If you had to explain why you use one mobile messaging service over another to your grandmother, would you be able to? Does she even care about forward secrecy or the difference between a private and public key is? Maybe she would if she understood the issues in relation to “normal” human experiences: holding secret discussions behind closed doors and sending letters wrapped in envelopes.
Or maybe your grandmother is the type who’d like to completely re-implement the messaging service herself, open source and verifiably secure. Whichever grandma you’ve got, she should watch [Roland Schilling] and [Frieder Steinmetz]’s talk where they give both a great introduction into what you might want out of a secure messaging system, and then review what they found while tearing apart Threema, a mobile messaging service that’s popular in Germany. Check out the slides (PDF). And if that’s not enough, they provided the code to back it up: an open workalike of the messaging service itself.
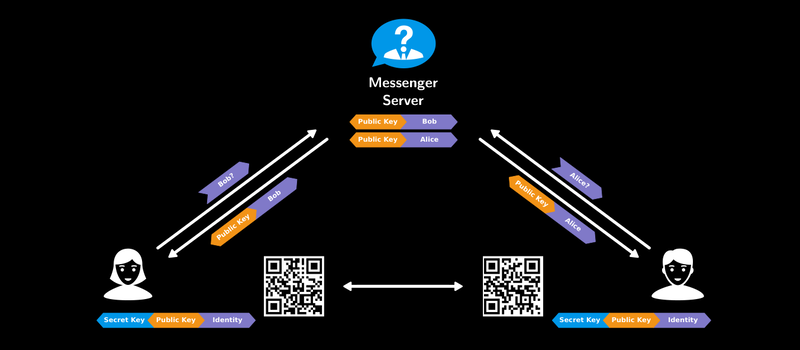
This talk makes a great introduction, by counterexample, to the way that other messaging applications work. The messaging service is always in the middle of a discussion, and whether they’re collecting metadata about you and your conversations to use for their own marketing purposes (“Hiya, Whatsapp!”) or not, it’s good to see how a counterexample could function.
The best quote from the talk? “Cryptography is rarely, if ever, the solution to a security problem. Cryptography is a translation mechanism, usually converting a communications security problem into a key management problem.” Any channel can be made secure if all parties have enough key material. The implementation details of getting those keys around, making sure that the right people have the right keys, and so on, are the details in which the devil lives. But these details matter, and as mobile messaging is a part of everyday life, it’s important that the workings are transparently presented to the users. This talk does a great job on the demystification front.
















Please stop using “grandmother” or “mom” as a stand-in for someone naive to the subject at hand. It’s sexist, and I believe you can do better. Thanks.
how about:
“If you had to explain why you use one mobile messaging service over another to your new dumb-as-a-bag-of-hammers President-elect, …”
that seems to work.
(sigh)
Don’t think that’s a suitable replacement at all.
My mum is perfectly intelligent and able to learn, but her computing knowledge are stuck back at the fortran/Cobol era, and crypto wasn’t on her Maths degree syllabus.
Your president on the other hand is a lying politician who’d hand over your crypto keys to every three-letter agency for your ‘safety’, and your new one adds a big dollop of stupid to that.
[/rant]
TLDR: I think Mum is a great stand-in for someone intelligent who we respect, but has no formal training in the specialist area.
Most politicians will hanf over the keys in the name of security because itbis the quickest and easiest means to and end. The difference between the outgoing and incoming president is that the incoming will tell you he’s doing it.
The security of an entire nation is always tough to balance with one’s individual privacy. Hell, the security of one’s children is just as hard. This is not to advocate that Big Brother should be able to monitor and analyze all of my communications, it is merely pointing out that it is a tough decision to make.
Ultimately it does not matter what decision is made, there will always be those who are unhappy with the decision.
LUV IT.
I wonder what he’s going to do next?
We should use him for everything.
Agreed—these little things add up.
Even doing something as simple as making the hypothetical idiot a guy is better…
(i.e. ‘so easy your grandfather could do it’)
its not sexist, its relatable. But people that have their politically correct knickers in a twist usually can’t make that distinction.
Dave Z. it is not sexist at all, and I am upset by the fact that you mentioned it here. You certainly wouldn’t have said anything about sexism had Elliot Williams used “your father” or “your grandfather” instead of “your grandmother”.
It is because of reasonings like yours that REAL sexism is so rarely taken seriously.
+10
It is also fun to notice how we tend to be sexist in our perception of sexism.
You’re upset because someone disagreed with you and shared their opinion in the comments section of an article? Boy, you must be real upset, real often…
Maybe you’re right that I wouldn’t have called Elliot out if he’d said ‘father’ or ‘grandfather’, but the world also doesn’t have a shortage of male engineers, and we don’t have a problem where important fields in math, computer science, and many scientific disciplines are missing male voices.
Welcome to 2016. Sexism doesn’t always look like a woman being passed over for a promotion in favor of a man. Or being judged by how tight her top is, and not her CV. Those things still happen, btw, but sexism also looks like a world where expectations are subtly communicated by the choice of words. Using the generic ‘your grandmother’ when you actually mean ‘technically illiterate person’ implies that you don’t expect women to become technically literate, or worse, that you don’t believe they are capable of doing so. There are plenty of other prototypes of technical illiteracy — grade school students, someone living in an underground bunker for the last ten years, etc. — pick one that doesn’t put someone else down.
(And if you think “words don’t matter,” just remember how upset you got just reading my three sentence comment…)
What was this article about again . . . . . oh yeah . . . . message security.
All you off topicers go bitch slap yourselves somewhere else please.
Yes!!!
Is grandparent or parent less offensive? Either way, just because you perceive it as sexist, does that mean it is? If anything, I would say it is more “ageist” or “generationist”. I’m sorry. I really believe this is not the place for this kind of discussion. I would think we would use the comments section to discuss the topic of the article. But I’ll bite and he a noisy hypocrite.
It isn’t sexist. If it was more along the lines of “imagine you are explaining it to a woman” then it would be sexist. But the generic person here is grandma. The generalization is made about grandmothers. I suppose it is pretty terrible that some people have the idea that, in general, grandmothers aren’t well-versed or interested in encryption….The terrible thing is that grandma is being used as ULTRALAYMAN: everyday folk don’t know much about it, so grandma REALLY don’t. But it has little, if anything, to do with gender.
Do you ever stop and think about how absurd it is? Why do people worry so much about words? If a person showed you a plot of some data of “[characteristic] vs [type of person]”, would it bother you? I can completely understand being outraged when somebody holds some belief like [type of person] is incapable of [x]. But what if I type “girls do not like math”? I am POSITIVE that it is, in general, a demonstratable truth. I am also positive that many people would really get bent out of shape, not only by the statement, but even more by my insisting its truth. What about “people like math”? Would that rub anybody wrong?
As an isolated article, I agree it’s not a bid deal. Further, this article goes on to suggest your grandma may even be a better hacker than you (my aunt certainly is). That said, I also sympathize with what the OP is getting at. A less polarizing label for the use of grandmother here might be to call it a stereotype. Unfortunately there is an overuse of negative female stereotypes in all media and collectively they have a compound effect that reinforces sexism. Whenever you use a stereotype you run the risk of insulting someone or a group of people; that was the entire basis of humor behind the Geico “So Simple a Caveman Could Do It” ad campaign. I believe the OP is suggesting that we all make a conscious effort to not use these stereotypes. This seems especially important in the STEM fields covered by hackaday articles which are notoriously over-represented by men.
As per the article itself, it didn’t do much to get me excited about the technical presentation (even though I love the topic in general). Maybe I just need some coffee.
“Please stop using “grandmother” or “mom” as a stand-in for someone naive”…
If you look through my posts here on Hackaday, you’ll see that I just about as frequently use “father-in-law”. These archetypes are actual people in my life. I’m sorry that some of them are women. And that my dad is very tech-savvy. (But not as much so as my wife.)
“Cryptography is rarely, if ever, the solution to a security problem. Cryptography is a translation mechanism, usually converting a communications security problem into a key management problem.”
Maybe the Chinese are on to something?*
*http://theindianeconomist.com/china-satellite-quantum-physics/