Far too much stuff is wireless these days. Home security systems have dozens of radios for door and window sensors, thermostats aren’t just a wire to the furnace anymore, and we are annoyed when we can’t start our cars from across a parking lot. This is a golden era for anyone who wants to hack RF. This year at Shmoocon, [Marc Newlin] and [Matt Knight] of Bastille Networks gave an overview of how to get into hacking RF. These are guys who know a few things about hacking RF; [Marc] is responsible for MouseJack and KeySniffer, and [Matt] reverse engineered the LoRa PHY.
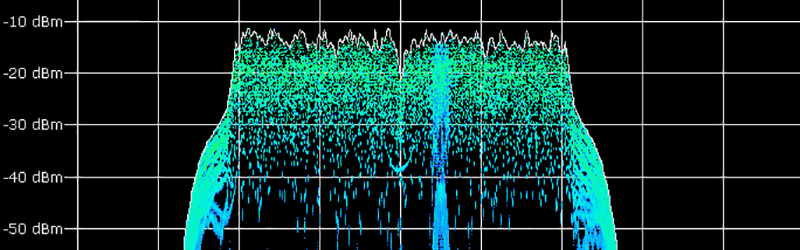
In their talk, [Marc] and [Matt] outlined five steps to reverse engineering any RF signal. First, characterize the channel. Determine the modulation. Determine the symbol rate. Synchronize a receiver against the data. Finally, extract the symbols, or get the ones and zeros out of the analog soup.
From [Marc] and [Matt]’s experience, most of this process doesn’t require a radio, software or otherwise. Open source intelligence or information from regulatory databases can be a treasure trove of information regarding the operating frequency of the device, the modulation, and even the bit rate. The pertinent example from the talk was the FCC ID for a Z-wave module. A simple search revealed the frequency of the device. Since the stated symbol rate was twice the stated data rate, the device obviously used Manchester encoding. These sorts of insights become obvious once you know what you’re looking for.
In their demo, [Marc] and [Matt] went through the entire process of firing up GNU Radio, running a Z-wave decoder and receiving Z-wave frames. All of this was done with a minimum of hardware and required zero understanding of what radio actually is, imaginary numbers, or anything else a ham license will hopefully teach you. It’s a great introduction to RF hacking, and shows anyone how to do it.















Is the talk available somewhere, I don’t see anything but a live stream on the event website
I need a lititle help reverse engineering a signal. So far I have used rtl-sdr library with inspectrum and I have been able to see the sigal I was looking for. I know is OK Manchester encoded but It’s a bit painful to extract the symbols by hand; it is 128 symbols and they don’t fit in my screen at a reasonable size so I get lost counting with a finger on the monitor, is a mess.
I was trying to use DSPECTRUM for getting the symbols but is not working properly I don’t know why. Is there any other automated way of getting the symbols out of the signal? A software like DSPECTRUM that works would be perfect.
Thanks!
Hi Manual,
Sorry a little late on the reply here. I am the guy behind DSpectrum and it has evolved into a new tool: DSpectrumGUI (https://github.com/tresacton/dspectrumgui. It will both pull signals out of Inspectrum and also demodulate Manchester automatically. However, the actual technique used to extract the raw binary out of Inspectrum is the same. If I had to wager a guess as to why this didn’t work for you, I would guess that you hadn’t lined up the bits perfectly in Inspectrum’s grid overlay – this is very crucial for accurately extracting the data. If you give DSpectrumGUI a shot, please let me know if you do encounter any difficulties (asking a question via github’s issue creator is a good idea, or just dm me on twitter (@tresacton). The new app is actively maintained and has entirely replaced the original DSpectrum.
Cheers,
nullwolf
A link to the talk would be great. Are these available online?
They won’t be for six months or so.
Here’s the talk link:
https://m.youtube.com/watch?v=L3udJnRe4vc