[Matikas] apparently forgets to lock the screen on his computer when he gets up to grab a coffee. And he apparently works with a bunch of sharks: “If you don’t [lock it], one of your colleagues will send email to the whole company that you invite them to get some beer (on your bill, of course).” Not saying we haven’t done similar, mind you. Anyway, forgetting to lock your screen in an office environment is serious business.
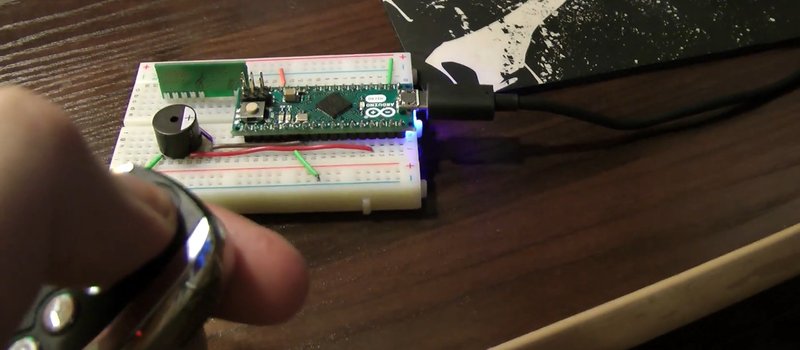
So [Matikas] built a great system that remotely types the keystrokes to lock his screen, or unlock it with his password. An off-the-shelf 433 MHz keyfob is connected to an Arduino micro that simulates a keyboard attached to his computer. It’s a simple system, but it’s a great effect. (See the video demo, below.)
But as a security device, it’s horrendous. Some el-cheapo keyfobs available on eBay don’t use rolling codes — anyone with a similar keyfob receiver will be able to listen in to the transmission, set some DIP switches, and replay it trivially. Even if it does use a rolling code, if anyone in your office plays around with RTL-SDRs, you may still be essentially broadcasting your password to everyone.
The second failure point is that [Matikas]’s password is stored in EEPROM on the Arduino. That’s a bit better than writing it on a sticky-note under the keyboard, but not against adversaries with an AVR programmer. By the time he’s taking his first sip of coffee, we’d be logged in and he’d be buying the beer.
Security aside, this is good fun, and it’s pretty cool to lock and unlock your computer with a car remote. And we’re sure that’s the right spirit in which to take it. Sometimes fun is more fun than paranoia. But maybe not if you work in an office like [Matikas]’s.















It’s good enough on the locking side anyway, who cares if anybody steals that keypress? Why oh why unlock with a fob?
More fun shenanigans – reprogram the Arduino to run a script instrad of locking. Perhaps only sometimes. Perhaps in response to detecting a longer button press – as might happen when the user is blindly trying to trigger from out of sight.
I agree.
I was thinking of having a transmitter on me that wakes and blips every second or so. Then once I pass out of range, limited by using very low power, a receiver automatically sends Windows-L to lock the computer. I still have to type in my password to log in.
I can touch type and can have my password typed in before you can say “One-Mississippi”.
Like very much!
Sounds like Bluetooth le. Sure it’s been done for Linux, so probably windows too.
http://www.howtogeek.com/67556/how-to-unlock-your-pc-by-being-nearby-with-a-bluetooth-phone/
it would not be that hard to throw in some AES and nounce.
As far as I unerstand, “you may still be essentially broadcasting your password to everyone.” is not true…. at least not over the radio. the receiving end knows the password and unlocks the PC simply when it receives a certain key press on the remote.
It is sort of true that you broadcast the key, you broadcast the key that is needed to do a replay attack (I expect the key fob to not have any encryption that is secure) and get the key from the arduino. It is like having a 4 digit pin for the box with your passwords in.
The locking part is more of a annoyance than a security risk if somebody got hold of that key fob key, since I am guessing that it corresponds to FlagKey+L.
Stupid idea… Why use such an insecure method of locking/unlocking your computer?
Ever tried https://sourceforge.net/projects/blueproximity/
There’s also a windows clone: https://sourceforge.net/projects/btprox/
Just pair your cell phone with your computer, all you need is a cheap bluetooth donge if your computer doesn’t have bluetooth.
Exactly. But it is a fun learning exercise and you could still make a million on indiegogo selling the device to idiots. :-)
And then buy a house???
From experience, the office at work is small enough that I can be across the building, and my bluetooth doesn’t disconnect for a long enough time that someone could get into my computer and send the aforementioned beer-mail. Another fun trick, the break room and bathrooms are on opposite sides of the office, but are well inside the Bluetooth connectivity range. That being said, a bluetooth based lockout would be a bad idea unless you modified the dongle to have severely reduced sensitivity(cut distance way down). This may work well if you work in a large office building/ somewhere that when you get up you need to walk a fair distance, 20-40ft from your BT Dongle depending on walls and other signal attenuation, but if it’s a small/ medium office space, it probably won’t lock fast enough/ often enough to be worth while.
In all honesty, the keyfob would be a great idea, hide the hardware in a box velcroed under the desk, and call it good for a mk 1 build. Maybe later, if the BT has a means of detecting signal strength, use that as a 2 factor authentication, if the signal strength is increasing/ above a set point, and the keyfob is pressed, unlock the machine, if it’s below, set a timeout that if it gets to the threshold level, unlock, if not, the timeout finishes and waits for another press of the fob.
@stichl – it’s a fun thing to work on, for the conditions, it seems to be a great fit, maybe it can be updated/ upgraded at a later time, and as it was written, you still need to want to get into the computer to get past the SLIGHTLY increased security.
You could try the BT remotes they add to selfie sticks on aliexpress. I believe they are HID keyboards on the protocol side. You would just force the system to change the keymap on the particular input device. Still doesn’t fix the security part, but hey – it is easier to just plug in a hardware keylogger and steal your password than play back RF signals with an SDR.
You guys are a bunch of wizards … gotta keep by laptop and phone a mile away from all of you!
NOT if they’re internet connected lol. (Nothing personal).
He needs to play a wav file of a car alarm chip every time he locks and unlocks it with the fob.
And then add some lights motors and wheels to the box so that it can indicate as it drives away.
I hope he has. If someone tries to unlock with the wrong password a car alarm should go off.
For five minutes of course!
Tokenlock does the same thing using the bluetooth on your smart phone.
You need to be a person who a) carries a (powered-up) smartphone with b) BT enabled.
But I guess that’s a rather large percentage.
Have a dummy keyboard on your desk and then keep a wireless one in the trash can. Fart in their chairs. If you can’t remember to lock your machine just remember to fart in the empty chair. That would probably work. You could also call their loved ones and tell them they bought a boat and were telling you about dating again. That should keep them busy for a while. You would also be wise to START COUGHING ON EVERYTHING as they are your germs and you will rise to the top of the heap over your weakened competitors. You should also give a grimace and a snort whenever you see them eating or if they present an idea that is better than yours just to throw them off and make them question their judgement. I would refrain from gossip but the occasional ‘dropped’ note around the office keeps things lively.
You could upperdeck the toilet just before you leave for the night and then call in sick the next day with a sore throat. I usually use the day to catch up on laundry with a pork shoulder in the crock pot. Sometimes it is nice to have some store-bought cookies laying around so you don’t have to wait for them to bake.
Are YOU baked?
No, you just have the reading comprehension of a carrot. Try sounding out the words as you read them.
+1
Nice.
I knew somebody would figure it out eventually.
You win the internet. ;)
.
At least I got to see a polar bear.
http://i1097.photobucket.com/albums/g352/Useruser2/itstimetostop.jpg
You sound fat.
You sound like you are a pretty good manager.
http://i1.kym-cdn.com/photos/images/newsfeed/001/119/553/723.png
Why should I fiddle around with the capture and replay of the unlock signal, if can just plug his receiver into my computer and open an editor?
Guess it all depends on what type of office he’s working in, are his co-workers technoidiots or HAD contributors?
Hmm, not mutually exclusive!
I said hack a day contributors, the people who do the hacks, not the commentators.
This. I can think of only two people in our entire building who could unravel even this. Yes, it’s an academic engineering department.
They can publish the daylights out of equations though.
If [Matikas] can’t remember to press two keys to lock his screen when getting up, how he will remember to use keyfob? And why he didn’t set up a autolock timer in his Windows?
He did if for http://tvtropes.org/pmwiki/pmwiki.php/Main/RuleOfCool
Though yeah, autolock that computer!
I’m wondering if it would be easier to hack the hardware instead of the radio signal.
The old, restart badly, use the text file in the repair report to gain access to make sticky keys the prompt; restart, change password and login. Almost makes anything like this moot, unless it’s really time critical.
Then again, if it’s that imperative, it’s worth thinking about a bit more.
Who knows, maybe it’s booby trapped, to check certain things are what they say they are and things point to the right places.
Better to use an implanted NFC tag. Still convenience rather than security, but better than a remote. Less likely to lose it for a start.
https://0xfred.wordpress.com/2016/03/04/nfc-login-2-1/
I had the same problem 5 years ago, so I made a small windows service which monitored the Bluetooth connection to my phone, and locked my computer if the connection was lost.
Version 2. didn’t lock the computer but simply “armed” it.
If somebody tried to use the computer when it was armed:
1) Display a picture of a laughing Horse and play an audio clip with a horse at full volume.
2) The computer would take a picture of the user, place it inside a picture of a horse’s ass and post it on Yammer.
3) The computer would lock.
Actually, I can see that it was a normal (tray-Icon) application, and not a Windows Service….
I must not know anyone intelligent enough to even try to hack the security on anything I could rig up. Where are all these people at? I love the articles but seriously, is it really that necessary to discuss the vulnerabilities in something like this? Seems tin-foil-hat ‘ish to me.
Well, some people work with smart coworkers. Poor security is a very valid argument here. If everyone here copied his hack verbatim, at least one of us would get hacked. Do you think he did this and didn’t tell anyone that he can unlock his computer with a remote?
Hi, I’m the author of this hack ant you sir speak my thoughts. I totally understand it being super unsecure but cmon… since my biggest loss would be beer for one who actually would not lazy and sneaky to crack my pass.
The discussions about security here were really great though! I did like the hack. I think it would work good on a toolbox with a keypad safe.
Great job!
[quote] “Seems tin-foil-hat ‘ish to me” [/quote]
No-one wears tin foil hats anymore. They all us aluminum hast because tin conducts alpha particles and the NSA detects those to read your mind.
I use the thick foil. You know, the stuff they market for grilling outdoors.
Saves my vegetables from getting burnt to a crisp and keeps the brainwaves where they belong. Great stuff!
.
Also, homemade capacitors.
Anyone else remember when PCs came with an actual honest-to-goodness keyed lock for the keyboard? The only problem was that most of them used the same darn key!
I have three locks on my keyboard! Num lock, scroll lock, CAPS LOCK.
http://cdn.memestache.com/2012/6/14/memestache.com_214846_1340272805.jpg
Okay, sorry I derailed your question for a stupid meme. I am too young (30ish) to remember lockable keyboards.
Was it usually so the keyboard wouldn’t get stolen or so an unauthorized person couldn’t use it? Or was it just standard practice for awhile? I’ve read that some keyboards were very high quality and weren’t cheap back then.
It was a key selling feature and many people bought them.
You might also be able to (minimally) increase security by implementing a 2-factor style unlock sequence. Maybe generate a random interger a day or hour on the PC or Arduino that would be need to be keyed into the fob… If today’s magic number is 3, you’d need to press the unlock key three times…
That being said, I’d be more likely to put tech like this to use as a remote rick-roll detonator for a co-workers PC. :-D
A pressure mat to lock screen would be better, no unlock needed; unless laziness was the primary reason for this. ~My office chair is from a S-type Jaguar 2006 and *Oh hey*… It has one built in.
Still, nice hak
The gatekeeper works pretty darn well, here is a review – https://www.youtube.com/watch?v=z_6HEoOrdE4