[Jim] used a logic analyzer to do some in depth analysis of the Syma 107G helicopter’s IR protocol. We’ve seen work to reverse engineer this protocol in the past, but [Jim] has improved upon it.
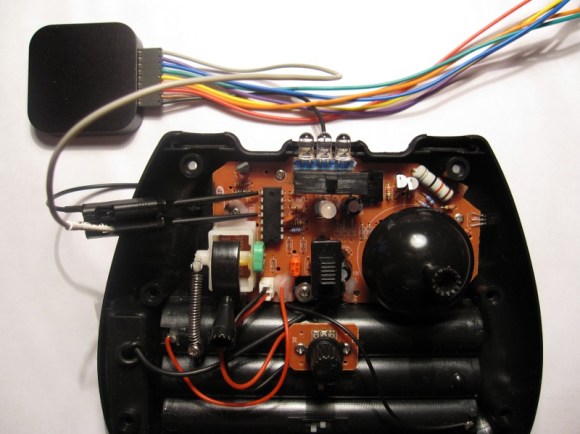
Instead of reading the IR output of the controller, [Jim] connected a Saleae Logic directly to the controller’s circuitry. This allowed him to get more accurate timing, which helped him find out some new things about the protocol. He used this to create a detailed explanation of the protocol.
One of the major findings is that the controller used a 3 byte control packet, which contradicts past reverse engineering of the device. There’s also a new explanation of how multiple channels work. This allows multiple helicopters to be flown without the controllers interfering.
The write up is quite detailed, and explains the reverse engineering process. It also provides great information for anyone wanting to hack one of these low cost helicopters. From the details [Jim] worked out, it would be fairly easy to implement the protocol on your own hardware.
















Thanks for the write-up. I have both the copter and the logic analyzer and have wanted to get under the hood and hack. Your contribution gives me a leg up. Again, Thank You for taking the trouble to document and post.
This is pretty cool:
http://www.cs.ru.ac.za/research/g09C0298/index.html
She built a system for a school project to autonomously control the S107.
This tiny remote control helicopter is very much amazing. Not only its movement is very stable, but the rotor speed, forward backward movements and turning can be all proportionally controlled as well. I thought it might be interesting to take a look at its control protocol to see how things are done.
Hey everyone – since this post is still generating regular traffic to my Blog, I just wanted to say that I’ve formalized my work on reverse engineering the S107G in an RFC-like document that should be much more convenient for those just interested in the protocol:
http://www.jimhung.co.uk/wp-content/uploads/2013/01/Syma107_ProtocolSpec_v1.txt
I’ve also written a simple prototype Arduino library for parsing the Syma protocol so you could use the S107 controller for other hacks/projects easily:
http://www.jimhung.co.uk/?p=1138
Thanks!
Jim