Two weeks ago, news broke of an incredible abuse of power from the National Security Agency. A DEF CON talk was cancelled, and speculation raged that information was not free. This was the ProxyHam, a device that puts you miles away from any agency hunting down your IP address.
Of course, as with just about every DEF CON talk picked up by the press, ProxyHam is an ill-conceived, terrible idea. You can replicate it with parts bought from newegg, and despite using a highly directional antenna the FCC – or any other government agency – can still track you down.
In lieu of a talk on using off-the-shelf networking hardware in the way it was intended, [Dave Maynor] and [Robert Graham] of Errata Security gave a talk at DEF CON that is the proxy to the ProxyHam. They completely debunked the outrageous speculation surrounding the cancellation of the DEF CON talk and managed to introduce a new version of Internet over radio that is actually useful for the security-minded individual.
The ‘debunking’ part of the Errata Security talk was exactly what anyone would expect; the talk was probably cancelled because the creator of ProxyHam exceeded radiated power limits, the FCC caught him, or simply because of ‘advice from counsel’. No big deal; someone was doing something illegal – encryption over ISM bands – and the things you would expect to happen in fact happened.
In the last two weeks, the guys replicated the ProxyHam build, but found a few major shortcomings. Even with a highly directional antenna, interested parties could still track you down. This led the guys at Errata Security to make this system better. They managed to do it in two weeks.
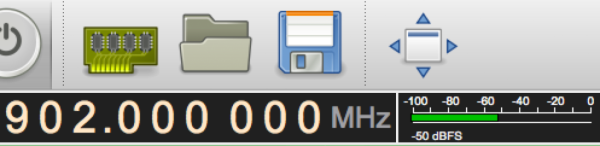
The Errata Security relies on JT65A – a radio mode made for very weak signals – to hide signals underneath the noise floor. By multiplexing data across multiple channels, this system has about the same bandwidth as a 56kbps modem from 1999. It’s not much, but it is possible to use this proxy for ProxyHam over 20 miles away from where you’re stealing WiFi from. That’s far better than ProxyHam could ever manage, and all the transmissions stay below the noise floor. The FCC and similarly equipped agencies might be able to find you, but no one with a $20 SDR dongle will.
There are no releases yet, but Errata Security plan to make the software that allows this multiplex transmissions available soon, and hope to have a Raspberry Pi-based hardware solution for this technique coming shortly. It’s a radio proxy solution that’s actually somewhat secure, and won’t immediately draw the ire of the FCC.