If you work at all with British software or hardware engineers, you’ll find that there’s an entire generation perhaps now somewhere between their mid-40s and mid-50s, who stand slightly apart from their peers in their background and experience. These were the lucky teenagers who benefited from the British government’s 1980s push to educate youngsters in computing, and who unlike those before or who followed, arrived at university engineering courses fresh from school fully conversant with every facet of a computer from the hardware upwards.
[Alan Pope] is from that generation, and he relates a tale from his youth that wasn’t so out of place back in those days, of how he wrote what we’d now call a simple virus for the BBC Micro. Better still, he’s re-created it.
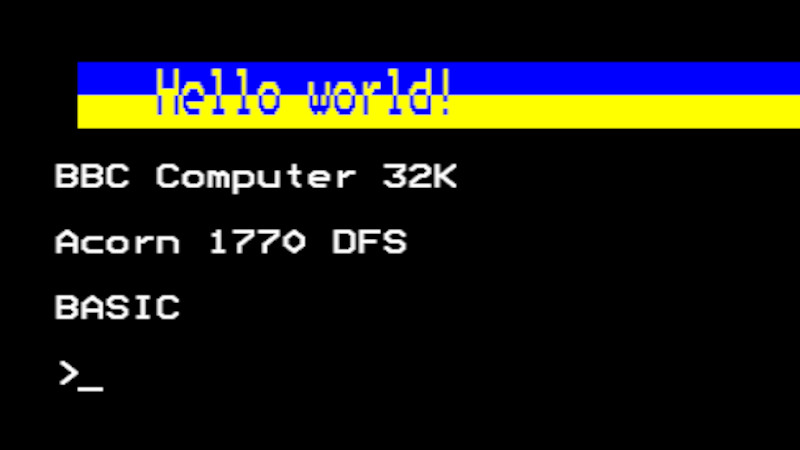
The post is as much a delightful trip back through that era of microcomputing, including an entertaining aside as he shared an airline journey with BBC Micro designer Chris Turner, and it serves as a reminder of how the BBC Micro’s disk operating system worked. There was a !boot file, which was what would be run from the disk at startup, and his bit of code would subvert that and hide itself in the machine’s so-called sideways RAM. The payload was pretty simple, every 32 soft reboots it would print a “Hello world” message, but it seems that was enough back in 1989 to get him into trouble. The 2023 equivalent works, but we’re guessing no teacher will come for him this time.
If you can’t find a real BBC Micro but still want one on hardware, we’ve brought you an FPGA version in the past.















Very cool! Wish there were a few more pictures in this article.
Lol
Amiga had this problem, virus would load and stay resident and do different things. And pc something similar..
Memories :-)
Cascade, Burger, Parity Check, Michelangelo, Brain, Jerusalem, Joshi, Herbstlaub..
Any PC user on DOS might has heard about at least one of them back in the day. ^^
Me and my friend done a similar thing of redirecting an interrupt (in 1990s). We done the dos int for the rtc timer to run some code and then go back go the usual interrupt by changin the address table. Done stuff like changing keyboard lights, making a beep etc. Not a virus but example of hooking a call 😀
Hi,
brings back memories from 90. we created a *.com that would store the next 255 keystrokes and call it’s *.exe brother. The teachers would log into their system, giving us their login and key. Of course they found messages from Meyer to Meyer: „change your password“… great fun! As well as flipping a DOS screen by software and finding the monitor upsidedown the next day:-P
Cheers to those low level hacks!
GvT
Not a virus but had a dos program that used a tsr to cause a reboot of the system anytime you wanted from point of execution to 4 hrs 15 minutes in advance. Caused a lot of unexplained reboots and lost assignments in high school. They never did figure it out. Even caused a rep from Novell to visit the school To a teenage nerd…lots of fun.
I created a very similar BBC micro ‘virus’ in the ’80s, purely as an academic exercise. Since news cycles would spin up over any computer virus report, drive fear mongering and hype, I wanted to see if it was really that hard to write a virus.
Mine virus would propagate via the !boot file, then hide out in RAM, if SRAM was available (not everybody had that) then hide out there. Since I was wanting the a “full” virus experience I did make it destructive – although never released it into the wild. After a certain number of infections it would wipe the disk.
While I had no intention of releasing it in the wild, it did get on some disks I didn’t intent it to get on, and that did cause a bit of havoc for me. Ultimately it managed to wipe a few disks, including the one with the “anti-virus” (if I could call it that – it just removed the virus from RAM/SRAM) and the one with the virus source code. The main issue was my SRAM was battery backed up, so power cycles would still leave the virus resident on my machine.
After that I was careful to wipe any infected !boot files and make sure I didn’t have the virus in memory…. I learned a lot that week.
I’m not best pleased with a discussion of BBC on a family site. I’ll be contacting management.
Why? Please explain. This is the BBC micro. The only BBC reference is the name. The hardware was by Acorn.
Well, Trenton is either a conservative MP who despises the BBC for telling citizens (mostly) the truth. Or they are really into porn to the point that they assume every reference they see is porn related…
Came across this virus in my final year at school, was rampant in the end across students 5.25 disks and even on the primitive networked harddrive the school had bought for our Beebs. A student wrote a routine that searched it out and removed it. He now works for the big boys in software programming.