At the top of the British electronic intelligence agency is the Government Communications Headquarters (GCHQ), a very public entity whose circular building can easily be found by any inquisitive soul prepared to drive just off the A40 in Cheltenham which is about two hours west of London. But due to the nature of its work it is also one of the most secretive of UK agencies, from which very little public information is released. With over a century of history behind it and with some truly groundbreaking inventions under its belt it is rumoured to maintain a clandestine technology museum that would rewrite a few history books and no doubt fascinate the Hackaday readership.
Perhaps the most famous of all its secrets was the wartime Colossus, the first all-electronic stored program digital computer, which took an unauthorised book in the 1970s to bring to public attention. Otherwise its historical artifacts have been tantalisingly out-of-reach, hinted at but never shown.
A temporary exhibition at the Science Museum in London then should be a must-visit for anyone with an interest in clandestine technology. Top Secret: From ciphers to cyber security occupies the basement gallery, and includes among other exhibits a fascinating selection of artifacts from the Government agency. On a trip to London I met up with a friend, and we went along to take a look.
Technology From Our Finest Hours

The first exhibition highlighted a fascinating aspect of World War I communications technology. In the trenches of the Western Front an intricate web of field telephone lines criss-crossed, and presented a easier evesdropping target than you might think. They used single-wire earth return and the enemy could use earth electrodes to sense their earth return currents.
The Fullerphone was built to defend against this It’s an ingenious telegraph that used a low-pass filter and electromechanical chopper to allow Morse code signalling with tiny currents that were so low as to be undetectable by the current sensing would-be interceptor.
When looking at the history of GCHQ it is inevitable that the path will lead to the WW2 codebreakers at Bletchley Park. There is the Enigma machine with an exploded view of a rotor, followed by a fully functional Enigma clone created by the prewar Polish codebreakers, and then a selection of exhibits dedicated to the vital work of the Poles who came to Bletchley to continue their work after the war had started. This echoes the sentiment of Bletchley’s prominent memorial to Polish codebreakers in acknowledging the importance of their work to the success of Allied codebreaking as a whole.
Part of the exhibit is dedicated to the Lorenz cypher, dubbed “Tunny” by the codebreakers. It is here that that we see the value of the GCHQ artifacts and get to lay eyes on some truly priceless relics.
Working with a captured German Lorenz machine, details of the cypher were pieced together, leading to the creation of Colossus. While we’re familiar with both the Bombe and with Colossus, it is only through replica units because the originals remained classified and were destroyed when they had outlived their usefulness.
GCHQ have loaned the Science Museum in London a genuine Bombe rotor, and a pair of original Colossus parts that appear to have at some point been turned into desk ornaments. Not even Bletchley Park themselves nor the National Museum Of Computing can match the importance of these artifacts, they are the Real Deal!
Cold War Tech At Its Chilliest: Suburban Spy Gear and Mechanical Cyphers

The Portland Spy Ring, exposed in 1961, was a spying network that passed Royal Navy secrets back to the Soviet Union. The news came with the revelation that its kingpins, a couple known as the Krogers, had been Soviet agents in deep cover as a respectable couple living in a suburban bungalow in a town just outside London. Learning that the People Next Door might be communist spies caused a sensation in the staid world of early-1960s Britain, and some of this gallery covers the public reaction to the case. Of technical interest are the Krogers’ radio transmitter and high-speed Morse sending unit, discovered concealed beneath their kitchen floor.
This exhibit includes a cross-section of encryption technology from the 1940s to the early 2000s in a series of glass cabinets. The existence of all of the machines on show have previously been classified, and in the case of the newest items though we are told their existence is no longer secret the technology they contain will remain so for a few more years.
Some of the earlier mechanical cyphers in the Enigma mould are not unfamiliar, but in these cabinets is plenty of gear never before shown in public. Everything from a super-secret 1950s Soviet mechanical cypher machine obtained after the fall of Communism to the Queen’s personal telephone encryption token is on show, and it was here that my friend and I lingered the longest.
While examining in detail the largest exhibit, a wartime rack-sized one-time-pad encryption system which appeared to have the pad encoded upon a paper tape, we were approached by and had an in-depth technical conversation with a Science Museum staffer. Was he simply someone who shared our interest in and knowledge of historical technology or had we been sounded out by one of the spooks themselves? Probably the former, but the prospect made us laugh. (As it happens back in the ’90s in one of my tech-related spheres it was intimated to me that somebody with my skillset at the time would find ready employment as a civil servant in Cheltenham, but I took a look at the salary as against the cost of housing in the city and decided against it. I suspect I would not have been good at the whole secret thing anyway.)
The Sinister Side Of The Spooks
It’s fun to see this equipment, but also refreshing to see items that don’t paint a rosy picture of all intelligence operations. The exhibit also challenges the visitor think about the implications of surveillance and espionage.
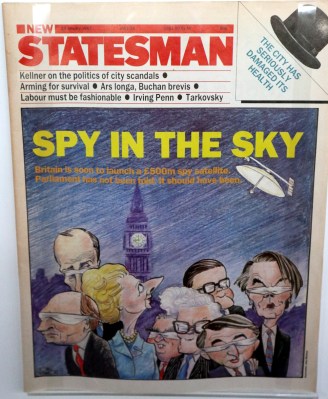
On display is the tale of a 1980s political scandal when the existence of a huge covert budget unapproved by Parliament was revealed. Under the codename Zircon, these funds were allocated for a top-secret British spy satellite. The story was surfaced by the investigative journalist Duncan Campbell (who in 1976 had been the first to reveal publicly in a Time Out article the existence of GCHQ) when a British Aerospace press release accidentally let slip some details of the project. The whole affair concluded with Special branch raids upon Campbell and his associates, the offices of the BBC, and the Spectator newspaper.
The Good Guys in Cheltenham built up in the previous section of the museum are revealed as a cog in a machine that includes a far more sinister side. In an era when public access to information was much more tightly regulated than it is for us in the Internet age, this revelation rocked the Government to its core.
Educating The Public About Their Data

The theme continues by introducing us to the world of Big Data and the threat that it poses. This should not be news to most Hackaday readers, but the general public remain largely unaware of the implications of so much information about them being available. There is an interactive artwork that mines Twitter and produces a mass of thermal printouts, and a 19″ rack full of what look like RAID units that we are told came from a Facebook data centre. Bringing us right up to date we have a look at the implications of IoT devices, including the infamous Cayla doll which had an unsecured Bluetooth connection.
It is here that the irony of the Museum entrance comes into focus. Entry to the gallery is free, but ticketed. At the barrier they ask you for a name and an email address, an early reminder of Big Brother’s eye on you. Is Mailinator still a thing I wondered, (it turns out, they are) as I remarked to the museum staffer the implications of starting a GCHQ exhibition with a data slurp.
An odd juxtaposition is provided by evidence of the community of GCHQ staff, in case we have reduced them to a shadowy faceless mass. We learn that the agency has a Lego club, and in a slightly surreal exhibit to prove it there are Lego models of the GCHQ building (complete with a laser-etched crest in the reception area) pictured at the top of this article. Something tells us that the model’s layout will not reflect the real thing.

Also on display are laptop parts from an episode in which technicians from GCHQ oversaw the destruction of computer hardware at the Guardian newspaper’s offices that had at one time held the revelations of the whistleblower Edward Snowden. The action that was symbolic at best in terms of its efficacy in destroying the data itself.
Then as you walk out the gift shop, displayed next to the GCHQ hoodie is a quantity of dust in a lighted frame. When GCHQ really want to ensure data never sees the light of day, they grind the machine containing it to a fine powder.
This Top Secret exhibition is only temporary. A fascinating way to spend about an hour and a rare chance to see some of GCHQ’s historical collection, as you might expect there’s nothing too secret in it but what’s there is still worth a side trip for anyone nearby. It runs until the 23rd of February 2020 so there is plenty of time left in which to see it, and there is enough in the rest of the Science Museum to detain a curious Hackaday reader all day. If you are visiting London, go along.




























The Enigma Machine and Fialka together! Love it!
If you’re in the UK but don’t manage to (or can’t readily) visit this exhibit at the Science Museum in London, it is expected to tour next year (pretty sure Manchester is on the itinerary).
If you do see it, take the time to watch the video of Duncan Campbell and the GCHQ Historian (Tony Comer), next to the Zircon stuff. It contains one of my favourite bits of video *ever* – a little clip of Duncan interviewing a UK government science adviser (Prof. Sir Ronald Mason) as part of the BBC programme he was making about Zircon.
I got the opportunity to attend the fancy grand opening event of the exhibit (as Duncan is my husband) but didn’t get to spend nearly enough time looking around the actual exhibit itself. I really want to go back and be able to take my time looking at all the other fascinating stuff gathered there.
(Unlike some of the Science Museum’s temporary things, Top Secret is free – but you do need to pre-book a free timed ticket on their website.)
They let us in without booking, perhaps because it was a weekday afternoon and the place was hardly rammed.
I certainly hope you had fun there, Jenny. I’d give anything to have the chance to visit that one.
Everyone reading this article has been added to 37 watchlists.
If I’m put on a watch list the watchers are going to be pretty bored.
AI watchers don’t get bored, that’s the point.
Actually … Why NI watchers get bored, and is boredom inevitable in sufficiently advanced I ?
why 37? ))
Five less than 42 ;-)
“At the barrier they ask you for a name and an email address”
Do you win a sticker if you SQL inject it?
Drop tables :D
Aw, goddammit, I was only there on Saturday, amusing one of the little darlings and never made it to the basement.
Curses!
Every horror movie tells you to not go into the basement.
Nice to see them at least acknowledge the existence of cypher machines after World War II. There’s tons of documentation, simulators, etc. about the German Enigma, but the whole point of the Polish/British effort was that it was flawed enough to be cracked from the outside!
I want to know about the details about the other machines worked, like the British Type X or the American SIGABA. Simon Singh’s “The Code Book” mentioned them, but no details. And no details about later Cold War machines, or even non-mechanical methods. How did the White-House-to-Kremlin Hotline work? Things like that. No need to have those still classified.
https://www.nsa.gov/about/cryptologic-heritage/historical-figures-publications/publications/assets/files/sigaba-ecm-ii/The_SIGABA_ECM_Cipher_Machine_A_Beautiful_Idea3.pdf
Thanks very much for your comment on the exhibition. I’m the exhibition curator and we have plans to include more content on the Science Museum blog including how some of the unclassified systems work. The focus of the exhibition was British SIGINT and GCHQ’s historic collections so unfortunately SIGABA was out but I did get to see one on display at the National Cryptologic Museum in Maryland – more information about their display at https://www.nsa.gov/about/cryptologic-heritage/museum/exhibits/#sigaba-ecm
At the super highest level of government, I would imagine there is things that can still be deduced from the internals of those. Things like who may have been working on the team that designed it, etc. Stuff that may still be classified because of some fixed time limit law that requires a big review meeting to declassify early.
I love those military grade all steel machines, I’ve been trying to get inspiration for my own builds from these old hunks of metal, a touch screen is all you really need but having a thousand knobs, buttons and dials is much more fun.
I’m building a desktop multimeter/general purpose arduino i/o and since it has to sit on my desk I’m making a steel box and trying to get that 80s aesthetic to match my vintage power supply. I’m more of an “if it works it works” kinda guy but its fun to do some heavy duty arts and crafts sometimes.
All steel construction, wire wrapping, hand drawn pcb, old school toggle switches, thats the stuff!
–unrelated: why do we have to use our email to post comments on this site? Kinda weird isn’t it?
“Perhaps the most famous of all its secrets was the wartime Colossus, the first all-electronic stored program digital computer, which took an unauthorised book in the 1970s to bring to public attention.” Does anyone know the Author and/or Title of the book?
That would be F. W. Winterbotham “The Ultra Secret”, first published in 1974. Winterbotham worked at Bletchley Park but not as a cryptologist and “The Ultra Secret” is now considered a bit inaccurate and also overly promoting of the work Winterbotham did.
Thx :-)
The NCM is a very worthwhile stop if you’re in DC. Mum was one of the WAVES at Nebraska Ave during the war. She died before I knew enough to put the screws to her about exactly what she did, but I have her discharge paperwork and her Unit Commendation ribbon. There’s a small piece of paper she was supposed to show any job interviewers after the war. It says something like “This person was engaged in important work during the war. Please do not ask them anything further about their war work.”