You read about well-publicised security exploits, but they always seem to involve somebody with a deity’s grasp of whatever technology is being employed, as well as a pile of impossibly exotic equipment. Surely a mere mortal could never do that!
Happily, that’s not always the case, and to prove it [Gonçalo Nespral] replicated an attack against RF devices such as some garage doors and motor vehicle locks that use a rolling code. His inspiration came from a device from2015, that encouraged the owner of a key to keep transmitting fresh codes. It did this by swamping the receiver of the car, garage door, or whatever with a strong slightly off frequency signal. This would cause the lock to not work, so the user would try again and again. The attacker listens with a very narrow bandwidth receiver on-frequency that is good enough to reject the jamming signal, and can harvest a sequence of the rolling codes enough to compromise it.
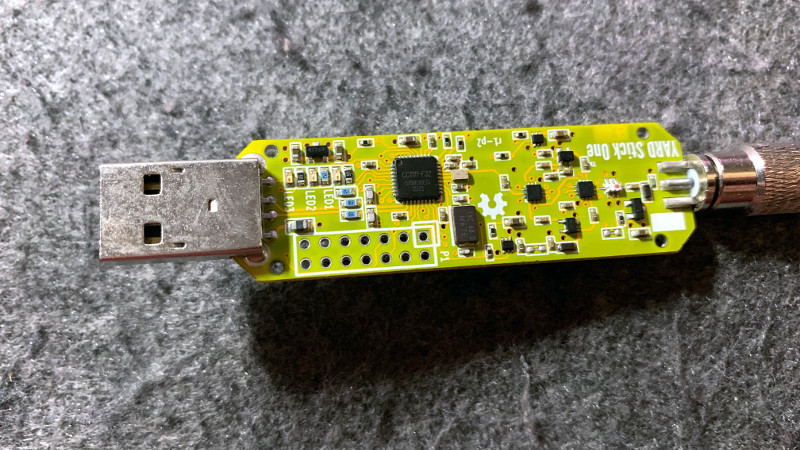
[Gonçalo]’s set-up uses a YARD stick One transceiver dongle as its transmitter, and an RTL-SDR for receive. A GNU Radio setup is used to retrieve the key data, and some custom Python code does the remaining work. We wouldn’t advocate using this in the wild and it could conceivably also gain you access to another car with a flashing light on top, but it’s an interesting exposé of the techniques involved.
Rolling code keyfob attacks are something we covered a few years ago, back when these attacks were all shiny and new.















All you have to do is make sure the vehicle honks or flashes to completely mitigate the attack…
These systems all use the same seed-state as the key transponder and it’s usually stored in a SKIM or BCM module. You can disable it in newer systems because it just sets a state in the ECM to enable fuel management. It’s never effected TCM.
Old systems the SKIM or BCM actually controlled ground to ECM so you couldn’t just use ODBII or a plug ‘n’ play ECM to defeat it, but you could hotwire it..
The tool to write a ECM is like 3k USD, and there have been weaknesses found in ciphers, but the government jumps on the researchers..