Did you ever wonder what your monitor and your computer are talking about behind your back? As it turns out, there’s quite a conversation going on while the monitor and the computer decide how to get along, and sniffing out VGA communications can reveal some pretty fascinating stuff about the I²C protocol.
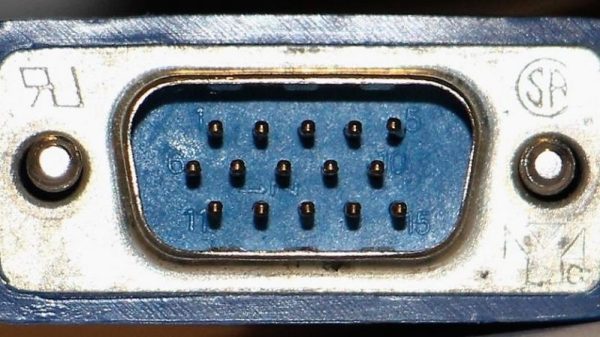
To reverse engineer the configuration information exchanged between a VGA monitor and a video card, [Ken Shirriff] began by lopping a VGA cable in two. The inside of such cables is surprisingly complex, with separate shielding wires for each color and sync channel and a host of control wires, all bundled in multiple layers of shielding foil and braid to reduce EMI. [Ken] identified the clock and data lines used for the I²C interface and broke those out into a PocketBeagle for analysis using the tiny Linux machine’s I²C tools.
With a Python script to help decode the monitor’s Extended Display Identification Data (EDID) data, [Ken] was able to see everything the monitor knows about itself — manufacturer, serial number, all the supported resolution modes, and even deprecated timing and signal information left over from the days when CRTs ruled the desktop. Particularly interesting are the surprisingly limited capabilities of a VGA display in terms of color reproduction, as well as [Ken]’s detailed discussion on the I²C bus in general and how it works.
We always enjoy these looks under the hood that [Ken] is so good at, and we look forward to his reverse engineering write-ups. His recent efforts include a look at core memory from a 50-year old mainframe and reverse engineering at the silicon level.