When you need coffee, you don’t need any hassles standing between you and caffeination. Especially ironic hassles, like having to do more to turn on appliances inside of home automation schemes than you did without them.
[Maurice Makaay] bought a smart plug to add this beautiful drip coffee machine to his Z-Wave setup, but it isn’t all that smart. Starting the brew remotely means making sure that both the machine’s power switch and the smart plug switch are on. Some members of the household still like making their coffee the old-fashioned way, so [Maurice] came up with a smart, single switch solution to satisfy both cases.
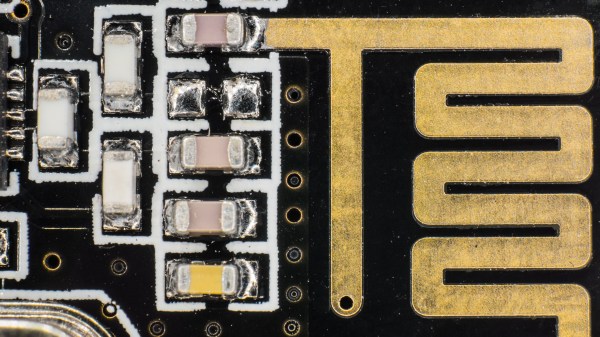
 The answer comes in the form of a Z-Wave switch that takes dual inputs and is small enough to fit inside the machine. After a lot of searching around for compatible, splash-proof parts, [Maurice] replaced the existing on/off rocker with a momentary rocker for making coffee manually. That switch labeled ‘extra heet’ used to turn the warming burner on and off. Since he never uses the burner, the switch receptacle now houses a power indicator light.
The answer comes in the form of a Z-Wave switch that takes dual inputs and is small enough to fit inside the machine. After a lot of searching around for compatible, splash-proof parts, [Maurice] replaced the existing on/off rocker with a momentary rocker for making coffee manually. That switch labeled ‘extra heet’ used to turn the warming burner on and off. Since he never uses the burner, the switch receptacle now houses a power indicator light.
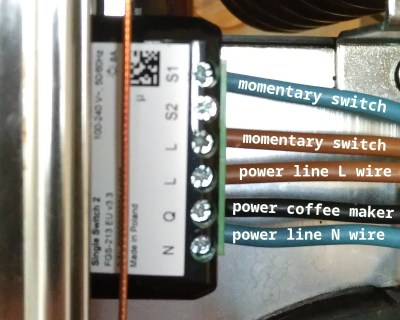
[Maurice] went about this mains appliance hack the right way — he used extra thick wires connected with lever nuts, and kept the machine’s equally beautiful spare parts and safety documentation by his side the whole time. A person could probably become a lot more comfortable with the idea of installing these by looking over [Maurice]’s pictures of the process.
You know how coffee makes everything better? Turns out ‘everything’ includes printer filament.