As if you needed any reason other than “just for the heck of it” to hack into a gadget that you own, it looks like nearly all of the GSM-to-IP bridge devices make by DBLTek have a remotely accessible “secret” backdoor account built in. We got sent the link via Slashdot which in turn linked to this story on Techradar. Both include the scare-words “Chinese” and “IoT”, although the devices seem to be aimed at small businesses, but everything’s “IoT” these days, right?
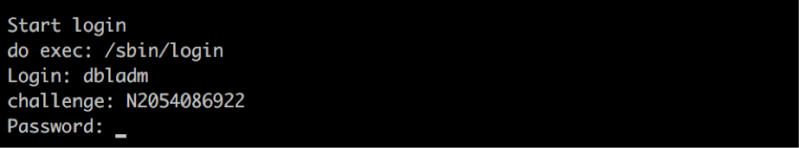
What is scary, however, is that the backdoor isn’t just a sloppy debug account left in, but rather only accessible through an elaborate and custom login protocol. Worse still, when the company was contacted about the backdoor account, they “fixed” the problem not by removing the account, but by making the “secret” login procedure a few steps more complicated. Which is to say, they haven’t fixed the problem at all.
This issue was picked up by security firm Trustwave, but they can’t check out every device on the market all the time. We may be preaching to the choir here, but if you’re ever wondering why it’s important to be able to break into stuff that you own, here’s another reminder.















Can’t even get to the DblTek website since our web filters have classified it as serving malware…
We will keep getting that until there is a law that requires you to disclose your source code (complete, verifiable and letting you build the firmware) before you can sell anything to the public, or install anything in the public infrastructure. Just like the airplanes. And no, that doesn’t mean the code needs to be released under an open source license — it can still be proprietary and protected by copyrights. We just want to be able to inspect it.
You say that will only make the backdoors move into the hardware? That’s an excellent point! Next step is to add the same requirement for hardware designs. You want to sell us something, tell us exactly what it is and what it does.
‘MERICA !
you make capitalized variation on my nick? :(
yes
sOmeone needs to do something about this name capitalization issue.
That sounds like a great idea! You for president 2020! The issue is were american. Were going to bitch about it being crappy, but still buy it anyways cause its cheap in most cases. Until we stop buying and using the inferior products. They will continue to rule the world.
Nice idea but will not work. I’m a software dev, why should I work for free? Because that is what will happen with your plan. Copyright does not stop stuff being copied. Most developers and their employers do not have the funds to protect their software. And if they do by the time it comes to court the damage is done. It’s hard enough to defend against piracy without giving the source code away.
Do you want to work for free????
I understand your point. But then there is only one way to solve this problem: Forbid such backdoors by law and make it a criminal offense (e.g. similar to fraud) to sell such tainted products. So if anybody finds such a security hole the maker or seller is personally responsible for any possible future damage caused by this.
Also not a very practical solution, but a different one from disclosure of source code.
Good luck enforcing your American law in China.
Besides, you think the American stuff doesn’t have back doors? Course it does. Just for Prism, not the Chinese.
What good does releasing the source code do? They’ll just release the back-door-free source code, but the stuff they flash onto the devices will still have the back door.
That’s where the “verifiable” part comes in. You build it and you compare the checksums. Or, if you are paranoid, you build it and reflash yourself, to make sure.
Stories of compilers which insert backdoors aren’t uncommon, so compiles to the same binary proves nothing. But realistically, most users won’t do this anyway, only those already savvy enough to understand the security.
I just want to point out that horrible binary blobs don’t prevent stuff from being copied either. So it doesn’t really put you in a worse position. I am a software developer too, all the code I write is publicly available and guess what — they still pay me for writing more of it. So apparently it is possible to make a living by writing new code, instead of re-writing the same thing again and again because it can’t be easily copied.
Think of the poor manufacturer! Any “fix” would remove their backdoor. how can they steal info/comply with alphabet agencies without backdoors?
This is just another reminder that you should always just build it yourself. If this is aimed at business customers, you can bet the purpose for the back door is industrial espionage. When Intel comes out with their first new CPU designed and built in the factory they plan to build in Arizona (I think that’s where it is supposed to go), I will finally upgrade from my trusty i7-3930K. I really hate the idea that all my stuff could have ICs in it that will reach out over the internet and send all my data to China.
Yeah, I understand that I am not important. I know China wouldn’t be interested in knowing anything at all about me. I also know that there is nothing on my computer or any of my devices that I would mind anyone else in the world seeing/knowing, but I cannot, in principle, allow myself to be complicit in allowing China or anyone else to spy on me, my family, or my nation. I also hate to think of all the people in China who are using goods sold by American companies that are being utilized to locate, spy on, and eventually “rendition” those people (“dissidents”).
That is why if I ever want a smart thermostat, I’ll build it myself. If I ever want an IP camera to monitor my home, I’ll build it myself. If I can’t build it myself, I’ll be happy to do without it.
Lucky you for living in the USA. They’d never spy on anyone.
Oh, and anything I build will be behind a firewall that disallows all traffic from the IoT device to the internet. I will then just open an ssh tunnel to my router that would allow me to access the thermostat or camera as if I’m on the LAN. This is how I access the mysql database for my email to add throw-away aliases for creating web accounts.
I use JuiceSSH on my phone to create SSH tunnels to my VPSes. I also created my own dynamic DNS service with the help of Linode’s API, where I have my domains pointed (same could be done with other cloud providers). So I could basically create a subdomain that points to my router, and then I could utilize SSH tunnels or a VPN to safely access my IP camera or thermostat without those devices being able to send data out as long as the router I built isn’t hacked.
This isn’t perfect (because the router PC is still full of Chinese backdoors), but it at least makes it harder, and would require an actual human being to get through.
Youre afraid of China-build-in-backdoors, while the USA is doing the same on a great scale in the “fight against terrorism”? Please readjust your paranoia.
At least in the USA you can find out who owns the company and take them to court, that isn’t the case in China. Even then it will probably end up being the Chinese goverment who has ultimate control of such companies and they have sovereign immunity so you can’t even take them to court in the first place, and even if you could they would ignore any unfavourable ruling.
Don’t kid yourself that the playing field is even.
“Echo” is a fool, or a communist shill.
“At least in the USA you can find out who owns the company and take them to court”
Not necessarily true, through the use of LLC’s and other legal means it is actually not that hard to hide ownership of a company in the united states. sure it is feasible if you have some good lawyers and alot of money, but if your just an average joe, well good luck taking a multimillionaire to court unless you find a lawyer that will take your case on contingency of winning.
the main difference between the US and China is that the people in china are upfront about who controls the power and because of their culture the majority of the population is ok with it (not everyone). In the us, the powerful hide behind lawyers and money and because of the culture the majority of the population is ok with it.
“Don’t kid yourself that the playing field is even.”
no where did he say that the playing field was even, the methodology in the US is different because of their physical location and how the majority of internet traffic still runs through their borders, there fore they dont need to make IOT things, they can just sit on the major through points and collect traffic that goes by. Even if it is encrypted, they will just keep it to decrypt it later.
““Echo” is a fool, or a communist shill.”
calling people names solves no problems and is an indication of weak logic in your arguments as you show that you are trying to get people thinking emotionally rather than logically. personally i think that you are above that.
That is utter bullshit there are enough big powerful, well funded, groups in the USA to launch action against any party that is seen to be acting unlawfully. Even the NSA finds themselves having to deal with them. There is no chance of taking such action against totalitarian states.
So I guess that makes you a fool or a shill too, and if you don’t like the label try acting in a way that deserves another.
For evidence that you are talking crap, these guys can and will go after anyone they legally have a right to go after, https://www.eff.org/ and if you didn’t know they existed you really need to stop sharing your opinions in public until you know something about the subject.
Who owns the company? Do you mean the shareholders, or the CIA who tell them to insert backdoors? :P
USA law does give consumers of products rights, this is not the case in China or similar states, this is the same thing that was originally pointed out and there is no amount of trolling that can change that fact.
I don’t want the USA spying on me, either, but right now everything is made in China. As for US spying, I just give up. Chances are that they can read AES encrypted data in real time, or at least rather quickly. I doubt that my SSH tunnels would be much of a hurdle for them to jump. In the face of this, I don’t know what I could possibly do. At least with the Chinese I feel like I can do something about it.
As Dan said, if I had ever done anything that was to be used against me in court, it would be able to be thrown out in court unless they got a warrant to collect that info. The USA is also not going to spy on me and then give any of my intellectual property to some company, while the Chinese government has its fingers in much of the industry in China. They will give IP to a company that is run by one of their generals or by some high-ranking communist party official.
“I don’t want the USA spying on me, either, but right now everything is made in China.”
I am pretty sure USA agencies and firms have the requisite knowhow for making IC’s, if you really wish to be protected from Chinese built hardware, why don’t they help the US public defend itself and possibly even compete against the Chinese by showing step-by-step instructions for building our own hardware?
On China vs. US: Chinese espionage seems to mostly be aimed at industrial / defense espionage, while US spying seems to cast a broader net. I’m not making any judgement calls here.
But as for “it would be able to be thrown out in court unless they got a warrant to collect that info.” Counterpoint: Parallel construction.
You MIGHT want to search about Intel Management Engine, and that it can talk to Intel when your computer is turned off, or that no one knows exactly what it talks with intel..
LOL
I was thinking the same thing. Now AMD is adding a variation of that to their new processors which i also don’t like,
Yeah, that is another issue we’ve been living with for a long time, now. That is going to be a problem no matter where the CPU is built. It is just another case of things you don’t have anycontrol over. At least in the future we might be able to choose CPUs built in the USA.
They will still spy on you, and with BIOS now being regularly stuffed in a 16-32MB Flash, there is lots of space for extra code, any mobo OEM can spy on you if they want, you can mod the BIOS and disable some things, but you can never disable ME Firmware or your computer wont turn on..
The real reason it was added is so that they can sell the same silicon for say a 12 core CPU and 2 core CPU and have the ME disable what was not working/bought. But there is nothing stopping a secret FISA court order form ordering Intel/AMD (both US companies) to use these for anything and everything since it is a separate CPU with full access to all RAM, all devices and literally everything in a PC. It can be used as a full access back-door.
Nah, you can disable extra cores with something as simple as a fusible link, or a laser cutting a trace, or a couple of bits of EPROM, etc. You don’t need an entire extra CPU complete with network and full RAM access. The IME is entirely for fucking with people remotely. Well, it’s so broad that it can be used for pretty much anything.
But its the ME that manages things like if you have Vpro or not, or if your cpu as HT or how much does it boost under use and whatnot….
There is a bugged micro-code that allows for overclocking laptop Haswell SKU’s…
This isn’t how nation states build backdoors, its probably been put in by someone at the company who personally wanted to have some fun or its there for support purposes, yes we should talk about the stupidity of it but blaming *.cn for it isn’t thinking the problem through.
Its much less damaging to a company of countries reputation to introduce a known bounds error than something that looks like a backdoor out of a movie. In your fear of .cn I think a lot of you are seeing shadows. Sure countries spy on one another, its in their populations best interest.
Backdoors like this should be illegal, I know sometimes there are genuine sloppy code backdoors but this is outright disgusting. I really hate companies/governments that think they are entitled to know what I was doing today or if I checked my email etc. Governments are destroying the internet with their spying and forcing companies to add backdoors to their software. When you go to the ballot box when so you ever see flyers about “more spy powers for gov” never!! that is because we don’t live in anything close to real democracy.
“Governments are destroying the internet with their spying”, except there is nothing new in what they are doing. Right back to the BBS days they were distributing “warez” with backdoors knowing how widespread the copying of software was.
“Here have the latest whatever, and look we even made a special crack and keygen for it so you get the full version for free….”
Now it is “Here have some incredibly cheap hardware with goverment subsidised shipping costs that no honest company can compete with…”
See the pattern?
I know they have been doing it for years but because the internet is so important to most peoples lives now that breaking into their devices for data mining purposes is starting to get scary. Technology today allows algorithms to find patterns in our activities along with great computational power, I think the government is invading privacy too much. They tell us it’s because of terror attacks but when was the last terror attack stopped by using online intelligence? how many lives have been saved vs how much is spent spying on your own citizens? It doesn’t make sense if you invested 5% into health care rather than spying you would almost certainly save 1000’s more lives. so that leaves you to think why? Why do they want to know about us? what is the net benefit?
“when was the last terror attack stopped by using online intelligence?” Well that you can never know, otherwise the methods and or sources would become compromised.
In a nutshell your thinking is overly simplistic and you are comparing incomparables. This says nothing about your world view, it just prevents you from adequately justifying it in a logical and factual manner.
The internet is only ‘important’ to those doing business. Any individual who absolutely MUST be online should seek professional, psychological help. It is not a requirement of life that one must post duckface 12-15 times per day, or check that bobcat109 has sent yet more photos of his cat. Anyone believing that internet access is a basic human need deserves to die in the Siberian cold..and is probably under 25 years of age.
Most jobs these days are posted online only (at least in here in the UK), I understand what you are saying there is no need for social media but the world is slowly changing and you are expected to have an internet connection.
You’re correct we do not live in a real democracy, and have never caimed such. Check this site out. http://www.todayifoundout.com/index.php/2014/01/united-states-republic-democracy/
I understand we don’t live in a real democracy but I do think our elected officials should try their hardest to vote for thinks they believe their constituents would favour, Not what they or their party favour.
This is stupid pedantry that has nothing to do with the topic at hand.
It US is not really a true democracy, any more. https://www.youtube.com/watch?v=mw2z9lV3W1g
I would be more scared if it said Russia :O
It’s a backdoor. Once they’re in the wild, they respond to whoever logs in. There is no nationality filter.
They got interesting test gear: http://www.dbltek.com/products/TSA4G1.html (~$500)