Two weeks ago, news broke of an incredible abuse of power from the National Security Agency. A DEF CON talk was cancelled, and speculation raged that information was not free. This was the ProxyHam, a device that puts you miles away from any agency hunting down your IP address.
Of course, as with just about every DEF CON talk picked up by the press, ProxyHam is an ill-conceived, terrible idea. You can replicate it with parts bought from newegg, and despite using a highly directional antenna the FCC – or any other government agency – can still track you down.
In lieu of a talk on using off-the-shelf networking hardware in the way it was intended, [Dave Maynor] and [Robert Graham] of Errata Security gave a talk at DEF CON that is the proxy to the ProxyHam. They completely debunked the outrageous speculation surrounding the cancellation of the DEF CON talk and managed to introduce a new version of Internet over radio that is actually useful for the security-minded individual.
The ‘debunking’ part of the Errata Security talk was exactly what anyone would expect; the talk was probably cancelled because the creator of ProxyHam exceeded radiated power limits, the FCC caught him, or simply because of ‘advice from counsel’. No big deal; someone was doing something illegal – encryption over ISM bands – and the things you would expect to happen in fact happened.
In the last two weeks, the guys replicated the ProxyHam build, but found a few major shortcomings. Even with a highly directional antenna, interested parties could still track you down. This led the guys at Errata Security to make this system better. They managed to do it in two weeks.
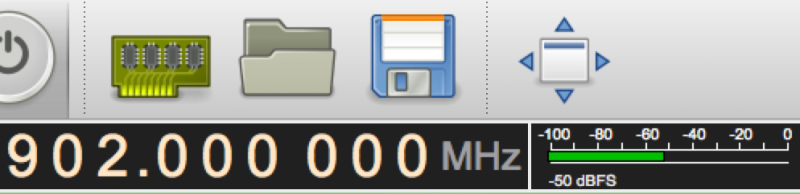
The Errata Security relies on JT65A – a radio mode made for very weak signals – to hide signals underneath the noise floor. By multiplexing data across multiple channels, this system has about the same bandwidth as a 56kbps modem from 1999. It’s not much, but it is possible to use this proxy for ProxyHam over 20 miles away from where you’re stealing WiFi from. That’s far better than ProxyHam could ever manage, and all the transmissions stay below the noise floor. The FCC and similarly equipped agencies might be able to find you, but no one with a $20 SDR dongle will.
There are no releases yet, but Errata Security plan to make the software that allows this multiplex transmissions available soon, and hope to have a Raspberry Pi-based hardware solution for this technique coming shortly. It’s a radio proxy solution that’s actually somewhat secure, and won’t immediately draw the ire of the FCC.















Encryption is prohibited on HAM bands, but isn’t it OK on ISM bands?
2.4 GHz and 5.8 GHz (as used by Wi-Fi, Bluetooth, 802.15.4 among others) certainly do permit encryption. As you mentioned, ham bands do not permit encryption.
Whaaaaat? For what pvprouse would encryption be prohibited?
I can think of several. To begin with it’s “Amateur” radio. If nothing else, allowing encryption would make it trivially easy for people to co-opt the amateur bands for commercial purposes.
it prevents the ham bands being used for commercial purposes by allowing the hams themselves to inspect the traffic therein.
Ah, yes. That wold make sense.
Yes, encryption is legal on the ISM bands, but don’t forget that there is some overlap between them and the ham bands on at least the 2.4 GHz band, so anything on channel 1 or 2 at ham power levels cannot be encrypted.
Once the device has been discovered, finding the originating transmitter is trivial. People who want anonymity should be looking at the KISS principle and using McDonalds Wifi or Burner prepaids. Even a second DOCSIS modem + VPN will get you busted if you piss off the wrong people.
This notion that you can violate tradecraft best practices and eat your cake too are only kidding themselves. “Dirty Harry” had the right idea.
I think you are right about KISS principle. The problem is that the citizen does not decide how simple the world works. Many shops have camera surveillance. If you buy the burner electronically, it is easy to correlate. If you pay with cash in form of a bill, they have unique serial numbers (and money really does not travel that far between emission by one bank, and absorption by another). Also you can not bring your normal phone when buying the burner, since in many parts of the world cell phone positions are practically triangulated. Even not bringing a phone leaks data because it is sitting still at home, instead of your usual activity, so you would have to plan to buy it at a moment when you are usually at home. If you have the bad luck that people try to call you, your nonresponsivity (compared with previous responsivity) betrays you.
I do see your point i think the best methodology would be to be in a hight density urban location with multiple exit / entry points. while using a radio proxy and set up ip cams / motion trips at the hams network entry connection. then when they bust down that door you casually leave via any exit into the aether.
There is such a thing as the noise floor (the power level of noise as a function of frequency). There is no such thing as transmission below the noise floor. There is such a thing as an eavesdropper selecting too wide a band for monitoring: the noise of the spectrum adjacent to the signal decreases the S/N ratio. If you can transmit from your sender to your receiver, that signal is above the noise floor. Using very low power just puts a bigger strain on ADC resolution, and number of ADCs (dividing up the spectrum into finer and finer bands) the eavesdropper would have to use. Expect nation states to be very capable to map transmissions close to (but necessarily above) the noise floor. Directionality seems a better bet, with lower diffraction at shorter wavelengths => optical transmission, expand a laser beam so that the intensity is low, sender and receiver will need big lenses though!
http://physics.princeton.edu/pulsar/k1jt/wsjtx.html The mode mentioned in the above article was actually developed for Amateur Radio Operators to use to bounce radio waves off at much lower power levels and with much less complex antenna structures than what had been used up until that time. And yes, when you’re receiving a signal, you cannot hear the actual audio tones being sent over the background noise, but the signals are still decoded by the software.
sure, one can get arbitrarily close to the noise floor and still transmit a signal (at a lower rate)
Aside from JT (Joe Taylor) 65, below the noise level LoRa™ ( US firm Semtech’s “Long Range” ) UHF data transceiver modules,readily available in the US$10-$20 range, may have some -ah- mileage? See => http://www.instructables.com/id/Introducing-LoRa-/
The LoRa modules are indeed very sensitive. The bitrate is extremely low though. Beware that they use coding gain and a wide bandwidth to achieve their sensitivity, as such they are quite susceptible to interference. (only a few dB’s of 20KHz offset interference rejection)
Manuka, thank you for this detailed lora article (looks like you’re the author also?) i have stumbled upon lora some time ago liked it and had aplication for it’s use but never put time into research, this is a big boost/help!
Zega: Guilty as charged -glad you found my heads up LoRa™ Instructable informative.! Perhaps add a few comments? The Dorji & HopeRF modules we’ve used have particularly suited long distance sat .nav based tracking. Ranges have been an order of magnitude better than similar traditional set ups – 10s of km instead of just ~1km are typical. Stan. (“Manuka”)
next time you hold a def con why not hold it out of your own house or do a steve jobs (“one more thing”) and dont announce the potential security threatening hack until the event so then the nsa cant stop it.
It wasn’t stopped by NSA.
JT65 and JT9 are cool low power methods but anyone integrating will see them as a series of sharp lines. For stealth purposes instead of having a long tone at a single frequency it would be better to shift frequencies such that the signal is only brought above receiver noise if you know the cryptographic pattern the transmitter is using.
What is this abuse of power by nsa he talks about in the first sentence?
Ars Technica suggested the reason it was cancelled was because of a National Security Letter.. This is only because it was specifically stated FCC and IP concerns weren’t the cause of it being removed.
The guys at the proxy proxyham talk suggested it was FCC-related issues, but I *much* prefer the meta-defcon theory, where the ProxyHam creator was just gaming the media. IMHO, every speaker that talks to the press before their talk should be banned.
ProxyHAM was from the beginning a terrible idea, surely it would be better to grab a bunch of off the shelf AP’s with dual radios, deploy over multiple locations, and just bounce the connection whilst advertising a ‘free WiFi’ open ssid as a smoke screen / junk data?