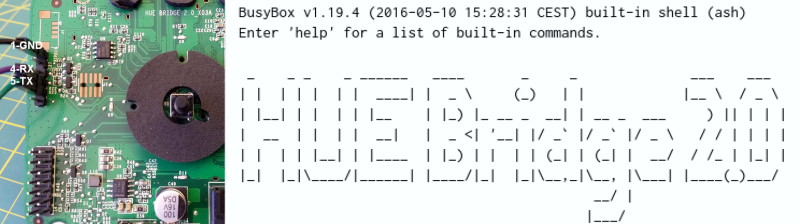
Building on the work of others (as is always the case!) [pepe2k] managed to get root access on the Philips Hue Bridge v2 IoT light controller. There’s nothing unusual here, really. Connect to the device over serial, interrupt the boot process, boot up open firmware, dump the existing firmware, and work the hacker magic from there.
Of course, the details are the real story. Philips had set U-Boot to boot the firmware from flash in zero seconds, not allowing [pepe2k] much time to interrupt it. So he desoldered the flash, giving him all the time in the world, and allowing him to change the boot delay. Resoldering the flash and loading up his own system let him dump the firmware.
The “hacker magic” glossed over in the intro consisted of poking around until he found a script that was called on every boot. This is how [pepe2k] gets around not knowing the root password. The script compares the hash of the typed password with an environment variable, set with the hash of the correct password. Changing that environment variable to the hash of his favorite password (“root”) made him master of the box.
And just in case you’re one of the few Hackaday readers who doesn’t understand why we do these things, besides the fact that it’s just fun, consider Philips’ (eventually retracted) clampdown on the interoperability of this very device, or Google’s red bricks. The fatal flaw of IoT devices is that they place you at the whims of companies who may decide that they’re not making enough money any more, and shut them down. Keep your hacking skills sharp.
Thanks [Jan] for the great tip!
















As a hue user, I feel slightly comforted that you need some physical access to make this happen.
That being said, I wonder what new and lovely attack vectors we’ll learn about now that we’re under the hood ;-)
I wonder what GPL violations we’ll find.
None. Philips, at least their TV division (before the sell) has a menu with all the licenses and software used.
until someone finds a collision for that hash in the environment variable perhaps ..
The physical access is the thing. This is absolutely a you-own-the-box-that-you-own hack, and not a remote exploit. It’s a good deed. As a Hue user, you should be stoked! Now you can play. :)
Your second point is unfortunately also right on. Botnets of lightbulbs. Shudder.
I don’t know if any GPL violations will be found but some credit goes to Philips for at least making it easy to get a broad overview of used open source as the only web page the hue hub displays to the user.
This is what the current firmware shows:
Welcome to hue – your personal wireless lighting system. For more information please see our website http://www.meethue.com
Open Source
hue statically links towards unmodified open source software libraries in the bridge software. For instance, we make use of a real time operating system called FreeRTOS which is distributed under a modified GPL license and an open source IP stack called lwip distributed under a BSD license. Links towards all license terms and sources are available below.
FreeRTOS v7.4.2
Website: http://www.freertos.org
License: freertos_license.txt
lwIP v1.4.1
Website: http://savannah.nongnu.org/projects/lwip/
License: lwip_license.txt
SHA-1
Website: http://www.packetizer.com/security/sha1/
License: sha_license.txt
OpenSSL AES Encryption
Website: https://www.openssl.org/docs/apps/enc.html
License: aesenc_license.txt
JSON_checker
Website: http://www.json.org/JSON_checker/
License: jsonchecker_license.txt
UTF-8 Decoder
Website: http://bjoern.hoehrmann.de/utf-8/decoder/dfa
License: utf8decoder_license.txt
Did something similar but easier with the nanoleaf smarter hub. Soldered the UART header, and exposed a shell with busybox nc and mkfifo. Haven’t carried about cracking it’s MD5 hashed root pwd yet.
The fact that Hue doesn’t provide an open interface for hacking/access to the device is the main reason I have not (and will not until they do) purchased any Hue devices.
Although these hacks are a good deed in service of those who have purchased such products, I believe that we should start discouraging people from buying products encumbered this way in the first place.
There are lots of IoT products out there these days that I would like to have, but I’m at a point where I am avoiding purchases of most products that don’t provide at least a local API for me to interact with the device directly. I encourage others to reject this idea that you have to purchase a device which you don’t actually own from a software perspective. Let’s face it, you don’t actually own it if you can’t pwn it.
While it’s not well documented, the hue does have a REST API I’ve been using for years that works just fine locally on my Lan. A little cron and PHP shuts off my lights every morning at 10a if I forget to turn them off before hustling out the door for work.
I am also using the Hue API with openhab and it works great