and a old PASSKEY,brute-force tool. I have IDA databases on some things too but they need clean-roomed of some code.
Oh yeah a replay circuit from 2003(the same one was used on TV that year) for primitive replay(no jamming)
Heya,
Recalling all the cars to implement two way auth between remote and car would be crazy expensive. Especially if a cost/risk analysis was done since so many people still do not know about their remotes being jammed etc.
There was a fantastic talk/paper a few years ago on using power analysis to break the remotes rolling code implementation itself, but this was more looking at doing this from a remote point of view without access to the remote :)
-AM
This is a attack on RF integrity, but there probably is an attack on the algorithm itself. Here they are just blocking the receive end so a replay attack still works. It’s 100% RF logging really.
Heya,
Yup, agreed, this definitely doesnt look at the algorithm at all, primarily because this attack is easy enough to pull off and works on all the different variants of classic rolling code systems.
At its core its just a stock standard replay attack (that I had done before anyway with AM/OOK signals).
The attacks against the algorithms before are usually very involved and invasive on the system — they usually have the remotes in pieces and are doing DPA. Otherwise people have tried to beat the PRNG on the devices, but I still haven’t seen a conclusive remote break in the algorithms for these devices. I suspect that will be the turning point for these type of systems to finally die.
-AM
I thought rolling codes were mapping of a large subset of natural numbers to a set of quasi-random codes. In other words, I thought that receiver can’t just keep the list of all codes that passed, because it would take too much non-volatile memory space. Instead, it should reject all codes which are of lower ordinal number then last received code. If it did that, then this type of attack would have very narrow window of opportunity, that between failed command by key-fob holder and first successful command following that one. Since wireless remote controls are usually operated until the car responds, in a short audio-visual feedback loop, how would this attack ever work?
“… thAn the last received code.” Sorry.
A staggering majority use real challenge/response with cached RNG or discreet math though. This is a side-channel attack that should exist for all the systems though just with varying timeouts.
I’m sure a static list system has been implemented before though either by a maker or third party alarm vendor.
Some criminals even used only a jammer: They prevented the car from receiving the locking command on a shopping center parking lot. After the people walked away, the criminals opened the door. Of course this only works with people who (in a hurry) don’t look if their cars flashes the indicator lights to signal that it has locked.
That’s what this is. The block it but they record the dongle transmission. It has the same logistics.
How would I alter the python script in PWMScanner.py to work for FSK?