Hacker culture in Germany and the US is very similar in a lot of ways, from the relative mix of hardware versus software types to the side-affinities for amateur radio and blinkenlights. Reading Hackaday, you’ll find similar projects coming out of both countries. Both countries have seen hackerspaces bloom in the last decade to the point that there’s probably one or two in whatever city you’re living in. But there’s one thing that hackers in the USA are still lacking that German hackers have had for a while: respect.
Say the word “hacker” in different social circles, and you never know what kind of response you’re going to get. Who exactly are “hackers” anyway? Are we talking about the folks blackmailing you for your account details on Ashley Madison? Or stealing credit card numbers from Target? Or are we talking about the folks who have a good time breaking stuff and building stuff, and taking things apart to see how they work?
The discussion over who’s a “hacker” is as old as the hills, by Internet standards anyway, and it’s not going to get settled here. But think about the last time you heard the word “hacker” used in anything but its negative sense in the popular press. If you can’t remember a single instance in this century, you’re living in the USA. If you answered, “just yesterday, in one of the nation’s most important newspapers”, then you’re living in Germany.
Hackers’ Place in Society
The article that sparked me to write this (here in Google translate) is titled “Why Hackers are so Important for Society.” You know why, and I know why; because we take things apart and think about how they work on a fundamental level: from consumer electronics to encryption protocols. But imagine reading that headline in an American newspaper.
 German hackers have enough respect that the German government frequently takes testimony from representatives of the Chaos Computer Club (CCC) on matters of IT security, electronic voting machines, data freedom, and similar areas of expertise. The press, and not just the computer press, comes to the CCC when they have a story to check out. The Pirate Party, founded at the c-base hackerspace in Berlin, actually got enough votes to have representation in four German state parliaments in 2012, and a single representative in the EU parliament. While it’s certainly not the case that every German would say “hackers” are a force for good, their media presence and overall political and societal impact is orders of magnitude better than in the USA.
German hackers have enough respect that the German government frequently takes testimony from representatives of the Chaos Computer Club (CCC) on matters of IT security, electronic voting machines, data freedom, and similar areas of expertise. The press, and not just the computer press, comes to the CCC when they have a story to check out. The Pirate Party, founded at the c-base hackerspace in Berlin, actually got enough votes to have representation in four German state parliaments in 2012, and a single representative in the EU parliament. While it’s certainly not the case that every German would say “hackers” are a force for good, their media presence and overall political and societal impact is orders of magnitude better than in the USA.
How this came to pass, and what it could suggest for US hacker society, is worth thinking about. I don’t claim to have all the answers; part of this essay is an attempt to open up a dialog by comparison. But it’s important to think about why US hackers are marginalized, or why German hackers are (almost) normal members of society, especially while the views of the tech-savvy are increasingly needed in public debate.
Hacking on the Phone
The US image of a hacker is a guy, maybe even a teen-ager, working long hours alone trying to break into AT&T’s system or playing tic-tac-toe with WOPR. And in the early 1980’s, this wasn’t far wrong, except for the loner bit. There were phone phreaks hacking away to make (illegal) free phone calls. But they were often organized in crews, sharing information and working together. The Legion of Doom’s own Technical Journal, Phrack or 2600, and the free information shared on myriad BBSes of the day were anything but isolating. If you had access, they were positively inviting.
Notice what’s going on here. At the time, AT&T had a monopoly on long-distance phone calls, and the prices were anything but reasonable. In order for a bunch of like-minded technical hackers to get together and chat, or to dial up out-of-state BBSes, they almost had to break into the system. Of course, it also helped that the phone network was one of the most interesting and challenging pieces of information technology around at the time. But the common thread among the phone phreaks is that they were communicating, both as the means and the end goal.
The German hacker scene came out of very similar roots. Germany also had a phone monopoly, but was even more restrictive than AT&T in the US. In Germany, not only did you have one phone carrier, Deutsche Bundespost, but they were directly state owned and Germany’s largest employer. The Bundespost could dictate by law what phone devices you could attach to the phone lines, and this included modems which were ridiculously expensive in the early 1980s. Some of the CCC’s earliest activities were in phone phreaking against the Bundespost, which I’ll lump into the definitely-illegal-and-morally-debatable category, but also in making affordable DIY modems to enable inter-nerd communication. And although this was also illegal, I claim it’s morally alright and definitely technologically awesome.

The “Datenklo” (Google translate version) was a DIY acoustic-coupler modem that ran at 300 baud. The name is a bizarre mashup of “data” and “toilet” because the foam-rubber rings that were used in the design to insulate the phone were readily available in just the right size from the plumbing supplies section as toilet seals.)
But I digress. Early-1980s hacking in both the US and Germany were characterized by legal and not-so-legal hacking as a group effort, and was centered around a love of technological exploration and its communication both in digital and print media. Everyone was phone-phreaking against a telecom monopoly just so that they could talk together about how the phone system worked under the covers, because at the time the phone system was the coolest system going.
This is where paths begin to diverge. By the 1990’s, the American hackers were marginalized and largely separated, while the German hackers had formed a strong national organization with branches in a number of cities.
The Turn
In the US, the golden age of phone phreaking came to an end in 1990 when the US Secret Service seized many of the computers on which people were running BBSes and essentially announced open season on hackers. Most all of the phone phreaks were driven deep underground. Groups of hackers were treated as “gangs” and communicating about the internals of the phone system on a BBS was conspiracy to commit crimes rather than free speech. Hundreds of computers running suspect BBSes were impounded for months or years, even if no charges were ever brought. At the same time, the US started to enforce laws that were previously intended to protect government computers as applying to any computer on the Internet.
 In short, there was an overnight raid on hacking in the States. Hacking was criminalized, the more organized crews were disbanded, and a very few even faced jail time. Whatever community there was in the US hacking scene became, at least for a little while, muted or pushed very far underground. Bruce Sterling’s The Hacker Crackdown is the canonical chronicle of the end of the phreaking golden era, and is a great read when you have the time.
In short, there was an overnight raid on hacking in the States. Hacking was criminalized, the more organized crews were disbanded, and a very few even faced jail time. Whatever community there was in the US hacking scene became, at least for a little while, muted or pushed very far underground. Bruce Sterling’s The Hacker Crackdown is the canonical chronicle of the end of the phreaking golden era, and is a great read when you have the time.
By 1990 this description of hackers in a 1981 New York Times article was painfully dated:
Hackers are technical experts; skilled, often young, computer programmers, who almost whimsically probe the defenses of a computer system, searching out the limits and the possibilities of the machine. Despite their seemingly subversive role, hackers are a recognized asset in the computer industry, often highly prized.
Public sentiment was already being pushed to recognize hackers as deviants or criminals.
L0pht Heavy Industries
 But hackers gotta hack, and the large geographically-distributed assemblages gave way to more local scenes. L0pht was one of the most visible hacker groups in the US in the 1990s. The actual “l0pht” in question was the archetypical hackerspace: full of junk (ahem, inspirational technological raw material) and computers and smart folks interested in all of the above. Early on, L0pht got a bunch of good press, for instance this article in the New York Times.
But hackers gotta hack, and the large geographically-distributed assemblages gave way to more local scenes. L0pht was one of the most visible hacker groups in the US in the 1990s. The actual “l0pht” in question was the archetypical hackerspace: full of junk (ahem, inspirational technological raw material) and computers and smart folks interested in all of the above. Early on, L0pht got a bunch of good press, for instance this article in the New York Times.
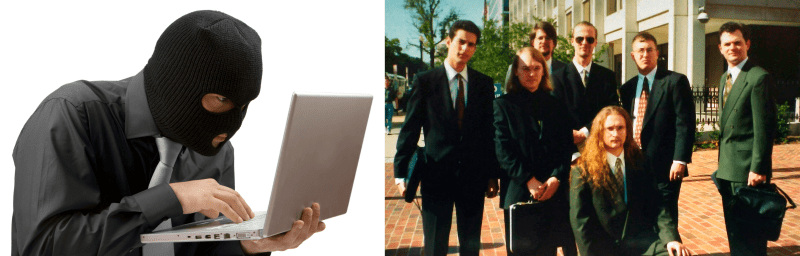
And at perhaps the high point of US hacker-government relations we saw a crew of seven from L0pht testifying in front of the US Senate on the relevance of hacking to US state security. Senator Fred Thompson introduced them as a “hacker think-tank” to his fellow Senators in an effort to soften the blow. Interestingly, the beginnings of the L0pht’s involvement with the government was a defensive maneouver by Mudge aimed at raising their profile and avoiding any misunderstandings, which is to say not getting raided.
The folks from L0pht would eventually become early advocates of full disclosure, whether responsible or otherwise. Their advisories were a must-read for anyone interested in hacking or computer security during the 1990s. While perhaps not everything that went on at L0pht was strictly legal, it’s pretty clear that their hearts were in the right place: somewhere between chaotic neutral and chaotic good. The Washington Post ran a good article on L0pht recently that should also be on your reading list.
What I think matters about L0pht, though, is that they became a visible group, and that they were much more motivated by a desire to get broken stuff fixed. Because of their high public profile, they knew they were being watched, and there was an incentive to “behave” or at least to appear to be behaving. They got flack from both the black-hat hacker community for having “sold out” and from the software industry for being rogues — a sign that they got the balance right. Moreover, they had a purpose, and they were organized.
And then L0pht stopped being a hackerspace and moved into the security industry, and its members grew apart over business differences. In a way, the end of L0pht parallels the business-ification of hacking throughout the US — or the growth of the security industry, depending on your vantage point. In a post-1990 US, “hacking” doesn’t sell well in the boardroom, and the dichotomy between the white-hat hackers (ahem, “security researchers”) and the black hats has grown very stark. With high salaries on one side, and a changing legal environment on the other, there’s little room for anything in-between like the L0pht any more. This is a dangerous hole in US hacker culture, especially for the younger folks who aren’t yet old enough to put on a suit but who like to play with computers. Where do they fit in?
Today the USA, Tomorrow Germany
Hacking in the USA has followed a long and winding road from being open and community-driven, to going fully underground, with a few exceptional groups in the public eye. Tomorrow, I’ll go back to the 1980s and replay an alternate history from the German perspective and argue that the US hacking scene can stand to learn a bit from the comparison. If you buy this argument, then there’s a lot of work to do in US hackerspaces. Stay tuned!
















This seems to be a problem of semantics as much as of culture and history.
“Makers” substitutes well for “hackers” in the constructive sense, even though it’s become a twee term in the press – mostly used to hustle crap 3D printers and hipster “builds” (are you watching, Pettis?). Makerspaces may help correct this a bit as well.
That said, stay the course…this place is doing fine (so far) – I hope HAD *never* becomes MAD.
Makers is definitely a different thing. It’s not risky to assume that the original phone phreakers and L0pht members don’t self identify as Makers. These are definitely hackers in the sense of the term that they’re looking for uses for technology in ways it was not originally intended. The term Makers doesn’t apply to this definition.
Makers make things. That’s only half of hacking. Hackers is take things apart, find out how it works, put it back together (after tweaking it, maybe making it better) and then they make other things with the knowledge.
If you wanted to use another word, I think ‘tinkerer’ would be better than ‘maker’.
My view of “hackers” is as people who take things apart (whether that be hardware, software or whatever else) and re-use things in ways not necessarily intended by their creator.
Someone who uses flat pack furniture parts to build something other than what the instructions say could be considered a hacker (witness the “IKEA hackers” website dedicated to exactly that). Someone who pulls computer software apart to figure out how it works and change the software in ways not intended by its creators could be considered a hacker. (I have been doing exactly this sort of reverse engineering of software for years). Someone who obtains an old payphone and tears it apart to reuse the parts could be considered a hacker (I visited a hackerspace here in Brisbane recently and someone there had an old Telstra Gold Payphone sitting there).
I started blueboxing in 1986 after learning about it at the Canada Wide Science Fair.
I agree with Mike as I would never identify myself aa a maker.
ST
That’s surprising since by 1986 it was rather difficult to find a trunkable line.
I found it pretty easy. At that time many US toll-free numbers did not work in Canada. “The number you have dialed cannot be reached from your calling area”. Even in 1988 there were no problems using it. There was a revolving door on my dorm room with all the friends coming to make free calls.
That’s really not true at all, unless you are talking strictly about inside the US to inside the US. There were still Step switches in certain parts of Africa even into the 2000s, for example. Yeah you’d probably need to know where to look in the US in the 80s but it wasn’t terribly difficult. Especially since phreaks tended to share a lot more than ‘hackers’. Heck, LOD wasn’t even LOD — it was LOD/H; probably the biggest cross-pollination at the time. Many if not most phreaks in the 80s didn’t have much in the way of computer skills (and vice-versa). pnce you get into the late 80s is really when that became more common (and into the 90s). By the early to mid 2000s, with PATRIOT act and more laws plus a lot of reunification and telco mergers and heavy implementation of stuff like securID and the implementation forst of x25 over ip then more or less the death of telco as pstn (packet switched ntwk) and engressia dying, so too phreaking.
The other major difference is size of country. It’s amazing to me that the USA is viewed as a monolithic culture, when some states are huge. http://ak-hdl.buzzfed.com/static/enhanced/webdr02/2012/11/16/17/enhanced-buzz-wide-28632-1353103917-7.jpg compares Texas, the second biggest state, to mainland Europe.
Even if one state the size of Germany did view hackers in a better light, they are surrounded by news media and a government that has their own agendas. The government had funded AT&T (if using tax money to pay for the copper phone lines isn’t “funding a company” in the most round-about way possible) in return for getting the usual donations and heads up on stock tips; you can’t convince me that the federal government couldn’t spot a monopoly, that they created, until 1974, or that letting it stay together for 8 more years didn’t serve some purpose.
They paid for it because they needed it for national defense. It was all part of the SAGE communication system for SAC and NORAD. Teletype and secure land line were the basis of the whole system – except submarines. Unlike England, Europe, and Japan and China, where it was all destroyed in the 1940’s and rebuilt in the 1950’s, the U.S. had telecom tech dating back to the 1890’s that was “good enough” for voice. Manual switch boards were in plenty of small towns into the 50’s and early 60’s. At the time, a hack was calling a store and asking of they had Prince Albert in the can.
When talking about people you should compare on population size, not land size.
I think we are talking about how far you have to run wires.
Population size has an effect, but the large distances involved in the USA means that the culture of big cities like New York and San Francisco are vastly different. If those cities were closer, topography not withstanding, they would be much more similar in mindset, goals, and culture. But it isn’t.
Comparing the USA to a country in Europe just doesn’t work that well; unless you only focus on the federal government level. The USA was a prototype of the EU, separate country-states governed by a joint federated system. Over time, we just gave that federal government more power than the states.
U.S hacking begins with thieves like Cap’n Crunch and “revolutionaries” who were liberating other peoples data with an ideology that all information should be free. They also caused the need for system security, which can be seen as a good thing, but inspired viruses as both a way to steal information and a way to cause damage.
So yes, the word “hacker” began with a very negative meaning in the US. I recall being surprised when it was reborn as a synonym of readers of Popular Electronics along with the odd usage of “maker” for home shop enthusiasts or what would.
Is it like everyone gets a ribbon? No one wants to be called an amateur anymore? How about Pro-Am woodworker? And nouning a verb to get the usage of “build”. Phooey! You kids get off my lawn :-)
In what universe is Captain Crunch a “thief”? At best he was thrown under the bus by the US government in the 70’s for ostensibly doing very little other than probing AT&T’s phone networks at the time. By all accounts, his phone phreaking ultimately amounted to just trying to see how many long-distance networks he could jump across.
The worst thing that he did – and I don’t even think it’s particularly bad – was prank-calling Nixon and telling him the CIA was out of toilet paper.
Don’t get me wrong, the things he was doing were certainly illegal back in the day, but I’ve hung out with him for the better part of a week, and we talked at length. He’s about as harmless as a marshmallow. A bit of a curmudgeon, and can border on slightly creepy at times, but harmless nonetheless.
“He’s about as harmless as a marshmallow.” – Never seen Ghostbusters?
Well, he spent many hours talking to me from Hawaii when long distance was not cheap, usually late at night west coast time with a complaint about one Forth compiler of another. Then wake me up again to say never mind, he read the docs wrong. You are framing his actions in today’s reality, when probing about the internet is nearly free. He was using and spreading the info on how to use, phone system control frequencies to disable long distance billing. You could cut down a Cap’n Crunch serial box whistle to get the duo-tone needed, thus his hacker moniker. There is not doubt it was theft. Theft is bad. Theft is at its root, taking a portion of someone else’s life’s work that they can never get back.
And how is “probing” a private network not trespassing?
I think the best part, is that after all these years, you still seem salty about being called by Cap’n Crunch. Sure that sounds really annoying back at the time (no seriously, for hours? argh), but you don’t seem to be one to look back on it now and laugh at the absurdity of it.
And your generation would have been the one making the laws at the time.
No wonder phreaking and then hacking became criminal in the U.S.
“Hacker” predates Cap’n Crunch by a while (and he is certainly a phreak). I think people go with the MIT model railroad (later computer) club on this one. And it was most definitely positive. http://blog.oxforddictionaries.com/2011/07/hacker-is-a-badge-of-honour/ for instance.
“Maker” in the sense that you mean it was coined in recent memory by a company whose name is strangely similar, and whose magazine we’ve probably all read.
“Tinkerer” is good by me for the non-computer types.
I had a few buddies back in the early 90s that were leaning toward the dark side, and they had a lot of interesting stories to tell. I never jumped on board with them, but I spent enough time around them to have a fairly good idea of what they were up to.
Those were interesting times, when the word “hacker” had no possible good connotation at all here in the US. I’m glad that things are starting to turn around, at least a bit. If the “makers” want to be associated with us hackers, I’m okay with that. It provides a possible way for the general public to see our community in a better light.
This is a fantastic image. My compliments to your artist.
Hackers in big corporations: people who like to code things up quickly – instead of sitting in long design meetings requiring hours and hours of definition and hordes of other engineers constantly reviewing. Its not a positive thing when judged by a group – but a good one is highly appreciated on an individual basis.
I love how no actual changes in the letter of the law were required to turn harmless hobbyists into criminals. All you need is to convince a bunch of police officers and judges to interpret the existing rules from a little different angle… What could possibly go wrong?
+1
Just short side about the CCC representatives being invited to comment on things in the Bundestag.
This does not anyone in the government would actually listen to us hackers.
Usually it’s more about hearing all opinions so that everyone can feel included in the process.
Also this way the press can’t claim that the politicians didn’t talk to experts.
This may be true, and I’m on weaker footing arguing about the German scene than I am about the US scene (through which Ilived).
The German press, at least to a semi-outsider, seems to be surprisingly on the side of hackers, and they _do_ matter to public opinion. Bringing hacker issues up in a public forum is a big win. Whether or not the politicians listen is of course the next step.
Just to correct the little error that the pirate party was founded in germany:
https://en.wikipedia.org/wiki/Pirate_Party
it was actually first started in Sweden and had 2 representatives from Sweden in the European parliament for a while.
For sure. The Swedish Pirates were first. But the German Pirate Party (Piratenpartei Deutschland) was most definitely founded in Germany. :) And more importantly, in c-base.
Free Mitnick
He’s free, doing the American thing, cashing in on his fame:
http://speaking.com/speakers/kevin-mitnick/
Great article! Thanks man!
Whatever happened to calling the people up to no good with computer and phone technology, “crackers”? Cracking open secure computers, writing cracks to use software for free. Cracking their way into a credit card database to steal money. Like good old safe cracking, but applied to other mediums, with the intent to steal stuff that has value – without consideration for causing damage.
The problem with that is most people think that it takes a hacker to do the cracking.
There are definitely people who steal property and commit credit card fraud. Calling these people “crackers” instead of criminals is doing them a favor.
But you described three very different things: breaking into a computer system (“unauthorized access”), breaking copyright protection (which can be legal or not), and stealing credit card numbers (the selling or use of which is certainly illegal). That’s a wide range of activities, and very different “crimes” to put under a single name.
The thing that’s always bugged me (personally) about the cracker moniker is that it’s focusing on the means that they use to commit their crimes rather than the crimes themselves. This becomes a problem when other people use the same means for non-criminal ends. (Metasploit for security analysis, etc.)
So “meh” to “crackers”. But I know what you mean.
I travel as part of my job and I found (once they first turned it on) that the free Qantas-Club wifi that was offered had hackaday on its blacklist, simply because of the word “hack” in the title.
A quick email to the support team for the free wifi sorted out the kerfuffle and they white-listed this webpage, but it was still sad that even on a guest wifi network that the “hacking” term was dangerous enough to warrant blacklisting a webpage that is simply about understanding how things work.
Yeah. There’s a lot of censors that choke on the word. (And thanks for getting that cleared up!)
About the only good thing I can say about “lifehacks” is that they’re helping us a little bit with this problem. Every time someone thinks that waking up early in the morning is “hacking their biology” or whatever, a poorly-designed censor filter is retrained.
This article brought back a lot of memories from high school. Back then it was extremely hard to find anyone with the same passion for computers and the phone system. Even “computer classes” were mostly limited to typing and using Clarisworks. How boring it was, but oh so much fun I had coming back home and finally connecting to a BBS in the U.S. and read all those text files on assembly programming, or reading about the Nortel Centurion payphone and all the different boxes out there. Fortunately back then, at least in my area, nobody would know anything about hacking or phreaking, so it was easy to get a copy of the latest 2600 and was fortunate enough to have a meeting in my city. A guess those were a bit a precursor to the current hackerspaces we have nowadays. Interestingly, while I may have been labelled a hacker back then, despite the only hacks ever done was bypassing Winlogon on the school’s network and accessing some Wingates, the chain of events resulting for these experience resulted in a much different view of technology than many of my colleagues who followed the “security training” offered by the plentora of vendors nowadays. Call them whatever you want in any country, skills developed by hackers, tinkerers, makers, phreakers and what not, are now in high demand by the same entities that were doing the witch hunts 20 years ago for. I guess Germany just realized the potential before others. Good article.
Is it weird that my experience of free long distance calls was called “tapping” ? Literally you would tap out the number you wanted to dial using the phone hook. 1 very rapid hangup and pickup if 1 was the number … 9 for if the number was 9 and 10 if the number was 0. It used to only work on really really old analogue pay phones, but it did work through most of the 80’s and 90’s if you could find a rotary payphone in the back end of nowhere. The older the phone the better the odds of it working.
Congratulations, you discovered old phones used pulse dialing because they predated tone dialing. You can still dial a number this way on most landlines ;)
I know this: living with and hacking with members of l0pht and cDc was fun, interesting, enriching, and beneficial for my self, life, and career. Whether or not the general U.S. Public appreciates the American hacker phenomenon, I sure as hell do. Never stop learning and exploring. Teach your kids to hack.
I wonder if things in the us would be different had hackers not been blamed for ma bell’s crappy coding causing a serious outage.
timing. the early 90s gave us CALEA and the first staunch hacking laws thatt didnt arise from that but it didnt help either. add to that tht it was theitnick/paulsen/groups heydey and people were generally ignorant about all tech in general (not that todays so-called power users understand how things work) and bascally you had a perfect storm. wouldve happened sooner or later.
Is it just me or does anyone else find it really funny how most “hacker” stock photos feature a dude wearing a balaclava lol.