Airgapping refers to running a machine or machines without connections to external networks. Literally, a gap of air exists between the machine and the outside world. These measures present a challenge to those wishing to exfiltrate data from such a machine, leading to some creative hacks. [Jacek] has recently been experimenting with leaking data via Ethernet adapters.
The hack builds on [Jacek]’s earlier work with the Raspberry Pi 4, in which the onboard adapter is rapidly switched between 10 and 100 Megabit modes to create a signal that can be picked up via radio up to 100 meters away. Since then, [Jacek] determined the Raspberry Pi 4, or at least his particular one, seems to be very leaky of RF energy from the Ethernet port. He decided to delve deeper by trying the same hack out on other hardware.
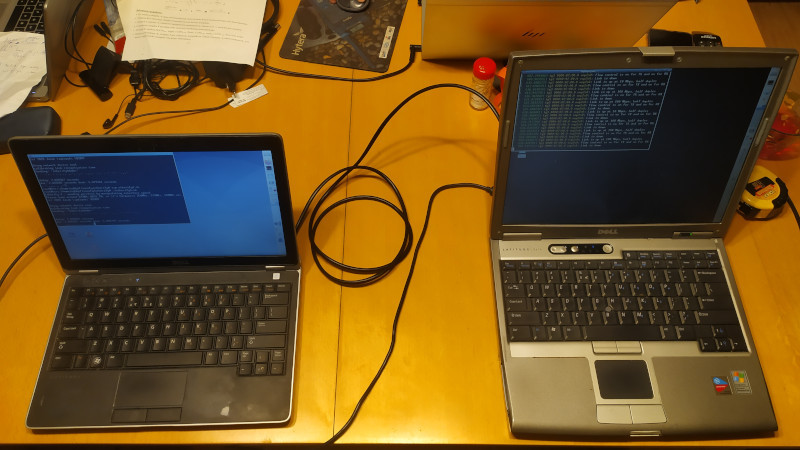
Using a pair of Dell laptops connected back to back with an Ethernet cable, the same speed-switching trick was employed. However, most hardware takes longer to switch speeds than the Pi 4; usually on the order of 2-5 seconds. This limited the signalling speed, but [Jacek] was able to set this up to exfiltrate data using QRSS, also known as very slow speed Morse code. The best result was picking up a signal from 10 meters away, although [Jacek] suspects this could be improved with better antenna hardware.
While slow data rates and the one-way nature of such communication limit the utility of such an attack, it nonetheless shows that securing a machine isn’t as simple as unplugging it from the network. We’ve done a feature on such hacks before for those interested in learning more. Video after the break.















Tempest…
A couple questions:
A stock RPi spews RFI 100 meters?
The ‘air gap hack’ described here shows the RPi with nothing in the RJ45, what happens when the RPi actually tries to do actual work on the Ethernet jack and this hack is constantly re-negotiating link speed.
I understand this is a proof of concept, but you’re trying to leak data out of a system with built-in WiFi – there has to be a simpler way to leak data… I’ve seen hacks that turn a GPIo pin into an FM broadcast band audio transmitter – that seems like another, more useful vulnerability (CW in the FM broadcast band should be easier than FM modulation).
I’d think the performance hit would show up somewhere. Part of “hacking” is no one noticing one’s doing it.
With modern multi core processors, you can hog a core with no noticable effect on user performance. If you’ve hacked into the machine you can hack the CPU stats reporting, so no, nobody will notice.
Not uncommon. The emi limits are low but not extremely low. With a narrowband signal, good receiver and directional antenna you can certainly pick up ethernet radiated emissions. He is probably picking up the RGMII clock from CPU to PHY. Doesn’t matter for that that there is no cable plugged in.
Not only FM, rpitx allowed even to send quadrature modulation signals using that GPIO!
The Ethernet mode switching noise from a Pi3/Pi4 is pretty significant.
I see spikes to -55dBm into a dipole across a very wide section of the HF band when this occurs on my HamMesh set up. It is so bad, that I had to force a non-negotiated connection.
Never considered this could be a way to send information.
It’s not truly air gapped until it’s inside a Faraday cage, I guess.
I wonder if something similar could be done by varying mipi clock speed. Granted that isn’t often accessible outside the kernel.