Things might be getting a bit dicey out in Jezero crater for Ingenuity. The little helicopter that could is starting to have trouble dealing with the thinning Martian atmosphere, and may start pressing against its margin of safety for continued operation. Ingenuity was designed for five flights that would all take place around the time its mothership Perseverance touched down on Mars back in February, at which time the mean atmospheric pressure was at a seasonal high. Over the last few months, the density of the Martian atmosphere has decreased a wee bit, but when you’re starting with a plan for a pressure that’s only 1.4% of Earth’s soupy atmosphere, every little bit counts. The solution to keeping Ingenuity flying is simple: run the rotors faster. NASA has run a test on that, spinning the rotors up to 2,800 RPM, and Ingenuity handled the extra stresses and power draw well. A 14th flight is planned to see how well the rotors bite into the rarefied air, but Ingenuity’s days as a scout for Perseverance could be numbered.
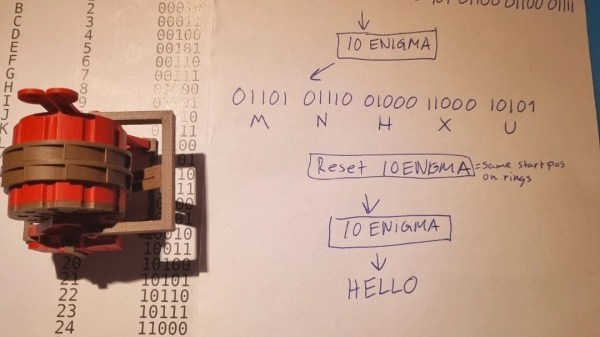
If you thought privacy concerns and government backdoors into encryption technology were 21st-century problems, think again. IEEE Spectrum has a story about “The Scandalous History of the Last Rotor Cipher Machine,” and it’s a great read — almost like a Tom Clancy novel. The story will appeal to crypto — not cryptocurrency — fans, especially those fascinated by Enigma machines, because it revolves around a Swiss rotor cipher machine called the HX-63, which was essentially a refinement of the original Enigma technology. With the equivalent of 2,000-bit encryption, it was considered unbreakable, and it was offered for sale to any and all — at least until the US National Security Agency sprung into action to persuade the inventor, Boris Hagelin, to shelve the HX-63 project in favor of electronic encryption. The NSA naturally helped Hagelin design this next generation of crypto machines, which of course all had backdoors built into them. While the cloak and dagger aspects of the story — including a possible assassination of Boris Hagelin’s son in 1970, when it became clear he wouldn’t “play ball” as his father had — are intriguing, the peek inside the HX-63, with its Swiss engineering, is the real treat.
One of the great things about the internet is how easy it is to quickly answer completely meaningless questions. For me, that usually involves looking up the lyrics of a song I just heard and finding out that, no, Robert Plant didn’t sing “Whoopie Cat” during Misty Mountain Hop. But it also let me answer a simple question the other day: what’s the largest single-piece metal object ever created? I figured it would have to be a casting of some sort, and likely something from the middle of the previous century. But as it turns out, the largest casting ever appears to have been manufactured in Sheffield, England in 2015. The company, Sheffield Forgemaster International, produced eleven castings for the offshore oil industry, each weighing in at over 320 tonnes. The scale of each piece is mind-boggling, and the technology that went into making them would be really interesting to learn about. And it goes without saying that my search was far from exhaustive; if you know of a single-piece metal part larger than 320 tonnes, I’ll be glad to stand corrected.
Have you heard about “teledriving” yet? On the face of it, a remote-controlled car where a qualified driver sits in an office somewhere watching video feeds from the car makes little sense. But as you dig into the details, the idea of remotely piloted cars starts to look like one of those “Why didn’t I think of that?” ideas. The company behind this is called Vay, and the idea is to remotely drive a ride-share vehicle to its next customer. Basically, when you hail a ride, a remote driver connects to an available car and drives it to your location. You get in and take over the controls to drive to your destination. When you arrive, another remote drive pilots the car to its next pickup. There are obvious problems to work out, but the idea is really the tacit admission that all things considered, humans are way better at driving than machines are, at least right now.