As an itinerant Hackaday writer I am privileged to meet the people who make up our community as I travel the continent in search of the coolest gatherings. This weekend I’ve made the trek to the east of the Netherlands for the ETH0 hacker camp, in a camping hostel set in wooded countryside. Sit down, connect to the network, grab a Club-Mate, and I’m ready to go!
Forget the CTF, Connecting To WiFi Is The Real Challenge!
There no doubt comes a point in every traveling hacker’s life when a small annoyance becomes a major one and a rant boils up from within, and perhaps it’s ETH0’s misfortune that it’s at their event that something has finally boiled over. I’m speaking of course about wireless networks.
While on the road I connect to a lot of them, the normal commercial hotspots, hackerspaces, and of course at hacker camps. Connecting to a wireless network is a simple experience, with a level of security provided by WPA2 and access credentials being a password. Find the SSID, bang in the password, and you’re in. I’m as securely connected as I reasonably can be, and can get on with whatever I need to do. At hacker camps though, for some reason it never seems to be so simple.
Instead of a simple password field you are presented with a complex dialogue with a load of fields that make little sense, and someone breezily saying “Just enter hacker and hacker!” doesn’t cut it when that simply doesn’t work. When you have to publish an app just so that attendees can hook up their phones to a network, perhaps it’s time to take another look .
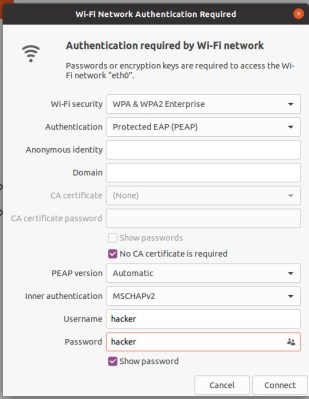
So what exactly am I complaining about and what does it all mean? Here’s a screenshot of the offending dialogue, in all its verbose glory.
At the top is a pulldown: WiFi security. This defines what type of network it is, and on my Ubuntu system it has the full range of security types from ‘None’ for an open network to “WPA3” for the most recent security standard. Most wireless networks in use today have WPA2 security, and this one is no exception. It has “WPA & WPA2 Enterprise”, which means that it follows the fancy version of WPA2 which uses a signed certificate to authenticate the access point. By contrast those other networks use “WPA Personal”, meaning that the client automatically trusts any access point following the same SSID and password combo, without requiring a certificate.
This use of WPA2 enterprise security makes sense for the security conscious administrator even if it’s annoying for the end user to configure, and as it turns out it’s the next pulldown labelled “Authentication” that’s the annoying one on my system. By default it shows “Tunnelled TLS” as its sprotocol, where it turns out that the hacker camp networks use “Protected EAP (PEAP)”. This is a protocol that protects the initial key exchange against a third party eavesdropping on packets and hijacking the connection.
The Network Giveth Security, And Then Taketh It Away
There are a few options for identity, domain, and certificate authentication servers, but the next important setting is a checkbox: “No CA certificate is required”. This is both important and infuriating, because going back to the point earlier about WPA2 Enterprise requiring a signed certificate, it appears to dispense with that entirely making the whole point of all this annoying configuration meaningless.
So if you use a protocol that requires a certificate to authenticate the access point and then do without the certificate, where is the benefit? I am no networking guru, but as far as I can see it lies in PEAP protecting my key exchange. Since my access point isn’t authenticated using a certificate there is nothing to stop a malicious third party setting up a rogue access point and capturing my connection anyway, so that benefit seems marginal.
I started this investigation from a standpoint of being annoyed at arcane WiFi set-ups, and assuming I understand the configuration correctly I have ended it unsure whether there is any benefit to the end user of having it in the first place. If you’re a wireless networking guru then please weigh in down in the comments, I’d really like to know.
Meanwhile I have a suggestion. Most camps have two networks, the WPA2 Enterprise one described above, and an open “insecure” one with no encryption and sometimes precious little between client and the wider internet. Can I suggest that they also have a network running WPA2 Personal, like every Starbucks, and leave the extra configuration for the 1337? It would save *so* much confusion!
(Editor’s note: If you’re wondering what’s up with the porta-potty full of network gear, it’s a long story. But the short version is, cheap and easy weatherproof housing.)
Header image, SHA 2017 Datenklo, Mitch Altman, CC BY-SA 2.0.
















I really have to ask “what’s the point” when all of my connections are TLS encrypted.
Yes, you can sniff the TLS and get the SNI to know what I am connecting to, so what?
The battlefield is in the browser blocking extensions and “custom” firefox security settings anyway.
Rogue DHCP servers, DNS hijacking/poisoning unless you use DNS over HTTPS, most people don’t bother to harden their TLS-using services or SSH.
Also: seeing your traffic tells someone ot only how to target your device, it gives them a list of things your device is talking to, to try and attack. “Oh hey, that server has an IMAP service running” and so on.
And if we’re behind a NAT, guess what? I’m not really going to raise much in the way of flags from any monitoring you have set up unless I’m really not careful. Everything’s coming from the same IP…
Everything I do is unsecured. I use passwords. But the stalkers rape my routers and modems anyway. They also use jammers to block me. So I get in my car. I drive around getting their license plate numbers. Then go back inthe house. I unplug everything. Then they drive off. It’s mostly dick ball state bastards.
Two things:
The two SSID idea is best. The setup they have is probably because they have a local DNS server and operate there own namespace, additional to the internet namespace.
This is the first time I have heard about this secure protocol – “sprotocol”.
If they didn’t make it as complicated and messed up as possible, they couldn’t be a real B1ff’s 1334 h@x0r Camp!!!
WPA2-PSK provides no security at all. Put the shared password into Wireshark and you can decrypt everyone’s traffic. If any users are not using a VPN, you can pick out all sorts of information such as websites visited etc.
WPA2-Enterprise PEAP on the other hand gives everyone a unique session key, making it impossible to decrypt their traffic if the wireless packets are sniffed. As long as users join a legitimate network, their traffic is safe – at least until the packets hit the wired network when all wireless encryption is removed.
That’s what I kept telling att and earthlink. They all lie. I use a gaming router and a att modem. I shut the wifi off. They still get into the wifi in my modem. I unplug it. They drive off. You can’t win for losing with stalkers
Just for a second there, I thought I heard Bob Pease.
Because all the WiFi security is just theater at this point. It doesn’t matter how secure a network is if you don’t have a way to validate every hop between you and your destination. This is the why behind the major push for SSL/TLS on everything. Otherwise you are putting blind trust in everyone upstream being upstanding and well behaved.
Exactly, and _especially_ at a hacker camp, you can bet (because all the hax0rs are there) that someone is capturing everything for later analysis.
It does make sense on a corporate network … particularly a centrally managed one. Microsoft’s ActiveDirectory even supports distributing the CA key to all clients, you then point your access point at a FreeRADIUS server that talks to AD via LDAP, and there you go: your users authenticate to the network using their own network credentials.
I used to use such a set-up at home, worked fine on Linux, Windows was a pain in the arse. These days, with an AP that supports multiple networks and 802.1Q, it makes more sense just to run separate SSIDs and map those to dedicated VLANs.
At a hacker camp for a temporary set-up, this is probably overkill. And pointless unless they run some parallel open network with restricted access over which you can reach some HTTPS server that stores the necessary CA certificate to access the restricted network.
As I was going to say: This network type is *extremely* familiar to anyone who has logged into wifi with institution-created credentials, say at a company, school, or university.
Instead of logging in with one password for everyone, you’re supposed to have each person log in with their own set of unique credentials. Here they’ve done the boneheaded thing of setting up such a system but gave everyone the same credentials anyway. Maybe they’re recycling enterprise equipment?
Incidentally, if you’ve ever tried to use ESP8266s (or any other kind of hobbyist device) at an institution, these networks will be the bane of your existence. Basically every library and product out there only supports regular WPA2 home networks. Even the quite capable ESP8266’s wifi libraries have terminally-bugged handling of WPA2 enterprise.
This, a thousand times this. I ended up using my phone as a hotspot because the school’s wireless didn’t play nice with the Rasperry Pi or ESPs. Nightmare.
Using the same credentials makes sense, because they’re only using WPA2 Enterprise for clients to authenticate the network, not for the network to authenticate clients. (Now, how it’s configured in this example completely throws that out the window — but if you install the app on your phone or follow the setup instructions correctly, it works).
Basically the client needs to be configured to either trust a certificate signed by a particular CA (which happens in many enterprise scenarios), or it needs to be configured to require authenticating to a particular FQDN with a certificate from a public CA. Unfortunately, some OSes don’t really support the latter. But in either case, once you’ve authenticated the authentication server, you just specify some default credentials to get a unique, per-connection session key. The reason this is required is that WPA2 Enterprise doesn’t really support anonymous client authentication. This situation has supposedly been improved with HotSpot 2.0, but I suspect even fewer devices support that.
My unqualified guess’d be that using that auth scheme even without a cert allows for beter network/load/user management and maybe better client hopping between APs.
I assume just using normal WPA2/3 all those information stay at the individual APs. Using “WPA2/3 Enterprise” delivers those information to the RADIUS server instead were they can be analyzed etc.
Thank you editor for the porta-potty explanation.
I think you might need to study up a bit more on WiFi security before publishing an article on it. In a well designed network there should never be a need for a client to configure very much. There are many methods to automate all of that. Also, on the TLS side of things, remember that the “require CA Certificate” is from the client perspective not the wireless network. All you are doing is telling your client that it does not need to validate the certificate it receives from the network. This is common when an organization is using a self signed or locally signed cert (i.e. do you care if the cert is signed by an untrusted CA). The most common use for EAP-TLS is when I have a network and I want to ensure that only devices owned by me can join it. This is commonly used in networks with handheld data collection devices like inventory scanners. These devices often do not have a full UI making it hard to enter credentials so we just upload a certificate to the device which proves to the network that the device is authorized by us to enter the network. It also acts as the traffic encryption method without entering easily compromised static keys. If we automate certificate distribution we can easily expired lost or stolen devices. There are provisioning systems that can validate the software uploaded to a device and then sign it with a certificate. These devices will often be able to verify the code and will delete the cert if the software is compromised or altered.
As you touched upon a little bit, it is also common in corporate networks to have devices signed by their Windows domain during commissioning as additional insurance that the device is owned by the corporation or at least authorized to be in the domain. We often use the presence or absence of the cert to tell us whether a device belongs on the internal network or should be steered into a BYOD or guest network. If you wanted to get really fancy with it you can use certs to put devices into different security groups with different access controls on the same wireless BSSID. For example you finance people and your HR people could have different resource access rules since I can ID the user by the certificate they were issued during commissioning. When combined with single sign on mechanisms for user credentials you end up with a very powerful way to know who is on your network AND confirming they are using an authorized device to access it.
In a properly designed enterprise wi-fi network it is often possible to not ask the user for anything at all to join the wireless corporate network and at most maybe a EUA splash for the guest network.
Now, I know your article is mainly about event networks. In that use case I cannot see the need to jump through all the TLS and other hoops when you are allowing absolutely anyone join your network. There is really no expectation of security in an event network unless you really want to keep non-participants out of the network. In that case, the best method is either an onboarding process that somehow validates who you are or a simple code printed on a ticket or badge. Anyone making you go through all of those options does not really know how to build a user friendly network environment.
Assuming you trust the network operator and configure your client correctly, these event networks *are* actually secure. Clients are fully isolated (so no rogue ARP/DHCP/DNS shenanigans), the network you are connecting to is authenticated, and if you have protected management frames enabled, it even prevents deauth attacks.
Even when you want everybody to be able to “join” the network, the important security difference between using WPA-PSK vs. WPA-Enterprise is this:
– With WPA-PSK, all connected users will be able to interfere* with other users traffic.
– With WPA-Enterprise, they can’t.
*With interfere, I mean intercept/decrypt/MITM,etc., not performing a DoS, etc…
With other words, the network operators are trying to protect their normal users against malicious users by implementing a mitigation against an entire class of attacks.
This is suppose to be a hacker camp? Its not difficult to setup Cisco ISE on a VM on eval and provide every guest user a set of unique credentials for PEAP authentication. They can go one step further and get a paid cert on their ISE so people can check off that “validate certificate” box.
wpa2 personal is not as secure if sharing same credentials with every guest user .
wpa2 enterprise using peap is lot more secure.
wpa2 enterprise with eap-ttls most secure