[JJ] picked up a Garmin Nuvi 780 GPS from an auction recently. One of the more frustrating features [JJ] ran into is it’s PIN code; this GPS can’t be unlocked unless a four-digit code is entered, or it’s taken to a ‘safe location’. Not wanting to let his auction windfall go to waste, [JJ] rigged up an automated brute force cracking robot to unlock this GPS.
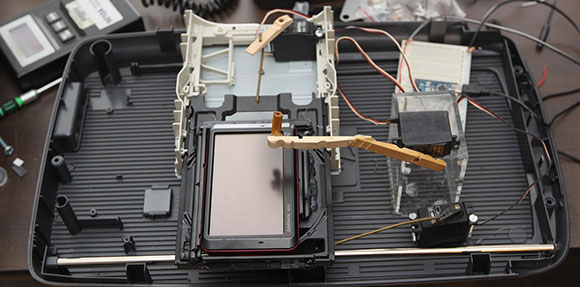
The robot is built around an old HP scanner and a DVD drive sled to move the GPS in the X and Y axes. A clever little device made out of an eraser tip and a servo taps out every code from 0000 to 9999 and waits a bit to see if the device unlocks. It takes around 8 seconds for [JJ]’s robot to enter a single code, so entering all 10,000 PINs will take about a day and a half.
Fortunately, the people who enter these codes don’t care too much about the security of their GPS devices. The code used to unlock [JJ]’s GPS was 0248. It only took a couple of hours for the robot to enter the right code; we’d call that time well spent.
You can check out the brute force robot in action after the break.
[youtube=http://www.youtube.com/watch?v=sHp4px45uQY&w=580]















Fantastic! what a hack!
if he hacked the servo to act as a motor with gearbox that would be a hack, but now it’s just a (pretty ghetto) device.
hack – seek and exploit weaknesses in a computer or computer network.
i fail to see how the post doesn’t meet that definition.
COMMENT FAIL
“”hack – seek and exploit weaknesses in a computer or computer network.””
That may be a teenager’s dictionary definition of ‘hacking’, but to those of us that came through the early 70’s – we know and respect the word and activity a lot more than that simple definition.
Reusing or redefining technology – both hardware and software – to achieve new and unsuspected applications of same. Explore – Learn – Innovate – Share… nothing to do with computers or networks by definition, but if they are in the path of exploration – then so be it
Just because Facebook says something is a fact – doesn’t make it so!
“but to those of us that came through the early 70′s”
And you start your comment with all-caps “COMMENT FAIL”?
Yeah.
Yeah…
The hack was great – the comment FAILed
sounds like you were hacking before it was cool….
You missed the point. You claim to have come up in the 70s, making you around 40 to 50 years old, yet you write like a teenager or at best a twenty-something. To put it another way, I was born in the 70s and I don’t say things like “fail” in normal conversation because it’s the vernacular of the kids today. I talk like an adult because that is what I am.
Maybe you’re young at heart and trying to stay “in” with the teens, but I think it’s more likely you’re just a kid posturing. Either way, it’s kinda lame (something we did say back in the 80s and 90s, BTW).
Good logic, but missed a few key input parameters..
Hint: I was programming my first micros (2650 & Z80) in the 70s, and was working for Digital (DEC) around 1980 on {PDP-8s and 11s)
I have kids ranging from 15 to 29, so I’m loosely in touch with teen jargon, but more specifically – the initial comment about hacking showed (lets call it) disrespect for the origins of the hacking ethic – which was in fact ‘ethical’.
Cheers – I enjoy the sparring, but still wondering how to open a tin of paint !
Oh – BTW – most modern kids posturing can’t spell to save their lives, so my posts probably can’t be classified using that criteria!)
How could I miss something you didn’t mention until you replied to me? Not a single word about your work experience or family stats in the post I replied to. To expect me to somehow intuit all that detail, just to prop up your claims, is quite silly.
So much for _your_ logic…
@kaidenshi – no offence intended in my previous posts.
I was following that you tried to identify my era from my initial post, and was off by a bit. Consequently the teenager/posturing was quite a bit off – although I do admit to being young at heart.(most of the time)
Hugs
technically he could have went straight for the data stream, and wrote code to brute force through software, but he chose to make a hardware and software approach that is muchh harder, and it’s not ghetto because there was no proper defined way to hack it in the first place, there would have to be a standard first to have a lesser standard
This place has become the youtube community of hacking. Turning a servo into a geared motor is even considered a hack? It’s considered ghetto because why? Because he should have went all out and spent a ton of money and make it look super pretty to essentially accomplish his original goal? The man spent very little with whatever he had laying around to crack through a password protected device. That is, in every sense of the word, a true hacker. You should go back to doing PC case mods.
im sure that CD drive was never made for that, im sure those closepins were never made for this and im sure that case was not made for this … its a hack
Does prying open a can of paint with a screwdriver constitute as a hack? I don’t mean to deride [JJ]’s work by any means, I’m just tired of seeing this quip all the time.
Just curious… How do /you/ guys open a paint can ?
I’ve always used a screwdriver to pry the lid at intervals around the perimeter.
Is there a better way ?!
TIP: in the groove of the can lip ( that the tin lid fits into ) – punch 2-3 holes with a 1/16 pin through – which allows excess paint to drain back into the can – but is covered & sealed when the lid is back in place.
TTFN
lastchancename,
Thank for the tip,
never thought punching holes in the groove.
I often use a paint can opening tool instead of a screwdriver to open a can of paint. The tool was less than a buck at Sears.
Agreed, love it for doing something just because.
That said, it looks like Garmin Nuvi’s have reset procedures.
But that wouldn’t have been the hacker way, nor as fun to watch.
Doing a hard reset does not clear the pin code.
nice one :P
How the bot knows when to stop and dont screw gps by accidental press by another bbutton for example locking it again? And how the user figured the code of unlocked device?
I think he just timed the process and set a delay for the successive iteration
probably once running you can just deactivate the pin protection withouth having to input the old one
You could also put a camera on it and fast forward through the video to get to the part where it unlocks to see the code.
You could also add some image recognition to do this of course ;)
An itteration counter would be quicker as it is already in software. Just display the current code and stop.
But for the camera route I would think taking photos would be more of a hack. Two wires attatched to the shutter switch extend the button to a micro switch which is pressed when the cd tray gets to a certain point. maybe even set up a few more switches to erase the previous photo so you don’t have to flick through. :D
But how would you know when to stop the iteration? How/will it give feedback?
I figured I’d let it run without any sort of “check” to see if it unlocked. If it failed or re-locked the device, I would have set up a camera to monitor its progress. Coincidentally I went downstairs to check its progress about 2 hours in, and I witnessed it unlock on “0248”. Pure luck!
Great work! Back in high school, I built a PIC based brute force unlocker for Master combination locks (the ones with the dial face). It used a stepper motor to turn the dial and an actuator to pull on the shackles. This was before I learned that you could just shim the darn things.
there was an update
“The robot does not currently have any check procedure to see if the device unlocked and will continue to pound the screen even after it unlocks. I figured this may not be a problem, and let it run. I had plans to add a camera to monitor its progress if this does not work or re-locks the device.
Coincidentally, I went downstairs to check on its progress about 2 hrs in, and I witnessed the unlock with my own eyes!”
Did he have to watch the whole time to get the code?
i bet once you get in, you’d get to a point in the menu where the button presses would have no effect. However you might need to reset all the settings to get it back to normal.
That’s exactly right. However, about 2 hours in I checked on it to see its progress, and coincidentally, it attempted 0248 right in front of me, so I witnessed it unlock!
Amazing timing :D Must have been very satisfying :)
I had a Nüvi too where the customer forgot the code and the safe location, rendering the device pretty useless. After some various shorting of data lines to GND on the Flash RAM pins, i managed to confuse it, and bypass the check at boot – Hey, there was nothing to lose!
I was going to attempt this, but didn’t want to risk the device. Can you duplicate and document your method? This would be valuable info to share, as its much faster than brute force!
I could try to lock it again and have a go on video, I will write it on my todo-list and update here when I get it done, or even post it to HAD.
I’ve looked for the unit, but unfortunately it seems like it’s the unit that i’ve given to a family member, and it’s in daily use, so won’t get it back anytime soon. I have two more kicking around, and i’ve opened up those, and unfortunately the memory chips on those are BGA packages, and not TSOP like the one i “Fuzzed” – Crap :-/ It would have been fun to document it on video. Another time i’ll remember to do that when i have the device in-hand!
He only used the scanner and dvd sleds though, not the built in motors for each. THat’s a bit disappointing.
The original plan was to use the scanner’s stepper, and the DVD drives eject motor. However I didn’t have the hardware handy to run a stepper.
That other one with the matrix of “fingers” was better.
I saw that one, and it actually inspired me to build this one. Mine can be programmed for different sized devices and different button location for future devices. His solenoids are fixed in place.
Mmmmm. GPS turns up on Ebay, sold off really cheap, locked, and the seller doesn’t know the code…
He’ll have to send it to the police (or original owner) if it does turn out to be stolen property.
Or it’s someone like me who just got a car with built in navigation and didn’t need the extra hardware and didn’t want to pay extortion-like rates for updated maps.
What, they just “forgot” the code to it when they sold it?
And the Freight shipper excuse doesn’t ring true – these devices don’t ship with a PIN as standard, so it belonged to someone. At best, someone “lost” it during shipping from one person to another and it turned up on an auction site.
Was it, per chance, $3?
Its not stolen. It was purchased @ a freight recovery auction. It was lost during shipping and written off by the shipping company. Whoever lost it was paid an insurance claim.
Or someone like me who on many occasions have found myself on the receiving end of a password/pin prompt for which I do not recall the password/pin to my own device. As the last time I used said device in a capacity that required a pass/pin input was several months previous.
Your options at that point are trying to brute force your own device which might not be practical if your need is time critical, such as another trip. Preforming a factory reset if a reset is possible. If not writing the device off as a total loss, or selling it cheap on eBay. Which is better, some ROI or a paperweight?
I’m not saying it’s outside the realm of possibility that it’s stolen but it’s easily equally plausible that it isn’t.
My thoughts exactly. But of course sellers always have plenty of good excuses.
Typical noob comment… assuming auctions = ebay
Question.
The eraser works because it’s a resistive screen, correct? What would one do with a capacitive screen? A grounded sausage? I’d like to know for a similar project.
A 25 cent capacitive stylus from ebay
There are many things you can use, like some conductive foam. There are plenty of examples if you google for diy capacitive stylus, like on instructables:
http://www.instructables.com/id/DIY-Capacitive-Stylus/
Don’t the conductive foams require that they be touching your skin as well? For example, I don’t think the conductive foams or “capacitive stylus” accessories will work if you are holding them with gloves on.
Of course, correct me if I’m wrong.
I made something similar to play a game for me on my phone, I used a small piece of foal wrapped with aluminium foil and connected to a grounded wire.
*typo : should be “foam”, not “foal”.
Ah, so not a small piece of young horse… that would have been more interesting!
@Justin –
I always liked the (‘too good to check’) story about the TV repairman coming round & finding the remains of a pork sausage in the back of the set –
“Yeah well, We sometimes found it worked better if you put yr finger in there”…
Use a hotdog.
Thanks all. Slapping my forehead for forgetting about the stylus.
A grounded sausage… please take this free internets for making my day a bit “funner”. :D
Found a nicer way. http://www.youtube.com/watch?v=FCEhv1_OwEY Drive the sled from a cd drive using the original motor for y axis, and 3 tiny solenoids. Same basic concept, but smaller.
There are a couple of other guys that built similar machines. That one is pretty cool, but I used what I had on hand. Also, mine has the flexibility to program any X coordinate, rather than just 3 points.
Here’s another one, with just solenoids (and springs) ha http://www.youtube.com/watch?v=4EYdEnrJly0
I would have sat down to watch a movie and cracked it by hand. Have done it before with an old combination lock that nobody knew the combination to.
I’ve got a movie about paint drying if you’re interested.
Lol. I’m guessing jj spent more time building this than the couple of hours it took to crack, but then I know which task I’d prefer doing. Cool hack!
Yeah, wish I had one of these for my grandpa, who somehow enabled the PIN protection en-route when he “dropped it”.
This means a) he didn’t know his pin, and b) his “safe location” was somewhere in the city.
I think, in the end, he managed to exchange it at the store he bought it, or mailed it to the manufacturer or something.
I love it !
This is an excellent hack !
AGREED
LIKE ++
Let’s do it the hard way. These things are Windows CE devices, you can gain access to the Filesystem voa the USB and reset the code. Did he even look online first?
USB is inaccessible during a PIN lock. Pin is stored in flash even after a hard reset. Did you even look online first?
+1
YES I DID. Press left lower corner while powering on and enter loader mode, USB unlocked. Sounds like you did not even look.
Lower right corner brings up the hard reset option only, which does not reset the pin. Lower left corner does nothing. Thanks for playing, try again.
Exactly what I was wondering – That and how old the maps are, given he seems to dislike search engines.
Rube Goldberg lives!
Oh look, another worthless comment from everyone’s least-favorite commenter, fuckface! Well done, fuckface.
They like me better than the 80IQ moron that you are…. Duuuuurrrrrrr…. Go back to your fake friends on Myspace you loser.
Just BTW – How do you open a paint can, if not using a screwdriver ?
No, they are not based on WindowsCE. They run a variant of VXWorks OS…
248×8 seconds < 1h< couple of hours
“Fortunately, the people who enter these codes don’t care too much about the security of their GPS devices. The code used to unlock [JJ]‘s GPS was 0248.”
I don’t understand the “fortunately” part of this statement. With the only choices being 0000-9999 it seems that 0248 was as good as ANY other choice.
[JJ] could just as easily started at 9999 and worked down, so the “security” of the device was about as secure as a 4 digit pin can be.
So I don’t get the point of the sentence.
http://www.datagenetics.com/blog/september32012/index.html
(Don’t know how to edit my own post!) Instead of counting from 0000 to 9999 just use the “heat map” numbers to speed up the process. That password falls in some of the categories of usual pins: Ascending sequence number, little gaps betwen numbers, etc
Binary sequences have got to be high on the list.
2^0, 2^1, 2^2, 2^3? Such a password!
The vendor wasn’t in the military was he?
Fortunately for people that need to get around passwords, People are stupid. People really on visual patterns. People use common passwords. Since the password is a simple 4 digit pin, and has unlimited retries, he should have tried the common ones first. 1234, 1111, 0000, 0987, 2580, 0248, etc, Same thing with word based passwords. ILoveYou, God, Sex, family names and dates.
Here’s my take – It’s not a ‘hack’, nor are 90% of the projects/things listed here. What it is however, is a really cool tool developed/made, which could also be used for several other cool purposes by any DIY’er. Kudos to the inventor of that cool little robot/cracker/device. It reminds me of tools/devices used to test QA on touch panels. And I love that it was made with servos and clothes pins, simple and easy.
Without wish to decry [jj]’s achievement in any way, there are quite a lot of mechanical brute forcers targeted at Garmins on youtube – Some pretty fast ones with several fingers, even.
Garmin 4-digit pins seem to be far less memorable than others :(.
>> Here’s my take – It’s not a ‘hack’,
Really? You’re claiming this is the intended purpose for a DVD drive and an HP scanner?
I have a feeling if you asked a group of people what a DVD player is for, 98% of them will tell you it’s for playing DVDs, and the remaining 2% giving smartass answers would still not say “to brute force a GPS device password” :P
Beautiful! Next, where is the ATM-sized robot version… LOL but in all seriousness during NYE I wanted to get some cash but was so loaded I must have punched the PIN like 20 times – nothing happened, OMG at the end it just worked…. :) Terrible security.
this is an awesome HACK
but i dont see why one cant just crack it open and clear the eeprom or factory reset it XP
without looking to in to it , it was said the password is in flash not an eeprom . would be nice if there was a simple i2c eeprom there but chances are he at least looked
well its not exactly to hard to clear any of those with the proper datasheets unless its stored as part of the main IC
i dont know about these brands but i have reset mine that had a strange SPI eeprom that after i 0’ed it out the whole system reset to factory
… i tried reading the thing than was just like “NOAP to confusing”
The same flash that holds the password holds the OS and Maps. Zeroing it out is not the answer.
Factory reset does not clear the PIN. Not sure if its eeprom or flash. This hack is a bit more fun, and I can re-purpose it for other tasks.
yeah there is nothing like a nice brute force!
I like it, he had a boring problem that would take forever to do manually so he built a machine, from junk, to do the job for him, if it wasn’t for thinking like this we’ed still be using slaves. And if you put a capacitance glove fingertip on the end of the pencil you can brute force the touch lock on stolen phones. (Not that anyone would steal phones, of course.)
Actually, slaves were cheaper and more productive than machines at the time. So no, that’s not why we’d no longer have slaves.
Actually slaves ARE cheaper thats the reason for cheap gadgets that comes from countries with “legal slaves”
I think it is more that we now have millions of wage slaves who are given the highest level of technology to do their part of a job that leads to a ridiculously high level of technology for nearly no money. That, and differences in cost of living/ currency exchange rates.
“Fortunately, the people who enter these codes don’t care too much about the security of their GPS devices. The code used to unlock [JJ]‘s GPS was 0248. It only took a couple of hours for the robot to enter the right code; we’d call that time well spent.”
Are you implying that a code of 9999 is more secure
Incredibily there are passwords that are more common than others, take a time to read this: Statistics of PIN numbers: http://www.datagenetics.com/blog/september32012/index.html
what is there on a gps unit that you would want to secure? it isnt a pda or cell phone that can hold secrets and gps now isnt the multi thousand dollar devices they once where
also any halfway decent security will lock down the device if failed attempts more than say 3 to 5 times
It’s not about securing it, it’s about making it less useful to steal. A bike thief is less likely to take a bike without a seat or front wheel. A car with gps tracking.
Which is why this post is glorifying the theft of someone else’s property. Hence how the OP was able to ‘score’ such a deal… Thieves should be executed-slowly.
There is the Home button, which (if entered accurately) could lead the attacker to your house. Think of the case where the car is stolen, and the thief goes to the GPS Home. Perhaps there’s a garage door opener in the car which gives the thief access to your home and its contents. I know it’s rare but does happen. This is a security issue and a tip to consider entering a nearby but incorrect address into your GPS home feature
You forget, your insurance and registration also have your home address on them. 99% of people leave them in the glovebox.
I didn’t forget, and I did provide a useful tip. Plus a GPS makes it easier to locate someone’s home than a printed address,
“A GPS makes it easier to locate someone’s home than a printed address?” Only to a child who doesn’t know how to read, use a map, etc…
I know that I wouldn’t want someone who stole my gps unit (if I had one) to have my home address, friends addresses, work vendor addresses, etc.
It’s also an easy way to keep young kids from accidentally deleting stuff.
As far as theft deterent, it might be effective, but I doubt that most theifs would wait for it to power on and then leave it alone if it’s pass protected.
This is very cool
he used a printer and a cd drive to unlock a gps how is that not a true hack
i personally think this is both ingenious use of imagination, reperpouse of materials and generally cool as fuck
+1 (-10 for all the trolls) Happy New Year
It meets the modern definition. The post is after all about how to make use of stolen property.
@scott bates — that is well put and i agree 100%
to others of interest…
i never seen so much splitting of hairs on a HAD post surrounding the legitimacy of a “hack” — but i am somewhat new to this online community but far from new when it comes to both hardware and software and network hacks.
it is unfortunate that the true meaning of the word hack has been HACKED by our media. now days it is taboo to even associate oneself with the word. but up till the mid 80’s it meant you were innovative, thought out of the box to accomplish work arounds and fix that which had others at a loss. a software author might send their code to a hacker to have it fixed or us commodore users would figure out how to bankswitch 4 megabyes of RAM on a c=64 computer then use this hardware to hack INTO an establishments computer via a unpublished number we found using a program like phoneman JUST to look around explore but NOT to destroy or deface.
so while using a screw driver might to open a can of paint might not be considered a hack…. maybe BENDING that same standard flat blade screw driver to be used to open the can of paint MIGHT BE? i believe the small tool i use for opening cans of paint resemble a very short and bent screw driver of sorts.
as for FAIL and other terms used by teens these days i myself being 44 am often exposed to new words or rather use of words. FAIL SWAG IDK … etc etc IMHO it doesnt mean you are a poser or any way less of an adult to use them but yes you might need to be young at heart to appreciate them and yet responsible enough not to over use them XD
I (heart) U
“Fortunately, the people who enter these codes don’t care too much about the security of their GPS devices. The code used to unlock [JJ]‘s GPS was 0248. ”
How is 0248 any more or less secure than say 9999 or 5248? Every guess has the same probability of being correct. Or are you assuming all attackers are going to enter codes sequentially starting at 0000?
I wonder if any body supplies a “brick” option for passwords. The brick option could be set to a random location above and below the entered password. Brute force cracking would likely hit a “brick” password before the legit password and brick the device.
Yes. They are called self destruct codes and some mil-spec equipment has them. The really smart ones let you keep guessing while they zero the drive.
I’ve improved the speed quite a bit: http://www.youtube.com/watch?v=k_n5W69OdKM