Faced with a broken USB dongle for our wireless devices, most of us would likely bin the part and order a replacement, after all the diminutive size of those things probably means hard to impossible repairability, right? Well, [The Equalizor] took it as a challenge and used the opportunity to practice his microscopic soldering skills just for funsies.
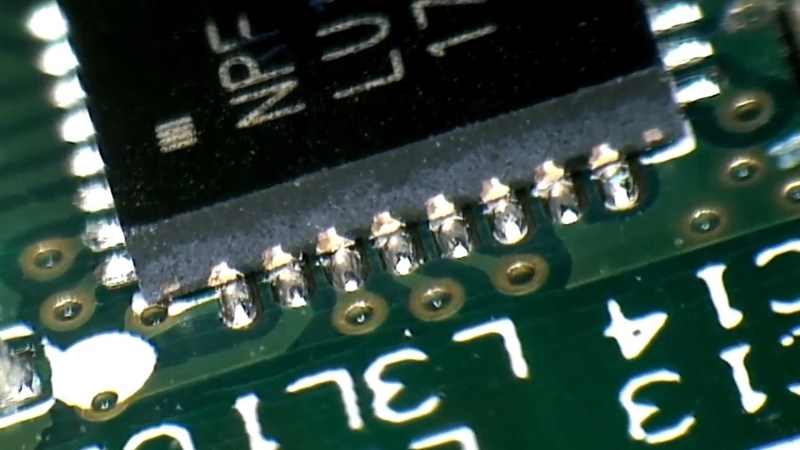
The wireless adapter in question, which came from one of his clients who accidentally bent it while it was plugged into a laptop, refused to be recognized by a computer under any circumstances. After sliding out the metal casing for the USB plug and snapping off the plastic housing, [The Equalizor] discovered that the slightly bent exterior hid a deeply cracked PCB. Then, with an inspection of the severed traces and lifted components, it was simply a matter of reflowing solder a few times to try to make the board whole again. Once the dongle was confirmed working, a new 3D shell was printed for it, replacing the original which had to be broken off.
It might not seem extraordinary to some people, but this video is a good example to show that repairs to delicate electronics in such a small scale are feasible, and can serve to reduce the amount of electronic waste we constantly dump out. Just because some electronics seem dauntingly elaborate or beyond salvaging, it doesn’t always mean there isn’t light at the end of the tunnel. You can see the work performed on this tiny dongle after the break.















It’s worse when you own a Microsoft Wireless keyboard and mouse set, rendering both useless when your dongle breaks, as you cannot pair a new dongle for your existing mouse & keyboard.
I haven’t actually watched the video, just read the text, and briefly saw “wireless adapter”.
Only after ending the comment above I saw the video title and realized this is exactly the type of dongle the video is about:
“Microsoft Cordless Desktop USB dongle repair”
I have such a dongle lying around after a failed fix attempt. maybe I should actually watch this and try again.
Go for it! Its a nice challenge and you have nothing to lose but a bit of time :-) Looking back on this video, some of those chip connections have almost no solder on them, making them prone to this kind of damage.
Would you be willing to attempt a repair on my dongle? Happy to ship to England!
I get why this is desirable behaviour if you want to sell offices full of them, don’t need crosspairing going on if 3 sets of batteries are dead the same morning. However it would also seem to add an extra expense in manufacturing, so one wonders if there was is there is a softer way of doing it going on. Does maybe the dongle pick the number/code when first initialised by driver, does maybe the keyboard have some super low power capacitor backed nvRAM to remember it??? So one wonders if leaving the batteries out for long enough would clear the keyboard and/or mouse.
I’m slightly more than academically interested, because I had a MS half-ergo* desktop for a desktop machine, where the dongle seemed to fry. It’s been languishing in storage, but recently I had an identical dongle turn up in a box of wires that came in from somewhere else. It’s an older type, uses PS/2 connectors. Have not tried pairing them yet.
( * I say half ergo, because it’s not quite as extreme/annoying as those full ergo ones. )
Anyway, if anyone knows about this in detail, whether it’s really hard firmware, or softer firmware, or firm seeming software or whatever, chime in and tell us about it.
Our office uses Logitech wireless keyboards and mice and never have issues with cross-pairing. Actual pairing is never lost in case of batteries dying or being changed. Never heard of any issues with these.
I buy Logitech due to its universal dongle. Life too short to deal with lost dongle. Never have a broken one. Lost it first.
I bought a Surface mouse/keyboard combo after a poor experience with Logitech a few years back, but I’m going back when these bite the dust. The buttons on the $60 Surface mouse started failing after a year, constantly double clicking when I’d single click, or letting up a long-click. I have some new tact buttons in my Digikey cart and will repair it, but for the price, I was not expecting bargain basement components. Everything today is designed to LOOK premium while being the same garbage on the inside.
I find it highly doubtful that the keyboard/mice end can be reset – that is the end its easier to bake in the ID on production and ignore. The usb end on the other hand surely must be able to be configured in some way its how that is the tricky part. (I figure the USB end will be as its got that USB connector that should be able to program it where the keyboard/mice would need either special jigs or firmware that listens for a rebind command and manual control to seek on the other end too. It also needs to be able to talk to multiple devices so its already the ‘complex’ PCB makes no sense to add costs to every peripheral.
The NRF datasheet for the chip suggests that its One Time Programmable and that it can have “125 RF channel operation, 79 (2.402-2.81 GHz) channels within 2.400 – 2.4853 GHz”. So I don’t think its pairing as such I think they just have to be on the same channel, and that’s programmed at the factory. As its OTP its fixed to whatever it left the factory with.
https://infocenter.nordicsemi.com/pdf/nRF24LU1P-OTP_PS_v1.0.pdf
Factory initialized unique keys and OTP firmware means that key injection and pairing MITM attacks. This has been a persistent problem for Logitech’s Unifying system: https://www.zdnet.com/article/logitech-wireless-usb-dongles-vulnerable-to-new-hijacking-flaws/
Worse than that, it’s easy to overwrite the firmware on Logitech Unifying receivers. It should be possible to patch the receiver FW to do something leaky, like periodically broadcast the pairing keys or traffic in the clear, do keystroke injection, or force the pairing process to use a weak key. Then it’s a just a matter of evil-maid substituting a hacked dongle for a target’s existing one and re-pairing their devices.
Funny, this is exactly what I’ve been working on for the last few weeks. I’ve bought some cheap MS keyboard/mouse sets with “missing USB receiver”, and I’ve just managed to get them to talk with a homebrewed receiver. I hope to have a writeup & code dump ready in a week or two.
Spoilers:
1. The firmware on the keyboard & mouse is not readout-protected. Get a SPI reader and have fun.
2. The devices use an OTP nrf24le1 soc (radio + 8051 cpu). Aside from code, the OTP contains factory-programmed settings such as address, RF channel set, and AES encryption key (not present in the mouse)
3. Despite the “O” in OTP, the configuration can be updated (a limited number of times) by appending new settings in the OTP area. The firmware simply looks for the last valid entry.
4. The firmware also implements “debug” radio commands which can, among other things, write the configuration area. This however, requires that you can communicate with the device beforehand. (note: I haven’t yet tested self-reprogramming on real hardware. It seems to work in an emulated environment though)
5. The devices implement a special “factory” boot mode, triggered by pressing a key combo on powerup. In this mode, the configuration area is not read, so all the settings are initialized to some hardcoded defaults. This allows you to establish communications needed for (4) without any modifications to the hardware.
6. So, basically, the devices CAN be paired to a different receiver, but MS just doesn’t admit it.
7. The original receiver is vulnerable to so-called “mousejack” attack, where an attacker sends unencrypted key messages which are happily accepted by the receiver. It’s trivial to filter out in the receiver firmware, but MS has an OTP receiver, so they can’t push a firmware update. I bet that they didn’t even bother to fix this in newly manufactured units.
Also, if you happen to have the original receiver (especially for the Sculpt Ergonomic keyboard), I’d be VERY interested in seeing the HID descriptors, I’m still having trouble with some special key reports. Email qq at kuku dot eu dot org.
Hi thanks for all that. I believe I have either the comfort or the laser desktop set. “New” dongle I have is a model 1029. Old one I may have discarded, because it caused a no-boot and a burning smell and at first I thought it had killed the motherboard. Anyway things like that I tend to not leave hanging around before I forget and manage to kill other hardware with them. Also, aware that most things are single custom IC doing the donkey work, I may have assumed it was that that had become defective, and thus no hope of fixing at the time.
The ubuntu forums have been showing some results for people picking around at them to enable various stuff on ubuntu, so might pick up some clues there.
I have a working Microsoft arc keyboard and receiver if you’re interested. I would love to be able to duplicate the dongle if it was lost.
“Also, if you happen to have the original receiver (especially for the Sculpt Ergonomic keyboard), I’d be VERY interested in seeing the HID descriptors, I’m still having trouble with some special key reports. Email qq at kuku dot eu dot org.”
Let me know what information you need/how to extract that (screenshots? just copy&paste?or a command output) and I’ll mail it to you :)
Thanks!
Here is how to obtain the information on Linux. I don’t have the slightest idea on how to do it on any other OS. Running Linux in a VM may be ok if the VM interfaces with the dongle directly at the USB level (instead of an emulated keyboard/whatever).
So, each HID device will have a directory in debugfs, something like /sys/kernel/debug/hid/XXXX:VID:PID.YYYY. In case there is nothing in /sys/kernel/debug, you may need to mount debugfs (sudo mount debugfs /sys/kernel/debug -t debugfs)
XXXX will depend on your USB controller. From what I can tell, VID:PID will likely be 045e:07a5. More google-guessing suggests that the dongle may expose three HID endpoints, so you may see three of these directories with various values of YYYY.
The first part I need is the contents of the “rdesc” file inside each one of these (sudo cat /sys/kernel/debug/hid/####/rdesc, for each #### matching the description above).
Additionally, I’d like to know how events are split among these endpoints. You can see the raw events via “sudo cat /sys/kernel/debug/hid/####/events”. Please try running cat on each of these pseudo-files, and checking what kind of activity triggers any output. I guess that each endpoint corresponds to the keyboard/keypad/mouse, but I’m not sure about the special keys.
Finally, as I mentioned, I’m having trouble decoding the special key (F1-F12) reports when the Fn switch is turned on. So my question is: does this keyboard report the special keys correctly under Linux? If so, please press each of these keys in sequence and send me the output from the events pseudo-file.
Also, my apologies for spamming the forum. If you need any further information please contact me using the email mentioned above.
Funny, this is exactly what I’ve been working on for the last few weeks. I’ve bought some cheap MS keyboard/mouse sets with “missing USB receiver”, and I’ve just managed to get them to talk with a homebrewed receiver. I hope to have a writeup & code dump ready in a week or two.
Spoilers:
1. The firmware on the keyboard & mouse is not readout-protected. Get a SPI reader and have fun.
2. The devices use an OTP nrf24le1 soc (radio + 8051 cpu). Aside from code, the OTP contains factory-programmed settings such as address, RF channel set, and AES encryption key (not present in the mouse)
3. Despite the “O” in OTP, the configuration can be updated (a limited number of times) by appending new settings in the OTP area. The firmware simply looks for the last valid entry.
4. The firmware also implements “debug” radio commands which can, among other things, write the configuration area. This however, requires that you can communicate with the device beforehand. (note: I haven’t yet tested self-reprogramming on real hardware. It seems to work in an emulated environment though)
5. The devices implement a special “factory” boot mode, triggered by pressing a key combo on powerup. In this mode, the configuration area is not read, so all the settings are initialized to some hardcoded defaults. This allows you to establish communications needed for (4) without any modifications to the hardware.
6. So, basically, the devices CAN be paired to a different receiver, but MS just doesn’t admit it.
7. The original receiver is vulnerable to so-called “mousejack” attack, where an attacker sends unencrypted key messages which are happily accepted by the receiver. It’s trivial to filter out in the receiver firmware, but MS has an OTP receiver, so they can’t push a firmware update. I bet that they didn’t even bother to fix this in newly manufactured units.
Also, if you happen to have the original receiver (especially for the Sculpt Ergonomic keyboard), I’d be VERY interested in seeing the HID descriptors, I’m still having trouble with some special key reports. Email qq at kuku dot eu dot org.
Hello, what is the progress? My transmitter is partially defective and I am looking for replacement.
Definitely keen to hear if you ever succeeded in this, I have 3 Microsoft Arc keyboard with no dongles that I’d love to resurrect!
Those Microsoft dongles are rubbish. Even if you take a lot of care with them and never bend, they will not work anymore after waranty period. I had two keyboard 3000 + mouse 5000, they both died because of the dongle. I opened the 2 dongles to look for the reason of those failures, both have the same defect. If i press the small BT component on the PCB; mouse and keyboard are imediatly detected, if i release the pressure on the small square component the link disappear. Even under the microscope i cannot see if a solder joint is not correct but i can easily see that the assembly quality is very poor. I will try to find the right equipment to remake the solderings like said in this video because i cannot accept to throw 200€ in the bin because of those 2 small defective parts which should cost nearly nothing. When Microsoft technicians says a dongle cannot be changed because it has only one frequency, they should have a look on models aircraft radiocontrol, they can be twenty flying together the frequency of each one takes care of their neigbours to adapt themselves ! They only reason is that Microsoft prefers selling an expensive keyboard and an expensive mouse even if those 2 are still in perfect condition.
I’ve recently managed to “recover” a mechanically damaged MS dongle by resoldering the NRF chip to a generic NRF24LU1 dongle board (try searching for e11-mlu1). The chip is quite unlikely to break, the paper-thin PCB gives up first.
If you’re comfortable with reworking QFN chips, it’s a straightforward solution. Of course, you’re left with a more bulky dongle afterwards.
Just get a Logitech mouse that uses the Unifying receiver. You can use the Logitech Unifying Software to pair a new dongle in under 30 seconds.
Looks like a good repair, though I think I would have potted it with epoxy afterwards to prevent future stress on the already damaged PCB.
He did.
Yup, I filled the 3D printed USB Plug up with Epoxy and pushed the whole board into it.
I looked into mice / keyboard pairing recently when giving my kids a raspberry PI to use for educational websites. Logitech has a paper on their dongle’s compatibility. Their mice / keyboards support up to 74 – 76 simultaneous devices in close proximity. They do have a PC tool available to change between fixed / isolated / multiple paring and listening to anything in range.
How does it manage that when the pairing software for Windows only does up to 6 per dongle?
78 channels x “> 65000” which is probably 65535 codes, TDMA to multiplex the many devices on each frequency.
https://www.logitech.com/images/pdf/emea_business/2.4ghz_white_paper.pdf
I would suspect the dongle “6” limit has something to do with available e2 to store paired items, processing power, or some other factor. It also may have limitations as to how fast it frequency hops. Consider it similar to being in a crowd of people and listening to a couple of people when 500 are talking. Listening to one is easy but 20 is another situation.
The following is based on the capabilities of NRF24LU1, which is used by some models of the logitech “unifying” dongle, with the 6-device limitation.
There can be countless devices in close proximity. First, they can use different channels, of which there are 126, but only 63 non-overlapping for the standard 2Mbit data rate.
Any devices sharing a channel will be distinguished based on a 5-byte address (defined by software configuration, and so, changeable). The NRF24L?1 radios can listen on up to six distinct addresses at once (with some limitations), and will ignore messages sent on other addresses. This is the reason for the 6-device limitation *per dongle*. The other guy can use his 6 other devices, possibly even sharing the same RF channel as you (the firmware will try to avoid this if possible to reduce interference), and so on.
The paper mentioned by thechad seems to be describing a technology distinct from the logitech “Unifying” dongles. For example, it mentions 300kbps data rate (unifying uses 2mbit), different number of channels, and TEA encryption (unifying uses AES). The basic principles seem similar though.
For comparison, here is a paper describing MS’ wireless technology.
https://download.microsoft.com/download/3/3/2/3324D913-59F5-4EA2-BC6E-AA6EDBECFB9D/Microsoft_Wireless_Comparison_vs_27Mhz.pdf
And then there’s the USB device that’s broke but still works.
I took a small USB flash drive apart to have just the metal part and the circuit board. Then took an old USB cord and cut off the end and frayed the wires. Carefully sliced open and carved out the rubber strain-relief boot around the end and put the flash drive into it and glued it back closed.
“Hey, you ever hear of a phantom limb where someone gets an arm or leg amputated and it feels like it’s still there? Well, this used to be the cord going to an old USB hard drive and someone cut it and stole the drive so now it’s just the bare wires . But watch this! See, I can plug it into the computer and the computer thinks the drive is still there!!!!! Yeah, it’s only registering as an 8GB drive but what do you expect?”
Heh, good one. There’s some really “nano” drives, wifi and other things around now, and a nano hub chip identified, be cool to do an “all in one” frayed end USB plug.
My broke but still works is an ancient prism2 802.11b card that is bent like a banana, lost it’s case over a decade ago, and overheats after a few hours, but still sees use as it seems to be the only one that every OS in the world supports out of the box (If it supported wifi at all) so gets used on clean installs to download the wifi drivers so the fancy wifi will work.
I have a Verbatim 4gig USB drive that’s the size of one of a Logitech receiver. A bit of close examination showed it has a Micro SD shoved into the end of the plug. A little prying with a sharp knife point had the card out. Then I carefully used a worn down cutoff wheel in a Dremel to carve a notch into the metal surround to make it possible to pull cards out with a fingernail. Currently has a SanDisk 16 gig in it.
The bigger the end on the donor USB cord and the smaller the original flash drive, the better/easier. On mine, I didn’t carve it out quite enough and if you look really close, you can see a tiny gap (maybe 0.2mm) along either side where it was cut open. But most people aren’t going to look that close at it.
Reminds me of the time a volunteer organization’s finance manager called me up to beg me to fix a thumb drive that wasn’t connecting and had the sole copy of the entire org’s financial records on it. What she didn’t tell me was that she had run over the drive with her car.
I managed to get the thing working (with tweezers and a fine-tipped soldering iron) well enough to grab a single copy of everything. Sometimes I wonder what the data would really have been worth to her or her boss.
“You can see the work performed on this tiny dongle after the break.”
I see what you did there XD
Thank you for posting about this repair !
My USB dongle had completely snapped near the USB contacts. From the video and also the reference schematic from the nRF24LU+ datasheet, I was able to bridge the broken connections and complete the repair.
Recently i found a way to fiz the broken Microsoft Sculpt Ergonomic USB dongle!
All you need is a generic USB NRF24LU1 based chipset dongle as show in this link:
https://pt.aliexpress.com/item/1005002721886615.html?spm=a2g0o.order_list.0.0.6fa9caa4isuzsc&gatewayAdapt=glo2bra
After that, you can change the original IC from your broken microsoft to buyed generic dongle. Works perfectly!!!
That’s all folks!!!
I found a altenative solution to fix the broken microsoft scultp ergonomic USB dongle.
First you need to buy a generic NRF24LU1 based usb dongle, as show in this link:
https://pt.aliexpress.com/item/1005002721886615.html?spm=a2g0o.order_list.0.0.2140caa4NzV9W7&gatewayAdapt=glo2bra
All you need is remove the original USB dongle IC and replace on new generic USB dongle (i used a SMD repair station).
After this my Microsoft Scultp Ergonomic return to live again \o/
Can you explain in more details what you have done?
– you get this module, then replaced the rf module on both keyboard and mouse?
can you send some pictures of where these chips can be found?
This technique is for “fixing a broken dongle”. You desolder the chip from the original (the chip is typically fine) and move it over to the generic dongle. So you don’t need to touch the keyboard or mouse.