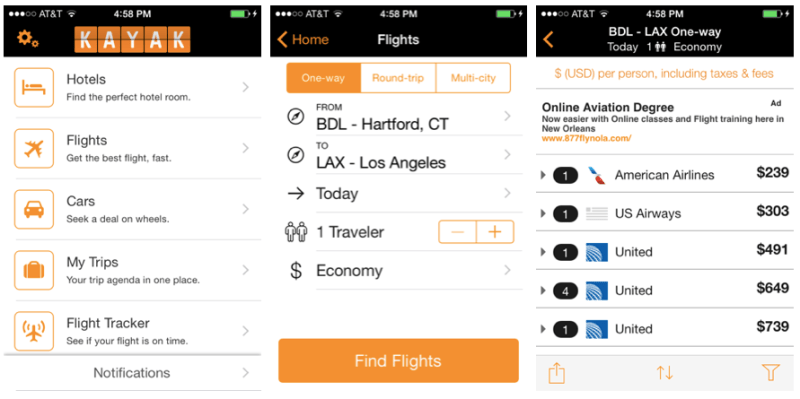
The travel meta-search website Kayak apparently used to have a public API which is no longer available. We can’t say we mourn the loss of the interface we’d never known about. If you are someone who was automating their searches for that perfect vacation getaway deal, there’s still hope. But either way you’ll like this one. [Shubhro Saha] figured out how to access the API used by the Kayak mobile app. We like that he details how to sniff the traffic between an app and the internet and make sense of what is found.
His tool of choice is the Python package Mitmproxy. We haven’t heard of it but we have heard of Wireshark and [Shabhro] makes the case that Mitmproxy is superior for this application. As the name suggests, you set it up on your computer and use that box’s IP as the proxy connection for your phone. After using the app for a bit, there is enough data to start deconstructing what’s going on between the app and remote server which which it communicates. We could have a lot of fun with this, like seeing what info those free apps are sending home, or looking for security flaws in your own creations.
[Thanks Juan via Twitter]















From what I can tell MTIMProxy is a bit more focused than Wireshark. Wireshark is the ‘inhale everything’ monitoring system. Sometimes this is a good thing (like debugging your custom UDP app). But MTIMProxy looks (from their website) to target just HTTP sessions. This allows this sort of tracing to occur and find some interesting things like [Shabhro] did.
I wouldn’t be surprised if Kayak pushed out a small change soon to change the communications to HTTPS. Bit surprised they didn’t do that in the first place.
Well I skimmed that article to quickly. Looks like they DO have HTTPS enabled. But the author is somehow able to install a new certificate that fools the client app into thinking it was secured. So is there anyway in an app to do a certificate check on the connection and only communicate if it is the server’s cert? I assume most developers don’t do certificate checking and just go with the HTTPS as is.
Oh and it’s MITM not MTIM (stupid morning brain).
Not a super new idea (and see ‘SSL pinning’):
http://nickfishman.com/post/50557873036/reverse-engineering-native-apps-by-intercepting-network
Ah. Wondered how they could do that. This might become important for the company I am working for. They are talking native app development at some point and we may want to do this. The article you linked has an interesting read on that SSL Pinning:
http://blog.lumberlabs.com/2012/04/why-app-developers-should-care-about.html
Seems you didn’t read the article. It explains how to install a certificate for mitmproxy to allow for sniffing HTTPS traffic as well. Something that wireshark can’t do easily (unless you have the certificates of client/server, which in this case Saha has neither).
mitmproxy provides its own CA certificate that you manually install on the phone. Since the OS libraries are handling all the proxying and certificate work, the app never sees that it is working with a bogus connection. I’ve always wondered how to do that – there are several APIs that I’ve been meaning to figure out.
I think this might be a good application for Charles Proxy!
A great HTTP(s) MITM proxy is in the Burp security suite
http://portswigger.net/burp/