[Matikas] apparently forgets to lock the screen on his computer when he gets up to grab a coffee. And he apparently works with a bunch of sharks: “If you don’t [lock it], one of your colleagues will send email to the whole company that you invite them to get some beer (on your bill, of course).” Not saying we haven’t done similar, mind you. Anyway, forgetting to lock your screen in an office environment is serious business.
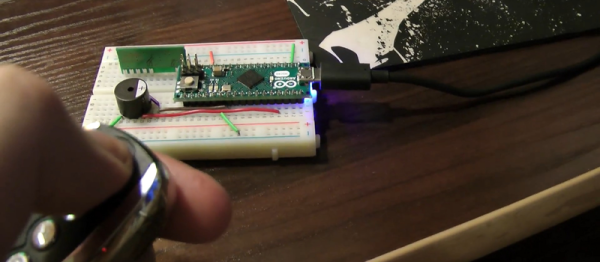
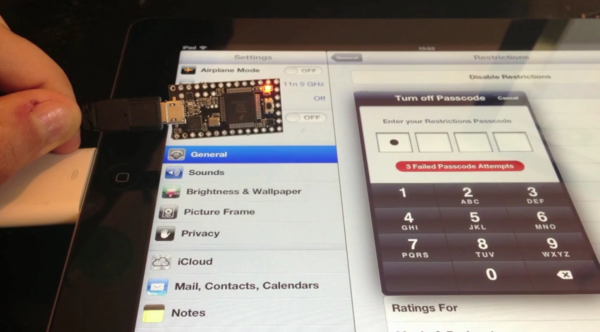
So [Matikas] built a great system that remotely types the keystrokes to lock his screen, or unlock it with his password. An off-the-shelf 433 MHz keyfob is connected to an Arduino micro that simulates a keyboard attached to his computer. It’s a simple system, but it’s a great effect. (See the video demo, below.)
Continue reading “Coolest, But Least Secure, Security Device”