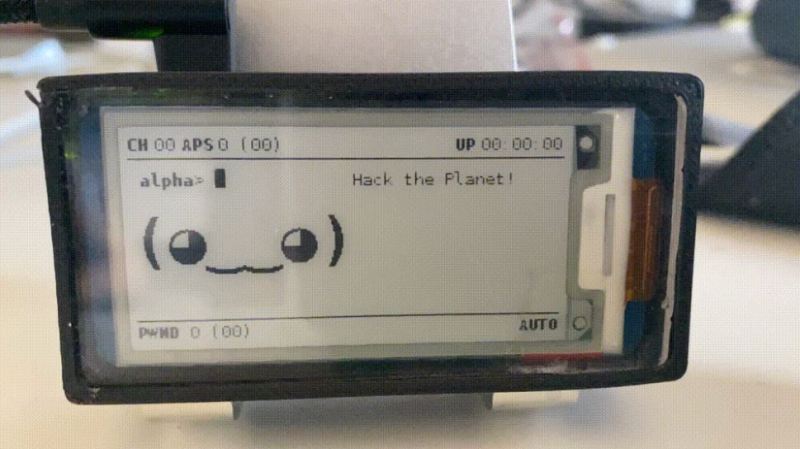
Knowing how WiFi networks can be attacked is a big part of properly securing them, and the best way to learn about it is to (legally) run some attacks. [Matt Agius] has been going down the WiFi-cracking rabbit hole, and in the process created Pwnagotchi Tools to automate the actual password cracking part.
The first step in cracking a WiFi network is to record the handshake that gets exchanged when a client connects to an access point. This has been made very simple thanks to Pwnagotchi, which turns a Raspberry Pi into an automated handshake collection tool and Pwnagothi Tools helps to automate the steps that follow. It downloads the handshakes (pcap files) from the pwnagotchi, and converts it to pmkid/hccapx files to use with the hashcat password recovery tool. Hashcat scripts can then be generated for the actual cracking using any of the attacks that [Matt] has compiled. WPA/WPA2 is slow to crack and requires a lot of processing power, so [Matt] also added the option to automatically provision AWS GPU instances to run the cracking task in the cloud. It also keeps track of the status of each of the handshakes being cracked.
As wireless networks and IoT devices become more pervasive, it’s important to know the dangers, and how to protect against them. WiFi and Bluetooth security is probably the easiest to learn about, but other networks are just as vulnerable when an RTL-SDR is used. Another option Flipper Zero, a hacking gadget for Sub-1 GHz networks inspired by Pwnagotchi, which recently hit $4.8 million in its Kickstarter campaign.















Oh cool, there’s a Goth version too
Really neat design!
There was an awesome tool https://github.com/jgilhutton/pyxiewps that actually worked surprisingly well.
You could just have a walk with this thing running and then find 5-10 passwords in a log file.
I’ve worked on a portable box with a raspberry pi inside that had 4 network cards. One was searching for WiFi, one was trying to crack the pixie wpa vulnerable ones, one was connecting to a WiFi and look for internet and one was for providing hotspot. I’ve gotten really far with it, until I’ve lost interest. The idea was that the box was always looking for WiFi and try to connect to them in order to share it to a device.it was in router case full of battery’s so the battery life was great. I wish I would have finished that…
I had something with very similar functionality (Minus the cracking). However the main purpose of mine was to provide wifi whilst in the car.
It continuously scanned for open wifi access points, hotspots, captive portals, tried default passwords for specific devices and tested if it could access the internet regularly or via a DNS Proxy (Iodine), etc. Obviously I was running a (very slow depending on connection) VPN to a server as well. Worked pretty well but I to eventually got bored of working on it once it was mostly completed. Also had its own battery that charged while the car was running.
My device was based initially on a cheap embedded linux board running openwrt with built in 2.4ghz and I added 5ghz with pcie to serve as hotspots for me, then USB Dongles for the outbound scanning and foreign network connections (2.4ghz, 5.8ghz, Bluetooth), GPSd for setting time and location marking.
Nice; if you restart the project you could consider LoRaWan instead of trying wifi for Internet acces.
That is super slow.
Yep, and that doesn’t matter if you only want to send limited information like gps position, SSID and password. And if you got coverage, it just works, or you can queue the info untill you got coverage.