Tektronix’s MSO2000 line of oscilloscopes are great tools, and with the addition of a few ‘application modules’, can do some pretty interesting tasks: decoding serial protocols, embedded protocols like I2C and SPI, and automotive protocols like CAN and LIN. While testing out his MSO2012B, [jm] really liked the (limited time) demo of the I2C decoder, but figured it wasn’t worth the $500 price the application module sells for. No matter, because it’s just some data on a cheap 24c08 EEPROM, and with a little bit of PCB design <<removed because of DMCA takedown>>
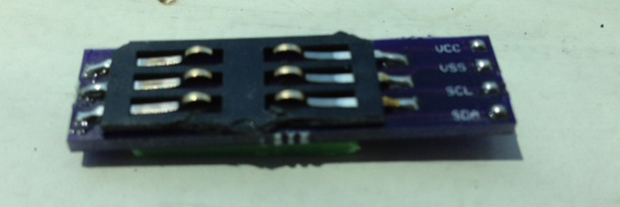
The application module Tektronix are selling is simply just a small EEPROM loaded up with an <<removed because of DMCA takedown>>. By writing this value to a $0.25 EEPROM, [jm] can enable two applications. The only problem was getting his scope to read the EEPROM: a problem easily solved with a custom board.
The board [jm] designed <<removed because of DMCA takedown>>, with the only additional components needed being an EEPROM, a set of contacts for reading a SIM card, and a little bit of plastic glued onto the back of the board for proper spacing.
UPDATE: Learn about the DMCA Takedown Notice that prompted this post to be altered: http://hackaday.com/2014/08/05/hardware-security-and-a-dmca-takedown-notice/














How is doing this not theft….I’m just curious… ?
Theft is the taking of another person’s property without that person’s permission or consent with the intent to deprive the rightful owner of it. It’s certainly a grey area, but not theft.
It depends on what licensing terms you have. Workaround for restricted software that came without licensing terms, but requires a valid key, not entitled to you, is generally considered stealing.
e.g. buying a Chinese copy of Windows install disc and cracking it.
It might “generally be considered stealing” but there are lots of wrong things generally believed by ignorant people. Theft has a specific meaning, which Wah Hammer listed above. Defending a correct use of terminology is not the same as defending an action. If I write an article making false and injurious statements about someone, I’ve committed libel. If I say the same thing in a speech, I’ve committed slander. The two terms are commonly confused and used incorrectly. That doesn’t change the fact that they are distinct. There is a correct way to use them, and correcting someone’s misues of the term doesn’t mean that the action is moral or permissible. Copyright infringement and actions like this are not theft, even if they are legally and/or morally wrong.
I would say that this is incorrect. You BOUGHT the hardware. It is YOUR hardware, including the bits inside with the software you are not “licensed for”. I would argue you have every right, as the OWNER of the hardware to modify it in any way you desire, including changing that internal code on YOUR DEVICE.
No theft at all. If companies want to make different products, they can. If they want to package it all together, they should not be shocked when people modify a crippled one to enable all features it is already capable of.
Sadly, this isn’t exactly correct. For example, you OWN the iPhone. You are free to throw it in a lake, dissect it and reverse engineer the hardware, to run your own software on it, or to use it as a cutting board in your kitchen if you so choose. HOWEVER, you are merely LICENSED to use the software, a license which may be revoked if you violate the terms. You could, conceivably, be legally reduced to owning an iPhone useful ONLY as a cutting board. The same applies here.
Of course, the design decision here deserves consideration: A company (Tek) has little to nothing to gain suing an individual hobbyist end-user, and that hobbyist also doesn’t represent a major profit center for them. On the other hand, a major corporation has lots of resources to lose in a software piracy suit, and also lots of resources potentially direct-able towards buying Tek application modules.
I think the major idea behind avoiding Tek application module contents being easily located on the internet (thus enabling easy module cloning) is that, if it becomes so easy EVERYONE can do it, SOME companies (really, individuals therein) will get the idea and pursue that path, and finding those cases to pursue is much harder than actually pursuing them.
This is the perfect statement, this BS would be like Nissan going after people for adding a Turbo to the NA 300zx just because the Turbo 300zx existed. Just because its “Digital” does not make it special and ignorant people making the rules will never win, there will always be people with less money than brains. I can and will do whatever I want with the things I purchase, even with your silly use rules in the box.
Wah Hammer, so if you write software and use it to provide services to people and I get a copy and can provide those same services for free, that’s a gray area and not theft?
it’s the fact these things use fermware that denotes the grey side of things.
Orginal perchiser agrees to terms second sail gets item and isn’t requierd to agree at start …
and just using something cant be a contract the license has to be presented each time.
it would be like charging for using cheatcodes in games. after the fact.
if they dont want that functinality accsess they need to 1 not include the hardware. and two not include the software in the base install.
Otherwise wheres the value for the new functionality.
@John
There are more categories of behavior than “theft” and “totally ok legally and morally, go hogwild.” Copyright infringement isn’t theft. Public urination, rape, genocide, and vandalism aren’t theft. That doesn’t make any of those things ok.
On the flipside, it was at one time legal to own human beings. Being legal did not make it right. At one time it was illegal for a person of color to enter a building with a “no coloreds” sign. Being illegal did not make it wrong.
I think you know all this. You’re clearly trying to make a statement of moral equivalency. The conversation would be a lot more productive if you actually made an argument rather than obliquely stating its conclusion.
Correct. That would be breaching the terms of a licence and it would be up to the licensor to litigate against you in a civil court for breach of contract and loss of earnings rather than for the authorities to pursue a criminal action against you in a criminal court. Breach of contract is a ‘tort’ which is unlawful, theft is a ‘crime’ which is illegal. Morally it’s a grey area but ‘legally’, no that is not theft.
It is exactly theft.
Oh come on – at worst it’s copyright infringement (for duplicating the <DMCA REDACTED> stored in the EEPROM).
You mean theft by Tektronix for charging $500 to de-cripple features that are already present?
If the “license keys” (<DMCA REDACTED>) are freely available on their website, than I don’t see how this is theft.
Are there prices on the Tek website (or in their quotes) attached to those <DMCA REDACTED>? Theft.
Thought experiment: You have bought a basic car, steel wheels, etc. You can buy an ‘upgraded’ version with alloy wheels for $3000 more. Instead, after a couple of months you decide you’d have preferred the alloys and buy some perfectly original looking ones at a local retailer, for the great sum of $500. Did you steal $2500 from the original dealer?
On one hand I can understand the desire of the OEM to offer a range of products for the development costs of just one. On the other hand: They did make it easy for those willing to do the work.
I think it is more like this:
You buy a new car, and to save money, you opt for the ‘no thrills’ package. No radio. No electric windows. No heated seats.
Upon receiving the car, you discover that the manufacturer did in fact install the radio. Did in fact install the electric windows. And did install the seat heaters.
However, none of them work. Upon further investigation you discover that to have the items enabled, you must pay the difference in price. But, you poke around and discover that in the fuse box (which required a special screw driver to open), three slots are empty: Radio, Windows, Seats.
You pop fuses into each slot and everything comes alive.
Was this theft, or did the factory simply give you the stuff at no cost, and hope you would pay them more money when you decided you wanted the options enabled after all?
If you download the trial version of a piece of software you might also have to pay $500 to “de-cripple” features that are already present in the version you’ve got.
If you download a crack for it to unlock those features because the company didn’t make it difficult enough for people to get around their protection, that still doesn’t make it right.
I imagine Tektronix just rely on the fact that a lot of people that buy their expensive kit will be businesses and businesses generally have to do things by the book, so they won’t bother unlocking things they haven’t paid for, in the same way Adobe relies on business users to buy Photoshop and mostly overlooks all the home users not paying for it.
Adobe definitely ignores the home users, says a home user who DID pay for Photoshop but can no longer use it because of Adobe’s idiotic DRM.
Good thing there’s Gimp.
Adobe is a really bad example, they were one of the first large company in the price-war on piracy, claiming they were losing huge amounts of money by counting the number of illegal copies and multiplying by the sale price.
They failed to mention any consideration of the fact that very few of the people who copied the software would have actually paid for it if it wasn’t available for free, they would have probably just used Gimp or MSPaint.
I’m not sure what it is. But it’s not theft. It’s also not copyright infringement. As he did not copy anything. Except for a public available number into an EEPROM.
The software was already available in his device. He just enabled it, no downloading©ing involved.
Most likely, it’s breaking a user-license agreement somewhere. But, as those are shrink warped with the product, they are no real legal value.
I’d say copyright infringement indeed, as he basically cloned a production by the original company. The next question would be: Can a non-profit publication of a reverse engineered add-on be considered fair use? I’d say not, after a quick look at the criteria.
The interesting thing is: They could benefit from a large following of people looking for a special deal (I do think the modability of the Rigol scopes brought them fans who would never have bought the real higher end model anyways)… Or they can come down hard on this and make a clear statement to their paying customers: We won’t let you mod your products. Which could lead to higher sales in their high end range. A dilemma, me thinks.
Minus the ‘indeed’, you can argue he just assembled things, but he did end up with a product which is feature-wise indistinguishable from the original.
Cloning something not copyrightable results in not infringing copyrights … his application module is sufficiently different to not infringe copyrights IMO and the number in it isn’t copyrightable in the first place.
If the scope loads the firmware from FLASH to RAM what he does could be termed circumvention of copy protection though. If it runs the code directly from FLASH even that won’t work, if there is no copying then the application module has nothing to do with copy protection.
So, what if they sent in the box a battery pack to enable the scope to be mobile. BUT since you did not pay for the option, you are not permitted by your user agreement to install the battery? You can only do so after paying the fee to receive installation instructions.
If software people want to insist that software be treated the same as hardware (as in, if you buy one copy you are only allowed to posses one copy… etc) then they have to start playing by the rules of physical items. That is, don’t ship something in the box that the user did not pay for.
Yes there is the ‘ethical’ question of is this hack legal or not, but at the end of the day it does not matter. The vendor shipped him the product. He did not steal the software. It was already installed.
The correct business decision would have been to put the additional software on the upgrade device they sell. “Hey if you want the upgrade, buy this module. Which is not simply a key, but the actual upgrade software you are purchasing.”
Now then if he ripped into THAT device and copied the software, with the intent to upgrade ANOTHER scope, then yes, I would call THAT action theft.
I think you can look at this in two ways, feature wise (as I did in my previous analogies): You buy a product as an item with a set of features, so trying to obtain features you didn’t pay for can be considered immoral and (possibly) illegal. You can also see it as buying a piece of hard-/software, which is yours to use as you please. In this case it could be argued that, within reason, any way to improve on the functionality is both moral and legal.
It is exactly NOT theft as the original owner has not been maliciously and permanently deprived of the ownership of the original item; it is a tort by way of breach of contract (i.e. the licence agreement) and the original owner has recourse through the courts for loss of earnings. Doesn’t mean it’s right but it does mean it isn’t a criminal matter i.e. theft.
There needs to a FAQ for this, or an Eternally Had Problem.
We do the “morality” of getting extra features out of products that are crippled for money, every time somebody cracks one.
The story itself is worth running since it’s a new hack that people might benefit from. The “rights” / “wrongs” really aren’t. We do the same thing every time, nobody changes their mind, and we very seldom learn anything from each other. The facts, points, and principles of this need laying out in a FAQ somewhere, taking both / all points of view on board while endorsing none of them.
On a wider scale this is the same argument as piracy, is it wrong to get stuff without paying for it, if you’re costing the producer nothing?
Eventually, if it becomes a costly enough problem, then manufacturers might have to do things the hard way, and ship actual hardware on modules rather than just activation keys. This will cost everybody more, and be less efficient, and indeed certain delicate signals won’t do well running through plug-ins and busses. But if it returns more money than hassle, it will happen. If.
Might not be that much of a worry, could be that most people who hack their stuff like this had no intention or capability of paying for it otherwise, so they’d just do without. Business customers are less likely to pull tricks like this than home ones are. In a business equipment costs are usually spending someone else’s money, and contracts and laws are more likely to actually take notice of you.
Simply enabling the software features using device-unique activation keys (such as is already done when enabling full features for a 30 day trial software) might be enough to make this legally copyright infringement.
In this case the manufacturer has probably avoided this solution for some reason, either the logistics is too much hassle, or they want the hardware adapter to be usable with several scopes, either way they have most certainly seen the possibility that people might make their own adapter but decided it’s not a big enough problem.
Why is “theft” bad? Is it the taking of the property, or the depriving its owner of their use of it, that makes it harmful? Is it because daddy said so and daddy spanks?
I firmly believe that the very *concept* of intellectual property is a world-scale *theft* from the intellectual commons. Copyright, patents and trade secrets are properly held to be rights to exclude; property is a separate right of exclusion altogether and to conflate the two only serves rentiers. I can’t possibly agree that executing code placed in the box by the manufacturer is theft. If it’s in the box, it’s mine to do with as I will.
It takes a very sick person to agree to not live in any way for which they haven’t purchased a permission slip, but that’s where society is heading.
“If nature has made any one thing less susceptible than all others of exclusive property, it is the action of the thinking power called an idea, which an individual may exclusively possess as long as he keeps it to himself; but the moment it is divulged, it forces itself into the possession of every one, and the receiver cannot dispossess himself of it. Its peculiar character, too, is that no one possesses the less, because every other possesses the whole of it. He who receives an idea from me, receives instruction himself without lessening mine; as he who lights his taper at mine, receives light without darkening me.”
If I steal your house, you no longer have it. If I steal your car, you no longer have it. If I steal you girlfriend, you no longer have her. Theft or stealing can only be on physical objects, items, etc. What you probably referring to, but have been brainwashed to think is theft, is profit cutting. This is the equivalent of being in business for the same purpose, yet when the other business is about to make a sale you swoop in and make the sale instead. You stole nothing from anyone, as no one lost anything, albeit its ruthless, but its not stealing. Its pretty simple logic really, you have to own something first before someone can take it away from you. And in this instance, Tektronix can’t own your ability to change the device, nor the action of, what Tektronix is doing is called controlling, which really just shows what the business model is. There are two types of capitalists, moral ones, and greedy ones. A moral capitalist gains, and “earns” money by production 99% of the time being thankful they can provide, and greedy capitalists control and extort money by selling, 99% of the time believe they “deserve” it. In the end its pretty much the difference between an entrepreneur and crony corporatist. An entrepreneur has a dream, a vision, or an idea that he/she only cares about and money is how they get there, and a crony corporatist only cares about the bottom dollar, and the dream is wealth, power, and money, nothing else matters. Welcome to the real world
Because its not theft? Chosing not to buy a product and instead making your own isn’t theft, its just good thinking.
Theft, How? all computers by that logic are stolen. you a thief>?
Most funny thing about it you can do it from the scratch – just need publicly provided <DMCA REDACTED> – or is that copyrighted as well?. I wonder then if by creating article itself is the author breaking some law? (like in case of nmap http://nmap.org/book/legal-issues.html).
Using it in Poland would be considered as “computer protection avoidance” -> law broken. This law is normally applied for cases like website hacking & data thief – and “protection” could mean something like that URL was not publicly known (ex. accessing mycompany.server/ultraSecretData.zip could get you some jail time if you just guessed it and weren’t authorised to access it).
As always sorry for bad english;)
that sounds like a horribly misguided and utterly stupid law. you should get everyone in your country interested in “war URLing” to build a database of unsecured URLs.
Got Weev a few years for the same thing, and he was only trying to help people, pointing out and making public a massive, lazy, stupid security hole. His “hack” was something a bright 11-year-old could’ve thought of, but then he wasn’t trying to hack in the first place, and the method he used was obvious by implication to anyone who paid attention to the URLs the site was serving.
That’s in the USA, btw. Stupid primitive country, run by and for the benefit of a few oligarchs.
Something like that happened in Sweden, a reporter was sued for hacking after he went to a company’s site couple of days before the release of the yearly economic report and read last year’s, and after that just by luck he tried changing the year in the URL which was something like “http://www.company.com/files/yearlyresults2010.pdf”. He got the unreleased document and wrote an article about it since he deemed it publicly available and therefore fair to use as basis for his article.
As far as i can remember the case was later dropped, or the reporter won. But people were a little scared what a case like that could mean if the company had won. No more iterating URLs automatically etc.
Interesting thoughts. How is this any different than unlocking a Rigol scope?http://hackaday.com/2013/07/02/unlocking-a-rigol-scope-once-again/
With the Rigol you’re sending unlock codes over the USB port. With the Tektronics you are just providing a <DMCA REDACTED> from an external memory. That seems less intrusive to me.
He’s going to get sued for sure.
Tek wants compensation per user to offset significant development cost of the feature. Someone gets the feature without paying Tek anything. Theft.
However I get bent out of shape over companies that hide behind laws (DMCA most famously) to protect their investment without doing due diligence themselves. If I leave every door and window of my house wide open and vacant for a week, it’s hard to complain about people cleaning out my house. They should have built more intelligence into the insert if they didn’t want this to happen. But even if you don’t properly secure, it’s still technically theft.
Tek wants compensation per user to offset outrageous significant executive salaries. Someone gets the feature without paying Tek anything. Theft.
FTFY
How much your imaginary idiot is paid is irrelevant.
The act of unlocking this is still not theft. Distributing tools to help others do it however, may fall under different regulations. Here’s a thought exercise that aligns better than the one above:
Say you buy a house. You own the house, the land it sits on, the mineral rights, air rights, whatever. But one day you discover behind the washing machine a door with a lock. You call the previous owner and they tell you that for $500 they will sell you a key to that door. You would not be a criminal for making your own key or picking the lock because you OWN the door and anything behind it because you bought the house around it.
This is the same thing. He bought a scope that already had code in it. All he did was unlock part of what was already his by virtue of purchase and possession. Argue all you want, try to apply law all you want.. You might even find one that fits and that you could convince a judge and jury applies, but MORALLY he has done nothing wrong in accessing a portion of a product that he owns.
If companies don’t want people to do this, they should stop including hidden code in their product. If you had to actually install the features from separate code after the purchase, this would be a completely different discussion.
Again, distribution and disclosure might be a different story…not here to argue that.
Tell that to DirecTV or the cable companies.
Theft of service is defined in the criminal code, and is spelled out in very strict legalese. In the jurisdictions I know, this action would not constitute “theft of service” and that makes your analogy invalid.
theft of service also covers computer software/service, which this is.
Agree; this is not theft of service. At worst this is a breach of the EULA…the software was put on his device by the manufacturer intentionally. He did nothing deceptive to obtain it.
“A person commits theft of services if the person obtains services, known by that person to be available only for compensation, by deception, force, threat, or other means to avoid payment for the services; having control over the disposition of services of others to which the person is not entitled, the person knowingly diverts those services to the person’s own benefit or to the benefit of another not entitled to them”
Which is grand, apart from the fact he hasn’t obtained a service.
@Morgen – a very nice logical and convincing argument – too bad Laws aren’t logical and don’t follow common sense. Using your logic, since I own my house, the yard, and all around it – if I have the smarts to decode the DirectTV signal that is washing over my property without my permission, I should be able to enjoy the fruits of my clever work without worry (or payment) – wrong – that’s been all the way up the courts food chain and it’s THEFT.
DirectTV is in a different vein than this. If you buy a house you do not own the airwaves (at least in the U.S.) and the signals awashing your property. This is a small, but important and annoying detail, that a lot of people tend to overlook.
Oracle distributes a server binary that has all features enabled. They say: if you use feature X, you have to pay Y. This makes it easy for users to “upgrade”. Just enable feature X pay the fee done! This is important for them: an “enable a feature” should not require a reinstall of their software, which risks throwing the whole system down.
Similarly, TEK shipped the software for the features, and licences you to use said software by giving you an eeprom on a module.
Now this whole thing is not new. I’ve known for years that those TEKs had a simple eeprom that enables the features using a plain-text string. I’ve never used one of those, so I didn’t figure it out myself.
Well.. and then consider who their customers are… I mean.. Its like selling a 12 pack of sausages for the price of 10 sausages, to people on their way to a BBQ and then telling them “you can eat all 10 sausages. But you MUST NOT eat these last 2.”
I applaud this hack because I’m personally getting very tired of how expensive test gear is. Yes, someone needs to get paid, I understand that. Looking at it from a “maker”/”open hardware” perspective, though, it would be really helpful for people to have the ability to test and verify their designs without having to fork over thousands of dollars just to rent a VNA or TDR or some other specialized test gear. This would accelerate the “maker” movement into more a “legit” and high-tech territory and less of a “these maker people just make silly blinking LED toys”. Yes, I’m rambling incoherently now. Monday morning coffee has not kicked in yet. Thanks for reading my drivel!
Glad you admit that your ramblings are indeed “drivel”.
If you’re so “tired of how expensive test gear” is, then no one is preventing you from making your own. Oh what’s that ? That requires R&D, engineers (who want to be paid), a lab (with more of that “expensive test gear”), a place to work (rent, utility bills, taxes), and let’s not forget the RISK of not having made a profit and losing all your money.
Put all this together, exactly how is your new business going to produce a laboratory grade test instrument for the meager price of say, $29.99
The ‘open source’ numbnuts on here are clueless to the “real world” of engineering
where a business is in – BUSINESS – to make a profit and put bread on the table for it’s employees and shareholders. Without which there is no progress. These so called “makers” – are using chips that took billions of dollars of CORPORATE investment to develop. You think a fab facility is built in a lame ‘hacker space’ ?
Reminds me of the loons from “occupy” , who were vandalizing their own bank where they kept their money.
Damn, guess I got you heated, son! I’m fully aware of the points you make, about risks and investments, R&D, paying engineers. I never said lab grade test equipment should sell for $29.99. I also don’t think that hackerspace has the ability to produce chips like an actual chip foundry does. You kinda twisted what I said into some crazy “Everyone should have everything for free!!!111 I’m a huge moron!!!11” diatribe, which is not what I meant at all. (Bonus internet points for capitalizing words as if you are yelling at me, kudos.)
What I am saying, though, is that it would be interesting and beneficial to all in the industry (pro & amateur), if we could make access to test gear more ubiquitous.
I think the “Maker Movement” right now has some merits, but it lacks some forms of credibility in my eyes. It’s pretty great someone in a basement with a copy of KiCAD can create some hardware accessory and sell it on Tindie. I think what is missing though, is the “engineering” aspect – what are your specs and do you meet them?
I have thought about developing a VNA specifically for characterizing power supply decoupling capability. If something like this could be sold for a couple thousand (vs $60k+ for a full fledged VNA with all sorts of features and junk), and still perform well enough, it could be a useful tool to some small hardware startup or something? Just an idea, have not researched it heavily and this is just a comment on a blog post, not a business plan or full dissertation, lolz.
Again, just some thoughts. Maybe you can grok what I’m getting at, maybe not.
I think GordonGekko could just copy paste his reply again.
It would be really nice and interesting if we could make chauffeurs more ubiquitous too. Just think how much more efficient everyone could be – we could get work done or have a nap while going places. That would be awesome!
It would be “interesting and beneficial” to have a lot of things but unfortunately “interesting and beneficial” don’t buy food.
Hackers and makers already have cheap access to a lot of things – mass storage, internet connections, servers, free CAD software, chip flash programmers, adjustable power supplies, oscilloscopes for ~£100-200. What are you complaining about! there are loads of ubiquitous tools out there.
You seem to have a problem with specialist, high performance equipment being expensive to produce. What.
Chauffeurs? What. to you. Totally irrelevant and false analogy. I specifically mentioned a VNA. Free CAD software, chip flash programmers, power supplies, et al, doesn’t help me measure what I want to measure. So yeah, I do have a problem with tools being too expensive. At one point ‘scopes were super expensive, and now you can get a Rigol or clone for cheap $$$. That’s exactly what I’m talking about. Getting the high end tools down to the lower to mid-range end of consumer who doesn’t have huge behemoth corporation R&D budget. You fail to understand me and my point entirely. Good day.
This modification has nothing to do with “open source numbnuts” since it is dealing with a proprietary product.
The open source solution would be to develop their own product and to license that product under an open source license. That product may be custom firmware on top of existing hardware or it may involve their own firmware and their own hardware. Either way, it seems as though most people believe that this is acceptable. That isn’t to say there isn’t conflict between open source developers and the developers of proprietary products. When the conflict does arise, it tends to be over patents. Patents are an entirely different issue from duplicating a license code to unlock existing functionality.
Although he’s unlocking the extra features, he is locked out of the tech support and other perks of actually purchasing the upgrade.
Doesn’t matter what anyone here believes. I’m pretty sure any jurisdiction in the world would at least hear both arguments in a criminal case. Tek will surely pursue anyone they believe is defrauding them of revenue. Even with the best counselor in the world arguing, “but Tek listed the <DMCA REDACTED> on their web-site” or “they are just copying an EEPROM” to a non-tech savvy magistrate, one is taking a chance. Tek will likely go after big fish first. However there is plenty of historical record of companies making examples out of little fish.
I this case, it’s hard to get noticed as this hack could be done in the privacy of your basement. However I caution both the original site author and Hack-A-Day. Some times the good fight is worth it. Sometimes it’s a destroyer of lives. Laws, ethics, or morality,rarely trump the church of profit.
Copyright violations in most of the world are civil cases, not criminal cases.
And that is exactly why it needs to be talked about. If fighting the good fight destroys lives and challenges laws, and ethics and morality can not trump the church of profit, then something is disturbingly wrong with society.
Here is the truth about the rule of law that most people will never understand (and it is just as true for money): It holds value only so long as the vast majority of society agrees with it. Monetary exchange rates are 100 percent faith. The same is true of the rule of law. 99.9 percent of society agrees that bashing through a shop window and running off with the cash register is wrong. Therefore it is a law that is inflexible. But pulling over people simply because they LOOK like they might not have a green card is NOT something we all agree on. As a law, it will only stand until enough people say “NO”
No law can stand long when it works against society and human nature. Eventually enough tech savy people will get together and push their way into the courtrooms and hearing rooms in which these stupid laws are dreamed up and voted on. WE must control the making of laws which directly affect us the most. A few of us WILL get stepped on. Meaningful reform often requires a few martyrs to inspire the masses to say “Wait a minute, that’s not how WE feel these things should work.”
This is the same as cracking software. By making the CAD file available on OSH Park, you have now drag down an open source resource to copyright infringement. Do you want OSH Park getting DMCA take downs?
This is not the way to help the open source at all.
The board on OSH park has *nothing* to do with Tek’s actual product. It’s simply a EEPROM breakout, which is what Tek’s product is too. So it could be for anything, it doesn’t really matter.
The files are the tools for breaking/cracking Tek’s copyright protection. The lawyers don’t care if they inconvenient a small business to chase down someone who enable others to circumvent their IP protection.
Also a very dumb move as OSH Park have the PCB delivery address and billing info if Tek decided to chase this person down via a court order/lawyer letter to OSH Park.
Ah, the old golden screwdriver.
Two things.
One: I will continue to do whatever I want with hardware I buy.
Two: As you start getting into higher end hardware these sorts of fantastically easy hacks become more possible because employees don’t feel the hurt having their company spend piles of money and home users aren’t paralyzed by the fear of losing a service contract.
If he had figured this out and not told anyone how, no one would even think about being mad. If this didn’t include ‘software hacking’ it wouldn’t be a big deal either. When one person makes modifications to their own hardware (whether it’s finding out that an undocumented serial port responds to commands, or soldering buttons on to the pcb where they were unpopulated and using the features now at your fingertips) no-one bats an eye. If I had an expensive oscilloscope and found out that if I populated the boards already present for two more channels I could have a quad channel scope then it would be fine, but throwing a few bytes at the firmware is now different?
My guess is people get most bent out of shape when there is great gain for less work, if he had reverse engineered the software and written a module he would be a hero despite making Tek’s module redundant, but this looks ‘easy’ so it’s ‘wrong’.
If the person reverse engineered the scope and wrote additional functionality on his own that wasn’t available from Tek, he would be a hero like those Canon camera firmware mods.
But no, this person only enable what was already in the scope, but not pay/licensed for functionality. This person is a cracker.
This person is a cracker.
That sounds racist to me.
The right thing to do is write code that does the same job and get it to run on the hardware.
No. The right thing to do is not ship something the user didn’t pay for. If you dangle a carrot in front of the horse, don’t get pissed if the horse manages to eat the carrot.
So you are arguing that the proper solution is something which saves the average user nothing (other than temptation), and costs Tek and the person purchasing the feature even more money than it already costs. In my book, that is a bad solution.
Looks like he created a piece of hardware worth 500$ to me.
This is theft. Some of the comments use the logic: hey, it is OK because I wasn’t going to buy it anyway, so I’m not depriving them of any revenue. That logic is warped.
Some say: hey, the software is in there and it is outrageous Tek wants so much money to enable software I’ve already paid for. No, you didn’t pay for it. If Tek actually made you return the scope for an upgrade, or had to mail you a module which you plugged into a slot somewhere, the price would be even higher and the ease of use lower, so arguing that that model is better is wrong.
I disagree with the moral part of your argument. If someone sells me a screwdriver I expect not to be sued if I open a tin of paint with it. I expect to have total control over what I do with it. If it doesn’t fit something I want to be able to hacksaw a slot in it. Prior to DRM we could do that. It’s like I bought a set of 5 screwdrivers and found a sixth in there. I’m told the screwdriver is legally mine but I can’t undo the string round it because I only paid for a set of 5 and the string constitutes rights management.
Strawman argument.
Explain please, the code is the screwdriver in my argument, how is that a misrepresentation?
As has been said over and over by both sides, physical theft and intellectual theft are not 100% the same. Your analogy is broken because you are comparing an intellectual theft vs some scenario which doesn’t happen in the real world.
Tek has a business model whereby you agree to purchase their system at some price and in return you get the physical machine and some set of software and some level of support. It is better (easier, more reliable, cheaper) for the Tek AND for the customer for Tek to ship the extra software with the base model then flip a switch if you pay for the extra feature. The alternative, that you have to order a chip, wait a week for it to arrive, then install it, is costly and inconvenient.
This was all made clear to me when I first started working as an engineer, working for a company making OCR machines, $35K per machine. It involved five or six 68K CPUs, tons of RAM, lots of TTL to glue things together. We developed a next generation machine which used fewer but more powerful 68020 CPUs. The new more powerful machine was sold for the same $35K price — a win for the customer, 50% faster at the same price. Customers who didn’t need the extra speed were happy that they could buy the old level of performance for only $25K. Everybody wins, right?>
The cost reduced $25K unit wasn’t the old hardware,though. It was a 2nd generation machine with a slower crystal. At first I was offended — why not sell the more powerful machine for $25K? Well, we’d go out of business because the profit was too thin at that point. Why not sell the old machines at $35K? The first generation machines were actually more expensive to build than the 2nd generation. The $35K customers loved the fast speed, and the new $25K customers were happy they could afford a machine now which used to cost $35K, and we were happy because we were making more money. It was a win-win, nothing unethical about it.
My scenario does not involve physical theft. The fact that it does not occur with screwdrivers I think provides context. Shipping chips to customers and having them wait is not the alternative, it’s what Tek are actually *doing*. The difference is they do not contain the software – which users already own a copy of.
My understanding of business is certainly naive but the engineer in me does want to find the person that made that OCR decision and replace the oscillator in his pacemaker with one running at 2/3rds the frequency.
Your story serves to explain why it makes good business sense to do what both your OCR company and Tek did, but you didn’t actually address the issue of unlocking the “better” functionality without paying.
To bring it full circle, you have to ask the question: If the owner of a $25K OCR system “overclocks” it to function like the $35K one, did he steal $10K from the company? And the answer, in my opinion, is: no, just as it is in the Tek case. The only difference is that Tek advertised the fact that their machine is upgradeable, while your unnamed OCR manufacturer (presumably) did not.
Especially given the typical skill-set their user base, it seems extremely naive of Tek not to expect this exact scenario to happen given the simplistic nature of the “protection”.
“This is theft. Some of the comments use the logic: hey, it is OK because I wasn’t going to buy it anyway, so I’m not depriving them of any revenue. That logic is warped.”
I dont think I have read any posts using such logic.
The dominant logic seems to be that the they shipped a product (a software feature) the user did not pay for, and the user found a way to use the product. That what most people would call a prize, bonus, freebie, gift or easter egg.
This is theft of Teks IP, probably a violation of copy right law. Theft any way you slice it. Is Tek a good company for building just top of the line scopes and crippling some of them and charging less for those scopes? It doesn’t really matter… They can still sue the daylights out of you and and you will lose. The law is the law. Period! I love how people spout their own opinion as if the court or the judge is going to accept that as fact and let you walk without raking you over the coals. Your opinon of “how things should be in MY world” don’t mean squat to facts and the law!
And how “easy” it is to break the law don’t make things any less of a crime! “well, the posted the <DMCA REDACTED>, and its just on a cheap little eeprom” HA! I can simply press on my accelerator a little harder, and before I know it, 100MPH your honor! So since thats so simple, I don’t get convicted for speeding, right?
Just because the <DMCA REDACTED> is public, and you can buy an eeprom, and the fuctionallity is there, buried in the the device doesn’t mean you have a license to use with without paying for the license!!! If he were selling these they’d probably sue him into oblivion. I’d be surprised if this doesn;t get at least a CaD letter.
There is no gray area here kids…. Theft is theft, no matter “how you feel” about it…
Copying != theft, copying == copying. END OF STORY
The law is the Law but you need to be clear which kind of law you are referring to.
Theft is a criminal matter, as are road traffic offences and are pursued through the higher courts on behalf of the state.
This article relates to a breach of licence which is a tort and is dealt with in civil courts IF Tek decide to sue – this is not ‘theft’ it is classed as breach of contract.
You’re right – no grey areas, no need for amateur opinions, we have hundreds of years of jurisprudence to define this for us.
Read the DMCA, it is a violation to break a digital lock. There is no justifying this by claiming it is too expensive for you, it is simple, Tek makes enough money already. It is a violation of DMCA, period. Just as unlocking your phone in the US was until recently.
If you do this in private then no one will know. But to make it public is another matter entirely. This is how entire web sites get taken down, with a DMCA order.
Not everyone one HaD lives in the US or has the same copyright laws. In Canada fair use allows you to make copies of your media for backup purposes.
Most countries in world have a ‘can’t pick digital locks’ law. Canada does as well, while you can make a backup of your media, in the case of a movie DVD you can’t because in order to do so you have to pick the digital lock. So the right is actually meaningless for most people. Ditto you can’t disassemble sw that is protected by a lock or in this case: enable sw that is protected by a digital lock. Courtesy of US trade agreements, most countries have digital lock rules that trump fair use rights.
Hackaday is a US site, Google is a US site, both are thus under the DMCA umbrella.
re Canadian copyright law.
Might want to actually pretend to read the law first. You are not backing up the OS of the scope either. More like “bypass, remove, deactivate or impair the technological protection measure” without the authority of the copyright owner.
http://laws-lois.justice.gc.ca/eng/acts/C-42/page-42.html#h-54
>41. The following definitions apply in this section and in sections 41.1 to 41.21.
“circumvent” means,
(a) in respect of a technological protection measure within the meaning of paragraph (a) of the definition “technological protection measure”, to descramble a scrambled work or decrypt an encrypted work or to otherwise avoid, bypass, remove, deactivate or impair the technological protection measure, unless it is done with the
authority of the copyright owner; and
>Prohibition
41.1 (1) No person shall
(c) manufacture, import, distribute, offer for sale or rental or provide — including by selling or renting — any technology, device or component if
(a) circumvent a technological protection measure within the meaning of paragraph (a) of the definition “technological protection measure” in section 41;
(c) manufacture, import, distribute, offer for sale or rental or provide — including by selling or renting — any technology, device or component if
(i) the technology, device or component is designed or produced primarily for the purposes of circumventing a technological protection measure,
Exactly, he picked a digital lock.
There is precedent in DMCA rulings that reverse engineering is OK. If it is judged as possible to have reverse engineered the part without copying codes, then DMCA has nothing against this.
Mamilos!
What if I get an STB for a cable feed in my house and use soft cams (imagine its 5 or so years ago when that stuff worked..) and watch some free TV is that a: legally ok and b: morally ok?
Legally just because someone left a wire in my house with scrambled TV coming out of it that doesn’t entitle me to descramble it… And morally I would know I’m getting something I should be paying for for free. I don’t think I would feel guilty but I would know it’s wrong.
To all those people that think that leaving disabled features in products is somehow dishonest and companies that do it deserve to be hacked. How would you ship optional features?
I think this is neat but really if you work something like this out keep it to yourself.
This isn’t quite the same as you don’t own the card that enables the TV so you don’t have a right to mess with it. (Pre DRM law proof). There is also a difference between modifying something you own and distributing or selling products of that to other people.
you mean like a slingbox?
http://www.sling.com/
Have been in operations for years and not illegal.
No, Cantido is talking about descrambling TV with third-party equipment, so he can view scrambled channels without paying the operator for them. That’s the metaphor. Slingbox basically lets you send video from your own TV setup over the Internet. They’re different things entirely.
“To all those people that think that leaving disabled features in products is somehow dishonest and companies that do it deserve to be hacked. How would you ship optional features?”
here is a thought.. by actually shipping them. Either bundled when purchased or shipped separately. Software retailers cant have the best of both worlds. Yes it is essentially a product free of physical constraints. But if you wish the customer to abide by the same physical constraints as a object product, you must also treat your software as object products. You have to play by the same rules.
it isn’t theft, the software was there the whole time in the hardware he purchased. If it was a separate product that he pirated, then it would be theft. In this case, Tek never felt a loss.
If I bought a car for $20k and it had 100hp at 25mpg and the upgraded model was $27k at 200hp/40mpg but the difference was a software key, you bet your sweet ass I would try everything possible to unlock the higher performance.
If they don’t want people accessing features already present, then don’t ship it in the product!
Finally a car analogy.
Hack the firmware all you want. If nobody knows about it there will not be any enforcements, so you get away with it. You still broke the law regardless how stupid it is to you.
But this is more like a dumb kid that broke the speed limit, post himself doing that on youtube and encourage others to do it.
1. if you could be able to unsolder the original eeprom from the module you could then put it in a rom reader and extract the program and using hex editor find and change the code to remove the date and time checks.
2. if the device has a user settable date and time and you dont mind the time date being wrong you could keep setting the date and time back 30 days to get another month (this is how software demos are defeated).
3. you could drop the money on the full module (make sure to maybe buy it from a dealer (not the manufacturer) then unsolder and resolder the full chip from the full version board onto the demo board then put the demo chip onto the full board and return the module for refund).
3a they will be likely to test the module before taking it back so you may want to fry the demo chip by reversing the polarity or over volting or even apply voltage to the data pins so it is unreadable and return as defective
3b. better yet if the chips can be imaged and reflashed you could just copy the software and flash the demo chip and return the original for refund.
That ranges from immoral to flat out fraud though.
I have made some comments above about the difference between unlawful (civil tort) and illegal (a crime). I would say that 3 thorough 3b are probably illegal by ways of ‘obtaining monies through deception’
Last I checked, it was Hack A Day, not Crack A Day.
Even if you think this is legal (and that’s dubious), it’s pretty unethical. Responsible behavior in this case would be similar to reporting a zero-day exploit: go to the developer (in this case, Tektronix), let them know what you found, and give them an opportunity to respond/patch before you make it public.
In my mind, it’s even worse that [jm] got a demo version from Tek first and copied that outright. At least there’s some “hack” to reverse engineering hardware (a la Bunnie and XBox), but this is just plain theft.
HaD and [jm] are both implicated here – shame on both of you!
(For those who say the protection is lackadaisical, you’re not wrong. This is pitifully easy to defeat, but to be fair to Tektronix, they are playing by the rules as laid out by the law, which is pretty clear on stuff like this.)
Also not “How to grow pot” a day nor “Scamvertising” or Pseudo-Science a day.
I wonder if the semiconductor companies advertisers are aligned with what HaD is trying to target readers. You know if these guys decided not to associate with crackpot a day, they can give their advertising money to somewhere else.
“Even if you think this is legal (and that’s dubious), it’s pretty unethical. ”
“(For those who say the protection is lackadaisical, you’re not wrong. This is pitifully easy to defeat, but to be fair to Tektronix, they are playing by the rules as laid out by the law, which is pretty clear on stuff like this.)”
And to many others who say simply “yea but its the LAW.. you cant fight the law!”
Well yes, and no.
The question of legal vs ethical is an important one. And more importantly, what are laws, really? But let’s start with the first..
Is it REALLY unethical? Detach yourself from your commitment to legality for a moment and really ask yourself, If I purchased a product, and the manufacturer sent me not only the product I purchased, but upgraded parts or software.. do I OWN those additional parts? Now on the face of it you could say “it was a shipping error. I should return the stuff I did not purchase.” And in that case, it would be the ethical thing to do. But if the parts were non returnable, and the manufacturer told you that they ship the extra parts to EVERY customer, no matter which version they buy, how about now?
Now let’s suppose that the manufacturer now starts bugging you about those extra parts. “Hey man.. if you want to USE them, you can pay the upgrade fee.” Would you NOT consider this MORE unethical than if you had opted to not inform the manufacturer that they sent you extra stuff you did not order?
We have a legal term for this form of sales activity. It is in fact a blend of usury and price-gouging in sheep’s clothing (true to some extent of ALL forms of “try before you buy” schemes in which the refusal to buy places burden on the potential customer, such as ‘return the product within 90 days for a full refund’) While not illegal, many would argue it is immoral of the company. However it is important to note this is exactly how drug dealers operate.
So here you have purchased a product, been shipped an upgrade, and told you can use the upgrade only for a limited time, after which you have to pay to keep using it. Ok. Not so terrible. Some would say dickish but whatever. Now you look at the upgrade fee. Its expensive. And the ‘product’ you would receive is not, in your opinion, of the value demanded (price gouging. It does not have to be of rapidly increasing value.. only far above what is considered appropriate for the market).
Now ask yourself “what is a law, really?” It is an instruction set forth by the few to rule the many. When these laws make sense, and we as a society (as in vast majority) can easily agree to them, everything is great. But as the balance shifts from 98 percent towards 50/50, obviously the legality and by extension MORALITY of the law is questionable. Abortion is something that is constantly under scrutiny and pushed one way or another. Legalized pot another.
Just because a law is passed does not mean it should be followed. Black people have to sit at the back of the bus. If no one challenged the assumption that this law was ethical, we would still be living in a segregated world.
It is clear that much of the laws that affect hackers, makers and engineers are NOT written by hackers, makers and engineers. It is time that they SHOULD be.
Whether it’s theft, copyright infringement or merely violating terms, the poetic justice is that the Tek MSO2000 series scope’s have terribly underpowered processors. Turning on extra features cause those scopes cause them to go from their usual frustrating slow performance to nearly unusable.
I can vouch for this having had the displeasure of having to use this scope. It is hilariously unresponsive and many times you can actually SEE the UI elements redrawing. It’s like running Windows ME on a 486, but worse.
Since the CPU is responsible for drawing the waveform, you get at best 15-20fps with absolutely no measurements on. Add one, and it drops to 10fps, Add another, it drops to 5. And so on. Using the rotary encoders is absolutely impossible because it only polls them during screen updates!
All in all it’s a decently featured and well built scope, with the worst software and embedded design I’ve seen in a modern scope.
Was the fact this was done just as Tek did it the uncomfortable part of this hack?
What if someone did the same thing using an ATiny to return the <DMCA REDACTED>. Would that be enough distance it from the original to make this a hack and not a theft?
I don’t understand people saying there’s a legal problem there…
it’s probably against the eula… but theft? copy infringment? defeating DRM?
common:
– there’s no copy, the software is already present in the device you bought…
– theft? what did you actually steal?
– deafeating digital lock? sorry but a plain <DMCA REDACTED> in CLEAR text without any form of encryption can’t be considered a lock, even if written on an eeprom…
while it’s definately not fair to avoid paying for software tektronik developped I can’t see a real legal problem… it’s definately not worst than the rigol hacks.
now you can be sure the next tektronic model will use some form of encryption…
I find most amusing the irony of those complaining about the high price of digital feature add-ons, like the I2C analysis module, in this thread of all places.
I also hope a big scope manufacturer takes notice that ‘Software Defined Scopes (SDS trademark, copyright, etc to me personally)’ are the wave of the future. Hopefully they will realize free base modules and user extensible features via SDKs are the way to profit in the future.
Agreed.
Give the best bang for the customer’s buck in the base model, provide for expansion and hackability. Provide open sourced expansions of your own at a fair market price.
If your target customer is EEs, makers and hackers, then cater to them. Build a loyal fanbase. Many/most of us will buy the best priced and performing product with the most hope of low cost / free / do it yourself upgrade potential.
Be THAT manufacturer. Better yet, do the google/android route and be the governing body of a totally open sourced instrumentation OS and hardware platform, of which ANYONE can make and sell product.
Yes, because of course it costs no money at all to do any of that does it? Tek has a loyal CUSTOMER base, that they earned by hard work, investment and the effort to create 700+ patents. Fanbois are by and large freeloaders. Just ask Nvidia or ATI/AMD how much they earn on their substantial investment in $$$ to keep the *nix fans quiet. (very little) Try >15 staff at one of them to keep up with the myriad of *nix flavours, to create, test and maintain drivers. Which of course is paid for by everyone else who buys their products.
Giving away things for free doesn’t keep a company afloat. What skill do you have that I can ask you to use for my benefit? Without getting paid of course. Lets say 50 hrs of development work?
I’m a little mystified as to how purchasing a piece of hardware from Nvidia or ATI somehow equates to NOT paying for that particular piece of hardware if my OS of choice isn’t by Gates?
“Son, did you break the window by playing baseball indoors?”
“No Dad, you told us not to play baseball in the house.”
“So why did I see you throw the baseball through the window?”
“We weren’t playing baseball; we were playing pirates. I tossed a cannonball against the enemy ship.”
(now add 20-something years)
“Isn’t this hack theft?”
“Well of course not, since the word “theft” would involve physical property.”
“Okay then, isn’t this stealing?”
“Well of course not. All we’re doing is putting a particular bit pattern in a EEPROM, how is manipulating bits in an EEPROM stealing anything?”
“Okay then, isn’t this ethically wrong?”
“Well of course not, because Tek is a multibillion dollar company that can afford it and besides, I think they charge too much, so I should get it for free.”
When you take away the language lawyer games (the word “theft”), the “I’m doing X that just so happens to unlock software feature Y” wink-wink-nudge-nudge, and all the rest of the other oh-so-clever side-stepping of the issue, it all boils down this: The people who don’t have a problem with this are the same people who wouldn’t have a problem coming up with excuses to rip off others for pretty much anything. Because when you get right down to it, it all boils down to “I want it, I can get it, so I will.”
Well freaking said, sir, ma’m, whatever. My vote for best post ever!!!
Agreed. It’s not ‘theft’, but it ain’t ‘right’ either
I hacked my LG TV using service menu IR code to turn on USB movie playback option that is present in more expensive models.
Am I a thief now?
Yes
Do they sell the code for doing this to people with your model TV? If they don’t charge money or they don’t offer it then probably not.
Well, I see what I written is quite ambiguous, “code” being just a command, just like “menu” or “mute” key, but not available on normal remotes.
If this was a secret code that the company officially charged money for then it could be theft. If, however, you cannot pay money to the TV company to enable this feature on YOUR model TV then it has no value.
The big difference here is that Tek are selling the upgrade.
Putting a price tag on something does not magically transform it into property or give one the right to exclude others.
Americans are just loopy. What next, demanding rich people’s imaginary friends have all the rights of flesh and blood and none of the responsibility?
I’d say it’s not illegal.
Many manufacturers actually do that to create a community or a hype around there TV.
It was meant to be discovered.
Sad for those who paid for the more expensive model.
I have one of those TVs. They didn’t lock those features out because they wanted to charge more. Actually use it a bit and you will realize they locked em because they don’t work too well, certainly not good enough to stand behind as an official ‘feature.’ Have a file it doesn’t like on the media and just navigating to the directory will lock the TV hard, as in pull the power cord hard.
As for the image viewer, it is also bogus. It uses the OSD instead of the main display engine so on a FullHD set I get 1366×768 at 15bpp and the color is way off as well.
This is not different from changing the jumpers on (old) AMD processors to release a second core or to allow overclock. Aint never seen anybody complaining about piracy on doing that.
This is old news: the original article in German is available here for at least 2 years: http://herzogmuehlweg.de/TDS3UAM/TDS3UAM.html
On the same website is an USB adapter for the TDS3000 scopes.
The hack by it self is quite harmless.
But posting a designed board on OSH Park that people charge for makes a very different ballgame?
Define harmless in this case. It may be a situation like the yellow multimeters and Fluke, where if Tek do not enforce their right they cannot enforce it later in other circumstances.
Harmless in the way that it takes quite a bit of knowledge and effort for anyone to pull off.
And the risk of breaking your scope if done wrong.
I think that most people won’t even try.
The next step would be selling the complete pcb and preprogrammed chip.
That would surely be asking for trouble?
My way of seeing this is that it’s actually the same as copying a subscriber card for enjoying something for free.
And that IS theft!
STOP. Copyrights and Trademarks are NOT the same thing. Fluke’s multimeter styling is a trademark and requires them to defend it if they wish to continue to keep it. Copyrights are COMPLETELY DIFFERENT and DO NOT need to be defended.
Actually, Fluke’s styling is covered by tradedress, not trademark, and refers to the product’s general color scheme/shape, not what’s written and drawn on it. But I’m being pedantic.
That is, assuming you’re referring to the Fluke/Sparkfun customs debacle
nothing wrong with pedanticism when talking about legal issues dude. There are too many people who have unnecessarily settled due to incorrect language used by a scary legal opposition.
I don’t need oscilloscope decipher for I2C or SPI, because I have bus pirate, open bench logic sniffer and Saleae Logic Analizer.
Two weeks ago I received an offer from Tek to receive several of the accessory modules free with the purchase of a new scope. The timing is a bit suspicious, as if Tek knew this was coming. More likely, however, Tek planned long ago to use these as deal sweeteners once the initial novelty of the scope family faded and price pressure increased.
If Tek really wanted to make the feature protection robust, they could have. They would have taken the approach I did at Ericsson/GE Mobile Radio did long ago, and tie the enabling data to the host’s ESN. Then the plugs would only work in the intended scope. Painful logistically, but cost effective for such an expensive “feature.”
Ericsson/GE used that approach, and it’s successor Harris still does, to sell additional functionality on mobile/portable communications equipment. The approach allowed us to market a single hardware model of each radio, and base the price on the overall capabilities. While there were a few complaints, most customers realized that overall this lowered everyone’s cost by simplifying the manufacturing process.
The original patent explains the (admittedly) simple process:
http://www.google.com.mx/patents/US5499295
SnapOn’s previous line of automotive diagnostic equipment used PCB “keys” to enable support for various brands and models. Most of those keys simply tied various pins together like the original Magnavox Odyssey video game ‘cartridges’ to activate code already in the device. Some of the keys have additional components on them, most likely to overcome running out of direct pin connection patterns.
It should be possible to make “One Key to Rule Them All”, at least for the no-components ones by making a PCB with a set of switches. If the extra parts are just stock items, that would present no barrier to including them in a universal key. If they’re proprietary then that would require some more work.
I doubt SnapOn would care since they discontinued all support and replacement parts for the system a couple of years ago. If you have a vehicle newer than the EOL date, it’s useless on them for anything but generic OBDII/CAN scanning.
The USA and United Kingdom have laws against companies demanding payment for unsolicited goods. He bought some equipment with firmware, they threw in firmware he didn’t ask for, so it’s basically finders keepers.
This is not theft. Textronix sold a product, and the product is therefore the property of the customer, who may stick what they please into whatever slots are on the product. It could be a screwdriver, it could be a blowtorch, or it could be some silicon with a special arrangement of floating-gate transistors, it’s all the same. If whatever the customer happens to stick in the slot changes the behavior of the product, that’s the customer’s issue alone, whether the effect is good or bad, because Textronix sold the product to the customer for the agreed purchase price, which includes the particular arrangements of bits in its memory. The customer may therefore do what the customer pleases with those bits, and send whatever signals they please through the PCB. Basically, just because a company built a product with some exposed wires to facilitate extra profit on their part does not mean that you can’t touch those extra wires with whatever you want. They’re your damn wires.
This ^
Best post I’ve seen on this page yet :)
If Tek was smart they would give these features away for the sub $5k models. They are being eaten by Rigol and other low cost high value tools. If Tek doesn’t get their equipment in the hands of people early in their career they run the risk of people only ever knowing Rigol etc. When it comes time to buy a $10k scope, Rigol will be the default choice. The makers of micros and software understand the value in having a place on the desktop or workbench. They actively pursue new engineers and makers. Test equipment companies should take a lesson.
You are correct…and they ARE smart. Here is an excerpt from an email ad they sent me last week.
“Our biggest sale of the year won’t last. Purchase any of the five Future of Scopes Series and get a free Protocol Analyzer upgrade – up to a 30% savings.”
There is precedent via the DMCA which asserts that codes such as the one on this EEPROM must be sufficiently difficult to reverse engineer (without directly copying them) in order to be judged as a copyright violation. The question is: Is this EEPROM code easy enough to reverse engineer?
It is *trivial* to reverse-engineer. You can even make your own without copying an existing dongle. <DMCA REDACTED>
The DMCA prohibits circumventing *effective* copy protection mechanisms. This term isn’t defined, but I bet it would be pretty broadly construed.
Finally, you might have agreed to not to do this with whatever shrinkwrap license they include. But, if you buy one of these scopes third-hand, there’s usually no agreement to click through. If you didn’t agree to anything and your circumvention doesn’t fall afoul of the DMCA, you *might* be on the right side of the law, although probably morally wrong.
I don’t think Tek should be too worried about this. If you’re buying a Tek, you’re probably using it to make critical measurements and care about things like regular calibration. Using some unapproved hack to enable additional options might void the calibrations and expose you to legal risk (if, say, someone gets injured because your hacked scope was giving you bad data). This is why I think the Fluke multimeter kit, even though it was a joke, was actually a great idea. It lets them do price differentiation between hobbyists and professionals who NEED a guaranteed, factory-calibrated and tested multimeter.
This has been known for years. This works on all scopes that use the application modules. The applications are generally not that useful to hobbyists, and a vast majority of businesses (tek’s primary source of income on these scopes) will always purchase the application modiles for legal reasons.
What would be much more interesting is a hack for the new MDO3000 series scopes.
Here’s the link for the original hack:
And at this time it was not new.
Really hacktek is where you want to go.
Find this :
MRE says:
July 28, 2014 at 10:41 am
I 100% agree with the statement made by this person. Worth reading.
This is DANAHER corp. They own Tektronix. It is the same corp that bought Fluke and declared that nobody else can produce yellow DVM’s. Remember the Sparkfun DVM’s? Same company.
They gobble up good brands, and some say they outsource the production overseas and the quality plummets.
This is what happens when Hackaday goes corporate. No balls guys. If you own it, you should be able to tear it apart, alter, and do with it whatever you damn well please. If Tek is that stupid, that’s their problem.
DMCA has no effect on my server: http://daid.eu/~daid/dmca/
Did you mirror the BIN files too? Oontz took down his project site.
And its the wayback machine to the rescue once again. :) https://web.archive.org/web/20140728140447/https://sites.google.com/site/blinkyoontz/hacktek
Or heck even the first edition of this page itself in the wayback machine!
https://web.archive.org/web/20140728140425/http://hackaday.com/2014/07/28/cloning-tektronix-application-modules/
One thought. As this is in essence a third party/DIY mod to the original device would it not be completely within the legal rights of the owner to do those mods as there is not pirating of software or hardware going on. Just wondering if the EU-sony ruling would apply.
So um, doesn’t anyone else remember the “Wayback Machine”?
https://web.archive.org/web/20140728140425/http://hackaday.com/2014/07/28/cloning-tektronix-application-modules/
Ahh yes, I think it’s the first rule of the internet, “What goes on the internet, stays on the internet”
I did, just figured Tek would have already have DMCAd them too. Guess there’s only so much work they’re willing to do.
Tektronix’s MSO2000 line of oscilloscopes are great tools, and with the addition of a few ‘application modules’, can do some pretty interesting tasks: decoding serial protocols, embedded protocols like I2C and SPI, and automotive protocols like CAN and LIN. While testing out his MSO2012B, [jm] really like the (limited time) demo of the I2C decoder, but figured it wasn’t worth the $500 price the application module sells for. No matter, because it’s just some data on a cheap 24c08 EEPROM, and with a little bit of PCB design it’s possible to build this module for under $5. ( https://sites.google.com/site/blinkyoontz/hacktek )
The application module Tektronix are selling is simply just a small EEPROM loaded up with an SKU. By writing this value to a $0.25 EEPROM, [jm] can enable two applications. The only problem was getting his scope to read the EEPROM, a problem easily solved with a custom board.
The board [jm] designed is available at OSH Park ( https://oshpark.com/profiles/mchamster ), with the only additional components needed being an EEPROM, a set of contacts for reading a SIM card, and a little bit of plastic glued onto the back of the board for proper spacing.
Tektronix please read this: Streisand effect http://en.wikipedia.org/wiki/Streisand_effect
Copyright doesn’t apply to this usage. The prevailing legal guideline is the supreme court ruling on Lexmark V Static Control Components, with a 9-0 decision.
You absolutely can copy the information as it is required for interop. Shame on hackaday for giving in so easily.
What? A DMCA for a bunch of hex like this?
0xFF 0xFF 0xFF 0xFF ‘D’ ‘P’ ‘O’ ‘2’ ‘C’ ‘O’ ‘M’ ‘P’ 0x00 0xFF 0xFF 0xFF
0xFF 0xFF 0xFF 0xFF ‘D’ ‘P’ ‘O’ ‘2’ ‘E’ M’ ‘B’ ‘D’ 0x00 0xFF 0xFF 0xFF
0xFF 0xFF 0xFF 0xFF ‘D’ ‘P’ ‘O’ ‘2’ ‘A’ ‘U’ ‘T’ ‘O’ 0x00 0xFF 0xFF 0xFF
I definitely agree, the Streisand effect will apply here.
Close, but no cigar.
Wake up – Once you make something public it is exactly that PUBLIC
The way back machine is good for such stuff and copies have gone to Sweeden and elsewhere and are still public now and will remain so.