Here at Hackaday we cover news and interesting features for the hacker community, with an emphasis more on the hardware side. Nevertheless we also cover stories from time to time from the broader world of security. These usually involve vulnerabilities discovered through the patient work of software or hardware researchers, and are certainly what we’d call hacking. But what about those information security breaches that aren’t hacks like that at all? What happens when the person being breached simply gives you the information?
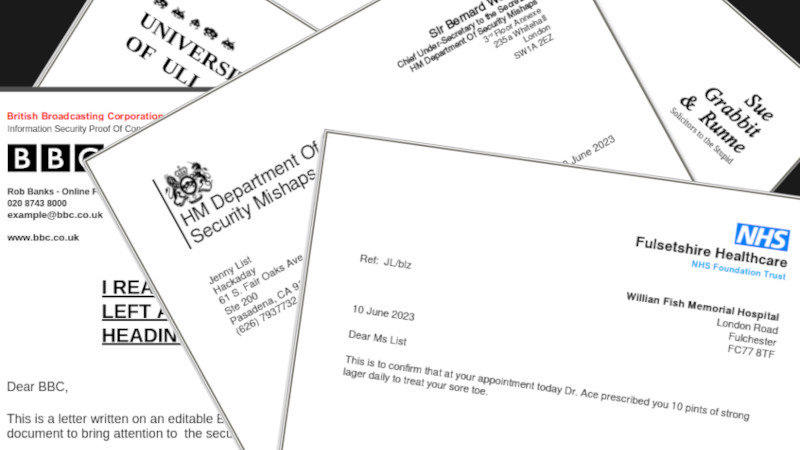
I’ve got one, and while it’s Not A Hack, it’s definitely something that we and those outside our community need to talk about. I’m talking about the depressingly common occurrence of organisations who should know better, gifting their letterhead to all and sundry in the form of freely editable Word documents.
A Bit Of Paper That Unlocks So Many Doors

A letterhead may seem to those of us on the cutting edge of technology as though it hails from a bygone era, but in legal and trust terms it’s still in so many circumstances the key that unlocks the door. If you turn up with an official-looking letter on the right letterhead, it’s taken at face value. In my time I’ve had to supply just that for medical, financial, and legal transactions. Thus the letterhead, and the ability to use it, is a key piece of an organisation’s security. We can poke holes in this outdated convention as much as we like, but anything printed on a letterhead carries that organisation’s trust and reputation with it.
In my time I’ve received Word document letters from numerous organisations that should know better, and using the letterhead is as simple as rewriting the letter in my word processor. These include my bank, my university, the BBC, more than one major publishing house, a specialist National Health Service clinic, and even in a particularly funny episode, the solicitors hired by some nasty people who were trying to harass me.
If I were a criminal I could have tried several lucrative financial frauds using those letter headings. I could have used the NHS one with my local doctor to be prescribed interesting pharmaceuticals, and I could probably have used the professional and university ones to secure work I’m unqualified for. Such is the value attributed to these documents. Sadly I haven’t kept a rogue’s gallery for you to leaf through, but instead in each case I’ve politely informed them of their security breach and deleted the document unless it was one of importance that I needed to hang on to. I’m uncertain of the legality behind it all, but I am guessing the crime isn’t in possessing a freely given electronic letterhead but in using it for nefarious purposes.
As if the above list of random big names who were kind enough to gift me their letterhead wasn’t enough, when researching this piece I was astounded to find large organisations in the public and private sectors who even make them available for download. I have declined to put up any links, but, in some cases letters for public consumption can be found online as Word documents, and there are even organisations that publish communication design and style guides containing the blank letterheadings ready for use. You really couldn’t make this up!
Basic Security Left To The Lowest Paid
At fault of course is partly a lack of understanding of just what an electronic version of a document really means. The task of drafting and sending out is left to the lowest paid workers at the bottom of the ladder, and they evidently have no idea that there is a security risk involved; to them the document simply is what’s spat out by Word. If ever a fraud is traced back to a letterheading in a Word document you can be certain it’s those lowly minions who will be for the chop, but the real culprits lie higher up the food chain for not instituting appropriate policies and training. What needs to happen is for letterhead to be considered as important a part of organisational security as any other electronic asset.
Documents still need to be sent out, so how should they be doing it? The obvious first choice is to use PDF, as a readily accepted electronic document format. They’re by no means perfect as a proprietary format, and some of the advanced PDF features need Adobe’s own reader which isn’t available on all platforms, but they are at least well understood and ubiquitous. PDFs can of course still be edited, but the barrier to entry for the miscreant is immediately higher. Alternatively there are various secure online delivery platforms, for example my accountant makes his documents available through a portal for which I have to supply a secured login. If there’s a credible open-source equivalent to either of these options, we’d love to hear it.
While my parody letter headings in the header image should be easy enough to spot, the same can’t be said for the real thing. I’m preaching to the infosec choir in a Hackaday piece so you’ll probably be with me on most of these points, but what’s to be done? As always, the comments await.















I think the security hole is not the distribution of an image (that image’s location at the top of a document notwithstanding) but the acceptance of an image at the top of a document as in any way shape or form authoritative.
Besides, cloning a letterhead from a PDF is just as casually trivial as from a word document, a ‘secure’ document delivery services ceases to be secure as soon as that document can actually be read by anyone (if you can see it on a screen or on a printout, you can duplicate it), and even a physical document is a relatively minor photoshop skill barrier away from casual replication.
Naming and shaming should be directed to those who accept an unsigned image as a certificate, not those who use it as a way to make their letters look pretty / conform to branding.
It’s the same “we imagine it might magically somehow be secure so treat it as absolutely secure without a second through” fantasising that leads people to distribute cleartext passwords via email (ignoring that email is also cleartext), or who print their WiFi password on the outside of their building and wonder how so many people can ‘hack in’ from outside.
Email is rarely cleartext these days. A quick check of my mailbox recently struggled to find any emails sent cleartext.
However you can’t guarantee it won’t be sent cleartext, and it’s only protected in transit, not end to end. But as most deliveries will be a single hop from your mail system to theirs, and you probably trust both, that’s usually going to be enough.
If by “not cleartext” you mean quoted printable or base64 encoded they are still considered cleartext. By far most emails communications are in cleartext in that sense, very few organisations use S/MIME or PGP, and even fewer use that for external communications.
So this leaves the only possible security on the transmission… Most webmails use https, for pop/imap/submission/smtp it really depends on proper clients and servers configuration, moreover there is no way to ensure the transmission will only happen over secure protocols. Besides clients there are still plenty of MTA’s that do not use smtps.
And we haven’t even considered authentication yet…
Can’t really disagree with this. All the assets you need to construct a realistic-looking letterhead are on the websites of most organisations. No-one is going to start treating those assets as “part of organisation security” – the whole point of having them on the website is to make them accessible.
Copying an image out of a PDF is so trivial that it’s not worth discussing, no matter how many of Adobe’s security features are enabled; a screenshot will still do the job. Likewise any “secure” document delivery system.
Even if there are open source versions of the “secure” document delivery system available, the problem is always where to host them (and that they don’t really help with this problem).
An image doesn’t even have to be correct.
An Australian group of comedians (Juice Media) have been poking fun at government for years. Their YouTube videos are called “honest adverts” and contain a DELIBERATELY ALTERED version of the Australian Coat of Arms, along with the title “Australien Government”.
Despite all these changes, they were facing investigation because some people honestly worried that these expletive-ridden videos could be mistaken as genuine Government announcements.
Sample video: https://youtu.be/bleyX4oMCgM
Love it. Juice Media, brilliant.
LOFL
Yup. I guess the next security-related article on Hackaday will tell us that “trees are bad because you can build wooden horses from them”.
Yep, and some guys even did that a few years ago. Put that wooden horse on a trailer, drove over to some companies and said that they had to deliver the horse. I think they had a 100% success rate. There’s probably some video of that, somewhere.
In my opinion…
It seems that the security hold more is whether or not somebody is going to verify what’s on that letterhead…. Letters of recommendation, let’s say as an example, basically mean nothing unless somebody reaches out to the supposed origin of the letter and verifies that letter of recommendation… This isn’t the 16th century we’re having a letter from the king presumes that you actually have a letter from the king … When hiring I would reach out to the people who supposedly gave the recommendation, and who the letterhead was from, and ask them what they said in their letter of recommendation. If it didn’t closely resemble what the letter said then, I didn’t hire the person because I presumed that it was forged or altered in some way.
Sadly the security hole is not the lowest paid person using the template… It’s the person presuming that it’s not forgery or fraud. The ego of the person receiving the document, is the biggest security hole 🤣 “Trust but verify” …. We don’t want to treat each person as though we don’t trust them, but that doesn’t mean we shouldn’t verify.
Unless something is sent directly from the source, and with a PGP key from a verified sender embedded per se, then we don’t know if it’s been altered enroute. It’s honestly no different than getting a link in a text message… We need to teach people but they need to reach out to that supposed sender and verify that the person actually intended to send them this link and that it wasn’t part of a hack or virus or phishing scam.
There’s a reason that universities won’t accept transcripts from people directly, and that the only way to get verified transcripts accepted to a university is for it to be sent directly from another school or university… It has to be sealed etc or they’re not going to accept it… And when they receive it it literally have somebody verify that the school sent it. If two sets of verified transcripts show up, you are busted for fraud.
It didn’t take schools and universities very long to figure out that people were altering the records and then sending them on to the university as forgeries. So they figured out a system to make certain that that has not happened.
Schools have not yet figured out how to work together and just have an actual database that comingles all of those records…. Of course that would make it much easier to hack, though, so probably a good thing 🤣
So back to the original issue… If somebody is willing to accept a random piece of paper as proof of something, without verifying it, then they get what they get.
Someone might be able to forge a letter of recommendation or something, but if the hiring party isn’t savvy enough to verify with the supposed author, then do you really want to be working for that place? I mean I suppose some nefarious people might really want that job… But ultimately it’s all going to go sideways because it means that there are probably a lot of nefarious people working there and unless they’re trying to create a super villain complex it’s probably not going to go well 🤣
This could be an excellent infosec way to get a job though… If you can get yourself hired on a bunch of false papers and nobody ever checked those papers… Then perhaps you could get yourself tired as the person that closes that hole.
The issue is that, in the United States, it would be forgery and fraud… And I don’t think anybody really wants to try their hand at using these ideas to get a job knowing fair and well that they will likely be brought up on charges.
But I do think that your article was necessary for the people who hadn’t thought of it and didn’t have the security acumen to realize that they need to trust but verify. Sadly posting it here on hackaday is probably just preaching to the choir.
It’s an excellent thought experiment though… As I was waking up this morning and I was reading this article it made me wonder how somebody might be able to make it easy to verify these things … And everything that I could come up with besides the old fashioned calling of the original person… Had security holes that I could circumvent or see being circumvented. Either the confidentiality of something would be circumvented or the authenticity would still be questionable.
But maybe somebody will read this article and come up with a way that those letters could be verified with the original sender, still maintain the confidentiality, and yet assure the authenticity without being circumvented through fraud😊 If so they will have themselves a billion dollar idea 🥰
One perfect example would be to provide a transcript key on the letter – this may be a muddled mix of letters& numbers like:
https(….)state.gov(…)/transcripts/{unique userID}/{transcript ID}
To verify the document you must visit https(….)state.gov – log in, then view transcripts – if it is not there – file a report & provide an image of the letter you received.
This is sent to a security team to review & they can let others know – potentially also identify which data is publicly available//if anything is internal & requires an audit of who’s accessed that user’s details
The Chaser did this a while ago to a variety of places around Sydney (including the Victoria Barracks lol) with great success. There’s a good clip of it here: https://www.youtube.com/watch?v=JjShDCqs7jk
Even “secure” document delivery services have been shown to be very commonly *insecure*. The software driving these applications were likely written years ago and have huge security vulnerabilities. Just search for MOVEit and find a plethora of ransomwared companies (and governments) whose “secure” document appliances were broken, stolen, and ransomed.
Absolutely this.
The same issue exists with social security numbers and identity theft. SSNs are effectively not longer useful for authentication since Equifax disclosed them all a few years ago.
If a bank gives out a loan to a scammer with an SSN, and then tries to ruin a bystander’s credit when the scammer disappears, that really needs to be ENTIRELY the bank’s problem.
I imagine Worldcoin is looking to replace Equifax in the unique ID sphere…
Freeze your credit with the big 3 if you are in the US. It’s free, and effective. If something breaks through, it adds to your defense that it wasn’t you that took out loan, opened credit, etc.
As soon as your kids credit appears, freeze theirs as well. Teach them earlier to protect their rating as if it was gold in hand.
Exactly.
That’s why if it’s important you sign the PDF digitally.
(most EU citizens either have a personal key or will have one in the next years. It might be that they do not know about this but that’s a totally different issue)
And if you need to be able to print out the PDF and keep the signature, QR codes can solve that problem too.
The hubris of believing that any viewable/readable electronic document is secure, is almost as hilarious as sending out “redacted” MS Word docs which simply have black rectangle images inserted to cover the sensitive text.
This is a really good point and just giving things away on the website is such an obvious risk that could be mitigated by simply… not giving it away on the website.
There are SO MANY ORGs that just up and publish communication and design guideline packages for everything in a nice tidy document complete with zip file of all the reference images.
I get how it is easier to keep it all in one document package for internal and external so the poor schmuck who has to update and compile it has an easier time, but it really should be split as internal and external.
ie, internal should be everything you need to send a letter **AS THE COMPANY** and nobody outside of the org would ever need that.
External is quite common and I see that as “this is how you need to treat our brand logo so the lawyers don’t get excited”
But then how would an individual or company receiving a letter they are dubious about check if the scammer at least put in some effort?!?! The official letter heads absolutely should be readily available, but verification should also be built into them – for instance on that same web portal that shows what a real letter from them should look you should be able to lookup the ID number on that specific letter to know to whom that letter was supposed to be addressed at least sanitised version like the postcode.
Obviously nothing can ever be really really secure, but corporate letter heads to which so much meaning are given need to either die or evolve. And that evolution must be largely self explanatory in how to verify this letter’s authenticity in general terms and highlight the importance of doing so – then even if the scum create a good fake you are hopefully well trained by all the other letter heads and going directly to the real company website or semi-directly via your usual search engine.
It would actually be quite easy to implement a system with a verification code into the footer that could be input along key information (depending on the letter type; could be date, recipient name, civic number, a prescription could include drug name and dosage) to validate authenticity.
Locking down the templates isn’t necessarily a bad thing, but it must not be considered a security in itself. It’s like security through obscurity, because no one knows your website runs through an old OS with unpatched bash shell doesn’t make you immune to Shellshock. Not shouting it out will probably just extend your grace period by a few minutes at best before you get hacked by a bot!
Verification is what my university does: Every important document has a short link and a verification code at the bottom. When you open the link and enter the code you will receive the same document as PDF via your browser for comparison. The system also refuses to validate older documents which have expired. Seems like a smart solution to me.
But you still have to trust the URL, an attacker could come up with a reasonable slightly different URL and spoof the process.
As noted in other comments, the problem is that a letterhead can be accepted as a security credential. There’s no such thing as a “secure” letterhead*, so an IT departnent that told people not to send headed documents in Word format “for security reasons” would be making their organisation /less/ secure by legitimising this bad practice.
*you could concoct a plan with dynamically watermarked logos, but any recipient who could authenticate such a thing could more easily just use proper encrypted communications anyway
** I once designed a self-generating logo for a small ISP, implemented as a PostScript program so you could embed it in (for example) a Word doc and it would print out differently every time. It didn’t help with security, and they ended up not using it for various reasons, but it was cool
This could be especially useful today if it were tied back to a dynamically generated/verified QR code. Scan with your phone, see a copy of the letter and you could verify it matches.
Well, one could put a QR code in the letter head that contains – I dunno – sender, receiver, time, process number and be signed with the company’s private key.
The receiver could check that with an app (URL to pup-cert in there too or with CAs like with HTTPS?).
I know it’s kinda backporting digital cryptography back onto analog dead trees instead of transitioning from snail mail to I dunno encrypted mails? ;-)
“Back in the day” my workgroup had a solid-ink printer which produced slightly raised, shiny text and images on the page – much different than laser printing. A little page layout magic with the right images, some high quality bond paper, and you could produce letterhead that looked (and FELT) very official. I used the solid-ink printer to make the letterhead, then ran those pages through an inkjet to produce the actual documents that had the look (and FEEL) of being on an official letterhead. I have to confess (statute of limitations has long run out I hope) to fooling some people who should’ve known better.
I’ll get to the article in a minute. But I just want to say that when I read a HaD article, most of the time I can tell who the author is from the first sentence or two. And when I think it is Jenny List, and then check and it is (!) it makes my day. Thanks for that.
Same here, and the reference to Messrs Sue Grabbit and Run Attorneys at Law clearly shows a mis-spent youth reading Private Eye.
:) I feel so seen. But did you get all the references?
Appreciate the support!
I recently came across a security issue involving paper: a donationbox where you could donate the receipt of your soda bottle deposits. The proceeds would go to some charity. The box was transparent so people could snap a picture of the bar code and scan the copy at the self checkout. I reported the security leak.
Maybe I’m mis-remembering, but I’m sure years ago important letters from large organisations (government, banks, etc.) would come on watermarked paper. Even if you could copy the letterhead forging this watermark which was manufactured into the paper itself would be extremley difficult.
Companies can also have a “seal” for official documents that punctures and warps the paper to present some kind of embossed watermark.
Granted this won’t stop people from just accepting plain letterheads on copy paper, but it’s an option.
As has already been mentioned, PDF is no barrier at all. However, there is even a simpler ‘hack’: as long as you can print it out, you can mask the lower part with any message you want. If you are really mischievious, you can just put what you want between the letterhead and the very original signature.
“I could have used the NHS one with my local doctor to be prescribed interesting pharmaceuticals, and I could probably have used the professional and university ones to secure work I’m unqualified for.”
So… you would be allowed to work and shop for medicine freely? Good! More people should copy letterheads, then.
in my youth i’d collect blank headed paper from as many places as I could (was quite easy in the olden days) and had 2 drawers of a filing cabinet of the stuff. Amazing what you could get or where you could get into using it and it was handy for pranks too.
I once obtained the letterhead of an ‘official agency’ and used it to send a letter to a friend detailing all the nefarious things they’d observed him getting up to on his motorbike and telling him to mend his ways or else.
How very timely, just today I read an article about how a New Zealand woman sent official looking fake letters to oil company execs telling them their event was cancelled. She was found guilty of making and using a fake document.
> Penwarden’s letter was laid out with a PEPANZ letterhead, and a row of member logos along the bottom.
https://www.theguardian.com/world/2023/jun/15/nz-climate-activist-faces-up-to-10-years-in-prison-over-fake-letter-saying-fossil-fuel-event-cancelled
I’ve got a letterpress, so I can make any company an embossed, foiled, or embossed and foiled letterhead that would be impractical to duplicate. Problem is that anyone who didn’t know that company used an embossed letterhead could be easily fooled anyway, because they wouldn’t know to look for that.
Taking a paper document (aside from the rare exceptions with substantial security features, like large-denomination currency in some countries) as authoritative just isn’t practical in today’s world.
Sounds like there’s a need for a Blockchain minted nft document. That’s almost trivial to a achieve on deso protocol. Maybe I will pursue this further. Thanks for the idea.
Social Engineering has always been one of the cornerstones of classical Hacking. Social constructs can be seen as a technology, a machine with organic components. Subverting them parallels mechanical and electronic means. And often times, they operate as “gaps” much like the “air gap”…. but instead the “meat gap”.
So in a way, it is a “hack”.
Sounds totally ridiculous that anyone would consider a letterhead to prove anything.
But then again, there are still countries where identity is proven with utility bill. And even EU still hasn’t figured out an international authentication method.
“And even EU still hasn’t figured out an international authentication method.”
Other than the standardised biometric passport, of course.
Working in municipal government, I have seen several documents(change of direct deposit).. that were faked very efficiently. We now require face to face verification for changes to payroll and other sensitive changes. My users are trained to verify anything suspicious with a (user initiated to a known #)phone call or in person meeting with the person in question. It is sad the world is headed this way, but zero trust is a thing. I hung up on a caller today who was asking the most basic of information, I think they were asking the brand of phone system we are using. Sadly, I think that the social engineering problem has to be solved with “unless you know someone personally, and can see them and talk to them, act like an asshole, delete their emails, hang up on them, and ignore anything until you get a few copies”.
I get an invoice yearly for ~$279 every year from a company who is doing “web marketing” on our behalf. They probably send out tens of thousands of them and get quite a few back with a check. it’s a small enough dollar value that accounting departments just assume it’s legit and pay it. Kind of wish I was unscrupulous enough to think of it.
Throw in the “your domain is up for renewal” graft.
I now work in a highly regulated industry. I receive notices, warrants, and visits from gov (BATFE, DoJ, DoD, DoC) officials all the time, so I don’t freak out with someone showing up to look at stuff. They are not confrontational (kicking in the doors) and allow us the freedom to do the following.
1. Verify the person standing in front of you.
Call the local office with the number YOU have on hand, not the one on their creds, business card. Verify employment, out of the office they claim to be from.
2. Verify the documents.
If court ordered, call the clerk of that court and verify the document by Id.
If agency regulations, again verify using YOUR own contact resources.
3. If the communication was received by email, if legal in nature, respond by certified mail to the office it SHOULD be sent to.
We walk a tight rope here between compliance and confidentiality. Warrants, and orders have scope to them, and we have to ensure that in the search for documents and information about Entity A that Entity Bs info isn’t disclosed.
I’ll share a rather humorous scenario that comes from personal medical space. Son has a DME that supplies his equipment. If I request information from the DNE they consider private and in need of securing, they fax us. The fax consists of an email with a “click here” button that I suppose takes us to a secured portal of some sort. I don’t actually know where it goes, as Iv never been able to click that button kn the printed fax! But that information does seem to be secure!
Ony 10 pints of strong larger? :O
Not like it’s proper beer, innit.
While we’re talking about printed media, can we address the inherent insecurity of handwritten signatures? People accept them as official and/or legally binding if you can at least vaguely duplicate it.
Then there’s the four digit-only code protecting my hard earned money from others, while a free online account (with no monetary value) needs a lengthy password with uppercase, lowercase, numbers, symbols and a hardware OTP.
When I got my visa to reside in my current country of choice, the two ways to obtain that visa was either a university diploma in a relevant field or 10 years experience.
I did actually have more than the 10 years, but I soon realised that with some plausible letter heads and creativity with work reference, a matching resume and timeline, no real work experience is needed as immigration doesn’t make international phonecalls to check up due to the language barrier and costs and etc etc.
I wasn’t going to take the chance, as I met the requirements anyway, but it would be doable…
(Your milage may vary based on nationality etc)
This problem has already been solved many years ago, it’s called “Amtssignatur” here in Austria.
https://www.bmf.gv.at/themen/digitalisierung/Verwaltung/Was-bedeutet-digitale-Verwaltung-/E-Government-Bausteine-und-Services/Amtssignatur.html
All Documents and Correspondence issued by the government carry a banner with verification data in addition to an electronic signature, which makes a printout verifiable and gives it the same legal status as the original PDF. The Ministry of Finance provides a verification service for printed documents.
You can even sign your own documents that way by using the governmental service “ID Austria”. Similar methods are available in all EU countries.
Correct, in the EU there is this thing called eIDAS that can be used to identify yourself within any country in the EU. (In the the Netherlands it is called DIGID.) Of course eIDAS ended for British citizens with brexit…
It comes down to resources, knowledge. For companies and employees to check every letterhead and run a background on the letter or whatever it is prior to accepting it costs time and money, plus the knowledge to be able to actually do so and most of the time people either don’t have the time to check out the source of whatever the communication is and fact check it’s legitimacy so their other options would be to hire outside hell for this purpose or hire an internal team which could be costly for something that they feel would most likely never be an issue and hence a waste of money and resources.
It’s a more technical approach, but the answer may be digitally signed PDFs.
I worked for an international scientific organization. They published on the website the design guidelines for the use of the logo. You could even find the logo in vectorized form on Wikipedia, which used to be a terrific source of vector logos.
Is this a security breach? Well, this organization uses email as a form of communication. The letterhead is meaningless internally. And any print communication with external partners is taken with a grain of salt because the logo is fairly knows and easy to copy. Most partners already have a secure digital channel to communicate info, purchase orders, etc.
I’m sure at some point in the past someone tried it. But it’s like OSS. The fact that’s freely available makes it more secure
>They published on the website the design guidelines for the use of the logo. You could even find the logo in vectorized form on Wikipedia, which used to be a terrific source of vector logos.
The CE logo is like this. The standards themselves are locked behind a paywall, but the vector logo is out there, along with the guidelines for its use and placement.
No wonder CE markings are faked so often.
What a sender could do is include a cryptographic signature in the paper letter, such that you can compare to a public key to verify that this particular message was signed by who it seems to come from. You could accomplish that with the sig in the form of a QR code. Easy to “solve the problem” in tech terms. But the real problem is, most people won’t even think to look for a code or bother verifying one if it’s there.
“If there’s a credible open-source equivalent to either of these options, we’d love to hear it.”
Epesi (17 years old FOSS project) has this built-in out of the box function where you send a link to a file (e.g. PDF) that has its token and you know if a person downloaded the file, from where, plus you have file version and access history… If sent via email then the link/token combination is used for security and access control. We don’t send files directly as attachments. This way there is a reduced risk of attachments being too large, network traffic is reduced, files are not sent unnecessary to people who will never open them, smaller chance of email being classified as SPAM, reduced risk of virus infection etc.
When I created my IT service company and went to get badges made, I had to send badge company a letter, on my letterhead, stating that I was authorizing the use of my logo for the badge. The upside is that I now have letterhead. The downside is that it took me 5 minutes and there was no other proof required. I could make fake badges for any company using their letterhead.
Reminds me of the time some digital documents were made available to the public after being “redacted” — such redaction being highlighting the redacted portions in black. It was but a moment before someone realized the “redaction” could be removed with the click of a mouse.
Yeah the funniest example to me is German private medical prescriptions. Private meaning not paid by a public insurance, but by private insurance or the patient themselves.
These are valid on any piece of paper as long as they’re signed by a doctor. Doctors aren’t known for legible signatures, but these prescriptions (which allow to buy any medicine except for opioids) can literally be made on a napkin.
Now, most doctors have a form for those but even those are just plain paper with their address on it, so you can just create them yourself.
In recent months, I’ve found that many email systems will reject encrypted attachments, so sending encrypted documents as attachments might not work.
This likely also applies to S/MINE and PGP messages.
Ostensibly, this is because encrypted attachments can’t be scanned for malware.