In an ideal world we would never lose our belongings, and not spend a single hour fruitlessly searching for some keys, a piece of luggage, a smartphone or one of the two dozen remote controls which are scattered around the average home these days. Since we do not live in this ideal world, we have had to come up with ways to keep track of our belongings, whether inside or outside our homes, which has led to today’s ubiquitous personal tracking devices.
Today’s popular Bluetooth-based trackers constantly announce their presence to devices set up to listen for them. Within a home, this range is generally enough to find the tracker and associated item using a smartphone, after which using special software the tracker can be made to sound its built-in speaker to ease localizing it by ear. Outside the home, these trackers can use mesh networks formed by smartphones and other devices to ‘phone home’ to paired devices.
This is great when it’s your purse. But this also gives anyone the ability to stick such a tracker device onto a victim’s belongings and track them without their consent, for whatever nefarious purpose. Yet it is this duality between useful and illegal that has people on edge when it comes to these trackers. How can we still use the benefits they offer, without giving stalkers and criminals free reign? A draft proposal by Apple and Google, submitted to the Internet Engineering Task Force (IETF), seeks to address these points but it remains complicated.
Game Of Tag
The first range of Bluetooth-based personal tracking devices that popularized tracking one’s belongings using these devices came from Tile, with the release of their Bluetooth Low Energy (BLE) 4.0-based trackers. These were marketed for keeping track of one’s keys, a backpack and similar easy to lose items, with an associated smartphone app being used to detect the tracker within a range of about 30 meters. The second generation also added a ‘find my phone’ feature where pressing a button on the Tile tracker causes the paired smartphone to make a noise.
Current Tile trackers feature a ‘crowd GPS’ feature, whereby a reported-as-lost Tile tracker coming within reach of any smartphone running the Tile app will result in the location being anonymously sent to the owner. While quite popular, it wasn’t until the Apple AirTag was released in April of 2021 that suddenly personal tracking devices appeared everywhere. The AirTags use the ubiquitous Apple Find My network that is powered by the about one billion Apple devices around the globe. Meanwhile the Samsung ‘SmartThings Find’ network is used for its Galaxy SmartTags tracker devices.
These devices only function fully within their own ecosystem. AirTags can only be paired with Apple devices, and Samsung SmartTags only gain access to ‘SmartThings Find’ where Samsung smartphones are involved. Although the BLE communication is universal and allows any BLE-enabled device to at least see the trackers advertising their ID, recent features such as precise localizing via ultra-wideband (UWB) communication – using e.g. Apple’s U1 chip in iPhones – is less universal, just like access to the tracker’s built-in speaker and stored (NFC) information.
Thus the bad news is that for example an AirTag can only be tracked while it is in range of Apple devices configured to listen for AirTags and will essentially vanish the moment it’s out of range. The good news is that you have to travel to pretty remote locations to get out of range of any and all Apple devices and never get near pockets of civilization again to make an AirTag go fully AWOL. If you, on the other hand, have an Android device, your only recourse to locate nearby AirTags is using the Tracker Detect app. Similarly, if you use a Samsung SmartTag or Tile, you need their app.
With Apple devices featuring so prominently, it is perhaps little surprise that AirTags also see the most use outside of regular legitimate uses. Recently, for example, the New York Policy Department has been giving out free AirTags to residents which they can hide in their cars, as a way to address rising car theft. If the car gets stolen, then the AirTag should theoretically lead the NYPD straight to what’s left of the car in the chop shop, or maybe even the intact vehicle and highly embarrassed thieves.
Naturally, everything that can be used for good can and will be used for evil, which is where the privacy aspects come into play.
Tag Warfare
A kind of weapons race has been taking place between those who would abuse these cheap and powerful tracking devices and those who are at risk of becoming a victim of such abuse. The commonly cited example of stalking is one of these, but another one involves the exact inverse of tracking down stolen cars, in the form of car thieves tagging targets with an AirTag while the vehicle is in a public area, so that they can steal it later when it’s in a more secluded area.

So how do you make a tracking device into not-a-tracking-device when it shouldn’t be one? How could you make a set of rules to tell these situations apart? In the draft that Google and Apple engineers submitted to the IETF, they propose a number of requirements that they hope will ensure legal tracker use.
The primary suggestion is to force the tracker to emit noise with its speaker when requested by a person who thinks that they’re being tracked, generally the person who got a warning about an unknown AirTag. The essential problem here is that anyone who has nefarious intentions will likely disable the speaker, along with any vibration motors, LEDs and similar features which are listed in the draft. As the AirTag teardown and those of similar devices by the folk over at iFixit makes abundantly clear, these devices are not hard to disassemble, and disabling the speaker very straightforward, while AirTag clones can conceivably work around Apple’s privacy checks. We’d say that any reasonable anti-tracking measures should be based around the assumption that the tracker is mute and has no functioning fallbacks.
Fortunately, not all hope is lost. Unlike dedicated surveillance trackers, AirTags are fairly easy to track because they communicate primarily via Bluetooth (BLE). By standardizing the information made available via BLE and possibly NFC, a subset of information could be made available to anyone. This could be used to identify the owner even when the tracker is not put into ‘lost’ mode, using details like a partial email address or phone number. This kind of standardization could at the very least seriously cut back the complexity of keeping track of unwanted trackers without juggling half a dozen apps on one’s smartphone.
It’s a shame that the draft does not mention UWB, even though this would probably be the easiest way to locate a tracker, while also being the hardest to circumvent — involving more work than simply ripping out a speaker. The draft does spend some time on a near-owner and separated mode, which would affect what information would be broadcast, but it’s hard to tell what the exact impact of this might be.
Existing Fixes
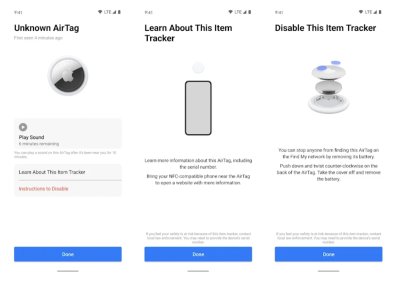
One might be excused for thinking that there currently exist no real attempts to reign in abuse of these tracking devices, but this isn’t entirely correct. Apple has detailed instructions on how to set up an Apple iPhone, iPad or iPod Touch so that you receive alerts when a likely unwanted tracking device is moving with you. After receiving an alert, the offending tracker can then be located either by sound, or if the i-device has UWB, by localizing its UWB signal.
Meanwhile on the Tile side of the fence, the company has taken a polar opposite approach to Apple with its Anti-Theft mode. Essentially in this mode Tile trackers are rendered invisible to the Scan and Secure feature of the Tile app, with the reasoning that this way thieves can not detect the tracker. Although this would seem to invite every possible abuse, the company will perform an intense ID verification on the requesting user, linking their real-life identity to all of their tracking devices and threatening with massive fines should anyone abuse the system despite this.
Google is at the table here because they are rumored to launch their own personal tracking devices soon, with similar specifications to AirTags. These would use Google’s Android-based Find My Device network, and the possibility of some level of interoperability between all these tracking devices by itself is not a terrible idea.
Making Water Not Wet
Something as simple as a knife can be a very useful tool, but also a murder weapon. A Bluetooth tracking device can help you locate your lost luggage, but also lead to a harrowing confrontation with a stalker or get your car stolen. The problem is that even with added technology a tracking device doesn’t know the intent of the user.
Until we get to a point where a tracker will respond to an unscrupulous owner with an “I’m sorry, Dave, I cannot let you do that.” we have to accept that silicon can’t solve everything. We’re not hopeful for Apple and Google’s all-technology solution to this dynamic problem — a problem so thorny that it almost makes us forget that all of this began because we just wanted to a good way to keep tabs on our keys and backpack.

















Well BT already lets one know like devices in the area even if not paired taking away any stealth capability. The rest is friend or foe, a known military problem.
Indeed. When I acquire a tag, add its id to my list of tags. Then, anytime in the future, show me a list of tags around me. Mark the ones I have on my list, and show me when and where the other ones were seen. If I keep seeing the same tag that’s not mine everywhere I go, then it’s attached to me or my belongings somewhere.
I think it was in a SDR-based newsletter that I saw someone had come up with a FOSS app for a similar concept but listening to any common radio signals following you around to show you when you’re being tracked/followed, in particular by other phones.
All of this tracking already exists, of course, in most people’s iOS and Android-based mobile phones, as well as most people’s cars, it’s just the power to use it rested mainly in the hands of relatively few people/companies/governments. Now it’s practically going mainstream, it makes me think of Isaac Asimov’s short story about a neutrino-recording device that was made OSHW before the prototype could be destroyed.
True. And because that’s so creepy, there’s a reason that police need to get a warrant to do that.
OTOH, I just looked it up for private people. If you’re one state, it’s “criminal surveillance”, in another state, it’s totally fine, and in another you’re a stalker. Go figure.
That’s “The Dead Past” by Isaac Asimov.
https://en.wikipedia.org/wiki/The_Dead_Past
The chronoscope was already in use by the government, supposedly doing historical research by viewing the past.
A historian who couldn’t get time for his projects on the government’s one (large, expensive, and inefficient) chronoscope talks a physicist into trying to build a smaller chronoscope. The physicist suceeds by using advances in physics outside of the neutrino physics usually associated with the chronoscope.
He discovers that the chronoscope can’t view back more than about 120 years – the research the government published had been done by conventional means and only ascribed to the chronoscope.
The government was trying to keep that fact secret because the past begins now – besides viewing the past, it can view the present at any place on the Earth.
The physicist and the historian hadn’t thought of that, but had arranged for the plans to be published before the government could stop them.
The story ends with a government agent hoping that the two will enjoy living in their new world where everyone can see everything everyon else is doing – “Happy goldfish bowl to you, to me, to everyone, and may each of you fry in hell forever. Arrest rescinded.”
Huh. That’s an Asimov story I missed! I was thinking of the one where a very wealthy man bankrolls the development on behalf of his wife after they lost their daughter in a house fire, seeming to not really believe it would actually be developed but hoping to say to his wife that he’d tried every avenue he could to find out what happened. He gets increasingle nervous as the machine becomes a reality and at its first demo, just before it shows the moment the husband did whatever it was that caused the fire, he takes a wrench (or similar) and destroys the machine as he can’t bare to revisit his guilt. Unbeknownst to him, the developer has already given the blueprints to a journalist, who’s just had them published.
We’re thinking of the same story. The historian wants to use the machine to prove that Carthaginians didn’t really sacrifice children to Moloch by burning them alive. His wife wants to use the machine to see their dead daughter again.
The daughter died as a child in a fire. The historian is afraid his wife will see that he caused the fire. He himself doesn’t know for sure what happened. He was home alone with the kid, at night. He woke up in the burning house and barely managed to get out alive – he couldn’t save the daughter. He is afraid he fell asleep smoking a cigarette and caused the fire.
The historian isn’t rich. I think he does use up all of their savings on the project.
Look it up, re-read it. You’ll see we’re talking about the same story.
I’ve been looking for an SDR tool to detect these tracking devices, do you have any decent keywords to search for? I’ve been searching for thing like “RTL-SDR airtag” with no success.
I feel like detecting tracking tags could be the “killer app” for SDR and I am very surprised that I haven’t found a nice solution yet.
It confuses me that there are multiple ways I can use my SDR to listen to the broadcasts of my wireless weather station, but none to tell me if I am being stalked. I would have thought there would be a greater demand for the latter.
And no, a smartphone app doesn’t suffice. Apple and Android have zero incentive to make their tags too easy to detect, and we have seen this evident in all their half-assed superficial approaches to addressing the stalking problem.
I won’t be disabling the BlueTooth LE scanner in my android phone. Even if we go the route where all manner of sensors and control devices ‘piggyback’ on my mobile data quota, the benefits in helping someone find a lost pet, or indeed a loved one who may be suffering Alzheimer’s, far outweigh the jilted lover scenario. My old maths teacher went like that…wandered off across the city, and off into the bush. A road worker discovered his remains at the side of the road, some months later. HUGE search, no result.
I don’t think people are getting stalked with airtags at any significant rate. They are being used to deter crime. Usually you have to put at least two on a bike, because the thief will find one using all these wonderful features and throw it in a dumpster. As if the police will ever help; the crime is the point.
But isn’t that the main problemn anyway?
How can one differentiate between “this is my bike and I want to know where the thief is taking it” and “this is not my bike, but I want to know where its owner goes”. Technically you can’t because it’s the same situation.
Sure, the Tile way with invisible mode after ID and fines sounds reasonable, but also not scalable and slow so maybe to late.
This is one of the most balanced and technically accurate articles on the topic that I have ever read. And I spent many years at Tile as a firmware engineer. To say that we were concerned about every privacy issue is not an understatement and your subtitle “Making Water Not Wet” perfectly summarizes the pickle we found ourselves in.
Another brand in this field is Chipolo.
Anybody know a source for a cheap decent broad band RF detector? Preferably one that can detect pulsed transmission.
Getting an apple product to be able to detect apple tags, Samsung, etc etc is a non-starter.
For those of you with big brother cars, it will help you locate and remove the cars antenna.
Double plus good!
Just hope they don’t use the estop radar antenna to call the NSA.
Thanks. Very interesting.
There are many versions of trackers out there and the race seems to me to be about technology, plus the costs are high to cover all your items, with the added risks you mention.
I’m a rep of a tagging business so apologies, but I don’t get that the solution has to me more tech, it could be a simple ‘analogue’ answer.
No bull from me; our website shows a tagging system that works all over the world with just one code on all your items. And your data is not collected or shared. Go figure!
So, they are trying to fix what they can’t
What’s the difference between a GSM based tracker from china and an airtag when used for evil purposes?
None!!!!!
I don’t understand the statement that UWB would be the hardest to circumvent. In practice, UWB is the simplest technology to just leave out.
Today you can buy “Works with Apple Find My” Trackers for less than 10 EUR, delivered from China within 10 days, from e.g. AliExpress. Most of them seem to be made by Shenzhen Tingting or ShenZhen RiShengHua, some are re-branded by importers – even Aldi Germany sells two for 29.95 EUR.
They are extremely easy to disassemble and if someone wants to disconnect or remove the speaker, that’s trivial. And they don’t contain UWB in the first place.
So I don’t see why any stalker would spend money on a full AirTag with UWB instead.