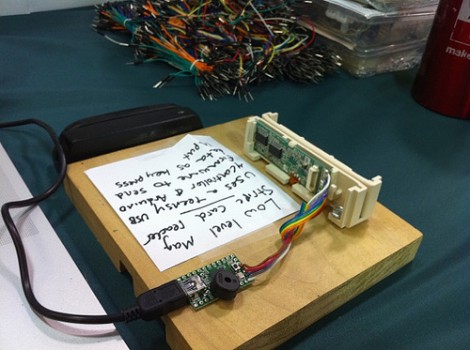
Here’s a hack that makes business sense. [PT] recalls last year’s HOPE conference when their booth was using a virtual credit card terminal for purchases that required manual entry of card information. This year they’ll have the same virtual terminal but this magnetic stripe reader will fill it out automatically.
A magstripe reader (reading only, no funny business here) from Mouser grabs data from the card. A Teensy microcontroller board, which identifies itself as a USB keyboard, automatically fills out the virtual terminal from the parsed data. The real question, are his customers comfortable sliding their plastic through a hacked reader?
















Are there any magnet based cards left?
Like I’m sticking my credit card in anything that looks like that lol. Other than that, I don’t have too much positive to say for this project or whatever.
Well, since you’re giving them access to your information either way, it boils down to the usual, “do I trust this person/party?”
So, basically serial to USB converter.
A “keyboard wedge” reader probably would have cost the same as the reader/Teensy combo, but where’s the fun in that?
As small as the Teensy board is, a slicker hack would have shortened the cable and embedded it inside the card reader, showing only the USB port.
Oops. Guess I should read the original story before posting a comment. I see a bit more parsing was needed than just the raw dump from the card.
Why was this removed from the front page?
And now it’s back again :S
And now it’s gone again. :SS
And now it’s back again :SSS. What is going on here?
@Kirby
Yeah California State IDs.
@Jayson
Along with Credit/Debit cards, security cards for buildings (HID still makes mag stripe cards), and lets not forget laundry/parking meter cards.
Just for the record, HOPE is every two years, and has already past for 2010. The wording of the post makes it seem that it is an upcoming annual event.
As for the project itself, it is clever that they put all of the required key presses in the micro code (I.E. entering Tab to switch between fields), but of course this device is now only good for this single purpose. It seems there are more elegant ways to handle mobile credit card transactions (Square?).
@carbuncle, Why not? They’re a electronics kit company that you would be handing your credit card to them anyway. If you don’t trust a business enough to use your card, then cash is the only safe option. It’s not like it’s attached to a gas pump or atm.
@MS3FGX, paying a second credit card processor is never an elegant solution.
You can buy MSR from ebay < 600$ but its kinda obvious what are these used for lulz
Why must every article instantly attract such negativity?
What’s up with all the complaining about aesthetics? Why comment that the materials cost the same or more than some fixed function, not easily modified off-the-shelf product?
Why even read Hack A Day? Really, why?
As far as hacks go, I personally think this one is pretty awesome. Not only does it give access to info that wasn’t possible with the other solution, but it customizes keystrokes so it directly manipulates a web form. How many off-the-shelf products do that?!
@MS3FGX: as to being “single purpose”, it’s easily hackable by just editing the code. Keyboard.print(…) Imagine that, hacking things!
It also uses Teensy (full disclosure, I’m the guy who designed Teensy and hacked Arduino to do non-serial devices… something that had been repeatedly called impractical and “too difficult” on the Arduino forums), so of course I think the Teensy-factor using the Arduino IDE is pretty awesome too.
@Manfire
They are paying a service fee to use the virtual credit card terminal already. This device simply saves them from typing in card information manually, it doesn’t magically allow them to process credit card transactions independently.
@Paul
Or they could have simply used the original USB HID magstripe reader and interpreted the incoming data in software PC-side, involving no modification to the reader at all. Why have to modify the firmware on the device because a field changed on the form you want to fill out? You are going to have to write parsing software either way, so why not do it on the PC where it is more easily modifiable and can work with any HID card reader on the market?
“What’s up with all the complaining about aesthetics?”
what complaining about the aesthetics? what 1 guy said it would be cooler if it were all shoved into 1 case?
sounds like your just tooting your high n mighty horn for the sole reason of starting something
not every comment is going to be “atta boy!” and if they were we would not have a reason to try harder
Pardon me if I don’t step right up to swipe my card at a hacker/tech-head conference using a home made magstripe reader.
@Paul Thanks for your work on Teensy. It’s my go-to for quick projects and what I like to recommend when someone wants to get their feet wet in embedded.
Most credit card processors offer two rates to reflect different fraud risks: 1) when the merchant has physical possession of the card and swipes it, and 2) “card not present” transactions conducted over the phone and online. The fee for processing physical cards is typically 1.5-2% of the sale price and “card not present” rates are 2.5-3.0%.
So, basically this hack allows to pay more for credit card processing than is necessary.
@Jamie: Also, Credit Card processors typically group sellers by volume, giving high-volume sellers a lower rate, like 1.5-2%, while low-volume ones a higher rate, like 2.5-3%.
Wow, personally I can’t wait until the teensy++ is back in stock, they’re going for $100 on ebay! (add http://) cgi.ebay.com/Teensy-USB-Development-Board-/260660298213?pt=LH_DefaultDomain_0&hash=item3cb09081e5
@MostofYOU There is a big difference between constructive criticism, and flaming. My last project got flamed up and down, as did the comment pages most other places I posted. I appreciate suggestions for improvment, like fitting it into a case, but on this site and others the community targeted needs to stop with all of the “dude ur dumb” type posts… nice project though!
Uh, Ladyada is a GIRL. Geeze, make better use of your pronouns.
“The real question, are his customers comfortable sliding their plastic through a hacked reader?”
earn it yourself.
Although this hack undoubtedly works, it is not compliant with the PCI Data Security Standards for virtual terminals (SAQ C-vt)