
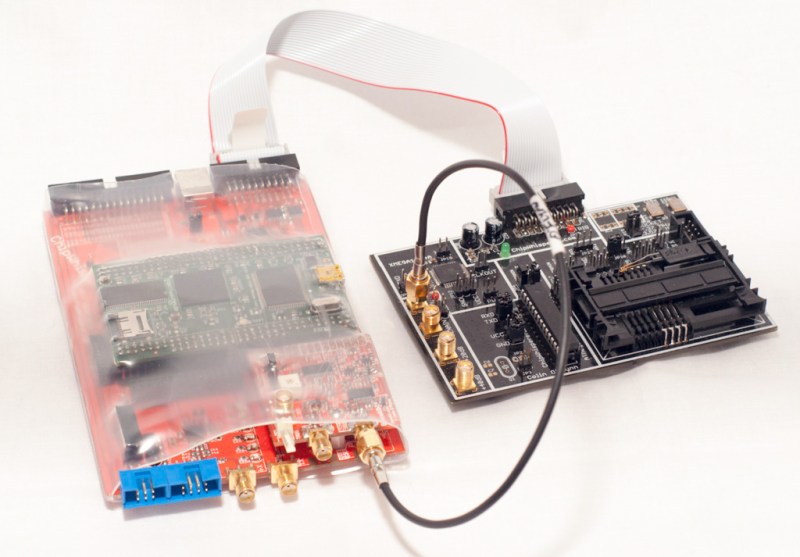
Every finalist for The Hackaday Prize has some aspect of it that hasn’t been done before; finding the chemical composition of everything with some 3D printed parts is novel, as is building a global network of satellite ground stations with off the shelf components. [Colin]’s ChipWhisperer, though, has some scary and interesting implications. By looking inside a microcontroller as its running, the ChipWhisperer is able to verify – or break – security on these chips. It’s also extremely interesting and somewhat magical being able to figure out what data a chip is processing simply by looking at its power consumption.
We have no idea who the winner of The Hackaday Prize is yet, and I’m hoping to remain ignorant of that fact until the party two weeks from now. Until then, you can read the short interview with [Colin O’Flynn], or check out his five-minute video for the ChipWhisperer below:
How seriously are the backdoors the Chipwhisperer opens taken in the industry? Are we looking at a huge problem with on-chip security out there, simply because the tools to investigate them have been really expensive?
For people who care about security because they directly have money to lose
(think chip & pin credit cards, satellite set-top boxes, etc.) they’ve taken
these problems seriously for a long time. But the majority of embedded
systems work doesn’t fall into that category, and it’s those products which
end up vulnerable. Part of the issue is the design engineers either don’t
know about these attacks. Or the engineers trust the vendors they are buying
from, which sell the crypto libraries, hardware accelerators, or stand-alone
chips as completely bullet-proof systems.
The problem may not be one of fundamental deficiencies in the design of
the crypto, but more the users (i.e. design engineers) don’t fully
understand how “secure” the specific implementation of the crypto is.
If you could give 100 words of advice to embedded designers implementing encryption, what would you tell them?
Crypto is not a check-box. Every implementation will be vulnerable, your
question is how secure do I need this to be? If someone is able to determine
the secret key in one device, does this mean they are now able to gain
access to all similar devices? The problems exposed by side-channel analysis
is often made worse by classic mistakes, such as re-using keying material
across multiple devices to make deployment easier, but when the devices
don’t actually require a shared key (think firmware images).
You’ve already said a few people have gotten the files and built their own ChipWhisperer. You’re also selling the complete kit. Who is buying it? Are we looking at academics, security researchers, companies verifying their own hardware, or just random people who sign their emails ZeroCool?
Mostly academics so far, although there has also been a few security
researchers and companies too. My intention with the design is for it to be
a learning tool, and about as far from an ‘offensive attack tool’ as I could
reasonable make it. Unless you understand the underlying theory of the
attacks you’ll never have success with them.
What was the reaction from different communities? What was the response from security researchers versus the general public? Are you surprised at how popular your project was?
The biggest reaction has been from embedded engineers, as they have often
been sold on ‘secure because math’ during their design process. They are
using AES-256 for example and assume that means someone attacking the system
would need to physically decap the chip, reset fuse bits, and then read out
Flash memory to get the key. They’d never seen practical demonstrations of
side-channel attacks, only vaguely heard about it.
I am surprised how popular the project was outside of this sphere though! A
lot more people are involved in side-channel power analysis then I first
realized, which is great to learn. I started a web forum with the intention
of trying to collect some of that community, as it would be great to share
research results in a more informal manner.
Hypothetical, and we’re not going to hold you to whatever answer you give. You win the grand prize, a trip to space or about $200,000 USD. Which one to you take, and what is your reasoning for doing so?
The trip to space would be great, but I think I’d have a hell of a time
turning down $200k! There’s no question I’d invest that back into this
project though. I really want to create a lower-cost version of these tools,
and a big part of that is doing a larger production run with more advanced
technology (mounting the FPGA directly on a multi-layer PCB). I’ve avoided
Kickstarter so far as I want this project to remain pretty technical – if I
went the Kickstarter route I’m afraid I’d end up with people who’ve only
ever used an Arduino backing the project, and then get frustrated when I’m
asking them to compile C code. I’ve also avoided trying to get an outside
investor, as they want to scale-back on the open-source/free nature of the
project. I’m also still part-way through a PhD, so can’t get too distracted
as I want to finish that off first!
Either way I’d need to check the tax implications of the prize too – if I
had to pay full Canadian income tax on the prize, I couldn’t afford the trip
to space anyway, even with the offer in the rules of the sponsor covering up
to 20% of the value! Unfortunately practical matters might dictate my
choice.















The raman spectro scope is the clear winner out of the top 5. It’s the most applicable to the medical field and the most value as a kit or already assembled for 1/4th the cost of current commercial units. what use would a chip sniffer be in the medical field?
Who says that the winner has to be related to the field of medicine?
surfingtheether does, and what he says goes around here!
Who cares? Medical is a small subset of science. Sheesh!
The security of pacemakers, maybe?
Shh…
Be careful, remember what they did to Barnaby Jack.
Very cool project, and congrats on the finalist round… if it were up to a vote, you would have mine, as I think this is a very important area of study and your project can greatly assist. (Bonus points for being a fellow Canadian, too!)
BTW, I am not a tax accountant, but I believe that prize winnings are exempt from income tax in Canada. Don’t quote me on that, though.
Cheers
Thanks for your kind words! I just saw this was posted today (did my weekly read of HaD). Unfortunately lottery winners are exempt, but ‘competitive contests’ aren’t explicitly… I know there was an article about Olympic athletes having to pay tax on winnings from medal placings. There’s some special consideration for certain contests which HaD may or may not fall under, but it seems like they can’t tell you with 100% certainty ahead of time which sucks, so you’ve just got to keep the money around to pay the government until the actual assessment is done…
I think it would be kinda funny if the winner took the $200k after HaD did the whole “but SPPAAAACE!” hype thing.
I would have to think VERY LONG AND HARD about which to take. I’m a pathetic millenial who needs a home… or my lifelong dream realized. Which to take?
I think I would take the cash, wait a few years for the price of tickets to space to drop. Then I could afford the ticket to space AND back!
The ChipWhisperer is such a cool bit of tech, if it ever makes it to my bench it’s going right next to the SDR.
Funny how we’ve gone full circle on “hacking”, from hardware (Locks and keys) to software (Encryption), and now back to hardware hacking again. Crazy how much data is leaked to the world with no concern whatsoever as to it’s security, or for that matter, it’s existence.
Stuff like this and cheaper SDRs are going to really screw with the security world for a couple years, that’s for sure.
Out of the finalists, this is the winner as far as I’m concerned.
The space thing is pretty stupid compared to what 200K can do to a life.
In fact, I would be super interested in whether Hack-a-day thinks they got their money’s worth out of the promotion once it’s all said and done.
Well…..maybe you should join the discussion over on the stack about what next years prize should be?
http://hackaday.io/page/577
Great link, tx. Guess AC doesn’t like space!
Space is awesome. I would love to go to space. But would I love more having a $200,000 buffer in my life to take a little worry out of money issues? The results of having the cash will last significantly longer than the15 minutes in space. (and don’t forget the potential of blowing the hell up on launch or reentry… see Orbital Sciences to talk about how confident they were before the other day)
Maybe the majority of HaD readers are just already millionaires, in which case 200k isn’t such a big deal.
Really nice work.
It”s odd and I totally agree.