Knowing how WiFi networks can be attacked is a big part of properly securing them, and the best way to learn about it is to (legally) run some attacks. [Matt Agius] has been going down the WiFi-cracking rabbit hole, and in the process created Pwnagotchi Tools to automate the actual password cracking part.
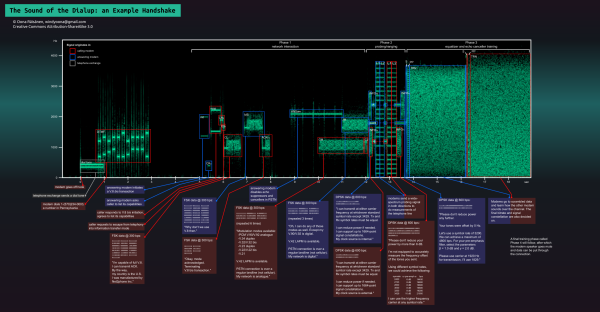
The first step in cracking a WiFi network is to record the handshake that gets exchanged when a client connects to an access point. This has been made very simple thanks to Pwnagotchi, which turns a Raspberry Pi into an automated handshake collection tool and Pwnagothi Tools helps to automate the steps that follow. It downloads the handshakes (pcap files) from the pwnagotchi, and converts it to pmkid/hccapx files to use with the hashcat password recovery tool. Hashcat scripts can then be generated for the actual cracking using any of the attacks that [Matt] has compiled. WPA/WPA2 is slow to crack and requires a lot of processing power, so [Matt] also added the option to automatically provision AWS GPU instances to run the cracking task in the cloud. It also keeps track of the status of each of the handshakes being cracked.
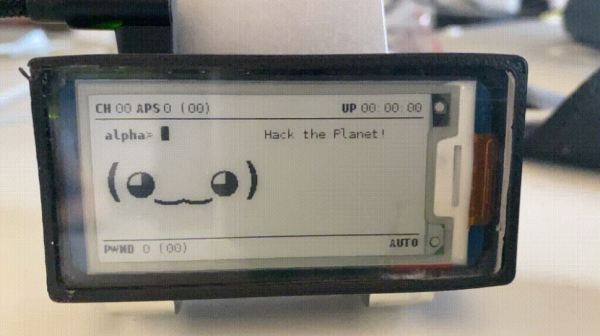
As wireless networks and IoT devices become more pervasive, it’s important to know the dangers, and how to protect against them. WiFi and Bluetooth security is probably the easiest to learn about, but other networks are just as vulnerable when an RTL-SDR is used. Another option Flipper Zero, a hacking gadget for Sub-1 GHz networks inspired by Pwnagotchi, which recently hit $4.8 million in its Kickstarter campaign.