With the summer’s big security conferences over, now is a good time to take a look back on automotive security. With talks about attacks on Chrysler, GM and Tesla, and a whole new Car Hacking village at DEF CON, it’s becoming clear that autosec is a theme that isn’t going away.
Up until this year, the main theme of autosec has been the in-vehicle network. This is the connection between the controllers that run your engine, pulse your anti-lock brakes, fire your airbags, and play your tunes. In most vehicles, they communicate over a protocol called Controller Area Network (CAN).
An early paper on this research [PDF] was published back in 2010 by The Center for Automotive Embedded Systems Security,a joint research effort between University of California San Diego and the University of Washington. They showed a number of vulnerabilities that could be exploited with physical access to a vehicle’s networks.
A number of talks were given on in-vehicle network security, which revealed a common theme: access to the internal network gives control of the vehicle. We even had a series about it here on Hackaday.
The response from the automotive industry was a collective “yeah, we already knew that.” These networks were never designed to be secure, but focused on providing reliable, real-time data transfer between controllers. With data transfer as the main design goal, it was inevitable there would be a few interesting exploits.
Infotainment and Telematics
Automotive companies are working hard on integrating new features in to distinguish their products and create new revenue streams. Want a concierge service? You can pay for GM’s OnStar. Need an in-car WiFi hotspot? Chrysler has that built into uConnect for $35 a month. Want to control every aspect of your vehicle from a touch screen? Maybe the Tesla Model S is for you.

There are two main features that are leading to more connected vehicles: infotainment and telematics. Infotainment systems are the in-vehicle computers that let you play music, get vehicle information, navigate, and more. Telematics systems provide vehicle data to third parties for safety, diagnostics, and management.
In order to provide these features, connections between controllers are necessary. For example, OnStar needs to know when your airbags deploy in order to call for help. For that reason, it is networked to the airbag controller.
Regulators are helping speed up the process. Due to the eCall initiative, all new vehicles sold in Europe after 2018 must provide voice communication and a “minimum set of data” in the event of an accident. This means vehicle will be required by law to have a cellular connection, supporting voice and data.
As vehicle get connected to radios, remote bridges to the in-vehicle network are created. The assumption that physical access to a vehicle is required for access to the in-vehicle network no longer holds true.
The “Airgap”
The Chrysler hack took advantage of a vulnerability that anyone familiar with network security would consider trivial: an open port running an insecure service. If you want to know the details of the hack, [Chris] and [Charlie] have published a detailed paper that’s definitely worth a read.
The crux of the vulnerability relied on an assumption made by Chrysler. Their telematics unit had two processors, one connected to the in-vehicle network and one connected to the internet. The assumption was that the airgap between these devices prevented remote access to the in-vehicle network.
Unfortunately, their airgap was made of copper. It was a SPI connection between the two processors, which allows for a variety of commands to be executed, including a firmware update. With rogue firmware running on the in-vehicle network, we’re back to the five-year old issue of in-vehicle networks being insecure.
I had the chance to talk to some Chrysler folks at DEF CON, and they continued to refer to this as an “airgapped system.” The truth is, we’ll never see a new car with a true airgap between the in-vehicle network and the cellular network. New features and regulations demand this level of connectivity.
The Supply Chain
[Chris] and [Charlie] decided to focus on a Chrysler Jeep Cherokee, but let’s not place all the blame on Chrysler. The uConnect device running the vulnerable service was actually made by Harman. Harman is the largest manufacturer of automotive audio and infotainment systems. You’ll find their devices in vehicles from Audi, BMW, Land Rover, Mercedes-Benz, Volvo, Buick, and others.
This is how the automotive industry tends to work nowadays. An OEM, like Chrysler, integrates parts from a variety of “Tier One” suppliers. The Tier One suppliers source parts from “Tier Two” suppliers. It’s up to Chrysler to choose these parts, then stick them all together into a vehicle.
When buying from a range of suppliers, security is a hard problem. As an engineer, you’re stuck with integrating parts that were chosen based on a range of criteria, and security isn’t at the forefront of purchasing decisions. OEMs do not always have the resources to evaluate the security of the products they are purchasing, and instead rely on the suppliers to build secure products.
The other issue with suppliers is that fixes happen slowly. Chrysler could not patch this issue themselves, but instead needed to wait for the supplier to do it. After the patch was complete, they likely needed to perform testing and validation of the patch before releasing. This all takes time.
What’s Next?
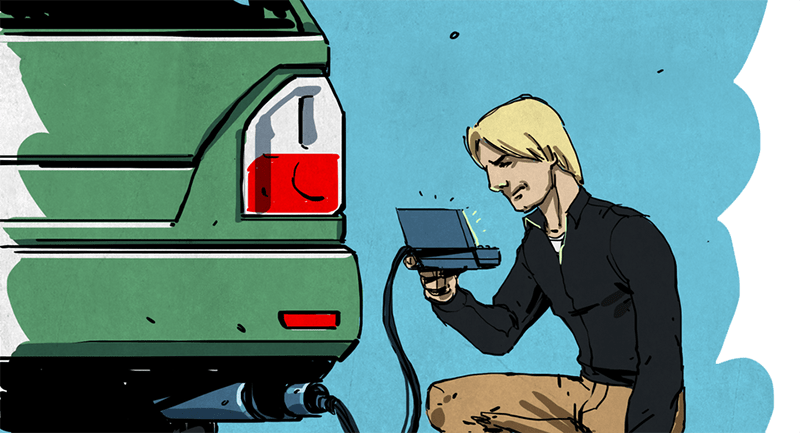
Outside of the security industry, people have been hacking cars for years. Tuners charge money for “chipping” cars to improve performance, remove limiters, and alter settings. The term “chipping” comes from the process of desoldering and replacing an EEPROM chip on old ECUs to change calibration values.
This type of work has good intentions, people pay for modifications to their vehicle. The security industry is more focused on nefarious motives. We’ve seen a few hacks that involve stealing cars by attacking the key fobs, but these type of attacks still require physical access to the vehicle.
Imagine this: your car starts up, and cannot shift out of park. A message appears on the infotainment display telling you to transfer Bitcoins to a specified address to unlock your vehicle. You’ve been targeted by automotive ransomware. Fortunately, we haven’t seen such an attack yet, but with the issues that have been demonstrated, it’s becoming plausible.
Vehicles are also becoming more automated. Advanced Driver Assistance Systems (ADAS) improve safety by giving computers control of the vehicles steering, throttle, and brakes. However, these systems also provide an additional threat to a compromised system.
Another concern is privacy. Infotainment systems have access to location data, microphones, and vehicle information. In regards to eCall, the European Union says “Do you have any concerns for your privacy? You shouldn’t.” We probably should. The good news is that people are trying to protect drivers. DEF CON’s new Car Hacking Village, run by Parsons and CANBusHack, had a strong showing of employees of OEMs and tier one suppliers. Car companies are starting to pay attention.















Figures Europe would go the forced big brother route… didn’t they learn from the last time?
Perfect airgap: From the processor (A) which is on the internet the MOSI line is not implemented to the processor (B) which is connected to the in-vehicle network. B sends regularly a bunch of data to A, therefore you can preserve the functionality.
Security problem solved.
The way SPI works requires both pins to be connected, it can’t just be one-way like traditional UART serial. From Wikipedia: “During each SPI clock cycle, a full duplex data transmission occurs. The master sends a bit on the MOSI line and the slave reads it, while the slave sends a bit on the MISO line and the master reads it. This sequence is maintained even when only one-directional data transfer is intended.”
the processor isn’t going to know the difference between receiving a packet full of 0’s and a grounded pin.
if you only want one-way data you don’t connect the MISO, done.
You could always just… not use SPI. Just for the link between the two systems. No law saying you have to, far as I know. Use SPI within a secure zone, since that’s what it’s good at. Use any old one-way link beween the processors.
Or, just as easily, don’t allow firmware updates to be done remotely! FFS! If you can drive to the garage to get your oil changed, you can drive there for new firmware. How often do cars need new firmware anyway? Except when the existing one has a great big hole in it like allowing remote updates to the firmware.
That means implementing the processor (B) instead of just having processor (A) poll all the sensors in the network directly.
That means the manufacturer spends more $$$, which means the feature won’t get implemented.
All this technology, touch screens, lcd distplays, remote starts, and satellite radios, and when there is something wrong my Jeep still does nothing more that flash a light on the dashboard. I’m happy to know that the ABS and Traction Control is off, but could we utilize one of the displays in the vehicle to say why? No, no, no, you need a $200 tool to tell you which wheel speed sensor is not working. So just replace them one at a time till you get it right. (And, no, the ELM/cheap scanners does not tell you because its not an ECU fault, its an ABS fault)
True, never ever understood why we can have such fancy computers and screens in cars but NO DIAGNOSTICs at all! They could put on some advanced screen, just for reading defects and values would be enough, do not need to clear the faults, just to know what is happening.
Because diagnostic tools in the car takes money from the dealers.
Of course it could be done but the OEMs don’t want you to. Spare parts are a gold mine and why should they help their customers to find a way around it?
That said, it’s of course also about liability. If a car crashes and kills 20 people in the process it doesn’t matter whether you performed some unauthorized repair or not. The result is that 20 people died and the OEM’s brand reputation suffers as a direct consequence. It’s actually understandable that they wouldn’t want that to happen.
They are cheaper than that now; they are just CANbus interfaces, which Bluetooth to your phone. There are a dozen or so of them on the market.
Still, you are right. When Ford debuted their MyConnect system a bunch of years ago, the first question I asked was: Does it have an engine code reader build in? Nope.
Back when Old GM was disintegrating, I was really thinking about starting an new car company with a completely new business model. Just publish the full Service Manuals and wiring diagrams as PDF’s on the website, don’t have service dealerships, sell replacement parts near cost, contract warranties with external shops, etc.
a lot of cars use special software or slightly non-standard interfaces that make the cheap readers useless. it will read ecu codes but any of the other computers on the bus need other tools to talk to them. volvo and saab are a particular nightmare in this way, without a vida/dice (volvo) or a techII (gm/saab) you can’t even get the misfire data for the cylinders. they support the absolute minimum number of obdII that they are required.
A cheap universal scanner will only do about 10% of what is possible through the diagnostic port. Each manufacturer has their own proprietary interfaces outside of the standard OBDII emissions diagnostics.
Just to play devil’s advocate here, but displaying problems isn’t quite that easy. If you put diagnostically valuable information on the screen, it may not be usable to average people, and may distract them from their task. A good error should be minimalist and say what you must do; optionally it can say what’s wrong. “Service needed immediately, airbag system failure.” is a good message, because it tells the driver what to do, and indicates it’s something about safety. The message to the driver shouldn’t provide all the diagnostic codes or information needed, because the driver generally can’t do anything about it at that time. What do you expect the driver do if it says “Airbag sensor 27 failed to respond to power on self test”? That’s what diagnostic log information is for.
Shouldn’t there be a way to display all that log information on the screen via a “Show me diagnostic logs” menu option? After all, it seems like it would be essentially free to implement. But if you’re going to a dealer, the dealer needs the ODB-II tools anyway in order to read data from cars that don’t have a GUI. So there’s not much point in adding the extra software to display it on a system the mechanic doesn’t need and won’t use, especially if that extra software could be buggy. This whole article is an indictment about vulnerable car systems; asking them to add more buggy software won’t help vehicle security.
“But if you’re going to a dealer,”
That’s my main contention. As a do it myself kind of person, I like to keep my trips to the dealer for more complex issues than a failed sensor.
Some of can still work on cars. .
Yeah go to a dealer who then proceeds to rip you off, doubly so for women and seniors. They know they have a monopoly and will bend a customer and suck their wallet dry.
I’ve dealt with enough dealer service shops to totally distrust those working back there.
One word greed.
** not on this topic, but it’s bugging me ***
HAD you should have more variety of cartoon people on your site. I’ve seen male & female, Caucasian/European, & Asian. I don’t see many Black, Hispanic, etc. Thanks. Just an observation from my limited exposure to your stories.
Make every one of them the same geeky white guy for all I care. I don’t spend a lot of time worrying about diversity in the illustrations on HaD — it’s a shame that anyone thinks it’s worth the effort to track…
I’m not “tracking” it. For the most part I don’t give it much thought. That does not mean that that it is a worthless endeavor. I like to see a variety of projects, ideas, people, etc. It’s a shame that you don’t value other’s opinions and thoughts.
It is a completely worthless endeavour and it is only people that note the difference that make problems with it. I have absolutely no interest whatsoever in race / religion / colour, to me they are just (probably) human and have something that is worth reading to say.
Once you start selecting people because of their race / religion / colour you are prevented from selecting the optimum for the job and it makes me sick to have to conform to such ridiculous criteria. Furthermore this site is not one where it can ever be relevant in the slightest so take your observations and put them away. << Polite that.
The reason for overt positive discrimination, is to cancel out covert negative discrimination. There are still people in the world who would refuse to take the optimal candidate for a job because of his sexual preference / race / religion / etc. Unfortunately those people don’t tend to publish that fact in their company policies. So positive discrimination is an admittedly inelegant way of balancing things back in the direction of fairness.
If you can think of a better way, please let us know. Obviously “Stop bigotry” would be a good one, but that’s proving difficult to implement.
Assuming all social groups contain an equal proportion of people suited for a particular job, then if the people doing those jobs reflect the makeup of society, things overall are fair.
One day soon this won’t be an issue, bigotry’s not as popular as it used to be, and it used to be very popular.
You’re noting patterns — the very definition of tracking. Because you might not have used a spreadsheet doesn’t make it any less.
And I do believe all opinions have value, it’s just that this particular opinion has an assessed value that approaches ZERO. Mind you, that’s _my_ individual assessment of this particular thought — others may value it differently (as, clearly, you do) and you may have other thoughts to which I assess a great deal of value.
Considering a single opinion valueless does not render me incapable of valuing other’s thoughts and opinions. That brush is a little too broad for good painting there, pardner!!
The diversity police has arrived, they take such things very serious
Well spotted, although I’m not sure if noticing or not noticing is the current best practice regarding race :P All I thought when I saw the cartoon was ‘man, these illustrations are so cool…’. I don’t think it’s a must-fix issue, but it would be nice to see a little more colour! And hey, while (s)he’s at maybe the artist could work in one of us poor, outnumbered, under-represented red-heads :)
Hmm, I guess it couldn’t possibly be because the vast majority of this site’s readership are caucasian and asian. lol
Please include aliens. Grays, Nordic longhairs, insect types, Reptilians, and light bodies. Oh and don’t forget The Mice.
+1 for Aliens!
What about Racoons, they are nature’s hackers. Besides they are cool looking. They look like old school criminals.
Seconded.
I think as far as racism goes, the little drawings on HAD aren’t a major source of oppression or inequality. There’s probably more worthwhile things to fix first.
It’s the year of fake car hacks. Every single one had prepped the car for the hack, none of them are able to hack a random car on a car lot or parking lot.
are they finding real holes? yes, are they actually exploitable without having full physical access to the cars for a few hours? no.
Windows 10 is completely insecure if I had it over to a hacker with all passwords and physical access.
Seriously,
Go watch the DefCon Videos on this. Before making a comment such as this one.
I have, and had a friend there they have not demonstrated a hack on a car that they did not already have information about or did not prep.
They did say that instead of finding the address of one jeep they could just ‘hack them all’!
Have you not been reading the news?
I’ll just place this here…
http://www.wired.com/2015/07/hackers-remotely-kill-jeep-highway/
Remotely killed without any prior access needed… and from long range!!!
Hmmm, maybe that is what the mystery switch on the wall of my house does….
It kills a car engine in New York City…
Damn shoddy electricians!
There is a whole realm of “car hacks” that really needs to happen, which is distinctly different from attacker penetration of the system.
What I am talking about falls somewhat under the realm of citizen science. There needs to be cheap and/or easy ways to do things like check the emissions of a vehicle. Don’t bother going to a smog test station, they are universally terrible, and just know how to push the buttons.
There was a story passed around a long time ago about how someone measured the emissions from a leafblower and a performance-tune F150 truck, and the leafblower output more emissions. Their data and methods were kind of hokey, and the story fell by the wayside.
So, an exhaust sniffer that can measure NOx, SOx, CO, CO2, O2, and HC’s would be a great tool to have to audit these things, and really expose how in this day and age, while there are Mercedes that leave cleaner air that then take in, and Teslas with no tailpipe at all, there are still allowed to be leafblowers, lawnmowers, and motorcycles that output emissions equal to 1000 (or more?) vehicles with proper emissions controls.
There are so many cars and they burn through so much gas that leafblowers, lawnmovers, and motorcycles etc. are a drop in the oceans that is not worth the cost or effort of thinking about.
measuring exhaust accurately is high maintenance equipment and only if you can measure absolute amounts does it really make much sense between different things.
Actually, those small engines produce so much more pollution per unit that they actually are significant problems. Another significant source of urban pollution is people with fireplaces and oil/wood/pellet burning heating systems, which produce particulate emissions similiar to second hand tobacco smoke.
I remember my dad used to get rid of old engine oil by letting it sediment and then just mixing it in the lawnmower fuel over the summer. The engine was so sloppy that it just ran better with the “additives”.
considering the car companies took the “THAT’S OUR DATA” stance with the systems they embedded in the vehicles, I can’t see this getting any better for a long time
Hence why you ignore them.. If data is produced by an item I own.. Its MY data.. and I don’t give a damn what you have to say about it..
we car hackers/tuners do a lot more than that, we add features, remove features, improve on existing programming, fix bugs,, make the ecu do things that it was never designed to do.
i (as can many others) can completely reprogram a large number of ecus from the obd ii(or older) port with entirely new software, even a new OS, add backdoors , use the ecu for something else etc etc, most of the car hacks i’ve seen recently have either been attack on external systems or replaying bus messages.
its certainly been interesting watching a different field start off with the basic stuff and work up over the last few years though.
anyone advocating the legally-mandatory internetization of cars should be charged with attempted aggrivated reckless endangerment with a dangerous weapon.
how many horses does it take to kill a man? less then one?
… the aggrivation comes from the rick astley playing lol
*shudder* Now THERE’s a nightmare scenario. I think if I were driving a car and someone hacked it to Rick-roll me, I’d most likely put it in gear, aim it at a river, and jump out. Drown it! Drown it to death!
I agree as there is no way to put big brother in the passenger seat without also letting hackers on board in mass. Plus who would want big brother riding shotgun everywhere they go as nothing good can come of it?
I’m wondering how soon will we receive our vehicle license plates with an RFID tag embedded in them, and RFID readers beneath the pavement at every intersection.
Putting mobile phones in cars is much cheaper. You just triangulate from the cell towers.
RFIDs are already in your car. As many as 4. One in each of your tires. All the gov’t needs to do is to place readers and they can track you everywhere you go in real time.
Coming from a true car enthusiast and tinkerer these car companies need to do what Apple, Mozilla, and Microsoft do. They need to offer a bug bounty. People are going to hack car systems regardless of a bug bounty or not, at least the car companies can offer something enticing for said hacker to submit the issue to them and receive a reward. I think the bug bounty is a nominal fee when compared to the severity of injury that could be caused by some of these hacks.
Still, admitting to knowing about a bug introduces liability issues. Nobody’s life, thank the gods, relies on Microsoft writing half-decent software. Cars are very different.
And that’s without bringing lawsuit mentality into it, I’m sure you can imagine that for yourself.
@Jake
That’s a great idea but a bug bounty it will never work until we do something about Section 1201 of the DMCA.
A bug bounty wouldn’t work thanks to Section 1202 (anti-circumvention law ) of the DMCA (Digital Millennium Copyright Act). This section of the DMCA makes it a federal crime to by-pass the protection on these device’s which is almost certainly necessary to find these hacks/bugs. That’s of course assuming the vendor has put some form of protection into their products to reduce possible exposure but I can’t imagine any company not doing this.
I have not read the paper referenced and so it may be that there was no need to by-pass or break any protection on these devices but I would be greatly surprised if they didn’t have to get passed some level of DRM protection to produce these hacks. Even if they didn’t have to deal with any DRM protection you can bet that the first thing these vendors will do to prevent any future exposure of hacks/bugs in their products will be to add DRM protection.
Until these corporations can be held liable for not providing adequate protection in their products from these kinds of hacks nothing is going to change; its going to be business as usual.
I’m really surprised we’ve not seen any aftermarket drop in replacements for car computers.. or at the very least custom firmware being written to address these issues ourselves rather than rely on the manufacturers.
There is in the performance modification industry such as the Accel DFI.
That is a one-way ticket to voiding your warranty, Atwas911. Not a lot of people would pay to fix an issue or problem that should have been fixed before they purchased the automobile. Not saying I agree or disagree with you, just stating what the publics reaction would be.
One of the biggest problems here is regulators mandating stuff like telematics of course some of the big brother features they want almost forces a connection to the ECM which of course in the cut throat auto industry will be done in the cheapest and most unsafe manner possible.
People need write their political leaders and say no to mandates for such technology even hold political demonstrations against it and call for the firing of the regulators pushing for it.
The 2010 paper by Koscher et al was not about physical access; they described numerous attack vectors that didn’t require physical access to a vehicle (“In our car we identified no fewer than five kinds of digital radio interfaces accepting outside input”), including radio, OnStar, tires (!), and others. They went further the following year and compromised their cars via all the above methods in their USENIX paper (http://www.autosec.org/publications.html) as detailed in the paper.
The latest Jeep exploits were basically a retread (sic) of the above on a different vehicle type.
Professional cars thieves have been exploiting keyless entry and start for years.
Some thieves even specialize in stealing only cars with push button start as there is no need to damage the column to extract a keylock.
http://spectrum.ieee.org/cars-that-think/transportation/advanced-cars/car-thieves-use-handheld-electronics-to-steal-keyless-cars
Am i the only one not getting the dislike toward ‘insecure’ (open) car networks? I love the potential that hacking my car has.
I want my car software open, just like my OS, my phone, etc etc.