To a casual observer it might seem as though our community is in the news rather a lot at the moment. It’s all about hacks on our TV screens in the soap opera of Washington politics, who hacked this, whether those people over there helped that lot hack the other lot, or even whether that person’s emails could have been hacked on that server. Keeping up with it as an outsider can become a full-time job.
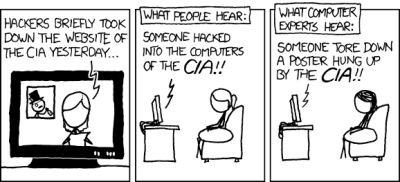
Of course, as we all know even if the mainstream journalists (or should I refer to them colloquially as “hacks”?) don’t, it’s not us they’re talking about. Their hackers are computer criminals, while we are people with some of the hardware and software skills to bend technology to our will, even beyond what its designers might have intended. And that divergence between the way we use the word in a sense of reappropriation and they use it in disapprobation sometimes puts us in an odd position. Explaining to a sober-suited businessman as the director of a hackspace, that no, we’re not *those*hackers can sometimes feel like skating on thin ice.
Boot up or shut up!
We’re all familiar with the sensationalized media portrayal of the hacker. Film characters who can develop and debug the most complex of code which breaks into Fort Knox or the Kremlin, all in about three seconds of aimless banging at a keyboard with a static mock-up of a command prompt in front of them. It’s become the subject of considerable mirth within our community, as with innumerable lists of awful hacking scenes in movies, photo galleries like this wonderful series of pages featuring stock photo “hackers”, or even the famous, and no doubt by now horribly burned, “Beautiful woman repair soldering a printed circuit board“. The trouble is though, behind the laughs at the awful tech portrayal is the sad truth, what is obviously fake to us looks real to Joe Public, and those are the criteria upon which we are judged. The credibility-stretching tech baddie on the screen is a hacker, they are told, so we must be baddies too.
Over Christmas where this is being written, the 2014 British film Pride was repeated on TV. In a memorable sequence the lead character explains the process of reappropriation of problematic language, as a tabloid newspaper insult against the gay community is turned against its originator by being adopted as the publicity slogan for a benefit gig. While the situation portrayed is very different, there is a valuable parallel to be drawn for any community in danger of losing control of their own narrative. In reclaiming the word “hacker” for our hackspaces, hackathons, and of course our popular and informative news websites, we are slowly educating the world that far from someone to be afraid of, a hacker is someone you might just welcome in your vicinity. Showing 3D printing or laser cutting in a hackspace to people from local businesses and organisations visibly opens their eyes on this front, having arrived looking wary they leave full of enthusiasm.
Something Done Without Constructive End
If we look at the word with several decades behind us, perhaps we can chart its fall into disreputable circles. Its early etymology is well-enough documented as a piece of the internal jargon at MIT’s Tech Model Railroad Club (TMRC), and it appears in Peter Samson’s 1959 TMRC dictionary to which he added italic notes in 2005.
HACK: 1) something done without constructive end; 2) a project under-taken on bad self-advice; 3) an entropy booster; 4) to produce, or attempt to produce, a hack3.
I saw this as a term for an unconventional or unorthodox application of technology, typically deprecated for engineering reasons. There was no specific suggestion of malicious intent (or of benevolence, either). Indeed, the era of this dictionary saw some “good hacks:” using a room-sized computer to play music, for instance; or, some would say, writing the dictionary itself.
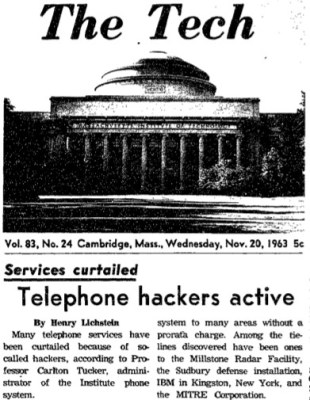
The word appears incidentally around that time in issues of The Tech, MIT’s newspaper, but we have to wait for November 1963 to see it break into the mainstream with a story of a group of students disrupting MIT’s phone system through wardialling with a PDP-1 (PDF link). Straight away we see the start of the association with computer crime, though there is an air of “Boys will be boys”, in the official reaction any approval is absent. (If by any chance any of that MIT class of ’63 whose nefarious activities are documented happens to be a Hackaday reader, we urge you to write your memoir of the escapades. We’d all like to read it so please get in touch!)
It’s entirely possible that our historical view is built on sand. We feel like “hack” as a term has been corrupted in our modern times and needs to be taken back to it’s original positive connotation. But there is an aspect of the 1959 TMRC use of “hack” having gained a negative connotation before ever leaving the confines of MIT. Perhaps only an etymologist or lexicographer could give us the answer, and even then it might have little relevance to our slow reappropriation of the word.
It’s a perennial in some hackspace circles, a few members bringing up the idea of replacing “hack” with something else a little less controversial. Some spaces go for it, ours where this is being written hasn’t. We hack, and we own it!
















I recall at one point there was an effort to split the concepts into the term ‘Hacker’ – as someone very good with computers, and ‘Cracker’ – those engaged in criminal activities, but the press didn’t cooperate, and that was that.
To be fair “Cracker” had the problem of already having been used as a racial slur.
I suspect that was likely part of the problem.
There are also people in Georgia & the Carolina’s who are self described crackers. Based on the driving of cattle during the settlement of those territories, rather than the racial connotation of slave owning.
I thought the racial use of cracker was because they’re pale, like crackers.
Perhaps fortunately the slur has not made it to the UK, where it remains a type of biscuit.
…Or a person who is attractive and/or fun to be with! Don’t think that it came from the biscuit meaning though.
You call cookies biscuits. What do you call biscuits? http://betterbatter.org/wp-content/uploads/2015/03/butterflake-biscuits-2.jpg
Having lived in the UK for several years, the answer is they don’t know the pleasure of American biscuits. KFC only serves stringy chips (aka french fries) with their famous recipe chicken. The closest thing I found was a few varieties of cheese scone. Also, their native recipe donuts (i.e. not Krispy Kreme) aren’t very good, but lots of other yummy pastries are available.
And as a bland crispy cookie
As far as I am aware, hacking means modifying code to adapt it for your own needs, to write code from scratch is difficult, but working from an existing framework and hacking compiling until you succeed is doable.
Hacking did not relate to hardware.
And then there is the original Black Cat Hacker,
https://www.youtube.com/watch?v=PU33djIftk4
WINNER!
The colloquial term around these parts seems to be “attacker” it definitely sets in the mind of the customer we are talking to, that the person being reffered to:
1. isn’t allowed to do what they are doing, and are of a criminal persuasion
2. A defense to this attack needs to be made.
Yes, I remember that too. Perhaps we now try to reinforce the latter should be rightly named a cyber criminal.
Cracker – the tail wagging the dog. A lost cause. Just embrace the dark side and go with it. It can be beneficial sometimes if people think you are up to no good.
That was likely the other side of the coin: there was a certain frisson about the term that those early computer hobbyists liked having the aura of.
Sometimes the language takes off on it’s own. “Band-aid” is the brand of an adhesive bandage and at one time the word “gay” meant happy.
A hacker is someone who does something that the original designers never intended. Now if that is converting empty cans into a 10 foot satellite dish or bypassing obscure security measures in a computer system, at the heart both are the same, the application of good intent or evil intent is the only differentiation. That and the actual ownership of the systems involved.
+1
My great aunt Violet Gay didn’t like her first name. She always went by her middle name – until the homosexual community adopted gay. So she grudgingly changed to telling people to call her Violet. Her twin sister Viola Vay went by Vay her whole life.
The mother of one of my dad’s best friends was also named Violet. Very few people knew her middle name until her funeral. What was it? Surprise. Violet Surprise. ;)
People have been calling gay people gay for more than a century. It’s just that until 40 years ago or so, nobody needed a polite or dignified name for gay people, that’s when the word became well known. So I don’t think your great aunt precedes the usage.
We can’t change it. Tech-people know that there are bad and good hackers, but most people think hackers=computer criminals. When talking to a sober-suited businessman I just call me a programmer and engineer, but no problem e.g. to call my project, which uses OpenCV for debunking a product by analyzing a video, a hack, most of my facebook-friends and real friends know the difference.
Think about Spam, what did they do?
Contrary to popular opinion, Spam is not a name of an organization or group of people, so “they” didn’t do anything.
Its the name of a company that puts “meat” in a can. They probably don’t want any negative connotation reinforced on the word spam.
It’s actually Hormel who make Spam.
Oh, and it comes from “Spiced pork and ham”. The spice is salt. The “pork and ham” are non-traditionally edible pig components.
Email spam is named after the canned meat because of Monty Python.
https://www.youtube.com/watch?v=anwy2MPT5RE
I guess the real question is: noun or verb?
Do you hack things?
Are you a hacker?
how do you identify yourself?
I personally am a hacker. But more specifically, I fix things. I make things work, sometimes better than they did before.
Either way, its a very personal question you have to figure out on your own, who cares what others think of the word.
Yes, you hack things. With a hatchet. Into small pieces.
You can also be a hack (or a quack), especially if you practice medicine without appropriate education.
I usually identify myself with my name.
My name is a simple designation, not necessarily unique, and I use a nom de guerre here, my reputation takes on a life of its own, as does my reputation as a fixer of things. I even have an image of a gear with the Chinese symbols for “I” and “fix” on parchment a local restaurant owner made for me. I am the original type of hacker, I am the repair man.
This is the part where you spout out some nonsense about the stereotypical repair man, go ahead, I’ll wait.
Are you sure you don’t mean “tinker”?
nope
If you look at the photo of the girl repairing a circuit board, She must be a super hero npt to get burnt holding the soldering iron like that.
If you look at the photo of the girl repairing a circuit board, She must be a super hero not to get burnt holding the soldering iron like that.
Despite the fact that the soldering iron isn’t powered (presumably) this doesn’t mean that ESD precautions should not be taken. In other words… where is here wristband.
Oops, stupid me, she must be wearing ESD safe shoes or an ESD shoestrap thingy.
She must know what she is doing, otherwise she would not have used here special (yellow) safety glasses.
We learn’t ESD protection with regards fixing NON Hi-Performance items is pointless (to quite an extent, ESD protection is built into most things).
The dust sucking into a working unit on a hot day into a hot unit past plastic grills via an ungrounded heatsink causing charge buildup, disturbed by overheated capacitors eventually going bang, then thrown over multiple speed-bumps before having all the dry charged dust swirl around the compressed air dusting bench past all the components. Surely the thing has already seen multiple mini electrical dust storms in its’ normal operating and maintenance life time anyway.
A (short-period employed) manager demanded I always wear a band attached to GND. The case was live. He threatened me with the door, so I said I’d rather him risk his life…. So he did, and as you could guess the result: we all laughed at his pain. Since then, anti-static bands were banned outright (exception for any high-end equipment only since performance, i.e. over-clockability is mainly affected by static damage). Oh and then he was a month or so after that, Fired.
There are more problems with Intel Q67-ish era BGA failures in everything from towers, servers to laptops, etc… and mainly just blown capacitors in older equipment.
Missed a correction: The case went live (NOT: the case was live, 3rd paragraph)
Forget that. #7 is Cory Doctorow!
Hack is a word that means cut roughly. As such it has been coined in lots of contexts to represent less than some presumed standard. With such widespread colloquial usage it’s going to be hard to find who first called a horse a hack, a journalist a hack writer , a golfer a hacker or a layabout that hacks around (no comma intended, I did just call a golfer a layabout that hacks around).
The word hacker is thrown around too much these days, I know we all know what a hacker is but the media is stupid, they will call a DDOS attack a hack. The problem is the word hacker to describe gaining access to systems you have no right too isn’t going anywhere. The public as a whole are not educated enough in IT/Tech to care what it is called and will continue to do so because the media have called it that for years.
I try to correct people when they have been hacked, 99% they were not “hacked” they downloaded a virus/trojan/adware voluntarily. Once I have explained this to them they still insist they were hacked. The IT illiterate make up a large percentage of people online, I have met a few people who thought Facebook was the internet and Mark Zuckerburg invented it. My step daughter used to play an online game called “Movie Star Planet” where you basically rent virtual clothes bought with virtual currency acquired by small cash payments, It’s like crack cocaine for pre teen girls. Anyway she would be telling me about these “hackers” on this site I asked about this she said they take over your account and steal your clothes, Turns out these were social engineering 8yr olds asking other children personal questions in the hope of resetting their password and taking control of their account.
So to sum it all up I don’t think we have much of a chance of reclaiming the word properly, but I will proudly call myself a hacker to anyone who asks and correct their ignorance once I star getting strange looks or questions about how to hack into friends/girlfriends/boyfriends Facebook account.
Do not worry about the old usage of an old word. Make and Maker have filled in the nice that we used to use hacker for. Use words to be clear what you mean and do not worry so much about what you want them to mean. Worry about what others think they mean and use it to communicate with others. Which is why we communicate.
Mr. (Supreme Court) Justice Potter Stewart, ruling on a case involving hard-core pornography–or not:
“…criminal laws in this area are constitutionally limited to hard-core pornography. I shall not today attempt further to define the kinds of material I understand to be embraced within that shorthand description; and perhaps I could never succeed in intelligibly doing so. But I KNOW IT WHEN I SEE IT…”
When it come to construction and repairs “hack” always has had a negative connotation for a long time (even before 11/20/1963), so “hacker” is going to share that negativity. In general DIY types have employed hacks as a temporary solution, until they can get it done right. Was not until I received internet access that I read hack and hacker in the tense that Jenny and others desire to “own” .As I can’t recall coming across hacker in this context on the Land line BBS’ or the amateur radio PBBS’ Good luck in trying to gain that ownership. In the meantime I will avoid using the terms to avoid have to void explaining. I really doubt you will be able to get enough DIY types to embrace the terms to gain ownership. As a jack of all trades I have built may things, so I’m partial to builder a description to that activity. I really don’t expect seeing existing space eliminating the work hacker from their name, I can see new spaces avoiding it, to avoid the hassle of endless explanation.
Maker, jury-rig, English is rich enough to find the appropriate words.
“…and needs to be taken back to it’s original positive connotation.”
You really DO need to stop hanging around so much with the people who comment on your articles…
Hackaday: Fresh hacks every day.
This article: Not a hack.
Yep. Screw people and what they think. It’s just a dumb word. Real geniuses talks about ideas not ponder on a subjective.
“some of the hardware and software skills to bend technology to our will, even beyond what its designers might have intended”
Come on, that’s an engineer. (Even regardless the academic piece of paper)
Yes. Like Ford, Edison, Leonardo…
Exactly! but I suspect that you missed what I’ve written in round brackets.
You’ve forgot Tesla :)