What’s in your crypto wallet? The simple answer should be fat stacks of Bitcoin or Ethereum and little more. But if you use a hardware cryptocurrency wallet, you may be carrying around a bit fat vulnerability, too.
At the 35C3 conference last year, [Thomas Roth], [Josh Datko], and [Dmitry Nedospasov] presented a side-channel attack on a hardware crypto wallet. The wallet in question is a Ledger Blue, a smartphone-sized device which seems to be discontinued by the manufacturer but is still available in the secondary market. The wallet sports a touch-screen interface for managing your crypto empire, and therein lies the weakness that these researchers exploited.
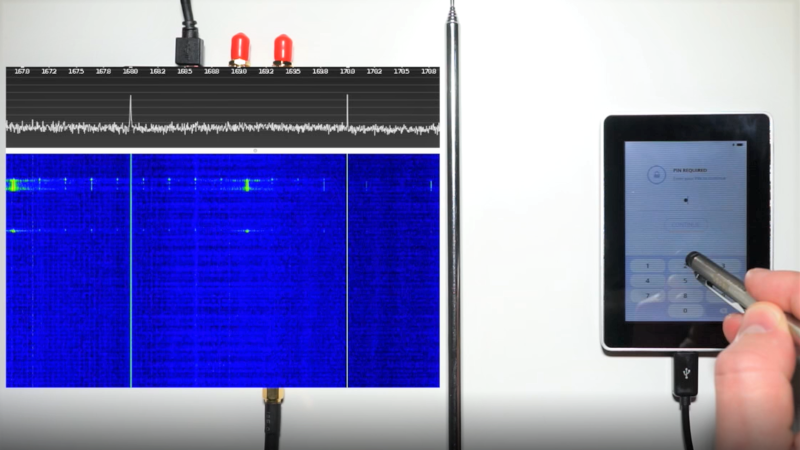
By using a HackRF SDR and a simple whip antenna, they found that the wallet radiated a distinctive and relatively strong signal at 169 MHz every time a virtual key was pressed to enter a PIN. Each burst started with a distinctive 11-bit data pattern; with the help of a logic analyzer, they determined that each packet contained the location of the key icon on the screen.
Next step: put together a training set. They rigged up a simple automatic button-masher using a servo and some 3D-printed parts, and captured signals from the SDR for 100 presses of each key. The raw data was massaged a bit to prepare it for TensorFlow, and the trained network proved accurate enough to give any hardware wallet user pause – especially since they captured the data from two meters away with relatively simple and concealable gear.
Every lock contains the information needed to defeat it, requiring only a motivated attacker with the right tools and knowledge. We’ve covered other side-channel attacks before; sadly, they’ll probably only get easier as technologies like SDR and machine learning rapidly advance.
[via RTL-SDR.com]















This weakness is so easy to fix, just change location of digits on the screen every time one digit is selected.
I feel like that would be a quick fix that should probably be implemented ASAP… what about just *not* leaking that information to begin with? :P
Hah! Good EMI design would have cost the manufacturer an extra dollar.
Yeah, that extra dollar is totally not worth your reputation as a designer/manufacturer or your customer’s confidence in your ability…
Seems like a good idea, but people expect the buttons to be organized in a logical fashion. If you shifted numbers into a random matrix, I’ll bet users would complain.
However, if you kept the keys in the same order but moved the whole keypad to a random part of the screen…
Or, change the font and style of the icon every time to something random, so the RF signature for each number is different every time. Or at least sufficiently different that it makes brute-forcing it with TensorFlow more difficult than it’s potentially worth.
Or, yeah – just fix your EMI issue with a little RF gasketing and maybe some foil tape.
That would not be a sufficient fix though – then you could still parse the digit from the actual image data. I think a fix would be to either to only outline the digit or to not highlight at all.
Gee, you’d think that a company designing such a device would check for spurious emissions… Seems like a pretty obvious attack.
I love how the product page states in the tag-line “Cutting-edge touchscreen security”.
It’s almost like they should have used real buttons.
Also, fingerprints :-)
This is why I keep my bitcoins under my mattress!
i don’t see any 3d printed parts in the test rig.
i thought that would have been a weird solution given the simplicity of the task
“As this can be a lot of work, we decided to automate it by building a USB-controlled ‘button pusher’ – built from an Arduino, a servo motor, and some random stuff that was laying around the office”
Side channel feature on these CPU’s both Intel and AMD just seems like a bad way to improve performance in hindsight. You either endure all the fixes that can serious degrade performance, or you turn off the side channel abilities that also degrade performance. The consolation here is that like Spector/Meltdown and those that followed seem rather complex to implement with any success outside of a lab. So is this all hyped to only prove a concept rather then an actual threat?