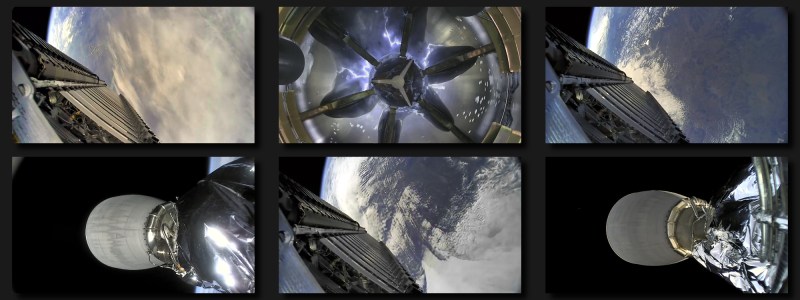
A few weeks back we brought word that Reddit users [derekcz] and [Xerbot] had managed to receive the 2232.5 MHz telemetry downlink from a Falcon 9 upper stage and pull out some interesting plain-text strings. With further software fiddling, the vehicle’s video streams were decoded, resulting in some absolutely breathtaking shots of the rocket and its payload from low Earth orbit.
Unfortunately, it looks like those heady days are now over, as [derekcz] reports the downlink from the latest Falcon 9 mission was nothing but intelligible noise. Since the hardware and software haven’t changed on his side, the only logical conclusion is that SpaceX wasn’t too happy about radio amateurs listening in on their rocket and decided to employ some form of encryption.
Since this data has apparently been broadcast out in the clear for nearly a decade before anyone on the ground noticed, it’s easy to see this as an overreaction. After all, what’s the harm in a few geeks with hacked together antennas getting a peek at a stack of Starlink satellites? [derekcz] even mused that allowing hobbyists to capture these space views might earn the company some positive buzz, something Elon Musk never seems to get enough of.
On the other hand, we know that SpaceX is actively pursuing more lucrative national security launch contracts for both the Falcon 9 and Falcon Heavy. For these sensitive government payloads, the normal on-screen telemetry data and space views are omitted from the company’s official live streams. It seems likely the Pentagon would be very interested in finding out how civilians were able to obtain this information, and a guarantee from SpaceX that the link would be encrypted for all future flights could have helped smooth things over.
At the end of the post [derekcz] echos a sentiment we’ve been hearing from other amateur radio operators recently, which is that pretty soon space may be off-limits for us civilians. As older weather satellites begin to fail and get replaced with newer and inevitably more complex models, the days of picking up satellite images with an RTL-SDR and a few lines of Python are likely numbered.
















Double standards are the only standards. There are two sets of rules, one for the haves, one for the have nots. I’m all for starting up opensource space flight. Everyone who wants to go to space should be able to. Everyone who wants to explore the universe should be able to. Everyone who wants to escape his fellow man should be able to. There is space enough for everyone, but I guarantee corporations will start carving up our infinite universe for their individual gain. Global warming wiping us all out may be the best thing for the universe.
It is completely irrelevant for the universe, if humans exist or not. So no “best thing”. Even for the existence of the planet it will not change anything. The planet can – and will – only be destroyed when the sun ends it’s life.
But also any climate changes are unlikely to wipe us all out.
You say it is completely irrelevant to the universe, and that’s true as far as inanimate objects don’t care about anything, but any other lifeforms out there may have a different opinion about earthling corporations claiming their planets. Simply look to our treatment of native americans and africans for ideas of what we may get up to once we start expanding beyond our planet. Of course we cannot currently destroy our planet a la death star, but that’s not what I said, so … Whatever.
Even if the human race lasted another billion years, we’d manage to potentially colonize a handful of planets and MAYBE make contact with 1-2 intelligent races. The universe is incredibly vast, we aren’t going to hurt it…
If you want to work on Open Source space flight, check out OpenResearch.Institute and Libre.Space
Unfortunately, organizations like SpaceX don’t get the to let all of their information out to the public. Open Source space projects can, there is a carve-out in ITAR and EAR for them. See https://www.openresearch.institute/2020/08/18/cj-determination-open-source-satellite-work-is-free-of-itar/
There is also law against publishing imaging of the State of Israel with greater than a particular resolution. It seems like someone used public satellite data to bomb them.
Interesting… “ground” laws and space flights probably won’t mix well for Open Source people, except if some powerful governments want to politically back up Open Source projects.
From the looks of things I am guessing that they didn’t fill out the NOAA Remote Sensing
license application soon enough – https://www.nesdis.noaa.gov/CRSRA/licenseHome.html
This has happened before – https://www.theverge.com/2018/4/5/17197742/spacex-falcon-9-rocket-launch-livestream-noaa-regulation
Not in this country…
I used to work on telemetry systems. The reason its all protected is to prevent customers and insurance companies from knowing just how messed up the satellite really is. Besides 99% of the telemetry is incredibly boring.
That makes total sense – money. Although for latency, which is something you do not want to add on live telemetry, I’m guessing that the encryption would be a very fast computationally light algorithm. That does not mean insecure, it just reduces the search space for the potential algorithms that are used.
I would use either AES with hardware acceleration (very common these days), or otherwise ChaCha20 in software.
Either of those two would be unbreakable and quite fast. If you need low latency, then use AES as a stream cipher, and pre-generate a bunch of the pseudo random sequence.
The data link is already encoded with a PRNG to limit runs of single values. All you need to do is use a different polynomial for the PRNG or at the very minimum, just use a different seed value and it’s all suddenly noise with zero additional computational overhead and it only takes a single line program change.
They are probably using a simple LFSR, which isn’t secure enough.
If they are using LFSR, then state can be recovered with the Berlekamp Massey algorithm. Assuming telemetry is highly redundant in the time domain, other cryptanalytic techniques may apply.
I think people are ignoring the entirely legitimate reason SpaceX would encrypt telemetry links. The militaries they contract with aren’t going to want anyone with an SDR, tuned antenna, and a bit of python code to eaves drop on the launch with nice up close and personal shots of their latest spy or communications satellites with no effort whatsoever. It’s one thing to infiltrate the vendors or get telescopic shots, quite another to get high resolution photos as it’s being launched.
Otherwise…
I seriously doubt there’s a lot to be gained tech secret wise from telemetry that SpaceX hasn’t already leaked themselves. They just don’t want people eavesdropping in on their commercial launches without their annoyingly bubbly commentators running PR interference if they screw up a launch/landing. I doubt they could prevent customers and insurance companies from finding out they flubbed a launch. That’s just ridiculous. One court backed subpoena from the insurance company would be all it’d take.
ONE day, they may need help from the amateur fraternity and now they won’t get it……
While they’re operating Starlink? Doubtful.
Surprising that it wasn’t encrypted from the start.
Well, predator drone video feeds weren’t encrypted originally either…
https://www.schneier.com/blog/archives/2009/12/intercepting_pr.html
not just the video feed… they were using unencrypted GPS to position the drone: https://hackaday.com/2012/07/01/spoofing-gps-and-getting-your-own-uav/
Kind of like the early days of C-Band TV.
The government and SpaceX wants to know who received the downlink just for HIRING THEN.
Now it’s one level UP, who will decipher the downlink.
I’d be pretty tempted to just enjoy the video and data, keep quiet so the level of encryption doesn’t get worse.
Guys with DoD IDs must have shown up somewhere and brown-jocked a few nerds over that security lapse. No advantage in giving the Chinwah Rocket Corp any helpful information is there?
Easy fix, just not encrypt streams when launching spacex own missions but encrypt them when they launch customer equipment…
It’s not a brilliant idea to add less tested variants to working systems.
Yup. Huge risk of accidentally leaving the encryption turned off for a DoD customer mission.
DoD-certified crypto has 324873432482 different failsafes to ensure that unencrypted data never “fails through”.
as someone who followed this project from completel beginning i must say.
why this article exists without mentioning r00t.cz or uhf-satcom, they were the guys that initially decoded falcon9!!!
https://www.r00t.cz/Sats/Falcon9
Back in the day, nothing was encrypted and you got all kinds of things from the air https://youtu.be/xnH7ItynPGw?t=470
Is there such as thing as “intelligible noise”?
I thought the phrase was “nothing but unintelligible noise”. If noise is intelligible it is no longer defined as noise in a scientific sense right?
Country and Western music?
On a more serious note, fricatives, sibilants and whispered speech are random noise that is band pass filtered by the vocal tract, and intelligible.
I am sure Rap music (?) is being used to pass secrets. It would make a better encoding scheme than C/W. 😆
Which is why we’re talking the data sense instead of the scientific sense. This is encrypted RF communications. If I can detect and demodulate the RF signal, it is intelligible. If I there’s no pattern to the transmitted bits, that is noise.
Exactly my thoughts as well, it is just noise to you. But you can see there is a design behind it, so its ‘intelligible’ to whoever speaks the right language, and not just nonsense of real random static noise…
Thanks for that, I was trying to articulate the point you make in my original comment but couldn’t get the wording right so deleted that part out. What you say makes sense, I just didn’t know if I’d been saying that phrase wrong all my life or not ha
When the Skylab went up, there were attempts to get ham radio on board. Owen Garriott wanted to take a little SSB transceiver up. Eventually NASA said no, because they wanted control of what was said (I can’t remember if that was specifically said, or implied).
And all this talk about rtl-sdr does a great disservice to what came before. People listened to satellites as soon as they went up. Not just Sputnik around 20MHz (easy since it needed oenky a shortwave receiver), but Popular Electronics had a converter project for 108MHz in the early sixties. And for a few years had a mothly chart of new satellites. CQ Magazine had a monthly column for a while about new satellites, and had a converter project ahead of Apollo 8 (though that turned to be on the wrong frequency).
Some of the moonbouncers had equipment in place for Apollo 11, no success, but heard something in a later mission.
Someone in England received weather pictures around 1966, and slowly that was a thing to do.
There was a group of school kids in England who got interested and in the sixties and seventues were often the source of information about new satellites. (Since after the early launches, there weren’t press releases.)
And nobody had an rtl-sdr when OSCAR 1 went up in December 1961, and all the others that followed.
Just because it took some effort doesn’t mean it didn’t count.
Although ham radio on Skylab may not have happened, ham radio operations DID happen from the Space Shuttle (https://en.wikipedia.org/wiki/Shuttle_Amateur_Radio_Experiment), and have been happening for 20 years on the International Space Station (https://en.wikipedia.org/wiki/Amateur_Radio_on_the_International_Space_Station). Ham radio transmissions are unencrypted by US law and international agreement, with a narrow exception for control uplinks to amateur satellites. (The downlink telemetry is not encrypted.) Ham radio operations with the ISS are very public (schools are encouraged to get their students involved, and scheduled voice conversations with astronauts and cosmonauts are only with schools and clubs) so everybody is very polite and proper. The radio equipment on the ISS also serves as a voice and digital repeater when the crew is not present on the radio.
Hmm last flights there where no images streamed from the rocket until it was over the horizon, i guess they dont yet have the means to encrypt the video signal and choose not to broadcast video untill no one but spacex can receive them. First i figured it was about that engine that blew but this makes more sense i guess. Spacex had a problem a couple of years ago that it discovered that they might not have a license to broadcast the pictures .. and they didnt broadcast for that flight. Last flight we only had images from the 2nd stage well after staging .. and from the 1st stage well after staging and from the landing. Maybe they made up the lack of images by showing the landing as seen from the rocket. Or maybe streaming those images via the support ship is now more affordable with starlink. Or maybe it was just a rare daylight landing.
If they -are- using LFSR, which is possible if they were in a rush to have -something-, then for a width n LFSR all we need is 2n of its outputs to retrieve the state using Berlekamp-Massey. If telemetry is highly redundant in the time domain, which I expect it is, there may be other hooks for cryptanalysis.
I assume they encrypted it because they run military payloads which contractually require privacy. Also, the article suggests that just a few geeks were looking at the data, but that was inaccurate, they published it to the world and the press picked up on it. The telemetry became very public. I understand their decision to encrypt it.
vaulted ceiling
Disappointing but also probably for the best. Our digital infrastructure should always be built (hardware, software, and communication protocols) with security in mind.
This communication should have been secured from day 1
What communications?
It was transmit only telemetry. The rockets run on internal control at that point.
I think it should be easy to de-crypt the link.
After all, the upbound link is just a repeating “”Don’t blow up! Don’t blow up!…”
B^)
How do you know that this stuff has been not noticed in a decade? That was an odd statement. Just because some people put it up on reddit after a decade doesn’t mean no one else saw it and kept it to themselves.
I tried to receive data from the Starship test launches but all I could make out was… “Ohhhh shiiit…. BOOM !”.. 😆
That’s illegal, FCC transmissions in any spectrum (other than Military use spectrum) are not allowed to be encrypted. Police/emergency bands are “trunked” but that’s not encrypted its different…so curious about this change from SpaceX
Incorrect. Plenty of transmissions are encrypted, including satellite radio and TV and cellular telephones. Even ham radio operators can encrypt satellite uplink signals for control (that’s the only use of encryption they’re allowed).
What are you talking about? Cell phones (since 2G, I think), Wi-Fi, and Bluetooth all use encryption. They wouldn’t be popular if they didn’t. Amateur radio is required to be unencrypted (to prevent its use for purposes that should use commercial radio licenses), though even that has an exception as Shirley mentioned. (Well, technically, I believe encryption’s actually allowed for any use of amateur radio as long as you publish the keys so that anyone can decrypt it, but that’s not very useful for secrecy.)
Negative, 2g-4g are not fully encrypted to today’s standards of data encrytion methods. Voice networks are easily hackable. Data transmissions are vastly different.
Ok, sorry for the original response, I see things have changed within the past few years that make it allowable (2014 era)…but voice comms, and some early bluetooth prior to 4.0 do not offer full encryption…but things are getting better these days…
My last post …
I’ll grant that “encrypted” and “fully encrypted to today’s standards” are not the same thing. GSM voice and DMR land mobile are old standards that use out-of-date encryption that isn’t difficult to break in 2021. The encryption is enough to prevent casual eavesdropping but won’t stand up to a serious attack. CDMA voice never had encryption at all, depending instead on the protection through obscurity that it derived from the use of CDMA modulation. (How to go from the device’s IMEI or MAC address to its spread code has not been published, and so far as I know still has no publicly released crack.)
But there is no legal bar to using stronger encryption. Those standards were much more difficult to break with the technology of the time when they were adopted than they are now. Cellular voice is in the process of shifting to voice over LTE (VoLTE), using the more strongly protected data channel rather than the old dedicated voice path. We’re now moving toward 5G networks, which means that voice calls on those would technically not be VoLTE, but the principle is the same.
Canada (and maybe others but definitely not the US) has that rule for allowing encryption if it is a publicly published key.
While it might not be legal, encryption is most assuredly being used on amateur bands here in the US. The glut of older Moto gear on the market makes it hard to not play around with “let’s go secure”
The FCC won’t police the HF bands, the repeater jammers, the people using someone else’s callsign, etc.
I’m not worried about firing up some AES256 once in a while.
It’s ok if China sees it, but a few amateurs? no-no. Turn encryption on!
With encryption on, China can’t see it either.