What exactly constitutes a cyberdeck is up for debate, but for us, one thing is clear: A cyberdeck needs to look like it’s ready to go to battle. When the machines finally rise up and try to wipe us all out, someone toting around a machine like Cyberdeck Red is probably going to be a sight for sore eyes; clearly, such a person would be equipped to help us fight back the robotic scourge.
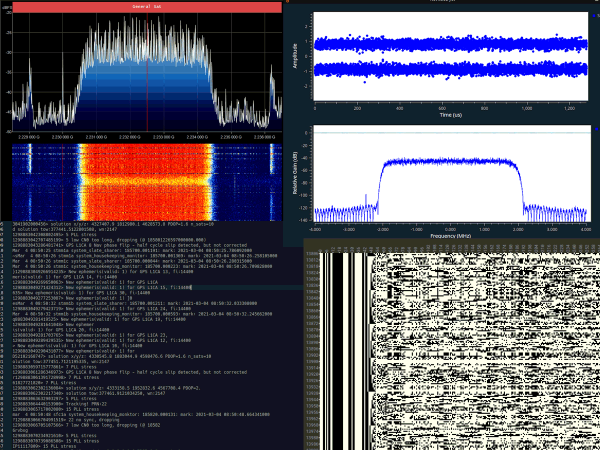
If this cyberdeck looks familiar, it’s for a good reason — it’s [Gabriel]’s second stab at this build. We thought the original was pretty keen, enough so that it won second prize in the 2022 contest. But like many cyberdeck builders, good enough isn’t good enough, and so rather than rest on his laurels, he set about improving a few things. The most visible of the changes are the spiffy new case, which is far less utilitarian than version one, and the new custom-made split keyboard. Things are a little different under the hood too; gone is the Raspberry Pi 4, which was replaced by Latte Panda 3 Delta running Windows. And like the original, version two is absolutely stuffed with sensors and diagnostic gear — a Hack RF SDR for radio work, plus an Analog Discovery 2 which provides everything from an oscilloscope and signal generator to a spectrum analyzer and an impedance tester.
But possibly the most useful feature of Cyberdeck Red is the onboard HDMI projector. The palm-sized, short-throw projector would be perfect for an impromptu combat briefing in an improvised command post, or just watching Netflix. If the machines will allow it, of course.
The 2023 Cyberdeck Contest wraps up August 15, so it looks like [Gabriel] just squeaked this one in on time. We wish him and all the other entrants the best of luck!