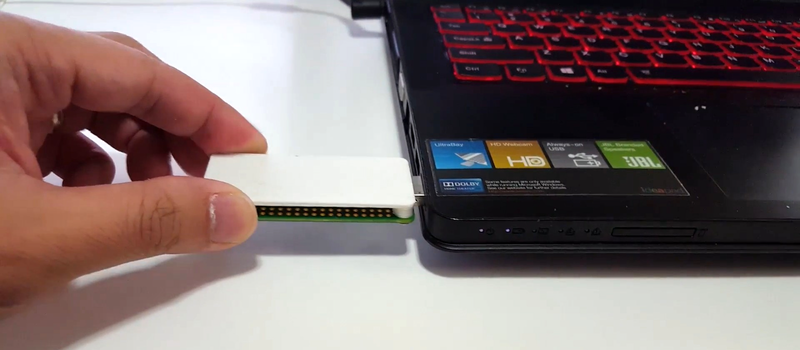
The Raspberry Pi Zero is small enough that it could almost be mistaken for a USB gadget, rather than a standalone computer. Maybe that was the inspiration that drove [Novaspirit] to completely “donglify” his Zero.
This is a great convenience hack if you’ve got a Zero just kicking around. With minimal soldering, he converted the Zero’s onboard female USB jacks into a male USB plug. From there on out, it’s all software, and the video (embedded below) takes you through all the steps on Windows.
First, he attaches the Raspberry Pi Zero running Pixel OS to his main computer as a USB network device, and then configures it to be useful. He sets up VNC on the Pi so that you can log into its desktop in a window, sets up networking on the Pi so that it can connect to the wider Internet through the laptop, etc. He installs OwnCloud so that the Zero serves as a cloud storage solution, only the “cloud” is plugged into your laptop’s USB port. The point of all this is getting the maximum benefit out of a Pi Zero without having to lug around any cables: just plug it in and you’re networked.
Of course, [Novaspirit] isn’t the first person to have ever connected a Zero over USB networking. But his hardware hack is neat and dead simple, and setting up the software side will teach you something if you’ve got a Windows background. Check it out.















It’s awesome. The Pi Foundation should consider selling Zeros in this form, actually.
Can you configure/program it to work as mass storage? It would be cool platform for implementing custom (=without backdoors) encrypted flashdrive or microsd reader…
Yes, you can make it a mass storage and we’v seen that functionality used in some interesting hacks.
After seeing http://hackaday.com/2016/10/22/hackaday-prize-entry-the-fog-the-cloud-at-ground-level/ yesterday this seemed to be the next logical step.
Having a tiny board that sits between a PC host and WiFi connection has possibilities…
I believe the setup described here has the PC host sitting between the tiny board and the WiFi connection.
Yeah, but think of all the things you could do with the Pi acting as a USB connected WiFi router…
I think the current draw for a stand-alone Pi Zero will exceed the limits of a vast number of USB ports on devices like laptops etc. (500mA max?) To prevent problems, protection would need to be built-in and perhaps a red LED that lights when the device does not get the current it needs (or negotiates to get the current it needs over USB). So a stand-alone Pi-Zero as a USB “stick” is probably just asking for trouble.
RPi Zero is around 140mA without any extra peripherals like USB devices or HATs. The larger RPi boards draw significantly more.
USB ports on a computer can supply 500ma if the board has identified itself.
It doesn’t have that high current-draw, to be honest. I actually have a Pi Zero with a WiFi-adapter connected to it, powered from a USB 2.0-port, at this very moment and both are working fine.
If the Pi Zero negotiates with the PC for more current, it can get as much current as a USB host port can supply, 2.1A I believe.
In theory the max is 500mA. The amount a device can ask for is communcated in a byte. The units are steps of 2mA. Thus the allowed values are 0-250, allowing the device to request 0-500mA of current. Stretching it would allow requesting 510mA……
USB 2.0 host-ports have a maximum of 500mA, not 2.1A. There is no such USB-spec in the first place that’d supply that much current and still allow for data-delivery. Battery-charging spec does allow you to build a circuit allowing up to 5A current, but that’s exactly that: for charging, not data, and no regular PC has such.
https://en.wikipedia.org/wiki/USB#Power
I’m pretty sure it’s in the USB 3 specs.
Earlier laptops / notebooks, with external CD-ROM drives, used a Y-adapter USB cable to draw current from more than one USB port.
With an adapter cable, you don’t even need to replace the USB connector on the Pi Zero.
Funny how I’ve read about using this thing in Gadget-Mode several times, but somehow it seems *entirely* different just being in a thumb-drive style housing. That could sound snide, but it’s legit.
I love the form factor, but I’m trying to find a way to autonegotiate bridging, so the Pi can use the host computer’s network connection. Anyone have any ideas on that?
With the current state of network threats and the required levels of security needed on our computers, I suspect your best bet is going to be a program or service pre-installed and running on the computer that watches for the Pi network interface device to come into existence, which triggers the desired networking configuration changes to be made to enable bridging.
No modern operating system is going to assist you in “automagically” performing such setup at the request of the Pi itself, and I would imagine most everyone with any security consciousness would desire such a thing anyway.
It may be possible on older a much older OS (maybe WinXP with security features pre-disabled, but quite likely on even older versions of Windows) to have the Pi show up as a mass storage device first with an autorun file and program to be installed to do the network setup, before having the Pi switch over to USB networking mode.
At least the pre-installed service monitoring the network adapters for the Pi interface would potentially be a sorta-cross-platform solution. Obviously the software would need to be targeted to the platform and would go about network bridging in different ways, but the software would basically be triggered using the same idea.
my, my, you are a trusting sort.
https://room362.com/post/2016/snagging-creds-from-locked-machines/
At first glance at that URL, I thought I remembered that being “fixed” in Windows 7 (well maybe Vista, I can’t say) and did just confirm that user interaction is required before SMB is enabled on a new interface.
A dialog comes up asking if the new network is to be defined as home, work, or public. Not clicking, or clicking public, does not enable SMB for even the basis of his idea to function.
So I figured maybe his proxy auto config was doing some trickery and decided to setup DHCP and actually try it.
He claims all the magic happens in his wpad.dat file sent to the computer to define a proxy. It doesn’t make sense to capture credentials as he claims, but I can see any passwords saved in your browser sent over plaintext to be obtainable.
But when following his setup, there is no wpad.dat file on his page, posted linked or otherwise.
There is absolutely nothing provided to replicate his claims, as he is clearly keeping his special wpad.dat file secret and to himself.
As-is the only way his “attack” would work at all is if:
a) you are at the computer, unlocked, and interacting with it.
b) you see the new network device dialog and click a button saying you trust the network, while pretending to not notice you just did that
c) you open your web browser, and go to a non SSL website, that you have previously been to, logged in to, and saved the password for
and d) you use the same password on that non-encrypted website as you do for your computer login.
But you know, you can get the same effect by just using public wifi. Your ISP already has access to everything you send non-encrypted too. None of his unique steps are required or do anything particularly special that a plain old network sniffer won’t do.
Make it connect as USB keyboard, and type the necessary commands.
You might want to check this out to learn more about USB in Linux on both host and device side.
https://www.youtube.com/watch?v=JLhcE0O4bt0
to be honest, i prefer to use just a 10cm usb cable. it kinda gives me a better feeling knowing there wont break anything that easily..
second thing i want to mention:
woudnt it be brilliant to connect a rpi0 to your android device with usb otg, and use an ssh app to connect to it. just imagine!
grab your smartphone, take a bluetooth keyboard and last but not least the rpi0 and you can code anywere ! ! !
:D
oh yeah, and you dont need to split that usb cable for power and data. just use the “USB”-labled usb port on the rpi0!
and one last thing, this works with an rpi1A+ as well..
This was done before by NODE :
https://youtu.be/qbWYUFgLhSU
And it was done before that by me:
https://www.youtube.com/watch?v=bayeH2iZA0c
Neat design!
But ugly firestick :D
That’s pretty cool. Where could I pick one up from?
What is important is that they drivers are in the kernel now. Before you had to do some driver magic that I don’t know enough to understand. Now, a couple text files change, and software done. :)
This had been done on the Model A and A+. But the zero’s form factor makes it very nice.
Raspbian is the best Linux based distro I have used. :)
What would be supercool is if it had a small boot partition for x86 on it, say trimmed down puppy install. So when you powered on any old POS PC it booted off it, and loaded clients so it is doing its braining on the pi.
Though some old stuff you might need a boot floppy, because it won’t usb boot.
For Everyone who isn’t an expert on soldiering-
Theres a project on kickstarter that’s basically the same concept except for it uses Pogo pins instead of wires.
https://www.kickstarter.com/projects/1728237598/notixed-turn-your-pi-zero-to-usb-device
For everyone that’s not an expert on soldiering:
I found a project on kickstarter that uses pogo pins instead of wires to connect to the Pi Zero. Its almost the same thing.
Its called NotixED on kickstarter
I have almost done this to my zero on Windows 10, but there is a but.
I have installed the RNDIS Gadget 2 driver to my system, no problems there.
But when I try to ssh into my Pi via USB I get : Network error: connection refused. Both using raspberrypi.local and with the Ip address.
Me not very clever boy….
Just needed to enable SSH.
When the tutorial video was created, SSH was automatically enabled. That’s why it’s not a step.
See here people, an usb adapter has now been done, I’ve bought two … ….
https://thepihut.com/collections/raspberry-pi-store/products/pizero-usb-stem
Has anyone done this but include access to a network share?
Example:
(Stand-alone DVD player) —-USB—– PIZero —WiFi——network share