There are a few old Capcom arcade titles – Pang, Cadillacs and Dinosaurs, and Block Block – that are unlike anything else ever seen in the world of coin-ops. They’re old, yes, but what makes these titles exceptional is the CPU they run on. The brains in the hardware of these games is a Kabuki, a Z80 CPU that had a few extra security features. why would Capcom produce such a thing? To combat bootleggers that would copy and reproduce arcade games without royalties going to the original publisher. It’s an interesting part of arcade history, but also a problem for curators: this security has killed a number of arcade machines, leading [Eduardo] to reverse engineering and document the Kabuki in full detail.
While the normal Z80 CPU had a pin specifically dedicated to refreshing DRAM, the Kabuki repurposed this pin for the security functions on the chip. With this pin low, the Kabuki was a standard Z80. When the pin was pulled high, it served as a power supply input for the security features. The security – just a few bits saved in memory – was battery backed, and once this battery was disconnected, the chip would fail, killing the game.
Plugging Kabuki into an old Amstrad CPC 6128 without the security pin pulled high allowed [Eduardo] to test all the Z80 instructions, and with that no surprises were found; the Kabuki is fully compatible with every other Z80 on the planet. Determining how Kabuki works with that special security pin pulled high is a more difficult task, but the Mame team has it nailed down.
The security system inside Kabuki works through a series of bitswaps, circular shifts, XORs, each translation different if the byte is an opcode or data. The process of encoding and decoding the security in Kabuki is well understood, but [Eduardo] had a few unanswered questions. What happens after Kabuki lost power and the memory contents – especially the bitswap, address, and XOR keys – vanished? How was the Kabuki programmed in the factory? Is it possible to reprogram these security keys, allowing one Kabuki to play games it wasn’t manufactured for?
[Eduardo] figured being able to encrypt new, valid code was the first step to running code encrypted with different keys. To test this theory, he wrote a simple ‘Hello World’ for the Capcom hardware that worked perfectly under Mame. While the demo worked perfectly under Mame, it didn’t work when burned onto a EPROM and put into real Capcom hardware.
That’s where this story ends, at least for the time being. The new, encrypted code is valid, Mame runs the encrypted code, but until [Eduardo] or someone else can figure out any additional configuration settings inside the Kabuki, this project is dead in the track. [Eduardo] will be back some time next week tearing the Kabuki apart again, trying to unravel the mysteries of what makes this processor work.

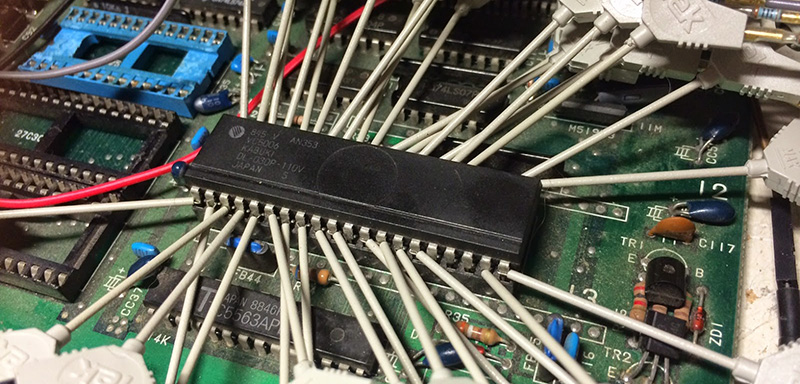














I always find spider wiring like that interesting. Point to point, banana clips, electrical taped wire to a pin… Definitely the start of a good hack :D
They’re test clips on the logic analyser probes. You squeeze the block that says Tek and a little tweezer like mechanism will extend from the end so you can clip it onto IC legs or other components. They’re not soldered on.
Some of these old arcade boards did some funny things. Some of them attempted to obstruficate the code by switching around data and/or address pins. I saw one that was a complex state machine that had no CPU, only SSI registers instead of RAM and heaps of ROM. That was fairly mind blowing at the time but RAM was expensive then.
Swapping address or data pins to RAM has no effect as long as the bus widths match. It doesn’t matter where the 1 or 0 goes as long as it’s in the same place when the CPU comes looking for it again. The same can be done with ROM but the original code must be swapped around to match the hardware swapping. There was a lot of this in simple devices where it helped to fit something on a single sided PCB.
I figured out the bit swapping on data and address lines very nearly all the way back to my first board supporting RAM. I think I did it the first time I used my shift registers.
It always interests me when people are surprised when this does happen on a board. Why deal with a multi sided board, vias and jumpers just to keep the bit arrangement “logical” to their assignment instead of just arranging things more conveniently. Not like the “RANDOM ACCESS MEMORY” cares what order you access each address.
I just love how well the MAME Kabuki source code is commented.
This CPU should have been named Seppuku.
where’s the like button???
kudos!
MUAHAHAHAHAHAHAHAHAHAHAHAHAHAHAHAHAHAH!!!
+10e6
This was figured out year ago. This is a Z80 cpu IC with some decoding hocus pokus. so you get the decoded roms and put a real Z80 in its place. I been repairing old arcade games for 30 years. This is not a new thing.
Wish you’d of read the hyperlinked article before blatantly dismissing someone else’s work…
“This blog post is the first one in a series of Kabuki articles that will analyze this security cpu in full detail, and share my research work and findings that successfully allowed me to reverse engineer this cpu and bring any dead Kabuki games back to life unmodified. “
i think miss his point. He’ s not trying to run modified code on different chip. He wants to resuscitate and reuse the kabuki with unmodified code.
Above was supposed to be YEARS ago.
suicide battery was common in some old arcade. Not just with kabuki chip but a few other arcade board design as well. Capcom and Sega for example used them in late 80’s and 90’s.
Especially military electronics.
but how does this work, I mean what was supposed to happen when the battery died? The guys sold you a very expensive device and told you : well in 3 years it will be dead… ? What was the commercial deal here? was it because they billed a huge fees to have it repaired then? and if the cpu cant “live” without an eternal battery it means the whole card or the whole machine has to be send to the manufacturer.. Because if a repaired guy from the compagny comes to change the batterie After it already died..how can he have cpu with batteries connected with him..shouldnt they had some special portable device and special port to connect that device to “program” on site a new cpu ?
The manufacturers weren’t trying screw the machine operators. It was the code bootleggers that they were focused on so I would imagine the manual clearly stated all the issues with the battery. With early machines, the manufacturers had profit share arrangements with operators so it wasn’t in their interest to let batteries die.
These machined got an incredible amount of use so maintenance was an ongoing thing for operators. It would not have been hard to the operators to keep an eye on the battery voltage during routine maintenance.
If a battery (board) did die then I would imagine that it would have had to go to the closest authorized agent or the manufacturer. They would not have let the code programmer into the field. It surely would have been well guarded.
hum oki. thanks for your answer.:)
i had a suicide mp3 player from the late 90’s,
i think, with 250mb of storage.
main power was a AAA battery.
when it died i opened it up to find
a tiny watch battery holding onto the program
(andor the whole entire memory?)
and when this died the unit was dead as a doornail.
the tiny 1.5v watch battery was reading less then 1v
and the program was lost forever.
BRICKED … back before DFU failsafes.
thankfully i have saved a device from suicide in the past,
one a little more ***EXPENSIVE*** and ***HARD-TO-FIND***
PS: a grounded soldering iron is grounded
PPS: a non-grounded with control(cheapdimmer)
has plenty of highvoltage (low current) RF noise coming out of it
PPPS: an ungrounded soldering iron that was originally grounded
is a true death hazard
all that PPSing was in reference to
“just solder it while it’s on”
may destroy entire machine!
or get you killed! (ect)
it is better to disconnect ALL cables and then parallel
a temporary battery, desolder the used battery,
then solder in new battery and desolder temp battery.
not all computer software in available on the internet,
esp the operating software for a 5000$ machine from the 80’s
Or use an isolation transformer.
Main screen turn on
You can solder live wires with a butane soldering iron.
This video came out just yesterday, very timely :)
http://www.youtube.com/watch?v=LiRIc0LDlu4
I’m just going to leave this here:
http://cps2shock.emu-france.info/
Cps2 stuff is old news. They are currently working on cps3 stuff.
Good thing this isn’t about CPS2 stuff then, and is about a specific security method used on CPS1 and prior boards, you complete fuckwit. Go back to shit-posting on MAMEWorld, or better yet, stop posting at all.
So much douchery over a simple article. It’s saddening. WTF?
I didn’t know any of this, so thanks from someone coming late to the party.