[Daniel, Adi, and Eran], students researchers at Tel Aviv University and the Weizmann Institute of Science have successfully extracted 4096-bit RSA encryption keys using only the sound produced by the target computer. It may sound a bit like magic, but this is a real attack – although it’s practicality may be questionable. The group first described this attack vector at Eurocrypt 2004. The sound used to decode the encryption keys is produced not by the processor itself, but by the processor’s power supply, mainly the capacitors and coils. The target machine in this case runs a copy of GNU Privacy Guard (GnuPG).
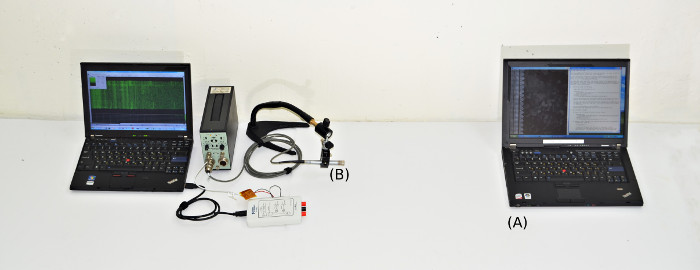
During most of their testing, the team used some very high-end audio equipment, including Brüel & Kjær laboratory grade microphones and a parabolic reflector. By directing the microphone at the processor air vents, they were able to extract enough sound to proceed with their attack. [Daniel, Adi, and Eran] started from the source of GnuPG. They worked from there all the way down to the individual opcodes running on the x86 processor in the target PC. As each opcode is run, a sound signature is produced. The signature changes slightly depending on the data the processor is operating on. By using this information, and some very detailed spectral analysis, the team was able to extract encryption keys. The complete technical details of the attack vector are available in their final paper (pdf link).
Once they had the basic methods down, [Daniel, Adi, and Eran] explored other attack vectors. They were able to extract data using ground fluctuations on the computers chassis. They even were able to use a cell phone to perform the audio attack. Due to the cell phone’s lower quality microphone, a much longer (on the order of several hours) time is needed to extract the necessary data.
Thankfully [Daniel, Adi, and Eran] are white hat hackers, and sent their data to the GnuPG team. Several countermeasures to this attack are already included in the current version of GnuPG.














What about the AC noise generated, could this leak information back into the grid?
Theoretically, yes, but because there are many other sources of noise in the grid (in home-automation systems, game consoles, TVs, other computers, not to mention other houses’ electronics and the noise already present in the line) it would be practically impossible to attack a computer this way.
There was an article a while back. I don’t remember if it was on HaD or elsewhere, but some people apparently were able to log keystrokes just by having a device plugged into the same circuit as the targeted computer.
Yep, over the power line. And as i remember this attack had a range of about a kilometre.
Read the article and the webpage listed. You can do the same thing by measuring ripple in the ground potential. They point out that most laptop power cables have high frequency chokes that kill off the frequencies this attack works at, so you would likely need to measure at a different point…for instance the ground shield of a USB cable.
There is one thing I don’t understand. Modern CPU’s are multicore and use multithreading. (not to mention multitasking OS).
How can one detect a valid sequence when all these activities are happening in parallel ?
Maybe because it’s the only thing which is happening?
If the other cores are doing exactly the same thing all the time, there is no interferance
Not to mention processing going on in the video card, network card etc. Also, how the hell does audio equipment pick up actions that are happening at GHz frequencies? I’m certainly not qualified to make such a call, but I smell bullshit. I’ll have to do more research on this later.
It doesn’t pick up activities at Ghz frequencies. Take a look at the website and paper, this is a legitimate thing. One of it’s authors, Adi Shamir, is one of the authors of the RSA (Rivest, Shamir, Adleman) algorithm.
Oh one of the guys that got 10 mil from the NSA for making their encryption algorithm subtly worse. That hit the news recently alongside this piece.
I think his credibility is rather questionable.
Will you read the fucking article? The RSA encryption algorithm has absolutely nothing to do with the weak random number generator that the NSA paid for. The RSA company was paid to use a weak RNG (DUAL_EC_DBRG) as the default in some of it’s products. It wasn’t paid to go back in time and weaken the public-key cryptosystem that shares the same name. I really doubt that Shamir had anything to do with use of the weak random number generator.
While your CPU runs at GHZ, there are still lower frequency patterns to code running cryptographic algorithms. I’ve personally seen evidence of power channels in the 100KHz range for a naive ECC point multiplicaiton algorithm running on a ~200Mhz PPC. Given that, it doesn’t surprise me that < 20KHz may have useful content as well.
To me, the only interesting aspect of this work is that what would have previously been "just a power channel" is also an acoustic channel. But after reading through the literature on DPA/SPA, not much surprises me about side channels these days.
FTA: “In a nutshell, the key extraction attack relies on crafting chosen ciphertexts that cause numerical cancellations deep inside GnuPG’s modular exponentiation algorithm. This causes the special value zero to appear frequently in the innermost loop of the algorithm, where it affects control flow. A single iteration of that loop is much too fast for direct acoustic observation, but the effect is repeated and amplified over many thousands of iterations, resulting in a gross leakage effect that is discernible in the acoustic spectrum over hundreds of milliseconds.”
They choose a ciphertext based on knowledge of the algorithm’s code. This allows them to essentially control the “modulation” of the power supply in a known way to recover the key at much lower bandwidth than individual CPU instructions. This is also how the “data” overcomes the noise generated by other computation elements (e.g. other cores, graphics, etc).
This kinda goes to show one of the disadvantages of open-source security software: it might have taken much longer if they had been trying to side-attack an encryption program in this particular way without knowledge of the exact encryption algorithm.
In a case like this someone could easily disassemble and re-construct the exact algorithm. It doesn’t get any additional security from not being open source.
The proprietary software would have had a backdoor to begin with, making your point invalid.
The world is full of unintentional RF detectors. mixers,direct conversion radio receivers, no it’s not inconceivable that the higher frequencies are being down converted by some means in some omputers. However if these is discovered occurring in a mix of random sample computers that would be interesting. I’m not an expert either bit I wouldn’t be surprise if it’s discover that down reconversion is found to be somewhat routine.
I’m curious about this as well. It seems like this might only work under very specific circumstances.
From the source: “Using multiple cores turns out to help the attack (by shifting down the signal frequencies).”
Could use fourier transforms to split the signal into its component pieces.
Wasn’t there a Phreaking “Colored” Box that could do this back in the 80’s? I recall a device that could listen to the EMF of a CRT monitor and recreate the display on a remote machine. I thought it was the Infinity Transmitter, but that’s something else. Anyone remember what this device was called?
You may be thinking about the “tempest” tests that the military an showing what could be picked up by pointing an antenna at the display – They could also detect what was prining on a dot matrix or sometmes a daisy wheel printer with this method. The firm I worked for back then passed the test, because we used a plasma display panel that updated all columns of the display at once, instead of the CRTs sequential scan of the display. We also did not need a ‘core clear’ [wipe] program, because our computer used dynamic RAM, that lost data when the power was turned off, instead of retaining it in core memory.
This is the so called ‘Van Eck Phreaking’ (see also TEMPEST). This delightful report from the BBC offers a rare demonstration http://www.youtube.com/watch?v=mcV6izFG3vQ but obviously the computers of the 1980’s we’re much more susceptible to this due to their CRT monitors.
Box of tricks.
the technique is called [Van Eck phreaking](http://en.wikipedia.org/wiki/Van_Eck_phreaking). Project TEMPEST was the military’s response which developed a standard for EM shielding to mitigate side-band attacks.
I have the solution: http://www.instructables.com/id/Laptop-Compubody-Sock/
…but yeah, even if you could pull data off, you’ve got a LOT of stuff to sort through to find an encryption key. It isn’t even a simple operation when you have a memory dump on hand.
In case you wonder. Adi Shamir is not your random “white hat hacker”, he is one of the co-inventor of RSA.
this was presented and posted here a few years ago during one of the black hat conferences. Good to see it being developed and publicized more.
The late Carl Sagan:
Extraordinary claims require extraordinary proof.
I’m looking forward to a public demo on 30C3, DEFCON or SIGINT.
Unless that happens, I’ll happily ignore vibrating smd capacitors giving away encryption keys…
Adi Shamir is one of the inventors of RSA, along with Rivest and Adleman
I totally agree that some demonstration is in order. This doesn’t pass the smell test. I’m guessing that if this actually does work, it requires a very specific computer running a very specific OS and very specific software with a very specific cyphertext to be decrypted. And it won’t work at all in the general case/real world. Just think about it, any other noise, any threading in the process or OS will blow away any info it could possibly get. And yes, I read the article.
Yet you missed that GPG has been patched….
“a very specific computer running a very specific OS and very specific software”
if it’s a directed target at a particular person then you will have this information anyway
“any other noise”
if the attackers have physical access to the location they can plant microphones with care and get excellent data to work with.
“any threading in the process or OS”
if you can hijack the scheduler in the target system (a flash program might do it) you can get it run the code on one core. If you have physical access to the location you can hook into the wifi and inject your flash program into their web streaming. Of course this can be mitigated if the target is running http everywhere.
If you have control over the physical environment and you are directing an attack at a particular individual then attacks like this become a lot more practical.
Well, IF (and thats a big IF) you have all that info on the target’s computer and you can hack their wifi, plant microphones and hijack the scheduler and run arbitrary code on it, why do you need to crack their crypto key again? Seems to me, if you have that much access to their system, then there are easier ways to go about getting the info that you want.
So GPG has been patched? Those guys are paranoid and will put out a patch for any vulnerability, perceived or real. This falls clearly in the former.
I’ve got no disagreement with your comment about the encryption keys, and my comment is admittedly off topic, but your Sagan quote struck me as interesting. I’d not seen it before.
So Sagan thought that “…extraordinary claims require extraordinary proof?” That seems in direct contradiction to his (and Drake’s) promotion of the idea that the earth is a mediocre place, nothing special, and that the universe is “teaming with life…”
Maybe it is, but Sagan never presented any “extraordinary” proof of his claim. In fact, he’s been dead nearly two decades (SETI-like experiments, by the way, have been going on since the 60’s) and yet there still is no proof of the idea whatsoever– Certainly not for the lack of trying.
So I wonder, to whom was Sagan’s comments directed and what was he demanding proof of? Moreover, why did he think that the bar he set for the claims of others did not apply to his own?
It’s again one of those internet misquotes.
The original wording is “Extraordinary claims require extraordinary evidence” which is not the same thing as “proof”. I.e. it simply means that if you make weird claims, simple handwaving won’t convince anybody.
So he said tomato instead of to-mah-to? It doesn’t change my fundamental point.
Sagan expected a standard of “evidence” for other people’s claims that he conveniently neglected to apply to his own.
That is why he was trying to gather evidence – to support his claims. To me, that is upholding his ideals.
I don’t think he ever claimed to have proof of extraterrestrial life. He was pretty sure, but that’s nothing at all like proof scientifically. He might’ve been a bit of a dreamer but he wasn’t stupid.
http://www.cs.tau.ac.il/~tromer/acoustic/ec04rump/
This is an archived copy of the web page accompanying the Eurocrypt 2004 rump session presentation, originally placed at http://www.wisdom.weizmann.ac.il/~tromer/acoustic.
For further details on those results, see Eran Tromer’s PhD thesis.
Newer results are now available at http://cs.tau.ac.il/~tromer/acoustic.
they said as the power supply struggles to power the system.
wouldnt a higher power power supply foil the attack as the parts will not be having to work as much?
also this means you have to be very close to the target system and at witch point you could see that they are trying something
Not really, the power has to come from somewhere. When the CPU cores
draws on more power, the PWM controller have to change the duty cycle to
deliver that power regardless of its size or rating.
A huge linear shunt regulator instead of a switcher would draw power
when the load isn’t. On the other hand, it is not practical as a CPU
supply – high power and bad efficient.
If this turns out to be valid, then I guess all those Tempest folks I scoffed at in the 80s were not all that paranoid.
My college thesis was a tempest reciever. I demoed it to the professor who turned white as a ghost as I was able to show him the screen of several computers by simply pointing my antenna at another direction. It’s easy as hell to make, granted they dont work now because nobody has a CRT monitor…
they dont work now because nobody has a CRT monitor…
No need for CRTs, we hooked everything up to the internet now.
I’m calling bullshit on this one. While it *might* be possible to distinguish between several pre-calibrated keys, it’s downright impossible to extract arbitrary 4096 bit key via a cellphone placed next to the computer, as stated by the paper.
a) As mentioned in another comment, CPUs are multi-core and process many task at the same same time, creating interfering noise patterns.
b) OS schedulers can and will dynamically relocate CPU time to other threads.
c) CPUs operate at several GHz, dynamically changing frequency as they see fit. No only does this affect the produced noise, but those are also much higher frequencies than any type of audio equipment could pick up.
d) Compact power supplies, like those found in modern laptops, operate at frequencies far out of the range of a cellphone microphone and likely out of range for high-end equipment. Typical frequencies range from 50kHz to 5MHz.
Instead of calling bullshit, which is so easy nowadays on the Interwebz, why not publish a paper? (Which is also very easy nowadays). But before you do, maybe read up first a bit on who Adi Shamir is…
GPG has been patched already, see my post below, so the devs didn’t think it was bullshit.
Read the paper. Really.
To be fair, the details aren’t as fantastickal as a lot of the press has claimed. He claims it’s possible, over a fair amount of time, if you’re free to send manymany specifically coded ciphertexts to the target computer, which the target computer is guaranteed to decrypt. The content of subsequent ciphertexts relies on the received results from the previous ones.
And it’s already been fixed. I paraphrase cos I’m not an expert, but basically you multiply in a random number at some stage in the calculation, then divide it back out again later. This defeats the attack.
And even then the attack’s pretty baroque, and relies on a fair amount of access. Stuff like this always gets hype. I dunno if Shamir’s fishing for contracts right about now.
“students at Tel Aviv University”
Pretty sure Adi’s not a student. Unless he felt he needed to go back after inventing RSA…
Patched 2 days ago:
Along with the publication of an interesting new side channel attack by
Daniel Genkin, Adi Shamir, and Eran Tromer we announce the availability
of a new stable GnuPG release to relieve this bug: Version 1.4.16.
This is a *security fix* release and all users of GnuPG versions 1.x are
advised to updated to this version. GnuPG versions 2.x are not
affected.
http://lists.gnupg.org/pipermail/gnupg-announce/2013q4/000337.html
What about simply adding white noise to muddy the signal?
It has already been patched, see my comment above.
you really have no idea about anything, do you
Right? XD
So this means now we need to tinfoil our laptops, foam-pad our vents, noise-scramble all radiation, change password every few minutes, run opcode-canceling infinite loops, and search our homes for drone-bugs?
Your average computer etc have some manner of shielding to pass “FCC Class B”.
The shielding material need to be a few times the skin depth at the frequency of interest. I’ll leave that as an exercise for the students.
Since this leak is at audio frequency, it means that your average “tin foil” is ineffective.
Has anyone actually read the paper before criticising? Although not an especially practical real world attack due to the limited range (up to 4 metres with a parabolic dish) and the time required it’s certainly not ‘pie in the sky’ and the authors go to great lengths to explain how this works. While not as exciting as Van Eck / TEMPEST style attacks it’s still enough of a concern for the gnupg authors to add blinding to the version that the authors exploited (http://git.gnupg.org/cgi-bin/gitweb.cgi?p=gnupg.git;a=commit;h=93a96e3c0c33370248f6570d8285c4e811d305d4)
Here comes the day where just merely setting your laptop on a well structured table makes it vulnerable to attacks.
I think this type of attack is well suited to someplace like a coffeehouse or an airport lounge because the potential hackers can plant microphones and other sensors.
Sure the microphones will pick up noise, but they could also have a sensor on the power line and a light sensor watching any fluctuations in your computer’s backlight brightness. They might even put an RFI sensor in the tabletop.
They can also break into the wifi that the customers are using. This gives the attackers an opportunity to run flash code on the customer’s systems.
Between these two things I think it might be possible to coax secrets out of, or malicious code into, people’s computers, not just in this particular case of PGP but also in other scenarios like web browsing.
Might seem outlandish and a lot of trouble but for a high value target it just might be worth it. The moral is, don’t do high-value encryption on an unshielded computer (where the definition of “unshielded” might change over time).
Try this one, record the audio of typing on the exact same make and model of keyboard as your target, ideally, get into the target’s office/home and do the calibration on that keyboard. Plant your mics or get a recording app on the target’s smartphone.
Then decode the audio output of the keyboard to dig out the slight variances in sound made by each key, which should vary even more on a well used keyboard due to the difference in use among the keys.
Just an idea but would certainly be much easier than winkling out data from high frequency, very low amplitude audio harmonics generated by electrical impulses in the computer hardware.
I remember in the 90’s, when 100 megahertz was screaming fast, typing and mouse movements causing noise in the audio output of some of my PCs. Could be that there were slight variances in that noise which could be used to decode what was being typed.
Since it’s not April 1st and it came from Israel, I have to say, “Who would have figured you could do that?”
This is pretty easy to believe, since I’m one of the few people who can actually hear the sound of the (cheaper) power supplies varying in response to the load.
Patent Services: Let our California patent attorneys that are seasoned allow
you to file your patent applications prior to the USPTO..
Judgment: A judgment could be order or the final court decree distributed by the judge according to all the facts and research introduced from
the events. Forby|One of many legislators who inquired the opinion that was appropriate, democratic Gary Forby|Democratic unresponsive and died|performers Bobby Brown and died and Whitney
Houston, who was likewise found unresponsive|Houston and singers Brown, who was also discovered
Direct Tax: A tax that is assessed on a taxpayer who is intended to suffer the last stress of
paying tax.