Occasionally, the extra features added to a product can negate some of the reasons you wanted to buy the thing in the first place. Take, for example, Apple’s AirTag — billed as an affordable way to link your physical stuff to your phone. If some light-fingered ne’er-do-well wanders by and half-inches your gear, you get notified. The thing is, the AirTag also has an anti-stalking measure, which after a while, notifies nearby iPhones, should the tag move but not be near your iPhone!
In a recent video, [David Manning] explains that this feature is great for preventing the device from being used to track people. But it also means that if said thief happens to own an iPhone, they will be notified of the nearby tag, and can find it and disable it. So in the end, it’s a bit less useful as an anti-theft measure!
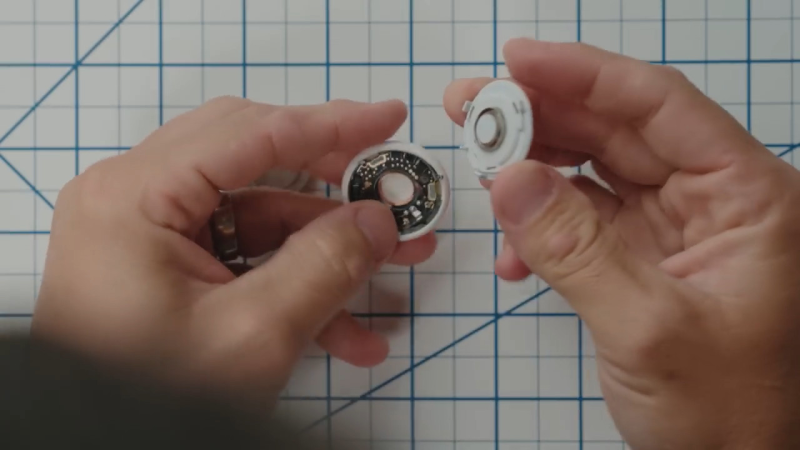
The solution is to pop the back off the tag and yank out the little sounder module from the rear plastic. You lose the ability to locate the tag audibly, but you gain a little more chance of returning your stolen goods. Apple could easily remove this feature with a firmware update, but it’s a matter of picking your poison: antistalking or antitheft?
Thanks to [Keith] for the tip!















“Apple could easily remove this feature with a firmware update, but it’s a matter of picking your poison: antistalking or antitheft?”
Society vs the individual, old as time, or recent as a pandemic.
oh Ostracus, you are too wise for these pages that shackle your truths
You know that you can do effectively the same thing using a burner phone, right?
It’s not as convenient or easy as using an airtag, but you can purchase a burner phone with a cell account and plant it in luggage, or wire it into a car for permanent tracking. Turn off all the extra apps, download an app that records GPS info, and download the data later or geolocate it live while in use.
I’ll bet anyone here can wire a GPS tracker up to an ESP device, tape it to a powerpack for long-term usage, and make an executable that puts the device into low-power sleep, then wakes up every minute to record GPS info. Then respond to a Wifi of bluetooth request to download the data.
You can also purchase tracking devices on eBay. Here’s one for $7:
1. Small size and light weight, easy for carry.
2. Black shell, easy to hide, perfect for tracking vehicles, teens, spouses, elderly persons or assets. 3. With two powerful magnets inside, easy to attach to vehicle firmly, no extra installation need.
3. All you need is a working SIM card (NOT included!) to insert into the device, then you can track and map (with Google Maps) in real-time over the Internet.
4. Dial SIM card number, then you can hear voice around this tracker, with no light and no noise, you can monitoring and spy what’s going on around the tracker silently and secretly.
The only thing about Airtags is that they make the process trivially easy. Airtags brought this into the public eye, but it’s not as if the technology wasn’t available.
Two words: battery life. Airtags have ~ 1 year. A phone ~ 1 day.
That is because the device emits a BLE broadcast every 2 seconds, if there are no Apple devices within range that broadcast is not going anywhere.
Or if the tag was surrounded with enough RF attenuation at the frequencies involved (Near Field Communication 13.56 MHz – 4 cm; ~1.6 inches , Bluetooth Low Energy 2.4 GHz band – 50 to 100 meters ; ~165 to 330 feet and Ultra-Wideband 6.5-8 GHz – 100 meters ; ~330 feet) to drop how far the tag could transmit.
I have more ideas but I do not feel like helping thieves.
As recent as theft significantly rising a few years ago. There must have been a national put a screaming junkie on every street corner act
Stuff vs the Individual, more like. But there has never been anything made as a useful thing that cannot be turned to evil, because humans.
Because that’s the nature of utility and power
Sadly there’s nothing that cannot be used for evil, with enough creativity.
Banana peels.
That’s not what I learned from cartoons.
Hippies were convinced to dry and smoke them.
Even my kid brother tried, he was in third grade. About as smart as your average hippie adult.
And the other classic conflict, Hackaday commenters vs. the Hackaday comment system.
I’m starting to think they keep the broken reply feature on purpose because somebody finds it entertaining.
> that cannot be turned to evil
Well they are tracking devices for Apple as well. They need to get to know their customers. But on the plus side, just like Google they will never sell the actual metadata to a third party, it is potentially far more useful for internal data mining. Keeping it, from when you join, until when you die and long after you are no more. In a century that metadata could be far more valuable than it is today for uses that we can not even predict.
Google dropped the “don’t be evil” motto and its parent company (Alphabet Inc.) has “Do the right thing” motto ( ref: https://en.wikipedia.org/wiki/Don%27t_be_evil ). But the “right thing” for who, I’m willing to bet five thousand quatloos that it is always the right thing for Alphabet.
The anti-theft features have always been a moot point. The pickpockets and thieves don’t steal the stuff for themselves – they usually work for gangs who turn the stolen items into cash as quickly as possible, so your stuff will be on its way to Romania within 24 hours of you losing it. Even if you do get a ping of its location somewhere, it takes too long for the authorities to react before it’s out of the country.
Actually, not true at all. A quick google finds many news stories of iPhones (which have the same tracking), bikes, cars, etc. getting recovered – sometimes with the help of law enforcement, and when they can’t be bothered, sometimes without.
I would expect some cases to end that way, especially when it’s amateurs doing the stealing, or some local kid who didn’t think things through.
Meanwhile, over half the cases of street theft around here are done by foreign transient groups who travel from country to country just to steal stuff and then get out as fast as possible. Then half of the remaining half is done by local criminal gangs who have similar tactics: get the stuff out of the country as fast as possible to turn it into cash without getting caught.
A simple method they use to foil any tracking devices is to put the items in foil lined bags, then extract the devices later in some remote location, preferably one without cellular coverage.
“A simple method they use to foil any tracking devices is to put the items in foil lined bags, then extract the devices later in some remote location, preferably one without cellular coverage.”
With Starlink that may no longer be the case.
Starlink needs a special phased array receiver to work. It’s quite power hungry, so a battery operated tag has no hope to use it.
You might want to look at the RF signal ranges in my post above. Summary 4 cm to 100 meters (~1.6 inches to ~330 feet). If there are no iProducts inside that range to relay the encrypted message back to the Apple Inc’s metadata loggers. And I’m guessing that the iProduct returns the signal strength and it’s GPS location in addition to the message from the tag.
It will not be on its way to Romania or in a chop shop or smelted down for raw metals in 24 hours. You ascribe far too much agency and efficiency to these thieves. My friends and I have gotten plenty of things stolen in the past couple years, and thanks to stuff like this we’d find it several blocks away a day or two later amongst an encampment of people on meth and fent, or crashed into a retaining wall, or at a pawn shop missing parts.
I’ve used trackers at least four times in the past year or so to good effect.
I’m going by statistics. Your mileage may vary.
I’ve heard rumors that the tracking alert can be beaten by simply adding a circuit to turn off the tracker for a few minutes at a time every little bit. Of course you lose some “resolution”, but generally you are wanting to find where your stolen item stopped for a period of time.
Person tracking is the most valuable aspect of BlueTooth LE trackers.
Had my Alzheimer’s afflicted ex-Calculus teacher been wearing an AirTag when he went out for a walk, he might have soon been found safe and well, rather than in a desiccated state, many months later, and very many kilometres away, in a lonely roadside strip of bush.
I’ll make no effort to defeat such technology on my mobile phone. It might save a life.
Stalkers will inevitably do what they will do, AirTags or not.
Unless there were lots of iDevices loitering in that lonely strip of brush there would be no signal. We got one of these for our dog who, whenever she gets, free bolts. There were no pings.
Control your dog, and it won’t be a problem.
It’s up to the humans to be attentive to doors and leashes, and prevent repeats of the same escapade.
For the good of society, I think it’s more important that stalking is prevented. Apple should issue an automatic firmware update that detects this and bricks the tag.
Apple and doing the right thing though…
As long as they sell more tags, they’re good.
Simply add a way to sign the tag as anti theft and only trackable by the owner, with severe legal penalties for misuse.
There are already legal penalties for using tracking devices to stalk people.
There’s already severe legal penalties for misuse, the stalker isn’t required to sign anything to be liable.
They will just recruit minors to steal your stuff. Minors will in some areas not be prosecuted and released immediately if caught.
This is such a first world problem
I dream about send message trought it.
manu users and offline communications in town
I spent a week playing with these trackers in 2022, wrote up what I learned here, may be of interest:
https://www.hotelexistence.ca/exploring-bluetooth-trackers-at-geekweek-7-5/
My group played around with ideas for building “stealth” Bluetooth trackers that evaded detection (rolling identifiers, random broadcasts – thought about adding an inertial sensor to only broadcast on movement, but never quite got there).
And we also played around with detection – how you might check to see if you were being tracked by a “stealth” Bluetooth tracker.
More serious/in-depth work in this area has been done by the Secure Mobile Networking Lab, previously reported in Hackaday: https://hackaday.com/2021/03/05/get-apple-to-track-your-bluetooth-devices-for-you/
So, who is going to confront a criminal thug?
Anything you do can be used against you, love liberalism.
So is there a way to detect these things without a smartphone? Can you program an SDR to alert you if it sees the same bluetooth ID a few times in a row?