Well it looks like the Play Station 3 is finally and definitively cracked. FailOverflow’s Chaos Communications Congress talk on console security revealed that, thanks to a flaw on Sony’s part, they were able to acquire the private keys for the PS3. These keys can be used to sign your own code, making it every bit as valid (to the machine anyway) as a disk licensed by the media giant. We’ve embedded the three-part video of the talk, which we watched in its entirety with delight. We especially enjoy their reasoning that Sony brought this upon themselves by pulling OtherOS support.
We remember seeing a talk years back about how the original Xbox security was hacked. We looked and looked but couldn’t dig up the link. If you know what we’re talking about, leave the goods with your comment.
[youtube=http://www.youtube.com/watch?v=HEFMAP0mTvY&w=470]
[youtube=http://www.youtube.com/watch?v=X8ohOy8_XO4&w=470]
[youtube=http://www.youtube.com/watch?v=Eag0VyRTld8&w=470]
[Thanks BoBeR182 via The Register]
















The talk is called “17 Mistakes Microsoft made in the Xbox Security System”. Extensive info, including videos of the lecture, can be found at http://www.xbox-linux.org/wiki/17_Mistakes_Microsoft_Made_in_the_Xbox_Security_System
A very interesting talk. I am always amazed by the genius of these console hackers.
Any links to download the videos?
Cool to hear, SONY is known for this kind of thing though. (Failing at DRM, that is)
Happy day!
Xbox talk: http://www.youtube.com/watch?v=9NqLljaHc80
I found this interesting youtube vid on xbox security http://www.youtube.com/watch?v=ktENZ2gyixg
@Spork: Use force…use JDownloader
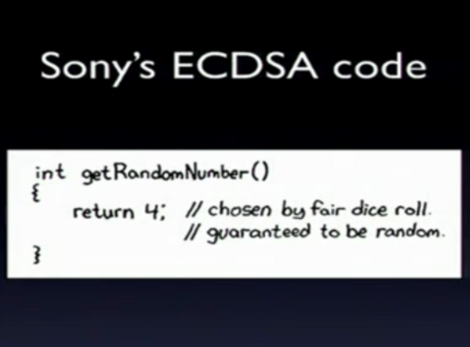
Wow, that truly is epic fail. Can’t wait to dig through failOverflow’s code… the stuff console hackers come up with always makes my brain melt. Also, love the XKCD reference, that one always makes me laugh.
Their x86 mighty commercial game DRM is still the same encrypted VM EP and ‘jump bridge’ engine that everyone in the RCE scene has been defeating since day one, even though it sees at least 3 updates a year.
Also read my comment on nano 6G reversing were I state it’s all memory corruption..This is an overflow in the revocation loader and poorly implemented keying.
They are still using Geohot’s work, which was before otherOS removal..Linux drones should remember that..it was the same morality with the x360 and wii..
I’d say they did pretty good at DRM, the PS3 is several YEARS old, likely THOUSANDS (or more) hard at work trying to crack it, and it finally succumbed. I am ashamed that companies feel the need to preclude paying customers from doing what they want, the pirates will always win in the end.
Oh god… hahahahaha that’s great!
i believe this may be the thread from 2003 that you may be looking for. the original project was the neo
http://theneoproject.com/
i remember those early great days of mod chips on the xbox. the evolution x and matrix chip made me the geek i am today
peace
seamonkey420
doh! link no longer is live :( however, here’s the slashdot article from 2005 referencing the private key project for the xbox
http://slashdot.org/articles/03/01/05/1456203.shtml?tid=109
Here’s a video on the Xbox 360, from the same conference three years ago: http://www.youtube.com/watch?v=XtDTNnEvlf8
@andar_b
Hackers broke one layer of security and every other security messure turned out to be useless. Doesn’t sound very good to me. Just because it took a while to crack doesn’t mean Sony did good. A majority of the hackers with the skill to do this didn’t bother because they had OtherOS.
@andar_b As they said in the video, while the PS3 still had OtherOS, there was little motivation to try and hack it. Once OtherOS disappeared, the timeline to breakage was comparable to that of the XBox 360.
While these guys do awesome work, and they are heroes in my eyes. They should let only 1 of them do talks. The one that did the statistics part.
It’s not the horrible accents (as dutch guy I can accept those) it’s just that giving a talk is a skill, and not everyone possesses that skill.
Cracking the Code was not easy…
1… Nope
2… Nope
3… Nope
4… Nope
(Now you know why it took so many years…)
Interesting note: This is leveraged off an exploit that was epically documented and published way before OtherOS removal. What is more is that otherOS has already been done off the dongle descriptor overflow, this just allows fake signing, so you can make true custom update packages now..
It should also be noted that x360 and wii were done by NT vuln-dev and RCE people, not Linux users..In fact the actual author of the x360, like Geohot who did the PS3, rarely touches a Linux shell..I know him personally as he also does work for Core Security.
@’took long’-sayers: They make the (imo valid) point that no-one seriously started hacking the system until Sony pulled the otherOS-feature, and seeing the omghuge amount of fail the team uncovered in a short amount of time, I tend to believe them.
Btw: They never stated where we could find the keys, but on the day of the talk all of a sudden small stickers appeared all over the congress building 27c3 was held in, with different QR-codes on them… you may guess what was on them :P
it was theneoproject.com that started it but it got moved in march 2003 to operationprojectx.com
here is an article from March 2003
The XBOX Attack
The goal of Operation Project X is to crack the 2048-bit RSA private encryption key Microsoft uses to sign Xbox media. The goal of this project is to make it possible to run Linux on a Microsoft Xbox console without a so-called modchip. A total of US$ 100,000 will be awarded by Michael Robertson (“donor”). Here are the rules, taken from Xbox-Linux.sourceforge.net
Project B Prize Rules
by Michael Steil,Milosch Meriac,Andy Green, 24 January 2003
Overview
As the goal of the original Project B of the Xbox Linux Award has not been met, this part of the award will be extended until December 31st 2003. Furthermore, the rules will be extended, so that solutions that use very different methods can be awarded as well.
The Microsoft Xbox is a PC-like gaming console that uses public key cryptography to prevent the user from running executables that have not been authorized by Microsoft. That is, the user buys PC hardware, but does not get the possibility to run applications Microsoft does not like, such as the GNU/Linux operating system. So, although the user has paid for his hardware, Microsoft controls which software can be used and the result is a Microsoft-only PC.
Hardware modifications exist that give the user the possibility to run arbitrary code back, but these require opening the Xbox.
The goal of Project B is to make it possible to run Linux on a Microsoft Xbox console without a so-called modchip. A total of US$ 100,000 will be awarded by Michael Robertson (“donor”).
Goals
The core goals are to be able to boot Linux on an unmodified machine, preferably by CD without opening the case, but via code directly copied to HDD or a USB device is acceptable too.
The prize fund will be allocated by a committee chosen by the donor at the end of the period. People working in public, sharing good information on the ML, will naturally have a higher profile with the committee.
Prize money will be allocated only for solutions that the donor can reward without getting his ass kicked into jail.
If there are multiple groundbreaking solutions by the end of the contest, money will be allocated between them as fairly as possible.
The committee may choose not to allocate all of the prize fund if all of the core goals are not met.
All specific technical informations like PCB-Layouts, Binaries, ROM contents etc. that are needed to reproduce the solution have to be released using an appropriate Data Format and under GNU/GPL, GNU/LGPL or MPL license.
Solutions must be practical in the sense that a 12 year old kid can hope to replicate them in terms of both complexity and cost
Example reward scenario
The goals are deliberately not very specific about methods and rewards because the kinds of contribution we may get – and the mixture of them – are so unpredictable. For example, since some approaches may only make it possible to 1) boot Linux only from Optical media, and others 2) only from hard disk (and both will be needed), the committee may decide to split the award into two parts accordingly (in all these examples, it will be up to Committee to assess events and actually decide for themselves, these are just examples we can imagine, but circumstances and multiple entries could change everything: that’s why there is a committee to decide at the end).
Partial Solutions
Both goals can be reached either without additional hardware or with additional hardware (“partial solution”). If no additional hardware is needed, $50,000 may be awarded; if additional hardware is needed (e.g. for HDD and Optical media: an external device connected to USB or Ethernet, for Optical media: a CD/DVD that cannot be created by the end-user, but must be bought) only $15,000 might be awarded.
Example: The design of a USB device that, when connected to an unmodified Xbox, makes it possible to boot Linux from a CD, might be awarded with $15,000, because it solves only a part of the Optical challenge. If it can boot Linux both from hard disk and CD, it could be awarded with $30,000, because it solves a part of both the HDD and CDROM problems.
Example: A hard disk image that, when put onto the Xbox hard disk, will boot Linux from hard disk (but this image won’t work for CDs), might be awarded with $50,000 because it fully solves 1. A CD image that makes it possible to boot Linux from CD without any hardware modification may be awarded with $50,000, because it solves the Optical method entirely. An XBE file that boots Linux from either HD or CD/DVD, depending on where the file is stored, could be awarded with the full $100,000 because it solves both problems.
In the event of a full solution (workable from HDD and Optical) becoming available before any other method, it is likely to get the full award and later partial solutions little or nothing; this is to encourage the most valuable HDD and Optical solution first. If there are partial solutions first, and then later a full (HDD and Optical) solution, we imagine the committee sharing any award a bit more evenly.
Rules
General Rules
Sharing knowledge about previously unknown facts, code and hardware schematics get honored.
If you find something out, don’t keep it to yourself to be the only one to be able to write code based on it. Share it with the others, your work will be honored anyway. Work on reverse-engineering devices of course gets honored, too.
To be honored, work must be submitted to the “xbox-linux” project at Sourceforge, either to a developer or to the Mailing List. It is not enough to publish information/code somewhere else.
We want people to work together, so there has to be a central point where all work concentrates.
Every step has to be published, people have to work in teams.
Development is much faster when people work together.
Work that has already been done before this initiative has been started can be honored, too.
But please submit it to the Xbox Linux Project.
With “Xbox”, we refer to the majority of the Xbox consoles on the market when this initiative was started.
If MS changes their box, that shouldn’t negatively impact someone’s successful work on an older box for sure. But all solutions should at least work on v1.0 and v1.1 boxes, or else not all money will be awarded.
Awards
All awards are determined by the awards committee. All decisions are final.
The committee is chosen by the donor.
The exact values of may change if the complexity a task was over- or underestimated. The 100.000$ for are always fixed, though.
It’s hard to tell how difficult the different tasks will be. To be as fair as possible, the values may be adjusted a little.
Completion of each step will be determined by the awards committee.
Awards may be split between groups at Award committee’s discretion. Group contributions should designate the lead participant who the awards, if any, will be distributed to. For group contributions, it is the responsibility of the lead participant to disburse the funds.
It will be impossible for the awards committee to decide the participation level of each person of a group, so we defer to the group coordinator.
The outer limit on the initiative is December 31st, 2003.
Please understand that we cannot wait forever.
Legal issues
All solutions have to be legal.
If there is any doubt about it, the legality of the solution has to be proven, before you can get awarded any money.
Legal issues are up to the individual participant, not the project.
People that are working with (possibly) illegal methods may not participate.
Don’t use the Xbox SDK. If your are a game programmer with NDA knowledge of Xbox details, don’t participate.
Nobody has the right to get money.
Don’t send us to court. This is supposed to be fun. We will do our best to be fair.
Legal aspects can be discussed on the Mailing List.
There are many additional opinions there.
Getting Started
If you want to participate in the project, you should read the documentation on the Project Website and join the Mailing List.
SOOOO LOOOONG AGO NOW!!!
Deconstructing The Xbox Security System is the talk I think you maybe referring to. It’s a fantastic talk about the security models, really simple to understand, highly recommended.
http://video.google.com/videoplay?docid=-4356347903120410001#
1:02:17 – 4 years ago
Google Tech Talks December 1, 2006 ABSTRACT In late 2001, Microsoft released the Xbox, their first gaming console, to compete against Sony and Nintendo in the living room. As the real money is made with the games and not the consoles, Microsoft had to make sure (as much as they could) that nobody could play pirated games or use the machine for anything other than games. Although the original security design idea was a good one and has been copied a lot since then, Microsoft’s inexperienced team made a variety of design, implementation, and policy mistakes. This talk first (re)constructs the design of the Xbox security system from Microsoft’s point of view, and then deconstructs it from the hacker’s point of view. As a bonus, the talk will feature some insights in the security system of the Xbox successor, the Xbox 360. Michael Steil is the founder and maintainer of the Xbox-Linux Project. He oversaw most of the Xbox hacks and also contributed to hacking, reverse engineering and porting Linux on the Xbox. Google Tech Talks December 1, 2006 ABSTRACT In late 2001, Microsoft released the Xbox, their first gaming console, to compete against Sony and Nintendo in the living room. As the real money is made with the games and not the consoles, Microsoft had to make sure (as much as they could) that nobody could play pirated games or use the machine for anything other than games. Although the original security design idea was a good one and has been copied a lot since then, Microsoft’s inexperienced team made a variety of design, implementation, and policy mistakes. This talk first (re)constructs the design of the Xbox security system from Microsoft’s point of view, and then deconstructs it from the hacker’s point of view. As a bonus, the talk will feature some insights in the security system of the Xbox successor, the Xbox 360. Michael Steil is the founder and maintainer of the Xbox-Linux Project. He oversaw most of the Xbox hacks and also contributed to hacking, reverse engineering and porting Linux on the …all » Google Tech Talks December 1, 2006 ABSTRACT In late 2001, Microsoft released the Xbox, their first gaming console, to compete against Sony and Nintendo in the living room. As the real money is made with the games and not the consoles, Microsoft had to make sure (as much as they could) that nobody could play pirated games or use the machine for anything other than games. Although the original security design idea was a good one and has been copied a lot since then, Microsoft’s inexperienced team made a variety of design, implementation, and policy mistakes. This talk first (re)constructs the design of the Xbox security system from Microsoft’s point of view, and then deconstructs it from the hacker’s point of view. As a bonus, the talk will feature some insights in the security system of the Xbox successor, the Xbox 360. Michael Steil is the founder and maintainer of the Xbox-Linux Project. He oversaw most of the Xbox hacks and also contributed to hacking, reverse engineering and porting Linux on the Xbox.
Now we just wait and see if this is just BS as was with Wii and x360. Still don’t see Linux on those xD just more piracy..
By the way the system was hacked way before removal of OtherOS..it even made headlines and is still doable even on non-OtherOS machines with an XDR FPGA..
There is this book too.
Hacking the Xbox: An Introduction to Reverse Engineering.
http://www.cad-comic.com/sillies/20101230/
This comic pokes fun at the PS3 being cracked, I am not posting it to offend anyone, I just thought it would get some laughs.
Anybody who remembers the XCP DRM mega-fiasco where Sony BMG got caught using pirated code as part of their anti-piracy protection would not be surprised that they shot themselves in the foot again.
SONY *HATES* THEIR CUSTOMERS!
@xorpunk:
There is linux on the Wii, and something called the homebrew channel:
http://wiibrew.org/wiki/Homebrew_Channel
http://wiibrew.org/wiki/Wii-Linux/Distros
Are the actual AES and DSA private keys (i.e. the things you need to create and sign PS3 executables so they can run on any unmodified PS3) out there yet?
Too late for me,
My PS3 simply died after the updates, and I now play on a cheaper 360.
F.U. Sony… the stench of that rotting giant will linger fore some time.
@Jonathan Wilson:They show how to dump them from LS using revocation overflow. You can expose everything on PS3 now except what loads lv0 on the CBE, and I think a few SPU binaries.
One thing they poorly assume though is that SCE can’t patch the overflow without breaking old code.
Not only can they fix PKI while keeping old keys, but they can fix everything outside what loads lv0 in ROM. LS memory overlaps as was demonstrated before geohot in the phrack paper, all it take is bounds checking on the SPE mailbox DMA..
Also note that lv2 has no w^x, so you can leverage a full attack from lv2 LPAR if all you care about is Linux, and keep doing it..
The thing that ruins these talks for me is the guy that says “This isn’t about piracy.. we want to run homebrew!”. Yes, that may be true.. but if you just want to run your own code you don’t buy a locked down/fairly expensive machine to do it. Why would you buy a PS3 for Linux? Why in hell would you buy an unsupported machine? Why would you pay through the nose for it? That explanation makes zero sense.
I get no impression that the reason people spend time cracking security systems like these is to run Snes9x ports. If I had to guess I would say it was more of a pissing contest i.e. who can crack it first and interest in how the hardware works. I can totally understand that.. but why the hell do they need a guy with some slides that basically conclude “If they let us run our own code we wouldn’t crack the security for the profit-making part of the device”, which is total crap. You can run whatever code you like on Windows and that hasn’t stopped anyone from trying to crack all the different protections that come along.. 99.9% of Linux distributions are open source software, but you still see cracked versions of commercial software floating around.
Making out that the reason the PS3 has been cracked now is that the OtherOS option was removed is just crap. Utter crap. How many people even cared when that was removed? How many people bitching about Sony being assholes for not allowing third party code actually intend to write/run any code?
It’s been broken now because certain people have come up and delivered discoveries that have changed the whole outlook. Ironically (in contrast to it’s for homebrew! think of the children! guy’s opinion) the PSJailbreak (piracy device) appearing seems to have accelerated work considerably…
Except it’s quite conceivable that what we see on consoles and mobile devices such as the iPhone in regards to lockdowns will be on pcs in the not too distant future.
It’s you device. You should be able to run what you like on it. If the side affect is piracy, so what! That’s ms/sce’s problem.
Imagine a pc where you can’t install Linux because only those dirty pirates want to run unsigned code!
This kind of hacking sends a message to these companies that they either work with us (so token Linux support) or we will find a way around them and it’ll be worse for them in the long run.
Also have we forgotten http://en.m.wikipedia.org/wiki/Sega_v._Accolade?wasRedirected=true already? Im looking forward to being able to buy 3rd party games from smaller developers who can’t afford to be a Sony licensee but can now sign their own games. It’s a win for consumers in many, many ways.
cause its cool to run linux on a 65 inch plasma on a set top box, then double click the power switch and run GOD OF WAR!!!
same with me and my XBOX 1, eh maybe I want to watch google video, maybe I want to watch something I stored on my hard drive, maybe I want to listen to shoutcast on my big sound, maybe I want to play some NES games (that I have the carts for, a entire foot locker worth along with snes and sega G games) fuck maybe I want to play psyconauts
I dont even have to get off my ass as its all in 1 box with a dvd remote and a wireless logitech controller
with most of the work done for me just add media and go
SCE Bent them selves over and lubed up for this when they removed Otheros. NO ONE but them are to blame for motivating the community to hack their console. Those with the ability refrained until SCE tried to screw already paid customers out of what they bought. Eventually they will learn not to futz with their loyal customers AFTER they pay. Otherwise you can expect to see game developers flock to other consoles.
ps cantido your the bottom of the barrel.
@cantido
“Why in hell would you buy an unsupported machine”
but when they did buy it it was supported
And the ps3 is a really cheap cell development station you could ofcourse buy this instead
Mercury Systems is offering the Cell processor on a PCI Express card for only $7,999. That’s otherwise known as a waste of money.
the ps3 is starting to look cheap or?
“How many people even cared when that was removed?”
it dosent matter how many, what matter is that the people that did care have the skills to make it run again.
What’s going to be funny is in a year++ from now when there still isn’t a Linux on the PS3, and it turns out just like Wii and x360 that were also claimed to be hacked to run Linux.
Also this is leveraged off Geohot’s hack which is what caused removal of OtherOS and Piracy..it appears people with skills can also suffer from talking before thinking ^^
@Dizzey
>>but when they did buy it it was supported
The OtherOS feature comes/came with no warranties implied or otherwise from what I can tell.. The PS2 linux kit was the same IIRC.
>And the ps3 is a really cheap
>cell development station
Unmodified you don’t have access to everything. You don’t get any sort of official development support or documentation. Doesn’t sound like a good cell development station to me. Sony’s official developer kits are probably a lot more than $8K.
>Mercury Systems is offering the
>Cell processor on a PCI Express card
>for only $7,999.
Do you have to have a cell processor for running Linux? Is it even well supported? Is it all that different from a PPC Mac running a PPC Linux distro? Does the architecture make much sense as a consumer grade computer? I guess for your ~$8K you get an unlocked platform, documentation, debugging support etc? If there was huge demand for Cell development kits there would be some cheaper kits out there like there are for ARM.. I guess the demand just doesn’t exist.
>That’s otherwise known as a waste of money.
Depends what you want to do doesn’t it? If you **really** need a Cell processor for something I would guess that ~$8k isn’t actually that much and that using consumer grade hardware with no support from the vendor for your intended use might end up more expensive especially if said vendor doesn’t guarantee hardware availability, continued support for however you’re loading you application (OtherOS here), you have to reverse engineer your own hardware documentation … oh, and how the hell do you interface the cell processor into anything external? With that $8K PCI-E board you get Rapid-IO etc support..
I really doubt Sony would replace units under warranty that have been used as part of some HPC cluster. Sony subsidize the cost of the hardware and have no interest in providing cheap hardware to Cell developers.
>> it dosent matter how many,
From all the bitching about the removal of the OtherOS feature you would guess that thousands and thousands of people depended on it.. I really doubt that is the case.
>>what matter is that the people
>>that did care have the skills
>>to make it run again.
Which is really great. It’s nice to see people that want something to actually do it instead of just saying “why doesn’t someone do this ..”
There is (or at least was) for example support in the mainline Linux source for a few machines that have a total of 1 in existence.. that’s some real dedication.
Just guessing here again, but I reckon people would have been trying to break into all the various security systems if OtherOS was still present today. The argument that no one would have bothered hacking the system if full access to the hardware was allowed is also moot.. the security here is 99.5% based on the fact that the end user and their software has limited control, people buying that software is the main way that it makes profit (which isn’t optional) so there’s no way in hell you’re getting access to the hardware. This whole argument is pretty much identical to “I hate adverts on google, youtube etc moan moan moan.. but I won’t pay anything for those services either”.
@addidis
>>SCE Bent them selves over
>>and lubed up for this when
>>they removed Otheros.
So no one in the world was trying to hack the thing from day one? Sony most likely removed the OtherOS feature just to save themselves headache opposed to being hugely worried about security implications and obviously it had no commercial interest.
>>NO ONE but them are to blame
>>for motivating the community to
>>hack their console.
“the community” being 99.99% teenage kids posting “I haz haxed the PS3” and like 5 people that actually know anything?
>>Those with the ability refrained
>>until SCE tried to screw already
>>paid customers out of what they bought.
Is that really the truth? Really really really? Isn’t it more the case the Geohots work and the PSJailbreak came along which shed huge amounts of light on the
situation? The OtherOS was an unsupported freebie from everything I can find. I can’t find any usage numbers but I guess that people using the OtherOS feature on a daily basis is in the thousands max.. how many million units have shipped?
>Eventually they will learn not to
>futz with their loyal customers
>AFTER they pay.
The customer paid for a PS3. Which is a proprietary games console that is intended only to run software licensed by Sony. The customer knew that when the bought it and agreed to various EULA’s etc to that fact (Forget the fact that they aren’t really all that legally useful in a lot of places).
>>Otherwise you can expect to
>>see game developers flock to
>>other consoles.
Which all have the same/similar security features.. because game publishers want those features? If game publishers were against this sort of thing why do they ship Windows games with all sorts of awful protections like online saves etc?
@osgeld
You can get an X86 box to do that for considerably less. It’s not like the PS3 (or Xbox 360) are silent which would make them good for media center.
You can get a Atom or Core machine with a GPU that supports DXVA or VDPAU, 4GB of RAM, VESA mountable case etc for less than a PS3.
>>ONCE AGAIN..PS3 WAS HACKED *LONG* BEFORE OTHEROS/LINUX REMOVAL!!<<<
the pseudo-ethical marketing is nice though..the original dongle makers also used it even though their product *also* till this day has no homebrew and/or Linux framework..they even protect it..
It's really annoying reading all this garbage, and to all these Linux drones(who never used the feature in the first place which was an assisted cause in it's removal..) please DO point us to where we can get these Linux loaders that were the supposed cause of all this DRM circumvention(I'm sure the game makers who can't cover dev and publisher costs will also like to see these too..since they are the *only* reason other than piracy ^^)
@xorpunk
If people are going to be pissed off about anything it would be the gradual removal of PS2 emulation. Did anyone really care about that? That was a selling point for some people..
Anyhow, there is Linux on the PS3.. I’m not sure if it’s terribly usable. Has anyone written a decent graphics driver for the RSX chip yet? That was the point of all this work right? To load Linux and unlock access to the RSX hardware.
If you want an expensive l33t Linux box why not get an Atari Falcon or something? I hear Debian m68k is coming back to life.
Can someone explain to me why this cannot be solved by software updates in a few lines?
And from what i gather fixing this flaw would make the system very hard to crack?
@Gert
Because they now have the keys that Sony use to sign software. ie, now anyone (with the skillz) can create an updater for the PS3 which is signed as being valid Sony software.
So, if Sony create an update to change any of this, a user can load a custom update that the PS3 will happily run to change stuff back, because it’s signed, it looks like it comes from Sony.
Essentially, the PS3 can’t tell where software is from, and wil happily run anything it’s given*
*except they’ve not got all the keys, enough to run Linux, but not yet enough to eg boot off a blu-ray, and they say they’re not interested in finding those keys.
@xorpunk
http://wiibrew.org/wiki/Wii-Linux
http://free60.org/Linux_Kernel
http://git.marcansoft.com/?p=ps3-linux.git;a=summary
Also, if you can find a system with 250gb hd, wifi, bluetooth, gigabit ethernet, a processor capable of decoding h264 in real time, a blu-ray player, a remote controller, hdmi and the ability to play a large library of games for 300€, all with a nice design, please let me know.
The PS3 has the potential to become a very nice and complete mediacenter, thanks to Linux.
Still some questions.
What if Sony now puts out an update that updates the system so it can not install new software using the old signing method.
It uses the old code to update on last time and uses a new/fixed method for future updates?
The hacker would not update becasue it renders his PS3 useless for custom software.
Or would this make old Blu-Ray discs useless?
If Sony would fix it now they could be quick enough before this knowledge spreads to far.
OK, hackers. Your challenge, should you choose to accept it is to build a mobile robot based on the PS3, capable of interacting with its surroundings and processing visual, audio and other inputs in realtime.
You may remount the pcb in a carrier as needed, to make it more compact/improve cooling.
any takers?
i’d expect the Cell architecture to be ideal for this, as the individual cores are effectively separate and can be retasked to process data as needed.
blows SBCs out of the water on power consumption alone.
@junkordure: You might want to look at what is actually at your links..
Here is a hint:
-Wii: kernel running in thread that has partial frame buffer driver and has 0-support for most of Linux even in kernel land. It gets updated maybe once a year..
-x360: Even less updated than Wii, just *slightly* more support because it’s not ARM. Gets even less updates..
-PS3: A thread that jumps to a stripped kernel that literally does nothing more than provide debugging for further RCE..
*The time stamps speak for themselves too*
It also doesn’t help that Marcan is 1/5 developer for PSGroove which has more game loaders and active development than any commercial, or other warez scene, offering to date.
Within 1 month of PSJailbreak being reversed PSGroove got more bug fixes and payload variants related to games than the commercial product or any other tool, and still does..
Compare their time on AsbestOS to their time on game Backups, he even dropped the project while working on backup bug fixes months back..
I think some people are just getting high off their own supply xD
It’s always amazing to read how very little most people get it… Even on this website, which is supposed to be ‘hack oriented’.
Next time, instead of writing garbage, making (bad) assumptions about why it was cracked, the ‘real’ non-marketing hidden motivations and so on, just come to CCC, and come to talk to them at our table. Until then, you’re just plain insulting people you dont even know based on why _you_ would do it.
I thought it has been known for quite a while now that making _anything_ run linux is one of the main game in the hackers’ world. So if you think it’s just an excuse to run pirated games you’re very short sighted to say the least, and you really dont understand this ‘hacking thing”…
And btw, a lot of scientists, hell even the US gov, bought a lot of PS3 because it’s a cheap computing unit, and based on the idea they could run linux. Not that it changes anything about the ‘make it run linux’ game anyhow, just saying…
@Daid: yes, presenting a talk requires skill, but if you dont practice you’ll never have it. Same goes with anything. Moreover some parts were rushed because during reharsals the talk was too long (and some slides got removed in the last 30min for some other reasons) and in the end, they were surprised to finish it with 15min extra.
@cantido: are you being paid off by Sony to bash the hackers, or Microsoft to bash the PS3? I’m just wondering which one I need to apply to for the fat paycheck you’re obviously getting.
Wow. Those are some awesome videos.
It’s stunning that we got the PS3 keys before we ever got the Xbox (1) private keys.
@Pete: The PS3 can be patched like the x360 just by fixing bounds checking on a few loaders revoke mailbox code and using new crypto in a fresh lv0 :P
I’m interested in seeing when/if SCE does fix it if they put forth the effort, and also if they even really make an effort to put Linux back on the PS3 in the first place..good luck getting even GNU packages and a fixed PPC kernel going on AsbestOS ^^
Also X86 only has 3 isolations and TPM, and that’s only on recent architecture. This is why encrypted VM and dongle envelopes are the strongest protection you see, and a lot of people can’t even break these. It’s mostly just people who have been around a while doing it for ISO teams..a lot of warez groups can’t even touch SecuRom, Byteshield, Starforce etc..