You are at the corner store, buying gum. The cashier rings up the purchase, showing you the amount. You casually pull out your cell phone and wave it near the credit card machine, which beeps appreciatively. The cashier nods, and you walk out, stuffing gum into your face. What just happened? You used Near Field Communications (NFC) to send data between your phone and the credit card terminal.
NFC is a standard that allows two devices to exchange information over a short distance without being in physical contact. The two devices communicate using a weak magnetic field that, in theory, only has a range of a few centimeters, so both devices have to be physically close, and someone standing nearby can’t intercept or alter the signal.
NFC transceivers are now being built into many mobile devices including the iPhone and iWatch, and the technology underlies touchless payment systems like Apple Pay and Android Pay. It has had a rocky evolution, though, going from toy-store curiosity to the mainstream of the mobile world. The technology evolved from the older Radio Frequency ID (RFID) system that was developed for making keys for electronic access systems. Unlike RFID systems, NFC communications can work both ways, and the devices can be written to.
NFC Origin and Basics
The first device to use an early version of NFC was a Star Wars toy from 1997, which used an early version of the technology called CommTech to give voice to the figures. You tap the chip on the player, and it plays the voice. These are now quite collectible.
The full NFC standard was defined in 2002, as ISO standard number 14443. Since then, the standards have been expanded by the NFC Forum, an industry group set up by the companies that use it.
There are two sides to every conversation, and NFC is no different. This conversation has two modes: passive or active. In the passive mode, one device emits a rapidly alternating magnetic field. This is picked up by the other device, which is a passive device that just receives: it doesn’t emit a magnetic field. This effectively turns the two devices into an air-gap transformer, with induction causing a current to flow in the antenna of the passive device. By altering the resistance of the antenna, the passive device can modulate the field, signalling back to the active device. This doesn’t require a battery in the passive device: it draws the power it needs from the induced current. This is the type of connection you will see between a card reader and a transit card, such as the Charlie Card system in Boston or the Oyster card in London.
In an active connection, both devices can emit a magnetic field, and they alternate between sending and receiving the magnetic field. This is typically used between two computers, or between two other battery-powered devices that want to exchange larger amounts of data.
Either way, this magnetic field is alternating at a frequency of 13.56MHz, right in the unlicensed Industrial, Scientific and Medical (ISM) band, which means that there is no licence required to use. The active device still requires FCC approval in the USA, though: you can’t just build your own active NFC reader and sell it without that approval.
Data Encoding
The data is sent using Amplitude Shift Keying with Manchester or Miller coding at a speed of 106, 212 or 426 kilobits per second, with each direction using a different speed. That way, data can be sent in both directions at the same time without colliding.
Once the two devices have figured out how to talk to each other, they have to decide what to say. There are three operating modes that can be used: Read/Write, Peer-To-Peer and Card Emulation. The first is used when a reader wants to read data from a card and then write something back, such as reading data off a transit card, and then writing back the new stored fare value.
In Peer-to-Peer, both devices are sending and receiving data. One example of this is when a cell phone and Bluetooth speaker use NFC to exchange data on how to pair for the Bluetooth connection.
In Card Emulation, the device pretends to be a dumb, unpowered NFC card, even if it is a powerful cell phone. The latter is used by the iPhone for Apple Pay, because the iPhone never knows the credit card number: that is held in an encrypted format in a secure location (called the Secure Element) on the NFC chip itself. Google uses a slightly different approach called Host Card Emulation, where the card details are encrypted by Google and held in the cloud, not on the NFC chip.
How to Use NFC
As I noted before, you probably already have an NFC device built into your cell phone. Accessing that is harder than you might think, unfortunately, as some manufacturers don’t allow you the hardware level access that this needs. Android offers the best support, allowing you to do basics like read NDEF tags, or more advanced things like sending large files over an NFC connection through the Android SDK on a device that includes NFC. Apple phones are less co-operative, though, as Apple does not provide access to the NFC capability in the current version of the SDK. In effect, only Apple apps (such as their own ApplePay system) will get access to the NFC system. It remains to be seen if this will continue in future versions of the iOS operating system, but I wouldn’t hold my breath: the current beta version of iOS 9.1 does not include this. Plus, it seems that the NFC chip on current Apple devices can only act as a passive device (like an NFC access card), which means it could not read other passive NFC cards and devices itself.
https://www.youtube.com/watch?v=bp2g9F7ousY
If you want to really get into the technical weeds of NFC, you’ll need to pick up an NFC development kit. Adafruit offers a nice NFC breakout board that can be easily connected to a Raspberry Pi or other type of computer using the Libnfc library. This handles the coding/decoding of the radio signal, while still allowing you to poke around. Other dev kits are offered by the manufacturers of the chips that cell phones and other devices use, including Texas Instruments, NXP and others.
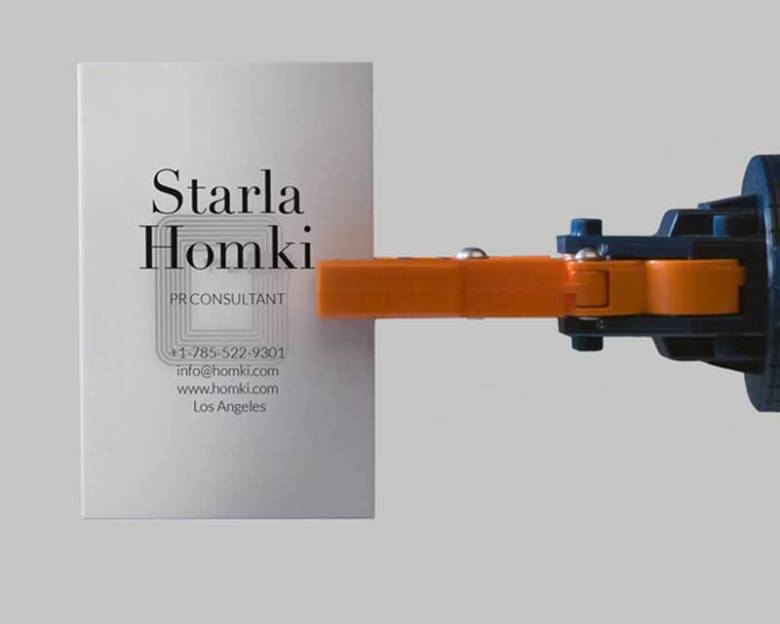
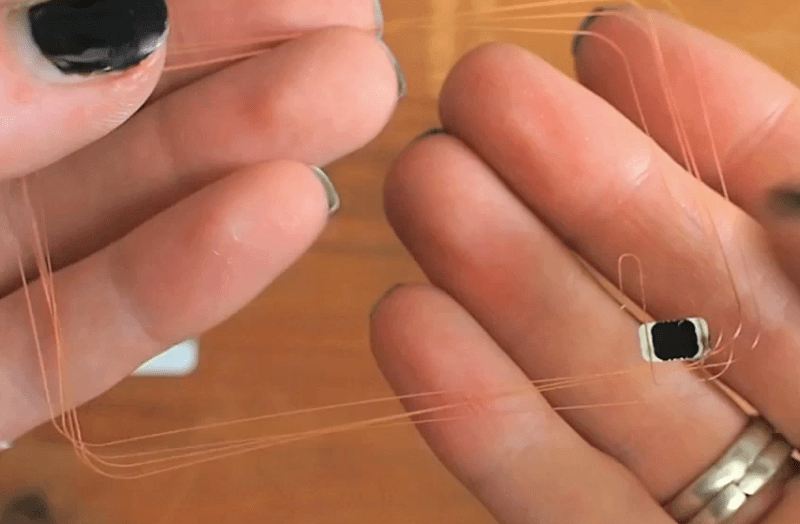
One interesting way to get hold of NFC cards is from Moo, who are now offering NFC-equipped business cards. They are calling this idea Paper+, and have some interesting ideas for it. These are more expensive than normal cards (at 20 cards for $30), but they have a significant nerdy appeal to them…
Top image: NFC Charliecard exposed, from Adafruit CC-BY-SA















STM also makes an NFC kit for the Nucleo .
http://www.st.com/web/en/catalog/tools/PF260759
I wonder how many bad implementations will be responsible for skimming and credit card fraud.
Which is one reason banks in the USA have now shuffled all responsibility for fraud protection to the merchant to cover instead, citing this as one of the reasons. This means in the near future you will have to get help from the merchants where you “think” you may have been skimmed or had your info stolen, and your issuing bank is going to laugh at you. One more reason to avoid credit cards.
Or just stay away from bluetooth pay systems??
There is a really cool bit-bang implementation for AVRs:
http://blog.nonan.net/2013/11/simple-nfc.html
The demo code emulates a dumb NFC tag (r+w), but It can be expanded easily.
I tried it out and it worked flawlessly.
“the card details are encrypted by Google and held in the cloud” – What could possibly go wrong?
“NFC transceivers are now being built into many mobile devices including the iPhone and iWatch”
I can’t believe that Apple are releasing the iWatch so soon after the Apple Watch.
Quick question to those who know: I seem to recall that paypass and others don’t do any authentication on the client’s side… is it correct? if so… has it changed?
Nice article on NFC. Thanks for writing it.
I like the Adafruit NFC shield, their libraries need expanding, or I suppose I just need to explore libnfc.
Another NXP chip for NFC is available though less capable than the one on the Adafruit shields and breakouts. Search for the RC522 on eBay and if you can live with the three week delivery from Shenzhen China you can get something that has good basic read and write capability to passive cards.
I’m just now diving into NFC, finding it very interesting and challenging-fun.
Many cellphones with NFC put the transceiver coil for it in the battery. On some it’s a thin film on the inside of the outer wrap covering on the battery while others, like the Motorola Photon Q, have it on a thin PCB, which for some reason is glued to the non-removable battery rather than to the inside of the not-easy to remove back cover.
If you’re going to swap in a higher capacity, larger battery and you use NFC, make certain the replacement battery includes an NFC coil, often mistakenly listed as a “chip”.
Why not use conductive ink or some type of metal plating to put the NFC coil directly on the inside of the phone’s back cover? Those processes could easily be duplicated by aftermarket companies manufacturing enlarged covers for larger batteries.
This is a wild-ass guess, but it may be a matter of manufacturing costs. Like, maybe it’s more expensive to add a metal/conductive component to a plastic backplate (likely made separately from the electronic guts of the phone itself) than to something that already has conductive components.
Conductive ink does not work well for NFC antennas due to the high resistance. Also, in order to place the antenna coil on a metal surface like a battery, you need a ferrite sheet to act as a shield. I was able to get an NFC antenna to work with silver ink, but had to print many layers to reduce resistance and performance was very poor even in free space. High resistance means low Q factor and also makes tuning difficult. Until some better ink tech comes around, copper works best.
Quick bit of nitpicking:
Terminal to Card:
Type A cards use On Off Keying(OOF) with modified miller encoding.
Type B use ASK (10%) NRZ encoding
Card to Terminal:
at 106kbit/s:
Type A cards use On Off Keying(OOF) with modified miller encoding.
Type B use ASK (10%) NRZ-L encoding
at 212kbit/s and higher:
Uses Binary Phase Shift Keying(BPSK) with NRZ-L encoding
There is one other standard used in Japan and Hong Kong – FeliCa – used for transit cards and stored value. Its not in wide-spread use due to Sony not supporting the ISO process during the early years.
If interested i’ve got a fork of Adam Laurie’s RFIDiot scripts to emulate a common payment terminal for paypass and paywave (mastercard and visa). This has recently been updated to support ApplePay as well:
https://github.com/peterfillmore/RFIDIOt
and i’ve done a number of talks on the security of NFC payments with regards to visa and mastercard.
https://github.com/peterfillmore/Talk-Stuff/tree/master/Syscan2015
https://www.blackhat.com/docs/us-15/materials/us-15-Fillmore-Crash-Pay-How-To-Own-And-Clone-Contactless-Payment-Devices.pdf
My favorite tools for playing with this stuff is:
ACR122U USB reader with https://github.com/AdamLaurie/RFIDIOt
Google Nexus 4 phone with kitkat or greater (as it supports HCE modes post kitkat 4.4, any android phone “Broadcom” chipset – not NXP)
Proxmark3 for sniffing, as it gives you a great view on whats happening at the lower packet level.
Interesting. Would have been nice to get some more information in the article about the so called secure RFID systems used. Things like Legic Advant/Prime or Mifare DESFire, and how they implement secure encryption techniques for RFID tags. From what i could gather there are apps out there that implement Legic Advant for NFC smartphones already? Are there any open source implementations for such security levels out there, or is that all proprietary closed source stuff?
Can increase read range 3* using a minor modification if anyone is interested.
Tested on Galaxy S4 and found to work well, it costs about £8 for the components which can be used to modify literally dozens of phones and still not void the warranty.
Railroads use it in some capacity, found a unit that had broken off something by train tracks.