Imagine a movie featuring a scene set in a top-secret bioweapons research lab. The villain, clad in a bunny suit, strides into the inner sanctum of the facility — one of the biosafety rooms where only the most infectious and deadliest microorganisms are handled. Tension mounts as he pulls out his phone; surely he’ll use it to affect some dramatic hack, or perhaps set off an explosive device. Instead, he calls up his playlist and… plays a song? What kind of villain is this?
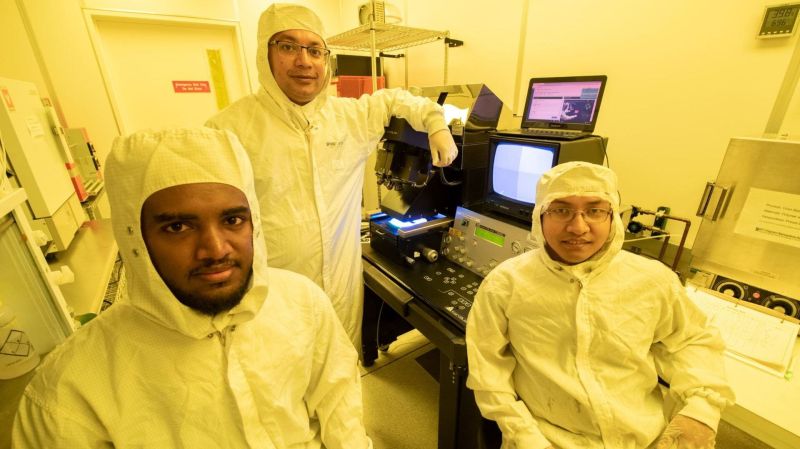
As it turns out, perhaps one who has read a new paper on the potential for hacking biosafety rooms using music. The work was done by University of California Irvine researchers [Anomadarshi Barua], [Yonatan Gizachew Achamyeleh], and [Mohammad Abdullah Al Faruque], and focuses on the negative pressure rooms found in all sorts of facilities, but are of particular concern where they are used to prevent pathogens from escaping into the world at large.
Negative pressure rooms use sophisticated HVAC systems to keep a lower pressure inside the room compared to the outside, and go to great lengths to keep it that way. The control systems for such rooms rely on differential pressure sensors, which detect the difference in pressure between two ports separated by a thin diaphragm. The diaphragm’s deflection due to pressure differences between the two ports can be sensed either capacitively or piezoresistively.
Trouble is, the diaphragms tend to have resonant frequencies in the audio range, making them vulnerable to spoofing. Several different commonly used sensors were evaluated with audio frequency sweeps, showing a resonance sweet spot at 700 to 900 Hz. This is right in the ballpark for embedding into an audio track, allowing the attacker to hide in plain sight — or sound, as the case may be. Tweaking the sensor with this frequency can potentially convince the control system to make an adjustment that removes air — and any pathogens it contains — from the room. You can imagine the rest.
We’ve become quite fond of finding and reporting on some of the oddest of oddball side-channel attack vectors, like potato chip bags and clicky keyboards. This attack is particularly terrifying since it seems both more plausible and has much higher stakes.
Featured image: by Steve Zylius / University of California Irvine
[via TechXplore]















” You can imagine the rest.”
Dumped into the outside air.
Serious comment here: the purpose of the room is to maintain negative pressure. That means air gets pulled into the room …. i.e. the air from adjoining entry rooms get pulled into the inner sanctum so that any pathogens stay in the inner sanctum and can’t escape out the door. But any air that gets pulled into the inner sanctum has to go somewhere anyway. Otherwise the pressure inside the inner sanctum would continue to build (which obviously doesn’t happen). So the inner sanctum air is continuously removed, most likely to some system (extreme heat? Chemical? Other?) that kills any pathogen in the air that is removed. Can any of you clean room experts confirm this, or correct me if this is wrong?
For BSL1 and BSL2 (most labs) nothing happens to the air that’s being blown out. For BSL3 and BSL4 (rare enough that most countries don’t even have them) the air gets passed through a HEPA filter.
Source: designed a number of BSL2 labs and was/am responsible for the biosafety of some BSL2 labs
That would be my assumption yes. It’s a negative pressure room, not a hermetically sealed room. Air can get in but doesn’t flow out in an uncontrolled way. There could be live lab animals in such a room who would require a fresh air supply.
Confirmed. Most of our operating rooms are positive pressure maintaining a little more pressure inside the OR than outside in the hallway, the thought being any dust or pathogens or whatnot get blown out of the OR for sterility reasons. The air in the room itself it handled by laminar flow recycling and HEPA filtration.
The other hospitals I’ve worked in also had one or more dedicated negative pressure rooms. But in our new facility we have the ability to make any room negative pressure for dangerous pathogen work- typically TB or much more rarely, prion (mad cow etc) or, recently COVID especially early in the pando. When they do that they tape up plastic airlock things at the entrances and a dedicated clinical engineer sits there monitoring everything. It’s cool but also a royal PITA.
Just play some Janet Jackson and there’s a possibility you might crash the creaky SCADA server nearby if it runs off turn-of-the-century 2.5″ HDDs…
https://arstechnica.com/gadgets/2022/08/janet-jacksons-rhythm-nation-is-officially-a-security-threat-for-some-old-laptops/
So playing rock music would work… like “Down With The Sickness” or “Mystery Disease” ?
Actually, the late Carol Lloyd was rather strong in that part of the spectrum, so anything from Carol Lloyd band or Railroad Gin would work.
40s swing with those brass sections aren’t bad either. Some of that stuff is coming out of copyright.
High potency and high tech at the same facility seems like a small number of potential targets. Most of the ‘interesting’ cleanrooms I have been in would have required a set of spanners and sheave of drawings that look more Indiana Jones than AutoCad to rebalance the HVAC pressure differentials. Last few haven’t even had speed control on the fans.
Also the pressure differentials are never going to be the only protection method, not are they typically a single point. (You’ll have several pressure ‘sinks’ between the excitement and the outside world).
The pressure systems I’ve seen in HVAC were always a pair of differential tubes from the measuring points to a heated wire sensor that worked much the same way as a load cell. When the heated wire was cooled by an air flow, it was compared to an adjacent identical wire isolated from the airflow and the two resistances were part of a Wheatstone Bridge voltage divider. This way, opening wide doors to an area took a minute before the system would start adjusting the dampers. This avoided the use of rubber diaphragms, which are prone to aging and chemical attacks (alcohols, etc)
How do you know which pressure is higher? Wouldn’t flow in either direction cause the same effect?
> rubber diaphragms, which are prone to aging and chemical attacks (alcohols, etc)
Natural rubber, slowly turns into a sticky goo if exposed to oil. Even happens with enough contact with oils from skin or hair.
I’m trying to imagine a lab working with pathogens that would have a biosafety room but allow employees to bring their phone in – and I assume back out again.
Me too. But it’s probably not hard to sing the resonant frequency if you’ve got a good voice. And you’d be louder than a phone.
Like any good cat and mouse game, it’s likely that bio-safety rooms are soon going to get a small upgrade to detect this exact kind of attack. I mean, you don’t have bio-safety rooms and not have a sizable maintenance budget.