While many of us were enjoying some time off for Thanksgiving, the US government took drastic action against Huawei and four other Chinese companies. The hardest hit are Huawei and ZTE, as the ban prevents any new products from being approved for the US market. The other three companies are Dahua and Hikvision, which make video surveillance equipment, and Hytera, which makes radio systems. FCC Commissioner Brendan Carr noted the seriousness of the decision.
[As] a result of our order, no new Huawei or ZTE equipment can be approved. And no new Dahua, Hikvision, or Hytera gear can be approved unless they assure the FCC that their gear won’t be used for public safety, security of government facilities, & other national security purposes.
There is even the potential that previously approved equipment could have its authorization pulled. The raw FCC documents are available, if you really wish to wade through them. What’s notable is that two diametrically opposed US administrations have both pushed for this ban. It would surely be interesting to get a look at the classified reports detailing what was actually found. Maybe in another decade or two, we can make a Freedom of Information Act request and finally get the full story.
Fuzzing for Recollapse
[0xacb] has a fun new technique to share, that he calls REcollapse. It’s all about regular expressions that get used in user input validation and sanitation. Regex is hard to really get right, and is full of quirks in how different languages and libraries implement it. A simple example is an email address that contains “punycode” — non-ASCII Unicode characters. It’s perfectly legitimate for an address to contain Unicode, but many normalization schemes collapse unicode strings down into the nearest approximation of ASCII. Take exámple.com and example.com. If some part of a web service sees these as the same thing, and another backend service keeps sees them as unique, that mismatch could allow account takeover. Enter your email here to receive a password reset link.
The novel thing here is a structured approach to fuzzing for these problems. [0xacb] suggests identifying “regex pivot positions”, places in a string where there could be unexpected or inconsistent regex matching. A very different example of this is the end-of-string symbol, $. A developer might use this to specify that a given pattern should only be matched when it’s at the very end of a string. But what happens when there’s a newline embedded in the string? It depends on the language. Yikes!
REcollapse is now available as an Open Source tool, and works great to feed fuzzing inputs into an automated tool. Run it against a target, and watch for different responses. Find something good enough, and profit!
Phishing With Smart Watches
The team at Cybervelia have cooked up yet another way to spear-phish a target. Many of us have smart watches, and one of the most useful functions of those wrist-mounted marvels is to glance at a SMS or other message without fishing out a phone. Could an attacker, with a Bluetooth Low Energy antenna, spoof a text message to a nearby smart watch? After some reverse engineering work, absolutely. With the right message, like “need help, 2nd floor”, the target might just start moving without checking the phone and discovering the spoof.
Real-time Malware Hunting
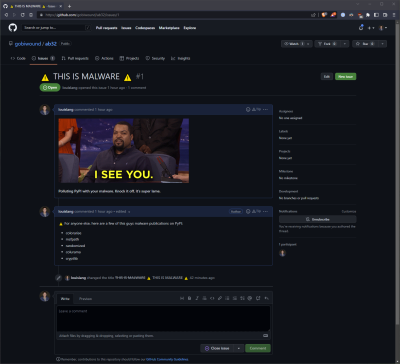 This one’s fun, as the researchers at Phylum found yet another malicious PyPi package campaign back on the 15th. Their tooling alerted them to the activity very early in the campaign, as packages were being uploaded and the payload was still being fine-tuned. That payload was being developed on Github, so there was only one thing to do.
This one’s fun, as the researchers at Phylum found yet another malicious PyPi package campaign back on the 15th. Their tooling alerted them to the activity very early in the campaign, as packages were being uploaded and the payload was still being fine-tuned. That payload was being developed on Github, so there was only one thing to do.
The union of memes and security research is a wondrous thing. The packages were reported, removed, and it looks like this particular malware campaign was eliminated before it really got started.
This does lead to a hilarious tangent from Phylum, about some of the laughably terrible attempts at malware they’ve discovered in other campaigns. There’s a certain poetic justice to be found in malware refusing to run, because the deobfuscation routine checks for the acknowledgement string and errors out when it’s tampered with.
Lastpass Breach Continued
Lastpass has updated their security incident report, noting that there seems to have been follow-on access of data. They noticed “unusual activity within a third-party cloud storage service”, which usually means Amazon’s AWS. The story here seems to be that a token to the storage service was snagged during the August compromise, and was just now used for more mischief. This does raise some uncomfortable questions about how well Lastpass understands what data was accessed in the earlier breach. That said, cleaning up after an incident is a complicated task, and missing a single AWS token in the action is all too easy.
Another “Legitimate” Commercial Spyware Vendor
In the just-what-we-needed category, the latest report from Google’s Threat Analysis Group names Variston as previously unknown player in the commercial malware game. Like NSO Group and others, Variston seems to have access to 0-day exploits in multiple devices and platforms.
A trio of bug reports were opened in the Chrome bug system, and each contained a mature framework and exploit code for a serious bug. Each of these were known and fixed bugs, but piecing together the clues would indicate that they were being used as 0-days by a vendor, probably Variston. It’s not uncommon for the “legitimate” spyware authors like the NGO Group, the NSA, and others, to properly report bugs once they’ve finished exploiting them, or assumably once a target has discovered the exploit.
500 Years Later
There’s a concept in encryption, that pretty much any encryption scheme is theoretically breakable, given enough time and technological innovation. As an example, see the rate at which quantum computers are developing, and the predicted breakdown of some classical crypto. The philosophy that spills out of this reality is that crypto just needs to be strong enough, that the secrets being protected are entirely stale by the time technology and computing power catch up. Which finally brings us to the story, that Emperor Charles V got nearly 500 years out of his cipher. Probably strong enough.
It turns out that this cipher had some clever elements, like multiple symbols that didn’t mean anything at all, just to make it harder to figure out. The real breakthrough was finding a cipher text that had been loosely translated. It was enough to finally figure out the basic rules. So what was in the central letter that was finally deciphered? Political maneuvering, fears of assassination, and a conspiracy to spread fake news to downplay a setback. Some things never change.
Font Fingerprint
There was a Reddit post over the break that caught our attention, where a user wired money online from his bank in England to Kenya, to pay for a trip. It was a legitimate transaction, but triggered the fraud protection from his bank. In the conversation with the fraud department, one of the flags for possible fraud surprised the Redditor in question: You have TeamViewer installed on your computer.
Now wait. That’s a bit disconcerting, a website can see your list of installed programs? No, not directly. There is no web API to list applications, at least, not since ActiveX died. However, there is an API to list installed fonts. And since Teamviewer brings its own font, it’s pretty easy to detect when it’s installed. And let’s face it, a remote controlled desktop is a reasonable flag for malicious activity. So now you know, your fonts may just be fingerprinting you.
Bits and Bytes
The Google Play store has ejected a pair of mildly popular apps, that were spying on users’ SMS messages. The data collection was incidental, and the real point was to enable fake accounts on various web services, using the victim’s cell phone numbers. Need a hundred Twitter accounts? Rent access to a hundred compromised phones, to use those numbers for the activation flow.
Need to get something past a plagiarism checker? Just rot13 and change the font! It’s a silly demonstration, but it does indeed work. Make your own font to change the letter mapping, and then apply the reverse mapping to the underlying text. To the human eye, it’s the same, but to an automated tool it’s garbage. Save as PDF, and off you go. While circumventing a plagiarism filter is a bad idea, this could have other, more positive uses, like censorship circumvention.
Black Hat 2022 videos are available, only three months later. There are some fun presentations in here, like the Starlink hack, analysis of real-world malware campaigns, and lots of software getting compromised. Enjoy!
















“Enter your email here to receive a password reset link.”
Wouldn’t the need for a hardware key stop that since even if someone has your e-mail account they’ll need the physical key to reset?
Sure. But users don’t use 2FA unless you force them to.
Sure, if that was an option for “most” services on the web. Yeah Microsoft, Google etc have it but plenty of local banks, insurers and medical sites either don’t have anything or only allow email / text identity verification. And some that do certainly don’t make it easy to activate, hiding it in layers of menus or requiring calling in to support to set up.
> Maybe in another decade or two, we can make a Freedom of Information Act request and finally get the full story.
Nine out of ten times it is always best to follow the money, who will profit most (and who has the most lobbyists). But in this case I suspect that it can be taken at face value, that no one is allowed to spy on US citizens. That is the NSA’s job, and google, and facebook, and amazon, and microsoft, and apple, and cisco and AT&T, and Bell, and the US banks, and power companies, and …..
Huawei or ZTE equipment – specializes in telecommunication
Dahua – manufactures video surveillance equipment
Hikvision – manufacturer and supplier of video surveillance equipment for civilian and military purposes
Hytera – manufacturer of radio transceivers and radio systems, supplier to China’s Ministry of Public Security
Well we could turn this one-eighty and ask if china has bans on US equipment in sensitive areas?
Most assuredly they do. Bad juju to have your classified stuff loaded on public hardware
They mostly use CPU’s based on a local variation of MIPS called Loongson.
I’m guessing it is mostly because it does not contain a ME or PSP core that only runs signed and encrypted code from Intel and AMD respectively.
https://libreboot.org/faq.html#intel
https://libreboot.org/faq.html#amd
But to be fair all you really need to do is have a fully airgapped system, and that can be clustered computers or a full isolated private network. Does not matter if the CPU’s are from China or the US, it is how most governments should be handling classified information.
Any good security installer will make video surveillance air-gapped even for private companies regardless of what brand equipment is used. It is not very difficult or expensive and prevents against many threats except infiltrated manufacturers.
The issue is not that “all governments do it”, the issue is that it’s an *unfriendly* government gaining the ability to do it in our critical infrastructure, doofus.
A number of EU countries have similar bans in place for similar stated reasons.
“Which countries banned Huawei?
Australia, Canada, New Zealand and Sweden have followed America in banning Huawei gear outright. New rules in Britain force carriers to remove all Huawei technology from public 5g systems by 2027. France has asked operators to rip out Huawei gear from many parts of their networks.”
Anecdotally, I’ve got a Huawei phone, and in learning how to unlock it I discovered that they require a 10 day period of usage and connectivity to link your account information, which is a little odd and I don’t believe is the common case. (Going off of other people complaining about how much quicker it is with other companies)
I’m not happy in direction where US gov. is headed with their bans on modern technology. In my opinion it only serves to keep other nations (incl. those in EU) behind in their development. Nothing but a legalized bullying. I work for Huawei office in Poland, I’ve been many times to China, even my gf is Chinese and I really don’t understand what’s the hate about them. I am embedded programmer so I seen first hand, it’s just telecommunication equipment, nothing evil there. When this health emergency passes, maybe next year I plan to emigrate to China because as engineer I don’t see future for myself or my children in EU.
I think the idea of kill-switches is more what people worry about rather than any information leaking back. Much easier to implement, and harder to detect. Want to invade an island country? Turn off everything first.
Ignorance is no excuse.
Pointing out civil rights violations is not “hate” Just because they are not happening right in front of your eyes, does not mean that they are not happening.
Nobody is perfect but everyone can do better. We only improve as a species when we introspect on our shortcomings.
…because…Communism.
Personally I think you have that more backwards its not much hurting the EU – USA isn’t ‘The Leader’ in many fields of electronics anyway, just one of them, and most of the EU has some great technical ability. So in many ways the USA lead tech and information war with China is actually just hurting the USA’s own business – why buy/sell and use stuff that is complex to get in or out of the US when you have so many other and potentially better options. Though with how belligerent China is acting and the power the folks at the top there have trusting anything from China in places that have any strategic or tactical risks associated, on that score I can agree – you don’t go to the neighborhood criminal for a door lock, its just inviting them to send their boys round to take everything… But if they want to sell you heaps of processed ‘raw’ materials or build toys for you cheap, not much harm can be done despite the lack of trust.
Even as an embedded programmer you can’t know anything about the gear being shipped – all you know is what its supposed to do, and that your work functions normally. Its not hard to piggyback dodgy logic, deliberate backdoors etc into the PCB or chips in a way you would never normally find in the course of doing your job. The folks building the secret dirty side may be sloppy enough to leave something YOU can find as you work there without huge effort but often even if you know its there it can be damn hard to find.
If it was easy to know what the silicon is really up to, and what all the code in use is doing nothing could be proprietary and the jail breaking of your game console to run Linux or your IOT smart home bollocks to run on your self hosted server wouldn’t even be news…
Ding-ding-ding, we found the PRC! No, but seriously- can we talk about how Russia’s just protecting the Ukrainian citizens, or how N. Korea’s nukes are only for defense (we promise)?
Russia is protecting Ukrainian citizens in the same manner that US was protecting Vietnamese, Iraqi, and Afghan citizens. End result somehow always ends the same, where protected are somehow much less in numbers…
Russians were just observing the US for the last 30 years. Even the rhetoric in their MSM is almost the same now. WMDs, humanitarian catastrophe of civilian population, evil dictator,…
N. Korean nukes protect them from US invasion. Libya, Iraq, Afghanistan, Yugoslavia didn’t have them.
First look in the mirror. US has been at war for 90% of it’s existence. And this was stated by Jimmy Carter.
The hate is not against the Chinese people. The US has more people of Chinese and Asian origin, myself included, than all of EU. The concern is against the authoritarians in power, and their co-opting of all technologies and techniques to oppress their own people and dominate the rest of the world in rather aggressive ways. The West had long (since Nixon) been trying to open up hi tech and direct investment to China (snd Russia) in hopes that they would become more democratic along with becoming more capitalistic. We have seen the results of that openness in recent years, and months. Those who have money or means in China and Russia are leaving by the droves. Some prefer the allure of authoritarian regimes. The western democratic model is messy but it has produced most of the capital and ideas that China has attempted to copy and monopolize. They don’t realize that the goose that lays the golden egg is free speech, civil liberties and participatory democracy. It is the rabble rousers in the west who created the IT sector as we know it. And please don’t pretend to understand all of the cyber security concerns that the west has with Chinese tech companies.
Unless you write all firmware yourselves in Poland without using precompiled binaries or source libraries supplied from China it is impossible to be 100% sure the device will be free from backdoors and kill-switches.
With Chinese hardware/firmware it doesn’t really matter how pure and trustworthy your software is, they can control the machine.
Try telling Uighurs in China that they “have a future” there. Also your kids will be reading books by Xi Jinping for studies. Literally. Oh, and say goodbye to the uncensored, free-information-filled internet.
I wonder if his GF is also a honey-pot.
I’m unconvinced by the smart watch attack. They claim “most” smart watches are vulnerable; what meaning of “most”? Most smart watches in usage? Or most cheap off-brand smartwatch designs found online?
I find it very hard to believe that you can spoof an SMS to an Apple Watch. Or a Samsung watch. Probably not a Fitbit. Apple alone is nearly 50% of the market.
This seems to be a lesson in buying decent stuff from reputable companies and not trusting cheap off-brand kit.
Android core security testing is not exactly comprehensive, some bugs are not caught by analysis tools, weaknesses are to be expected.
The only safe way to go is to assume that your devices are insecure and hackable. Bad security bugs are found on a regular basis in even the highest quality products, and there is no reason to think the parade of bugs will stop or even slow down.
Today we laugh out loud at how insecure our code used to be, just a couple of years ago. In the near future we we will be horrified at the current state of affairs.
With Bluetooth being what it is spoofing any device at all doesn’t seem implausible. Its down to the device to properly interrogate and so verify the source, and I highly doubt with how little care Apple has taken over security in oh so many ways over the years this is any different. The only things Apple have ever seemed to care about are building that wall around the garden higher and higher and making everything you own with an Apple badge on it so tightly intergrated to other Apple products its inconvient to use anything without that badge… Then once you buy in once they own you.
Though now the Apple watch come with eSIM do they not? Which means spoofing the cell tower to send the message rather than bluetooth…
Except it’s Samsung that is not to be trusted:
https://arstechnica.com/gadgets/2022/12/samsungs-android-app-signing-key-has-leaked-is-being-used-to-sign-malware/
I warned the Australian Signals Directorate, in a very specific way, about those cheap IP cams coming out of China all the way back on 20 Jul 2020. The meatbot who replied to me seemed to think I just wanted a recommendation for a camera that wasn’t compromised. Seriously, the government is not here to help, it is a parasite upon taxpayers. Given that the ASD is fully integrated into the Fives Eyes we can conclude that they are bloody useless, or that they have known for over two years that those cameras posed a very real threat. A cynic may conclude that they have used that time window to exploit the cameras themselves for whatever operational purpose thought justified doing so, meanwhile some mouth breather has been watching your kids. Or worse these cameras which are linux servers under the hood have been converted into staging points for DOS attacks and intrusion campaigns, not many limits as to what you can turn them to do for you one you own them and that is in some cases as easy as using an old NTP client exploit because many of those cameras have a hardwired NTP server setting that uses a PLA controlled time server in mainland China! Yep all that was spelled out to the ASD over two years ago, and only now the USA Gov wakes up and bans the worst offenders?
I was quite surprised by that Charles V encrypted letter.
Apparently it’s mostly a one to one substitution of letters but with a bit of non-lineairity thrown in such as simply omitting most instances of the “e”, adding a bit of garbage and a few other tricks.
I do wonder though how much effort has been spent on this in those 500 years. I guess it’s mostly been lying in some archive or museum without anybody even attempting a decryption.
It isn’t a very very long message, and I don’t know if there was any context to go with it. As without knowing something of what to expect in the first few words of the message even if it was long enough to easily decipher through frequency analysis alone it wouldn’t have been really practical to try for most of those 500 years. Otherwise there are enough tricks involved that you really have to process a large length of message and find sane results to know you have found the key, even when the key is so relatively simple – it would probably have become remotely practical to at least partially crack at some point only in the last 30 maybe 50 odd years as computers really come along. But before that even if you know it was a simple substitution cipher you really would need some context, an understanding of the history and spellings of the period and probably a few decades…
I expect you are right though, a message like that is not going to be readable at the time the information in it might be useful, and before computers would take a very very long time to crack without some help, so it probably has sat mostly forgotten for all those years.
That’s why Karol Wojtyła asked his husband that he fulfills Pope’s last wish – to burn all his private notes after he dies. That worked well for him, right?
Husband?
Good Grief!
It is indeed likely the case that most people just haven’t bothered trying to be fair.
Just like one basis for encryption being that “it only has to be strong enough to not be cracked within the time that the encrypted information is of importance/relevance.”
The same applies for trying to crack it in the first place.
The Dahua bit is interesting since they are the OEM for a number of other IP camera vendors. For example the very popular Amcrest. (Which run Linux but have no sources available, which is a GPL violation they didn’t respond to messages about, but that’s another matter) Probably they will also be affected, will have to see what they do in response.
There is some Huawei stuff I wish I could get, mainly VR/AR stuff, but some of their phones have really good high frame rate cameras…
The amount of “security” equipment which has Chinese hardware / firmware at its core is incredible, and it’s a shame it’s taken so long for folks to catch on that it’s maybe not a great idea.
And all the very large American and European brands that quietly diversified from Dahua and Hikvision to other OEM’s mainly from Taiwan. When you realise just how much/many of those companies are controlled from China, you understand this is all just about geography, politics and profit, and nothing to really do with security.
They were all happy to let the Chinese companies write their code for them and put nice logos on the products, and all they’ve done is move a few miles across the sea to a country which honestly isn’t China. Honest.
If they were serious about security they’d develop their own software, but that costs actual money so cant do that.
All the big western names have presence in China too. Do they treat all their employees as spys?
If there is really a problem, it’s not a couple of companies it’s the whole country.
But profit is more important than your perceived morality when your so called enemy contains 20% of the worlds population and has the biggest growth YoY.
“If they were serious about security they’d develop their own software, but that costs actual money so cant do that.”
Argument doesn’t fly far when it’s open-source they’re using.
All this storry is just maketing campaigne. Huawei have nothing about it.
If you don’t like Chinese products than trow away Iphones. But Wait, iphone factory in China is now closed. Maybe this grind your gears.
If Huawei spy me, I’ll let them die boring because i like my phone.
Some people in USA need tinfoil hat.