It kind of hurts watching somebody torturing a brand new Fluke multimeter with a soldering iron, even if it’s for the sake of science. In order to find out if his Fluke 12E+ multimeter, a feature rich device with a price point of $75 that has been bought from one of the usual sources, is actually a genuine Fluke, [AvE] did exactly that – and discovered some extra features.
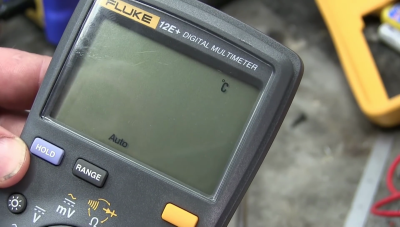 During a teardown of the multimeter, which involved comparing the melting point of the meter’s rubber case with other Fluke meters, [Ave] did finally make the case for the authenticity of the meter. However, after [AvE] put his genuine purchase back together, the dial was misaligned, and it took another disassembly to fix the issue. Luckily, [AvE] cultivates an attentive audience, and some commenters noticed that there were some hidden button pads on the PCB. They also spotted a little “C”, which lit up on the LCD for a short moment during the misalignment issue.
During a teardown of the multimeter, which involved comparing the melting point of the meter’s rubber case with other Fluke meters, [Ave] did finally make the case for the authenticity of the meter. However, after [AvE] put his genuine purchase back together, the dial was misaligned, and it took another disassembly to fix the issue. Luckily, [AvE] cultivates an attentive audience, and some commenters noticed that there were some hidden button pads on the PCB. They also spotted a little “C”, which lit up on the LCD for a short moment during the misalignment issue.
The comments led to [AvE] disassembling the meter a third time to see if any hidden features could be unlocked. And yes, they can. In addition to the dial position for temperature measurement, [AvE] found that one of the hidden button contacts would enable frequency and duty cycle measurement. Well, that was just too easy, so [AvE] went on checking if the hidden features had received their EOL calibration by hooking the meter up to a waveform generator. Apparently, it reads the set frequency to the last digit.
The 12E+ is kind of a new species of Fluke multimeter: On the one side, it has most of the functionality you would normally expect from a “multi”-multimeter – such as measuring both AC and DC voltage, current, capacitance and resistance – and on the other side it costs less than a hundred dollars. This is made possible by the magic of international marketing, and Fluke seems to distribute this crippleware product exclusively in the Chinese market. Therefore, you can’t buy it in the US or Europe, at least not easily. A close relative of the 12E+ which should be a bit easier to obtain is the Fluke 15B+; the meter we saw earlier today when [Sprite_TM] hacked it to share measurements via WiFi. The 15B+ seems to be identical to the 12E+ in appearance and features, although it’s unknown if the two are hackable in the same ways.
https://www.youtube.com/watch?v=FUmbsBYVTQ0
Thanks to [jacubillo] for the tip!
















Here’s a question, and I don’t mean to be smart, but how much content on Hackaday is now internally generated and user submitted vs. commentaries on articles pulled from other websites?
It just seems more and more common to see the “Thanks to “X” for the tip!” at the end of articles, indicating that either you’ve just writing a summary of someone else’s content (no doubt with their permission).
When someone sends in a link to a project we like to thank them for the effort at the end of the article.
As for covering others’ work, we do celebrate the greatest hacks from around the web. We have also been building our body of original content which you can see in the featured and columns categories that are shown in the right sidebar of the page.
For more on this you might want to check out the talk I gave at the Hackaday Supercon on Hackaday’s Editorial Vision.
If it linked to me,all of it.
> Here’s a question, and I don’t mean to be smart
Don’t worry about that.
> how much content on Hackaday is now internally generated and user submitted vs. commentaries on articles pulled from other websites?
Much less now. Me saying that doesn’t mean much, so let’s just do some random sampling. Here’s all the posts on May 6, 2012.. What do we have? Someone built an automated cat feeder. Someone built an Arduino shield for the Raspi. Someone built a gender monitor for a unisex bathroom (seriously. This would be the most commented post of the month if it were posted today, because you’re all so predictable.. Someone built a sound-dampening stand for a keyboard. Someone made a motorized zoom lens. You can see all those were projects *other* people did.
Let’s check out another random day. Here’s Feb 28, 2014.. Someone built a tiny ARM platform. Someone put a thermostat in a clubhouse. TI put an antenna reference app note up. Raspberry Pi GPU bounty was won. Someone made a computer play flappy bird. Someone modified a power supply for a quieter fan. Someone built a homebrew laser rangefinder. On that day, you’re looking at 7 posts, one of which was newsworthy, and another that was just a link to an app note.
So, in the last 24 hours, we’ve had an (internal) post on literate programming, An (internal) post from Maker Faire, a post about Cody’s Lab, A post on a DLP printer, A post on cheap RF modules, A hackaday prize post (arguably internal), a retrotechtacular (internal), Sprite_TM’s WiFi multimeter, Bob’s post about scrapping stuff (internal), a post on AM radio (internal), and a post on AvE’s meter. That’s 11 posts, 6 of which were generated internally.
So, you can see we are generating much more content internally. Now, it’s pretty much half. A few years ago, we would be lucky if it were one post a week. To answer your question, no, we are demonstrably not posting more content from outside sources. The opposite is true.
I would encourage you or anyone else to go through a few more days and figure this out for yourself. Write a script and post it on hackaday.io. That’s a sure-fire way to get a project on the front page of the blog.
> Write a script and post it on hackaday.io. That’s a sure-fire way to get a project on the front page of the blog.
I would love to see someone do this. Please. I love a good statistics hack
and maybe plot a curve to show how its changed over time?
damnit, now I know what im doing after work tonight… thanks Brian
classification is going to be your problem.
Easiest would be to use HaD’s name tagging format. Just find articles with [Name] in the first two paragraphs, pretty likely to be about someones project. If there is no name tag, it’s likely a column or other feature article.
@Kratz, thats what Im attempting now. Just need to find the right tools.
First attempt I am using wget –spider, but that catches *every* url on the page.. Now Im looking for a different trick to pull just the article names
You also have to account for reposts, like the train article.
Perhaps https://www.import.io might help you on getting all articles, classification as suggested by Kratz can be done afterwards.
Well I got as far as this script to list out the articles for a specific day, but as you mentioned, I see no reasonable way to classify each article :(
#!/bin/bash
wget –spider -o wget_log0 hackaday.com/2016/06/07/*
sed -n ‘/Location:.*http:\/\/hackaday.com\/.*/p’ wget_log0 > wget_log1
sed -e ‘s/Location:.*\/[0-9][0-9]\/[0-9][0-9]\///’ -e ‘s/\/ \[.*\]//’ wget_log1 > wget_log0
cat wget_log0
rm wget_log0 wget_log1
here’s a start
https://hackaday.io/project/12145-hackaday-webscraper
I’v been working on this as well. I started a hackaday.io project. I scraped the data from the Wednesday night all the way back to September 5th, 2004, all 22,556 articles. The python script to collect the postID, date, title, author, “posts” and tags is shown. I have also uploaded the entire dataset for others to slice and dice (~1MB zipped). I have a few plots showing changes over time.
Forget link to project: https://hackaday.io/project/12158-hackaday-statistics
There’s more than one website that started off lifting from Reddit. Hopefully it’s a stage you grow out of, or end up either reduced to whoring your mother on Facebook, or people get tired of your site’s complete lack of any independent qualities.
It is quite likely that Reddit was ‘lifting’ stuff off of HaD when *it* first started, as HaD predates reddit. And yes, I was there, although I have yet to order one of the rocking Jolly Wrencher tee shirts.
The internet, and maybe the world, is changing. Hacking is a more mainstream, legitimate thing than it used to be. There are more hack-centric websites than just HaD and some Reddit chan’s, and cross-posting, or lifting shit, as you put it, is fair use.
I’m glad there are plenty of great hacks to share, even if they’re not all born here.
do you even hackaday? lol.
Somebody should 3D model the top case shell so we can 3D print a new shell with the extra buttons. Should be identical to the 17B+ but with 3 more buttons and a different dial stopper
Whatever you do… don’t print it in yellow!!!
There’s no point in making a custom case because the 17B+ is only a few dollars extra. You’d only save like 4 bucks getting this model over the 17B+.
In other words, this Fluke is a 17B+ in a different case…. which is how this “hack” works. (It’s not a hack).
Unlocking crippleware is always a great hack. Admittedly there’s not much financial incentive here, but when has that ever stopped anyone from modding?
Did you watch the video? He didn’t unlock anything. He literally open it up and pushed a button that was covered up by the case. There’s no convenient way to make it accessible it for later use (you’ll want the cover back on). You could do something klugey, or If you know about the different models before you buy, you can buy that exact same board in a case that doesn’t cover up the button for only a few bucks more. If you went through the effort, you’re doing a ton of work for a $4 feature.
“Push a secret button, before closing it back up again and losing access to that secret button” isn’t unlocking a cripple, it’s just discovering it exists.
The 17B+ costs $100 more than the 12E+, not $4.
From an american vendor, maybe, because they want a profit. Go to ebay, type in 17B+ fluke, and you’ll find places in shenzen willing to sell it for $106 with free shipping. These are meant for the chinese market, but they’re apprantly real flukes (props to AvE for proving that in this same vid – again this is the real story).
So yes, a scant few $ more if you’re buying direct from china. Really. Otherwise you’re paying a middle man.
If you read the Youtube comments you will find that this “hack” has been know about since 2010 for the Fluke 15B.
https://dev.xdevs.com/documents/8
“Man opens case and pushes previously covered up button”.
It’s not a hack. It’s a 17B+ which costs a few dollars more than this model (both are meant to be for the chinese market only).
The real story is how cheap these genuine Fluke meters are.
I watch AVE, sadly often minutes after he’s posted. “Soldering iron” ? not this time buddy
I had an old Fluke 8X.. sometime i found (pressing one key) one function that was not at the manual, it was for test low resistence 0.01 ohm res. it was usefull for me.