Even if you wouldn’t describe yourself as a history buff, you’re likely familiar with the Enigma machine from World War II. This early electromechanical encryption device was used extensively by Nazi Germany to confound Allied attempts to eavesdrop on their communications, and the incredible effort put in by cryptologists such as Alan Turing to crack the coded messages it created before the end of the War has been the inspiration for several books and movies. But did you know that there were actually several offshoots of the “standard” Enigma?
 For their entry into the 2019 Hackaday Prize, [Arduino Enigma] is looking to shine a little light on one of these unusual variants, the Enigma Z30. This “Baby Enigma” was intended for situations where only numerical data needed to be encoded. Looking a bit like a mechanical calculator, it dropped the German QWERTZ keyboard, and instead had ten buttons and ten lights numbered 0 through 9. If all you needed to do was send off numerical codes, the Z30 was a (relatively) small and lightweight alternative for the full Enigma machine.
For their entry into the 2019 Hackaday Prize, [Arduino Enigma] is looking to shine a little light on one of these unusual variants, the Enigma Z30. This “Baby Enigma” was intended for situations where only numerical data needed to be encoded. Looking a bit like a mechanical calculator, it dropped the German QWERTZ keyboard, and instead had ten buttons and ten lights numbered 0 through 9. If all you needed to do was send off numerical codes, the Z30 was a (relatively) small and lightweight alternative for the full Enigma machine.
Creating an open source hardware simulator of the Z30 posses a rather unique challenge. While you can’t exactly order the standard Enigma from Digi-Key, there are at least enough surviving examples that they’ve been thoroughly documented. But nobody even knew the Z30 existed until 2004, and even then, it wasn’t until 2015 that a surviving unit was actually discovered in Stockholm.
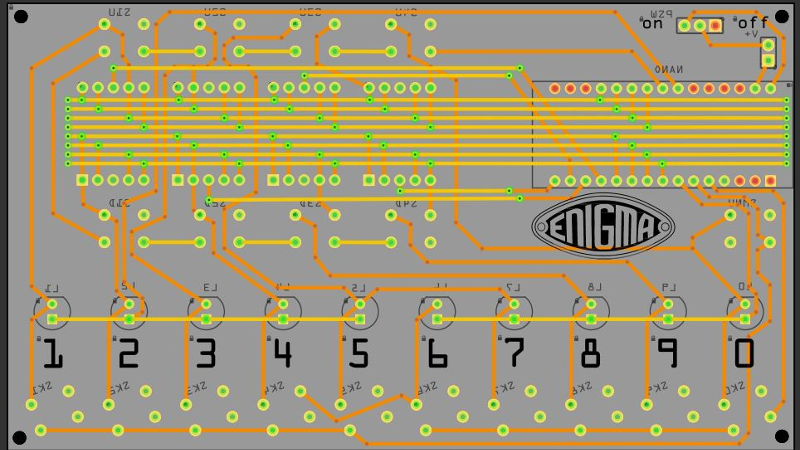
Of course, [Arduino Enigma] does have some experience with such matters. By modifying the work that was already done for full-scale Enigma simulation on the Arduino, it only took a few hours to design a custom PCB to hold an Arduino Nano, ten buttons with matching LEDs, and of course the hardware necessary for the iconic rotors along the top.
The Z30 simulator looks like it will make a fantastic desk toy and a great way to help visualize how the full-scale Enigma machine worked. With parts for the first prototypes already on order, it shouldn’t be too long before we get our first good look at this very unique historical recreation.


















Just a short reminder. Turing did no crack the Enigma code, the polish secret service did who passed it to Brits when Germans occupied Poland. Turing to his credit managed to automate decoding of messages and speeding it by orders of magnitude in time.
Where does it say it was Turing’s accomplishment? Or do you just post this on anything that mentions the Enigma to be a pedant?
Enigma’s cracking is widely misrepresented in the West and attributed to the British, while ignoring the contributions made by the Polish. Understandably, the Polish are a little pissed off at that, and are trying to straighten out the record in public discussions.
Just a short reminder. Turing did crack the Enigma code for the Kriegsmarine, while the Polish were successful for a period of time at deciphering the message keys for both the Luftwaffe and the Heer. Both use different techniques and both Alan Turing and Marian Rejewski deserve credit for cracking the Enigma code.
Don’t forget about Henryk Zygalski and Jerzy Różycki, both working with Rejewski to crack Enigma machine. Polish Bureau of Cyphers cracked the commercial Enigma before 1931, albeit that machine was much simpler. Also they had that machine. In 1933 Różycki and Zygalski began working with Rejewski on creating methods to decode Enigma keys. By the January 1938 Bureau of Cyphers was able to decode 75% of all Enigma messages, but with more people working they could bump that number to 90%. In middle of 1938 Rejewski created his bombe to compute Enigma keys in less than 2 hours, but later Germans changed their machine a bit and changed the procedures making bombe much less useful. Turing’s bombe was partially based on the Rejewski design…
Comments like Afzf and SATF1V3s are reasons I read this site, had never heard of Marian Rejewski before
I cant see any source code on their hackaday project page? Or is it just an advert for their product?
https://gitlab.com/arduinoenigma/enigmaz30simulator
It’s linked on the sidebar.
Now I’m thinking of encoding alphabetical characters in 3-number octal groups and using eight or nine for control characters……..
I’d be interested in knowing what types of all-numeric messages were sent with this device. Numeric codes, typically with four of five digits, are often used to send a standardized set of messages. 5609, for instance, might mean “Reinforcements are on the way.” But the sheer number of those messages mean that code books have to be distributed, code books that an enemy might get their hands on. A simple numeric encryption device would allow those numbers to be encrypted and make reading those messages more difficult. This device would also work quite well with the numbers stations that still exist on HF radio.
I also wonder why numbers were encrypted as numbers. In Morse Code numbers are long—a combination of five dots and dashes. It’d be much more efficient to send them as short letters such as “e” (dit) and “a” (dit-dah). For encrypting, the user would enter the number. For decrypting the key would also contain a letter and he would enter that.
You can find more about the Z30 here: https://cryptomuseum.com/crypto/enigma/z/index.htm
—-
For those who like breaking codes, today (June 17, 2009) the ISS will release three ham radio satellites that will send encrypted numbers of listeners to decrypt.
https://qrznow.com/ham-radio-satellites-to-deploy-from-iss/
http://birds3.birds-project.com/document/amateur/
It’s actually 2019 now. Let me know if you need to get your time machine recalibrated, I know a guy :)