Back in 2013, the NSA ANT Catalog was leaked. This document contained a list of devices that are available to the NSA to carry out surveillance.
[Michael Ossmann] took a look at this, and realized that a lot of their tools were similar to devices the open source hardware community had built. Based on that, he gave a talk on The NSA Playset at Toorcamp 2014. This covered how one might implement these devices using open hardware.
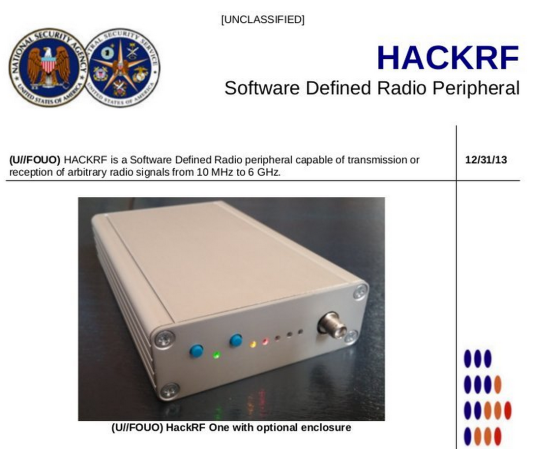
The above image is a parody of an ANT Catalog page, which shows [Michael]’s HackRF, an open source software defined radio. In the talk, [Michael] and [Dean Pierce] go over the ANT Catalog devices one by one, discussing the hardware that would be needed to build your own.
Some of these tools already have open source counterparts. The NIGHTSTAND WiFi exploitation tools is essentially a WiFi Pineapple. SPARROW II is more or less a device running Kismet attached to a drone, which we’ve seen before.
A video of the Toorcamp talk is available on [Michael]’s blog. There will also be a variety of talks on this subject at DEFCON next week, which we’re looking forward to. For further reading, Wikipedia has a great summary of the ANT Catalog.















Reblogged this on Carpet Bomberz Inc. and commented:
Ya’ know, there’s a whole world of contract manufacturers out there and the NSA lets them all bid on these. They do not do all this work on their own in house, they like CIA have front companies that go around seeding the ideas, bids, RFPs that eventually lead to these devices. It’s a cottage industry of sorts of small COMMs outfits making small runs of very sophisticated devices. All in the name of National Security.
NSA guys might have a lot of budget, but they are not stupid enough to have the NIH (not invented here) mentality. They don’t have a Q to invent all their gadgets. They do whatever a hacker would do putting things from sources available to them. If there is open source, good. If not, they buy, borrow, steal or even invent just like everyone else. They do have a lot of smart people working for them though.
So no big surprises there.
If you look at the analyses that people have done on the leaked evidence, you’d know the NSA certainly does have their own version of Q. But many of their motivations are driven by their need to be “deniable.” The devices in the ANT catalog are tagged with whether or not they were built with COTS components, or if they had to custom fab a chip. The reason is if a target finds a circuit board with an unidentified chip on it, they might figure it came from a secret US chip foundry run by the spy agencies. But if the device is built on an Atmel chip, it could have been built and planted by a hacker, a criminal organization, a private eye, a commercial rival, or just about anyone.
10MHz to 6GHz?
So all I need is a setup running at 9 MHz or lower, and I become invisible?
Time to pause and reflect on the “invisible” 80- and 40-metre HF bands.
I feel this would be for eavesdropping on a very specific thing rather than scanning the whole spectrum.
If they knew you were running something on 9MHz then they’d bring out the 9MHz SDR…
or just look at the harmonics to 9 MHz and still find you…
HackRF: 30M – 6GHz
BladeRF: 300M – 3.8GHz
RTL-SDR: 22M – 1.1G (lowest I could find)
USRP: 50M – 6GHz
Funcube: 64M – 1.7G
It’s not that coverage doesn’t exist (Funcube Pro+ is:150KHz – 240MHz) it’s just hard to find. People even make & sell diplexers (frequency shifters) to overcome what I’d call a basic design flaw.
Direct sampling of HF with an ADC was done on the HPSDR “Mercury” with a single 125Msps ADC. The concept seems to have been… overlooked… in newer designs.
Plenty of surplus gunnplexers at 10 GHz and above out there, 24 GHz ones can mess with police radars, so be careful.