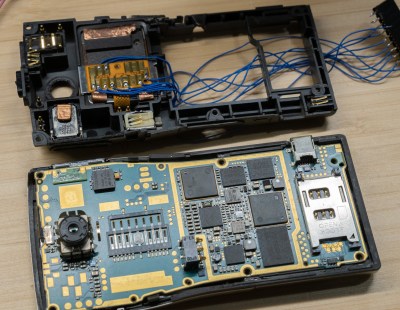
We have probably all at some point had to replace a peripheral not because it is faulty, but because it is no longer supported by our operating system. It’s especially bad for Windows users, but for older hardware this is increasingly a part of the Linux experience too. [George MacKerron] is here with what may prove to be a valuable technique to keep these devices active. He’s running a minimalist x86 computer in the browser, with just enough OS to support the device.
In this case the hardware is a USB scanner, and the resulting software takes a WebAssembly x86 emulator and adds a bit of glue software allowing it to use WebUSB to talk to the real-world hardware. It runs a minimal Alpine Linux environment with SANE — something that’s normal for Linux users but which has never been there on a Windows machine. The result is something which needs no installation, but can be run on any machine with a powerful enough web browser.
While such an approach might at first seem like overkill, we’re told it runs surprisingly quickly. In this case it’s for scanner, but we can see it could find a use with many other pieces of aged hardware.
If WebAssembly is new to you, we gave it a primer a few years ago.
Header image: Fir0002/Flagstaffotos, GFDL 1.2.