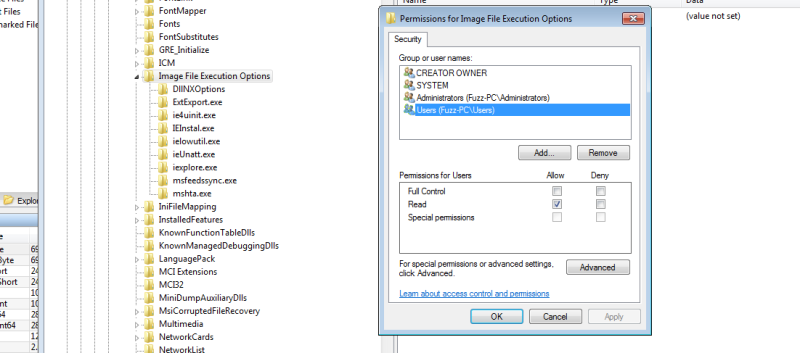
The Cybellum team published a new 0-day technique for injecting code and maintaining persistency on a target computer, baptized DoubleAgent. This technique uses a feature that all Windows versions since XP provide, that allows for an Application Verifier Provider DLL to be installed for any executable. The verifier-provider DLL is just a DLL that is loaded into the process and is supposedly responsible for performing run-time verifications for the application. However, its internal behaviour can be whatever an attacker wants, since he can provide the DLL himself.
Microsoft describes it as:
Application Verifier is a runtime verification tool for unmanaged code. Application Verifier assists developers in quickly finding subtle programming errors that can be extremely difficult to identify with normal application testing. Using Application Verifier in Visual Studio makes it easier to create reliable applications by identifying errors caused by heap corruption, incorrect handle and critical section usage. (…)
The code injection occurs extremely early during the victim’s process initialization, giving the attacker full control over the process and no way for the process to actually detect what’s going on. Once a DLL has been registered as a verifier provider DLL for a process, it would permanently be injected by the Windows Loader into the process every time the process starts, even after reboots, updates, reinstalls, or patches.
So it’s all over for Windows right? Well… no. The thing is, to register this DLL, the registered process has to have administrator rights so it can write the proper key to the Windows Registry. Without these permissions, there is no way for this attack to work. You know, the kind of permissions that allow you to install software for all users or format your own hard-drive. So, although this technique has its merit and can present challenges to processes that absolutely must maintain their integrity (such as the Cybellum team points out in the Anti-Virus software case), some other security flaw had to occur first so you can register this sort of ‘debugging DLL’.
If you already have administrator permissions you can do pretty much what you want, including DLL injection to fool anti-virus software. (Though it might be easy just to disable or remove it.) This new tool has the advantage of being stealthy, but is a 0-day that requires root a 0-day?
[via The Hacker News]
















But how many windoze systems run with the user as administrator? I know back when XP was around is was the norm, so much that many major applications had problems without it.
Back in the days you had to log in as administrator at least once when plugging in a new/foreign USB drive. A dialog popped up asking you to enter credentials to “install drivers” (well, actually it installed nothing but it cached the VID/PID/serial number in the registry for quick identification and to allow non-administrators to use it).
I think it was a “safety” feature to block users from plugging random devices into important PCs without authorization, but it ended up being useless and annoying. Safety should have been added to image decoders (do you know that WMF files support embedding hidden executable code?), Internet Explorer and that scary virus installer known as Autorun. All these flaws weren’t bugs but UX “features” that traded ease of use (as in: not having to double-click a file in a CD, which is extremely difficult, but rather having the installer pop up automagically) for security (as in: connecting the computer to the internet and immediately getting it full of viruses and assorted spyware without having to open anything).
We didn’t survive. Blaster and Sasser silently infected lots of PCs connected to the internet without any user interaction, Autorun brought hidden self-installing viruses to USB drives (many viruses today still drop a hidden installer and autorun file on all drives they can find) and IE’s ActiveX, Visual Basic scripting and drive-by downloads were largely abused by websites in the 2000s.
Only the WMF executables were discovered a lot of time later.
:/ I’m still usin XP, works fine; just Chrome denies to update the navigator. Sasser? I fiz a lot of systems :D that gave me for a used car.
Just pop up a dialog box that says “Right click and click Run This Program as Administrator to continue”, people will just do it. Most people just aren’t worried enough about security, and part of me thinks that might be healthier… but the bitter person inside me who gave up on computer security after realising it’s a social problem is still mad.
It’s not that people are “not worried enough about security”, it is more of “people are not expected to know every little secret of complex systems deeply enough that they know what they are doing when they do it”. People are not the problem, systems are the problem. It is not people’s (user’s) fault that a random DLL hosts a virus in itself…
When I last ran XP I ran as a non admin and still got 0wn3d. The big huge security hole thinly disguised as a web browser just lets anything in. The only thing XP ever did right was convince me to move to Linux.
While I ran an XP desktop for a decade as admin and was infection free … having gone so far as to block Internet Exploiter from running on the system and using Mozilla/Firefox.
Happened to me just before Firefox and AOL had bought and ruined netscape so there wasn’t much choice. Ran Windows 2000 since the betas were in Technet and never a problem, XP a few months and it had malware issues on top of all its other issues. People say it was better after a couple service packs but I wasn’t waiting that long, made the switch and never looked back.
“So it’s all over for Windows right?” Well… yes. The masses are used to clicking in the affirmative when the warning comes up to indicate that a process wants to run as an administrator.
The weakest link in any computer’s security chain is the operator.
I thought the first post-install step for windowz was to disable UAC :P
Why?
It started because UAC was hyper-paranoid on Vista, to the point that setting the clock brought up a full-screen block/allow prompt. Combine that with an ecosystem of legacy software and you’ve got a terrible user experience. UAC’s been around for 11 years now, and the ecosystem has grown with it, so you’re mostly going to see its prompts when you install software or if something hinky is going on these days.
The “wisdom” to completely disable UAC “because it’s annoying” has unfortunately persisted, like the “wisdom” to not wear seatbelts because it’s “safer” to be ejected from your car rather than held inside in an accident .
the problem was that it went from everything is allowed to damn near every keystroke asking for permission, so most people turned it off or allowed everything without looking
No, most people did no such thing. Most people just complained about it for a while, then got used to it because it’s not actually THAT intrusive.
The first post-install step is to install Linux dual-booting with Windows. The second is to log into Linux and use the dd command to corrupt the Windows partition and its boot sector:
dd if=/dev/urandom of=/dev/sdaX bs=4M
(Replace sdaX with the Windows partition’s device.)
The third step is to try booting Windows. The fourth is to destroy the computer with a hammer if Windows still works.
But… but the bazaar model and the million billion eyeballs on the open code anyone can read are supposed to prevent this from happening!
/s
There’s a lot of ways to get administrative privileges pretty easily. Just a little bit ago I was playing around with a workstation at uni and found that all users had recursive RW perms on C:\wamp. I enumerated all of the services with a startup type set to “Automatic” and sure enough C:\wamp\bin\mysql\bin\mysqld.exe ran under a SYSTEM context. Using https://github.com/PowerShellMafia/PowerSploit/tree/dev/Privesc and Write-ServiceBinary I crafted a malicious mysqld and dropped it in the directory, and sure enough I was Admin after a quick reboot. I told campus IT about the bug but it goes to show how easy it is to pwn Windows…
Dear NextGenHacker101 wannabe,
There is no C:\Wamp folder in Windows.
Someone at your university created the folder, installed a service in the folder and then gave everyone write permissions to it.
It’s easy to mess up an environment when you add or modify stuff without knowing how to handle permissions.What you describe would be just as easy to do on any given platform (yes, your beloved Linux too) when permissions are handled like that.
The only thing your exercise shows is how easy it is to “pwn” your school’s computers. Care to share with us which school that is?
Dear Hurr Durr I’m so smart cuz I know what the root of C looks like.
I think he’s aware of that, hence why he emailed campus it and not Microsoft….
Thats kind of IT fault there, I work on a uni IT too, we have wamp for our students in some images, you can grant permission to start/stop a service for a normal user instead of automatic running it using system, that way not only is more secure but doesnt slow down the machine if they arent going to use it.
Poor administration isn’t a windows problem. The exact scenario is possible on OSX and Linux ax well.
Sticky keys can be used to get admin xp-10…
No it can’t.
Unless you already have write access to system32\sethc.exe and read access to cms.exe
Don’t forget to replace the system\sethc.exe.mui file too !
setup or repair has access to system32\
Admin access can be transient, it helps to have some persistence.
Well… no. Once you have admin you can install persistence. Like we see now.
This is a typical trick that NSA could use to get persistent access to a machine. No files modified so tamper detection is not triggered. That sort of stuff.
Bill Gates’ real name is Pham Nuwen.
Zero day really? This is a known trick I’ve known and had tucked back in my toolkit. It was shown to me. There is all kinds of DLL sideloading tricks. Also it requires admin access to… maintain admin access. Nothing new to see here.
There is no exploit anywhere in this post, or anything novel. It’s like saying, “durrrr, if I have root, I can format your harddisk!”
Also, there are a slew of ways to autorun programs on virtually every operating system. Especially if you have root. This technique has been documented (well, of course, because Microsoft actually provides documentation for it), but also something quite a few autorun check tools look for. So this is really neither 0-day, nor an exploit…
Exactly. “Oh look ! A well documented way to do useful things, restricted by adequate permissions”. So what ?
To quote Raymond Cheng : “It rather involved being on the other side of this airtight hatchway”.
In a properly secured system there isn’t a “root”…
Yeah. This is like saying “Linux is so busted! If you put ‘export LD_PRELOAD=/evilvirus.so’ into /etc/environment you’ll get a persistent access to the computer!”
Window vs Linux war in 3-2-1…
Alright people keep calm. Windows is safe. It has to be!
I am curious if this could persist in my environment in any way. When a user logs off they are given a new vm from a gold image. Not much persists that I don’t intentionally copy with tools like folder redirections, profile (user’s registry settings) etc.
Permission issue aside.
It is easy to get admin rights without UAC stuff, what a fun time!
So Windows 98 is still safe?