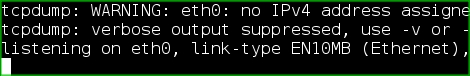
Here’s a chance to learn a little bit about network security. This article walks us through some of the core concepts of network manipulation and packet sniffing using Linux tools. [Joey Bernard] discusses the uses for packages like tcpdump, p0f, and dsniff. They are capable of recording all network traffic coming through your computer’s connection, seeking out machines installed on the network, and listening to traffic for a specific machine. This isn’t going to give you a step-by-step for cracking modern networks. It will provide some insight on what is going on with your network and you should be able to purpose these tools to check that you’ve got adequate security measures in place.











