Hacking has always brought more good to the world than not hacking. The successful efforts of the Allies during World War II in deciphering the Enigma machine output still reminds us of that. Today, the machine is a classic example of cryptography and bare-metal computing.
We have covered quite a few DIY Enigma machines in the past, yet 14 years old [Andy] really impressed us with his high school science fair project, a scratch built, retro-modern Enigma machine.
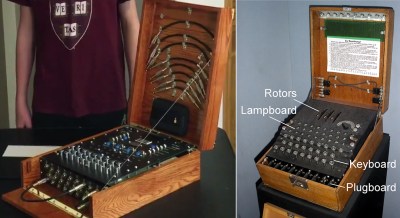
With its wooden enclosure, keyboard, interchangeable rotors, and plugboard, his build resembles an original Worldwar II enigma machine down to the letter. However, when looking closer, you’ll find that the rotors are implemented as electronic modules that plug into D-Sub sockets on the machine. Also, there is a 16 segment display that displays the rotor position as well as an LCD screen that lets you comfortably read the plain- and ciphertext. On the inside, you’ll find an Arduino Mega along with 1,800 other parts and 500 wires, and of course, this modern version has a backspace key.
It took [Andy] over 9 months to put all this together, and he now finds himself among the winners of the State Science & Engineering Fair (SSEF), who will be sent to Intel as representatives of their states. Given his experience in field-capable computing, we’re sure [Andy] can help Intel reconquering mobile. Enjoy the video!
Thanks to [Arduino Enigma] for the tip!
















I was pleasantly surprised that there was nothing about the akhmed clock bomb in the article.
very impressive.
Until you brought it up…
Addendum to Godwin’s law:
As any maker/hacker topic progresses the chance of someone bringing up Achmed’s clock bomb will approach 1.
A small clock program can probably be loaded on spare program memory. Everything is better when it has a clock…
Superbly done, and very well demo’d.
That’s a beautiful build. I hope you did well at ISEF.
WOW!!!
Well done, [Andy]! Well done indeed. That is an amazing project.
Deciphering the Enigma was a hack ?
Decoding messages without the key? Yep.
Some of it was “social engineering”. Not only did they have a machine (or was it the specs?) via the Polish underground, but some of the decoding relied on sloppiness on the German users.
There were strict rules about using Enigma, but some didn’t change the wheels or something as scheduled, leaving more messages in the sequence. Some locations would always start with the same phrase, which also helped.
That’s not to dismiss the work. One problem they had was that for the information to be useful, it had to be decoded fast. So some of the social mistakes allowed a pre-sorting, fast tracking those messages.
Michael
The Poles built copies of the machine, analyzed it and built the first Bombes to decode the messages. They weren’t allowed to participate in the Bletchley effort, because they were not thought to be a good enough security risk.
Yes, it’s been a while since I read the book. But that book, whatever it was, showed that the Poles had more importance in it all than many accounts. Providing the machine and the initial work isn’t good enough?
Michael
They had to ‘hack’ a few nazis to decode the machine. (Bad joke, sorry).
Absolutely. Using purpose built, one-off hardware. Time was of the essence and automating the process of searching for keys lowered the time between the daily key change and the first decrypted message.
Am i the only one that is a bit let’s say surprised by the number of parts (“1,800 other parts”)??
Does this superb work put you on the no-fly list when you try to enter a plane with it?
Job well done. Nice presentation of your enigma machine.
Great project!
Is that breadboard inside though? Sooner or later the contacts will become flaky if you leave the breadboard “in production”. Consider replacing with stripboard for minimal wiring changes.
Great job and looks nice .. except for those horrible blue LED displays. Down with eyeball-destroying blue LEDs!
Yeah. Red lasers or nothing.
Ah hahaha! I actually laughed for real. I was certain one would want neon lamps for the machine, but yeah lasers work! Why why why did he use blue LED’s?!
For antiquities sake use ruby crystal lasers! Fun fact: The first laser was apparently invented in 1960. So I guess not true to the machine’s time period. I hope I’m wrong; I half expect that someone, Nikola Tesla perhaps, invented it before then and didn’t tell the world.
The only problem with that is that one needs a very firm grasp of the structure of the atom as we know it today to build lasers, and Tesla was struggling even with the concepts of electromagnetism.
But I like to imagine him as a sort of Dr. Frankenstein that could do anything! I know he went a little (a LOT) crazy in his later years. ; )
He claimed to have built a particle beam weapon (death ray). I wonder just how close he got.
I just thought the laser had been invented around 1920 for some reason, no idea why!
That is some impressive work there Andy. The electronics/software is only moderately impressive, but the attention to detail and finishing is truly exquisite!
Very well done!
To verify the accuracy of the encryption, the settings used in the video are:
Machine: M4
Reflector: B thin
Additional Wheel: Gamma
Wheels: V VI VII
Ring Settings: A A A A
Plugs: U-P, Q-G, M-O
Initial Wheel Position: A N D Y
JIMMY encrypts to QXCKG
Notice his Harvard t-shirt. Is this 14-year-old already setting himself up for the university’s admissions committee? Probably. I wish him the best of luck.
Unfortunately, he needs all the help he can get. Being a white male and I assume not the son a rich alumni is one strike against him. If he likes girls, that’s a second strike. The only reason he’s not out of the running altogether is that he’s not a girl-liking Asian male. That’s instant death at the Ivies.
http://www.economist.com/news/briefing/21669595-asian-americans-are-united-states-most-successful-minority-they-are-complaining-ever
Alas, if you’re Asian, building a working Enigma isn’t enough. To stand a chance, you’l need to invent anti-gravity at fourteen and get nominated for the Noble Prize in Physics at fifteen. It is almost that bad.
At Ivy league colleges such as Harvard, claims about “diversity” mean precisely what they meant during the 1920s. Then “diversity” was a code-word for keeping out talented Jews, the children of hardworking immigrants. Now it’s a code-word for keeping out talented Asians, also the children of hard-working immigrants. Nothing has changed.
Behind that lies an obsession with protecting the lazy children of Old Money from aggressive, smart kids who weren’t born rich. That explains quotas that let in the lazy and stupid of some minorities, while excluding the hard-working and smart in other minorities. Those lazy and stupid minority admissions pose no threat to lazy and stupid ‘trust-fund babies’ who benefit from the ‘white privilege’ offered by their expensive private school education.
What’s happening in college admissions is so transparent, you’d think even journalists would understand.
–Michael W. Perry, co-author of Lily’s Ride
I’m ignoring your comments from now on.
Very Nicely done
@notarealemail (et al) … ENIGMA MACHINES TODAY! And online!
To All Would Be Cipher Masters! To send secret messages to one another without revealing who you are or your real email address. Here is the a little-more-complex technique better than the Caesar Cipher (which is too unsecured):
1. Go to http://enigmaco.de/enigma/enigma.html to compile a message with rolling cipher codes – even ‘you know who’ has trouble with.
2. Then ask the recipient to go throwawaymail .com and setup a temporary email address that lasts 48 hours.
3. When he sends you the throwawaymail email, you send the cipher FROM the enigma app as it breaks down rotors, modes, etc.
4. Recipient has only less than 48 hours (2 days) to go read it at the throwaway web site before it’s deleted. He will have to decode the message at the engima website.
5. But if you already know your friend’s email address then don’t bother with throwawaymail.
But all that’s for secret squirrel type stuff. If you just want to comment behind someone’s back, just the recipient needs to use throwawaymail site.
Here’s how dialog might go:
Hey dude! Go get a throwaway and reply it to me so I can send you something very interesting!
1. Once you get it in a HaD reply post, then send him the “interesting stuff” from your normal email service or sendanonymousemail .net if you’re that paranoid.
2. Recipient must remember to go back often within the 48 hour window to see your stuff.
3. Recipient must not permanently bookmark the site. What would be the point?
4. And don’t worry about target seeing it. He can’t. And he can’t spam you either as it will be gone in 2 days! All he’ll see is the throwawaymail email address in the HaD post but SO WHAT?
Good luck and make this technique viral please.
SOTB
Unfortunately I don’t have the time for this though it looks fun as hell. I might, but probably not. Don’t bother yourself with that guy. He is bored or something and picked you yesterday.
Have a good weekend! :)
notarealemail – LURKER! You should have jumped in and had my back! (just kidding!) You too have a good weekend… :-D
BTW – That information is for when we have something “sensitive” to say to each other without anybody listening in. Not an invitation “to go pick out curtains” ;-P
I was pleased to judge the Embedded category at the Intel International Science and Engineering Fair in Phoenix a few years back. This Enigma project is a fantastic reinterpretation using modern circuitry. The replaceable rotors was implemented using tiny plug-in PCBs each with a differently programmed EEPROM.
The build quality is beautiful and instantly recognizable. The other judges in the Embedded category wanted to recognize it, but didn’t feel it deserved a prize because wasn’t research. I argued that reverse engineering an existing product is something that most design engineers spend a lot of time doing. I was very was glad Andy was voted got a special award. I felt you should have won the category.